RouterOS 设定NAT loopback (Hairpin NAT)回流
In the below network topology a web server behind a router is on private IP address space, and the router performs NAT to forward traffic to its public IP address to the web server behind it.
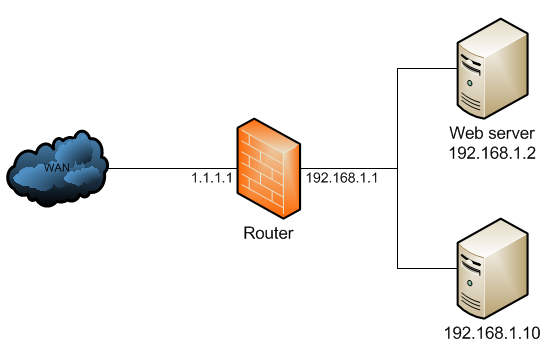
The NAT configuration would look like below:
/ip firewall natadd chain=dstnat dst-address=1.1.1.1 protocol=tcp dst-port=80 \ action=dst-nat to-address=192.168.1.2add chain=srcnat out-interface=WAN action=masquerade
When a client out on the Internet with IP address 2.2.2.2 establishes a connection to the web server, the router performs NAT as configured.
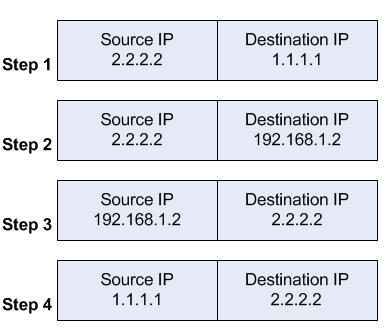
- the client sends a packet with a source IP address of 2.2.2.2 to a destination IP address of 1.1.1.1 on port tcp/80 to request some web resource.
- the router destination NATs the packet to 192.168.1.2 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 2.2.2.2.
- the server replies to the client's request and the reply packet has a source IP address of 192.168.1.2 and a destination IP address of 2.2.2.2.
- the router determines that the packet is part of a previous connection and undoes the destination NAT, and puts the original destination IP address into the source IP address field. The destination IP address is 2.2.2.2, and the source IP address is 1.1.1.1.
The client receives the reply packet it expects, and the connection is established.
When a client on the same internal network as the web server requests a connection to the web server's public IP address, the connection breaks.
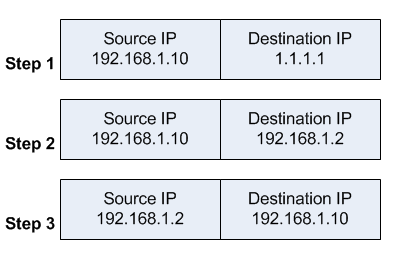
- the client sends a packet with a source IP address of 192.168.1.10 to a destination IP address of 1.1.1.1 on port tcp/80 to request some web resource.
- the router destination NATs the packet to 192.168.1.2 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 192.168.1.10.
- the server replies to the client's request. However, the source IP address of the request is on the same subnet as the web server. The web server does not send the reply back to the router, but sends it back directly to 192.168.1.10 with a source IP address in the reply of 192.168.1.2.
The client receives the reply packet, but it discards it because it expects a packet back from 1.1.1.1, and not from 192.168.1.2. As far as the client is concerned the packet is invalid and not related to any connection the client previously attempted to establish.
To fix the issue, an additional NAT rule needs to be introduced on the router to enforce that all reply traffic flows through the router, despite the client and server being on the same subnet. The rule below is very specific to only apply to the traffic that the issue could occur with - if there are many servers the issue occurs with, the rule could be made broader to save having one such exception per forwarded service.
/ip firewall natadd chain=srcnat src-address=192.168.1.0/24 \ dst-address=192.168.1.2 protocol=tcp dst-port=80 \ out-interface=LAN action=masquerade
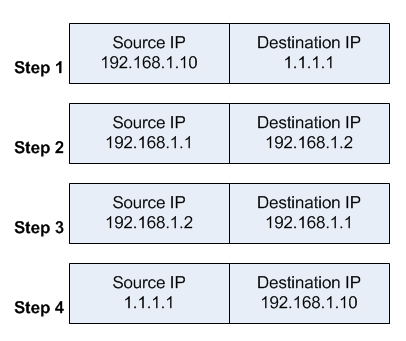
With that additional rule, the flow now changes:
- the client sends a packet with a source IP address of 192.168.1.10 to a destination IP address of 1.1.1.1 on port tcp/80 to request some web resource.
- the router destination NATs the packet to 192.168.1.2 and replaces the destination IP address in the packet accordingly. It also source NATs the packet and replaces the source IP address in the packet with the IP address on its LAN interface. The destination IP address is 192.168.1.2, and the source IP address is 192.168.1.1.
- the web server replies to the request and sends the reply with a source IP address of 192.168.1.2 back to the router's LAN interface IP address of 192.168.1.1.
- the router determines that the packet is part of a previous connection and undoes both the source and destination NAT, and puts the original destination IP address of 1.1.1.1 into the source IP address field, and the original source IP address of 192.168.1.10 into the destination IP address field.
The client receives the reply packet it expects, and the connection is established.
