Kubernetes Ingress-nginx使用
简介
Kubernetes 提供了两种内建的云端负载均衡机制( cloud load balancing )用于发布公共应用, 工作于传输层的 Service 资源,它实现的是 TCP 负载均衡器”,另种是Ingress 资源,它 现的是“ HTTP(S )负载均衡器”
Ingress和Ingress Controller
Ingress是Kubernetes API的标准资源类型之一,它其实就是基于DNS名称(host)或URL路径把请求转发至指定的Service资源的规则,用于将集群外部的请求流量转发至集群内部完成服务发布。然而,Ingess资源自身并不能运行“流量穿透”,它仅仅是一组路由规则的集合,这些规则要想真正发挥作用还需其它功能的辅助,如监听某个套接字上,根据这些规则匹配机制路由请求流量:这种能够为Ingress资源监听套接字并转发流量的组件称之为Ingress控制器
注意:
不同于 Deployment 控制器等 Ingress 控制器并不直接运行为 kube-controller-rnanager的一部 ,它是Kubemetes集群的重要附件类似于 CoreDNS 需要在集群单独部署
1. 部署Ingress-Controller
此处部署3.0版本
在你需要部署的node节点上拉去Ingerss-Controller镜像
[root@k8s-master01 daem]# docker pull quay.io/kubernetes-ingress-controller/nginx-ingress-controller:0.30.0
进入到GitHub上将mandatory.yaml复制到node节点上
[root@k8s-master01 ingressdeploy]# cat mandatory.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
#data:
# whitelist-source-range: 192.168.29.102 #白名单,允许某个IP或IP段的访问
# block-cidrs: 192.168.29.101 #黑名单拒绝访问
---
kind: ConfigMap
apiVersion: v1
metadata:
name: tcp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: udp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: nginx-ingress-clusterrole
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses/status
verbs:
- update
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: Role
metadata:
name: nginx-ingress-role
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
resourceNames:
# Defaults to "<election-id>-<ingress-class>"
# Here: "<ingress-controller-leader>-<nginx>"
# This has to be adapted if you change either parameter
# when launching the nginx-ingress-controller.
- "ingress-controller-leader-nginx"
verbs:
- get
- update
- apiGroups:
- ""
resources:
- configmaps
verbs:
- create
- apiGroups:
- ""
resources:
- endpoints
verbs:
- get
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: RoleBinding
metadata:
name: nginx-ingress-role-nisa-binding
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: nginx-ingress-role
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: nginx-ingress-clusterrole-nisa-binding
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: nginx-ingress-clusterrole
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-ingress-controller
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
replicas: 1
selector:
matchLabels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
annotations:
prometheus.io/port: "10254"
prometheus.io/scrape: "true"
spec:
hostNetwork: true ###修改成hostNetwork模式直接共享服务器的网络名称空间
# wait up to five minutes for the drain of connections
terminationGracePeriodSeconds: 300
serviceAccountName: nginx-ingress-serviceaccount
nodeSelector:
kubernetes.io/os: linux
kubernetes.io/hostname: k8s-master02
dnsPolicy: ClusterFirstWithHostNet
containers:
- name: nginx-ingress-controller
imagePullPolicy: IfNotPresent
image: quay.io/kubernetes-ingress-controller/nginx-ingress-controller:0.30.0
args:
- /nginx-ingress-controller
- --configmap=$(POD_NAMESPACE)/nginx-configuration
- --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services
- --udp-services-configmap=$(POD_NAMESPACE)/udp-services
