B - Image Perimeters
Technicians in a pathology lab analyze digitized images of slides. Objects on a slide are selected for analysis by a mouse click on the object. The perimeter of the boundary of an object is one useful measure. Your task is to determine this perimeter for selected objects.
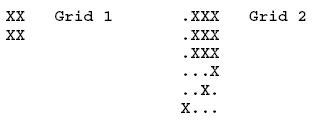
The digitized slides will be represented by a rectangular grid of periods, '.', indicating empty space, and the capital letter 'X', indicating part of an object. Simple examples are
An X in a grid square indicates that the entire grid square, including its boundaries, lies in some object. The X in the center of the grid below is adjacent to the X in any of the 8 positions around it. The grid squares for any two adjacent X's overlap on an edge or corner, so they are connected.
XXX
XXX Central X and adjacent X's
XXX
An object consists of the grid squares of all X's that can be linked to one another through a sequence of adjacent X's. In Grid 1, the whole grid is filled by one object. In Grid 2 there are two objects. One object contains only the lower left grid square. The remaining X's belong to the other object.
The technician will always click on an X, selecting the object containing that X. The coordinates of the click are recorded. Rows and columns are numbered starting from 1 in the upper left hand corner. The technician could select the object in Grid 1 by clicking on row 2 and column 2. The larger object in Grid 2 could be selected by clicking on row 2, column 3. The click could not be on row 4, column 3.
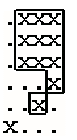
One useful statistic is the perimeter of the object. Assume each X corresponds to a square one unit on each side. Hence the object in Grid 1 has perimeter 8 (2 on each of four sides). The perimeter for the larger object in Grid 2 is illustrated in the figure at the left. The length is 18.
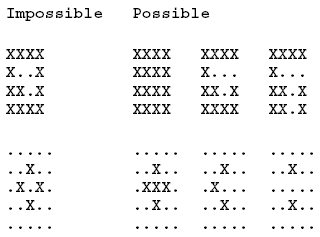
Objects will not contain any totally enclosed holes, so the leftmost grid patterns shown below could NOT appear. The variations on the right could appear:
The input will contain one or more grids. Each grid is preceded by a line containing the number of rows and columns in the grid and the row and column of the mouse click. All numbers are in the range 1-20. The rows of the grid follow, starting on the next line, consisting of '.' and 'X' characters.
The end of the input is indicated by a line containing four zeros. The numbers on any one line are separated by blanks. The grid rows contain no blanks.
For each grid in the input, the output contains a single line with the perimeter of the specified object.
Example input:
2 2 2 2
XX
XX
6 4 2 3
.XXX
.XXX
.XXX
...X
..X.
X...
5 6 1 3
.XXXX.
X....X
..XX.X
.X...X
..XXX.
7 7 2 6
XXXXXXX
XX...XX
X..X..X
X..X...
X..X..X
X.....X
XXXXXXX
7 7 4 4
XXXXXXX
XX...XX
X..X..X
X..X...
X..X..X
X.....X
XXXXXXX
0 0 0 0
Example output:
8
18
40
48
8
垃圾poj,ascall都不能正确输出,这题是求周长的,八个方向都搜一遍就好了,搜完改变自身的值
#include<iostream>
#include<stdio.h>
#include<stdlib.h>
#include <iomanip>
#include<cmath>
#include<float.h>
#include<string.h>
#include<algorithm>
#define sf scanf
#define pf printf
#define pb push_back
#define mm(x,b) memset((x),(b),sizeof(x))
#include<vector>
#include<map>
#define rep(i,a,n) for (int i=a;i<n;i++)
#define per(i,a,n) for (int i=a;i>=n;i--)
typedef long long ll;
typedef long double ld;
typedef double db;
const ll mod=1e12+100;
const db e=exp(1);
using namespace std;
const double pi=acos(-1.0);
char a[25][25];
int sum;
void dfs(int x,int y)
{
// cout<<x<<" "<<y<<endl;
a[x][y]='a';//把经过的位置改变
if(a[x+1][y]=='.')
sum++;
if(a[x-1][y]=='.')
sum++;
if(a[x][y+1]=='.')