However, the web server only ever sees a source IP address of 192.168.1.1 for all requests from internal clients regardless of the internal client's real IP address. There is no way to avoid this without either using a router that can do application level DNS inspection and can rewrite A records accordingly, or a split DNS server that serves the internal clients the internal server IP address and external clients the external server IP address.
This is called - among other terms - hair pin NAT because the traffic flow has clients enter the router through the same interface it leaves through, which when drawn looks like a hair pin.
RouterOS 设定NAT loopback (Hairpin NAT)回流的更多相关文章
- Linux 与 CONE NAT 和 Symmetric NAT
http://alexanderlaw.blog.hexun.com/31883661_d.html 1. NAT 的划分 RFC3489 中将 NAT 的实现分为四大类: 1. Full Cone ...
- 静态NAT、动态NAT
静态NAT.动态NAT 实验拓扑: 实验目的:熟悉网络地址转换协议 掌握静态NAT 和动态NAT的配置 分析静态NAT 和动态NAT的区别 使用show命令来检查NAT的运行情况 实验要求:按拓扑图来 ...
- 运营商级NAT(Carrier-grade NAT)
运营商级NAT(Carrier-grade NAT) 运营商级(Carrier-grade)NAT,是用于缓解是IPV4地址枯竭的一种方法,通过这种方法,原来被分配公网ip的端点.家庭网络等可以被 ...
- CONE NAT 和 Symmetric NAT
CONE NAT 和 Symmetric NAT 1. NAT 的划分 RFC3489 中将 NAT 的实现分为四大类: Full Cone NAT 完全锥形 NAT Restricted Cone ...
- 什么叫NAT,设置NAT的两个方法
NAT是网络地址翻译就是把公网IP翻译成私有地址, 又叫端口映射或端口转发. 采用路由方式是指ADSL拥有一个动态或固定的公网IP,ADSL直接接在HUB或交换机上,所有的电脑共享上网.这时ADSL的 ...
- NAT and Traversal NAT(TURN/STUN/ICE)
http://www.cnblogs.com/whyandinside/archive/2010/12/08/1900492.html -------------------------------- ...
- 静态NAT、动态NAT、PAT(端口多路复用)的配置
静态NAT.动态NAT.PAT(端口多路复用)的配置 NAT的实现方式有三种,即静态转换Static Nat.动态转换Dynamic Nat 和 端口多路复用OverLoad. 静态转换 ( ...
- NAT原理与NAT穿越
最近在看东西的时候发现很多网络程序中都需要NAT穿越,特意在此总结一下. 先做一个约定: 内网A中有:A1(192.168.0.8).A2(192.168.0.9)两用户 网关X1(一个NAT设备)有 ...
- NAT与FULL NAT的区别
LVS 当前应用主要采用 DR 和 NAT 模式,但这 2 种模式要求 RealServer 和 LVS在同一个 vlan中,导致部署成本过高:TUNNEL 模式虽然可以跨 vlan,但RealSer ...
随机推荐
- ZOJ2540 Form a Square
Form a Square 题意就是 判断 给你四个点,能否组成一个正方形 要点: 格式很重要, 很重要!!! 数据很小,直接暴力 四个点判断是否为正方形,只需将所有可能的边长度算出来,然后选其中最短 ...
- UI基础:UIView(window,frame,UIColor,CGPoint,alpha,CGRect等) 分类: iOS学习-UI 2015-06-30 20:01 119人阅读 评论(0) 收藏
UIView 视图类,视图都是UIView或者UIView子类 UIWindow 窗口类,用于展示视图,视图一定要添加window才能显示 注意:一般来说,一个应用只有一个window 创建一个UIW ...
- OC基础:数组.字典.集 分类: ios学习 OC 2015-06-18 18:58 47人阅读 评论(0) 收藏
==============NSArray(不可变数组)=========== NSArray,继承自NSObject 用来管理(储存)一些有序的对象,不可变数组. 创建一个空数组 NSArray ...
- 【c++基础】vector中按照Point类型某一个变量进行排序
code // sort(a.begin(), a.end(), cmpy); //subfunction bool cmpy(cv::Point const& a, cv::Point co ...
- centos重启redis后,数据丢失
编辑/etc/sysctl.conf ,改vm.overcommit_memory=1, 然后sysctl -p 使配置文件生效 T
- freemarker在js中的应用
<script type="text/javascript"> //freemarker在js中的应用: var newOrganizations = []; < ...
- pandas 里面对nan的判断
不要用math.isnan() pandas里专门有一个函数: age_null = pd.isnull(titanic_survival[‘age’])
- Linux设备树
一.设备树编译 1.编译设备树:cd linux-x.xx & make dtbs,生成的dtb在目录linux-x.xx/arch/xxx/boot/dts下 2.反编译dtb,生成dts: ...
- ballerina 学习 三十二 编写安全的程序
ballerina编译器已经集成了部分安全检测,在编译时可以帮助我们生成错误提示,同时ballerina 标准库 已经对于常见漏洞高发的地方做了很好的处理,当我们编写了有安全隐患的代码,编译器就已 ...
- streamsets 3.5 的一些新功能
streamsets 3.5 有了一些新的特性以及增强,总之是越来越方便了,详细的可以 查看官方说明,以下简单例举一些比较有意义的. origins 新的pulsar 消费origin jdbc 多表 ...