- --publish-service=$(POD_NAMESPACE)/ingress-nginx
- --annotations-prefix=nginx.ingress.kubernetes.io
securityContext:
allowPrivilegeEscalation: true
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
# www-data -> 101
runAsUser: 101
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
ports:
- name: http
containerPort: 80
protocol: TCP
#hostPort: 80
- name: https
containerPort: 443
protocol: TCP
#hostPort: 443
livenessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
---
apiVersion: v1
kind: LimitRange
metadata:
name: ingress-nginx
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
limits:
- min:
memory: 90Mi
cpu: 100m
type: Container
需修改:
hostNetwork: true ###修改成hostNetwork模式直接共享服务器的网络名称空间
执行create创建Ingress-Controller
[root@k8s-master01 ingressdeploy]# kubectl get deploy -n ingress-nginx
NAME READY UP-TO-DATE AVAILABLE AGE
nginx-ingress-controller 1/1 1 1 76m
Ingress-Controller已部署完成
2. 使用Ingress规则
创建测试的web应用
[root@k8s-master01 daem]# cat deploy.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
namespace: default
name: nginxapp
labels:
app: nginx-deploy
spec:
replicas: 2
selector:
matchLabels:
app: mynginx
template:
metadata:
labels:
app: mynginx
spec:
containers:
- name: nginxweb
image: nginx:1.15-alpine
[root@k8s-master01 daem]# cat svc.yaml
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
labels:
app: nginx-svc
spec:
ports:
- name: http
port: 80
protocol: TCP
nodePort: 30001 #node节点的映射端口 可以通过外部访问
targetPort: 80
selector:
app: mynginx
sessionAffinity: None
type: NodePort
创建Ingress规则
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/limit-connections: 10
#nginx.ingress.kubernetes.io/limit-rate: 100K
#nginx.ingress.kubernetes.io/limit-rps: 1
#nginx.ingress.kubernetes.io/limit-rpm: 30
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
浏览器访问
添加hosts解析
192.168.29.102 test.nginxsvc.com test-tls.test.com
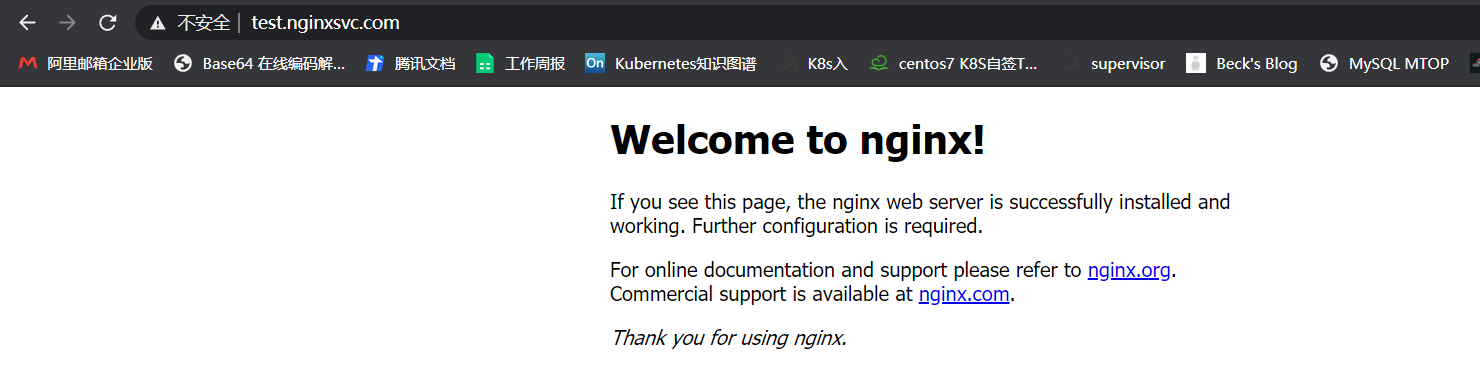
[root@k8s-master01 daem]# curl -I http://test.nginxsvc.com/
HTTP/1.1 200 OK
Server: nginx/1.17.8
Date: Thu, 03 Dec 2020 06:56:49 GMT
Content-Type: text/html
Content-Length: 612
Connection: keep-alive
Vary: Accept-Encoding
Last-Modified: Sat, 11 May 2019 00:35:53 GMT
ETag: "5cd618e9-264"
Accept-Ranges: bytes
2.1 Ingress地址重写
流量重定向到目标URL
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com #当访问 test.nginxsvc.com会被重写到百度上
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
前后端分离
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com
nginx.ingress.kubernetes.io/rewrite-target: / #当访问test.nginxsvc.com/foo 会把请求打到 nginx-svc此service上
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /foo
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com
nginx.ingress.kubernetes.io/rewrite-target: /$2
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /nginxservice(/|$)(.*)
paths:
- backend:
serviceName: tomcat-svc
servicePort: 80
path: /tomcatservice(/|$)(.*) #当访问test.nginxsvc.com:PORT/tomcatservice -> 就会被重定向到tomcat-svc / 资源下
2.2 配置HTTPS
[root@k8s-master01 ~]# openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.cert -subj "/CN=test-tls.test.com/O=test-tls.test.com"
Generating a 2048 bit RSA private key
..............................................+++
.........................................................................................+++
writing new private key to 'tls.key'
-----
[root@k8s-master01 ~]# kubectl create secret tls ca-cert --key tls.key --cert tls.cert
secret/ca-cert created
[root@k8s-master01 ~]# cat tlsingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
annotations:
nginx.ingress.kubernetes.io/ssl-redirect: "false"
name: test-tls
spec:
rules:
- host: test-tls.test.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
tls:
- hosts:
- test-tls.test.com
secretName: ca-cert
2.3 黑白名单配置
黑白名单
[root@k8s-master01 ingressdeploy]# cat mandatory.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
data:
#############添加如下信息#################
whitelist-source-range: 192.168.29.102 #白名单,允许某个IP或IP段的访问
block-cidrs: 192.168.29.101 #黑名单拒绝访问
2.4 匹配请求头
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
annotations:
nginx.ingress.kubernetes.io/server-snippet: |
set $agentflag 0;
if ($http_user_agent ~* "(Mobile)" ){
set $agentflag 1;
}
if ( $agentflag = 1 ) {
return 301 https://m.example.com;
}
解释:
如果你的http_user_agent == Mobile。那么就把agentflag set成1 ,然后当agentflag == 1时,就会return 到这个域名 https://m.example.com
2.5 速率限制
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
annotations:
kubernetes.io/ingress.class: "nginx"
nginx.ingress.kubernetes.io/limit-rate: 100K
nginx.ingress.kubernetes.io/limit-rps: 1
nginx.ingress.kubernetes.io/limit-rpm: 30
spec:
......
nginx.ingress.kubernetes.io/limit-connections
单个IP地址允许的并发连接数。超过此限制时返回503错误
nginx.ingress.kubernetes.io/limit-rps:
每秒从给定IP接受的请求数。突发限制设置为该限制乘以突发乘数,默认乘数为5。当客户机超过此限制时,将返回limit req status code default:503
nginx.ingress.kubernetes.io/limit-rpm:
每分钟从给定IP接受的请求数。突发限制设置为该限制乘以突发乘数,默认乘数为5。当客户机超过此限制时,将返回limit req status code default:503
nginx.ingress.kubernetes.io/limit-burst-multiplier:
突发大小限制速率的乘数。默认的突发乘数为5,此批注覆盖默认乘数。当客户机超过此限制时,将返回limit req status code default:503。
nginx.ingress.kubernetes.io/limit-rate-after
初始千字节数,此后对给定连接的响应的进一步传输将受到速率限制。此功能必须在启用代理缓冲的情况下使用
nginx.ingress.kubernetes.io/limit-rate
每秒允许发送到给定连接的KB数。零值禁用速率限制。此功能必须在启用代理缓冲的情况下使用
nginx.ingress.kubernetes.io/limit-whitelist
要从速率限制中排除的客户端IP源范围。该值是一个逗号分隔的cidr列表
以上就是Ingress常用的相关配置,所有配置均来自官方文档:https://kubernetes.github.io/ingress-nginx/user-guide/nginx-configuration/annotations/
Kubernetes Ingress-nginx使用的更多相关文章
- Kubernetes Ingress Controller的使用及高可用落地
Kubernetes Ingress Controller的使用及高可用落地 看懂本文要具备一下知识点: Service实现原理和会应用 知道反向代理原理,了解nginx和apache的vhost概念 ...
- Kubernetes Ingress 学习
Kubernetes 中暴露服务的方式有三种 Loadbalancer 这种方式往往需要云供应商支持,或者本地F5等设备支持 NodePort 这种方式调用方通过NodeIP:NodePort 的方式 ...
- Kubernetes Ingress管理
目录 Ingress介绍 1.Pod漂移问题 2.端口管理问题 3.域名分配及动态更新问题 Nginx Ingress配置 1.部署默认后端 2.部署Ingress Controller 3.部署In ...
- Kubernetes Ingress 部署
Kubernetes Ingress 部署 Pod与Ingress的关系• 通过service相关联• 通过Ingress Controller实现Pod的负载均衡- 支持TCP/UDP 4层和HTT ...
- 基于k8s集群部署prometheus监控ingress nginx
目录 基于k8s集群部署prometheus监控ingress nginx 1.背景和环境概述 2.修改prometheus配置 3.检查是否生效 4.配置grafana图形 基于k8s集群部署pro ...
- [转帖]kubernetes ingress 在物理机上的nodePort和hostNetwork两种部署方式解析及比较
kubernetes ingress 在物理机上的nodePort和hostNetwork两种部署方式解析及比较 https://www.cnblogs.com/xuxinkun/p/11052646 ...
- Kubernetes Ingress日志分析入门
本文主要介绍如何基于日志服务构建Kubernetes Ingress日志分析平台,并提供一些简单的动手实验方便大家快速了解日志服务相关功能. 部署Ingress日志方案 登录容器服务管理控制台. 将上 ...
- Kubernetes Ingress简单入门
作者:Nick Ramirez 原文链接:https://thenewstack.io/kubernetes-ingress-for-beginners/ 本文转载自Rancher Labs 不知道你 ...
- CORS跨源资源共享概念及配置(Kubernetes Ingress和Spring Cloud Gateway)
我最新最全的文章都在南瓜慢说 www.pkslow.com,欢迎大家来喝茶! 1 跨源资源共享CORS 跨源资源共享 (CORS) (或通俗地译为跨域资源共享)是一种基于HTTP 头的机制,该机制通过 ...
- 几张图解释明白 Kubernetes Ingress
来源:K8s技术圈 作者:阳明 Kubernetes Ingress 只是 Kubernetes 中的一个普通资源对象,需要一个对应的 Ingress 控制器来解析 Ingress 的规则,暴露服务到 ...
随机推荐
- python开发基础(二)运算符以及数据类型之tuple(元组)
# encoding: utf-8 # module builtins # from (built-in) # by generator 1.147 """ Built- ...
- 题解 P1541 【乌龟棋】
题目描述 乌龟棋的棋盘是一行\(N\)个格子,每个格子上一个分数(非负整数).棋盘第\(1\)格是唯一的起点,第\(N\)格是终点,游戏要求玩家控制一个乌龟棋子从起点出发走到终点. 乌龟棋中\(M\) ...
- 关于C语言中的位运算符的学习即应用
一.运算符的种类和运算规则: & 与:全1则1,有0则0 | 或:有1则1,全0则0 ^ 异或:相同为0,不同为1 ~ 取反:~是一元运算符,用来对一 ...
- JavaSE基础语法学习-异常
异常 异常指程序运行中出现的不期而至的各种状况,如:文件找不到.网络连接失败.非法参数等. 异常发生在程序运行期间,它影响了正常的程序执行流程. 比如说,你的代码少了一个分号,那么运行出来结果是提示是 ...
- ERP中HR模块的操作与设计--开源软件诞生26
赤龙ERP的EHR功能讲解--第26篇 用日志记录"开源软件"的诞生 [进入地址 点亮星星]----祈盼着一个鼓励 博主开源地址: 码云:https://gitee.com/red ...
- MQ-gogogo
1. RocketMQ https://github.com/alibaba/RocketMQ/wiki/quick-start 2. RabbitMQ https://www.rabbitmq.co ...
- MYSQL学习(二) --MYSQL框架
MYSQL架构理解 通过对MYSQL重要的几个属性的理解,建立一个基本的MYSQL的知识框架.后续再补充完善. 一.MYSQL架构 这里给的架构描述,是很宏观的架构.有助于建立对MYSQL整体理解. ...
- 睿象云:为什么 Zabbix 告警如此火热?
每当我们谈及监控工具的时候,Zabbix 总是最惹人瞩目的那一个.如同清晨荷叶上的剔透露珠,卓尔不凡:如同巷子末头的百年酒香,让人倾心.我们都知道 Zabbix 是监控工具里当仁不让的龙头大哥,却没几 ...
- 希捷powerchoice磁盘休眠功能arm打包
官方只提供了x86下面的包,没有提供arm下面的包,而我们的arm机器是32位的,需要编译一个支持armhf的二进制文件,这个文件只需要一个即可,但是编译是整套编译的,并且我们需要选定指定的版本,关闭 ...
- RTP协议解析及H264/H265 音视频RTP打包分析
一 概述 实时传输协议(Real-time Transport Protocol或简写RTP)是一个网络传输协议,它是由IETF的多媒体传输工作小组1996年在RFC 1889中公布的. RTP协议详 ...