sum++;
if(a[x][y-1]=='.')
sum++;
if(a[x-1][y-1]=='X')//左上
dfs(x-1,y-1);
if(a[x-1][y+1]=='X')//右上
dfs(x-1,y+1);
if(a[x+1][y-1]=='X')//左下
dfs(x+1,y-1);
if(a[x+1][y+1]=='X')//右下
dfs(x+1,y+1);
if(a[x-1][y]=='X')//上
dfs(x-1,y);
if(a[x][y-1]=='X')//左
dfs(x,y-1);
if(a[x][y+1]=='X')//右
dfs(x,y+1);
if(a[x+1][y]=='X')//下
dfs(x+1,y);
}
int main()
{
int n,m,x,y;
while(1)
{
sum=0;
char d[25][25];
sf("%d%d%d%d",&n,&m,&x,&y);
if(!n&&!m) return 0;
mm(a,'.');
rep(i,1,n+1)
{
sf("%s",&a[i][1]);
//pf("1%s\n",&d[i]);
a[i][m+1]='.';
}
dfs(x,y);
pf("%d\n",sum);
}
}
B - Image Perimeters的更多相关文章
- ZOJ 1047 Image Perimeters
原题链接 题目大意:鼠标点击一块,求与之联通的所有区域的边长之和. 解法:广度优先搜索.从选中的这个点开始,往周围8个点依次搜索,访问过的点做上标记.如果该点上下左右的一个或多个方向没有相邻的点,边长 ...
- 深搜(DFS),Image Perimeters
题目链接:http://poj.org/problem?id=1111 解题报告: 1.这里深搜有一点要注意,对角线上的点,如果为'.',则total不应该增加,因为这不是他的边长. #include ...
- POJ1111 Image Perimeters
Time Limit: 1000MS Memory Limit: 10000K Total Submissions: 8790 Accepted: 5260 Description Techn ...
- [POJ]1111 Image Perimeters
Description Technicians in a pathology lab analyze digitized images of slides. Objects on a slide ar ...
- poj1111 Image Perimeters 广搜
题目大意: 输入一个矩阵,再输入其中一个“X”的位置(从1开始).从该位置向八个方向扩展,如果是“X”就可以并在一起.问最后得到的模块的周长是多少. 解题思路: 按照广搜的思路来做.用一个二维的数组标 ...
- Image Perimeters
Description 给出一张由"x"和"."组成的矩阵.每个"x"可以向上下左右及两个斜对角进行连通,请问由某个点开始的"x& ...
- Project Euler 94:Almost equilateral triangles 几乎等边的三角形
Almost equilateral triangles It is easily proved that no equilateral triangle exists with integral l ...
- POJ题目细究
acm之pku题目分类 对ACM有兴趣的同学们可以看看 DP: 1011 NTA 简单题 1013 Great Equipment 简单题 102 ...
- HOJ题目分类
各种杂题,水题,模拟,包括简单数论. 1001 A+B 1002 A+B+C 1009 Fat Cat 1010 The Angle 1011 Unix ls 1012 Decoding Task 1 ...
随机推荐
- 1.2 Stream API
引例: List<String> strList = Arrays.asList("zhaojigang","nana","tianya& ...
- 17、python对内存的使用
python对内存的使用 浅拷贝和深拷贝 所谓浅拷贝就是对引用的拷贝(只拷贝父对象) 所谓深拷贝就是对对象的资源的拷贝 解释一个例子: import copy a = [1,2,3,['a','b', ...
- Nginx配置静态资源
静态服务器 静态服务器概念非常简单:当用户请求静态资源时,把文件内容回复给用户. 但是,要把静态服务做到极致,需要考虑的方面非常多: 正确书写header:设置content-type.过期时间等 效 ...
- 解决zabbix的中文乱码
CentOS7.1 x64上下载了zabbix官方的rpm包,导入后使用yum安装了zabbix 3.2.6,但是启动zabbix server的时候报了个段错误的错,谷歌了一会儿,发现段错误不止一次 ...
- c链表之oc AutoReleasePool
直接贴 原文吧: http://blog.sunnyxx.com/2014/10/15/behind-autorelease/
- [k8s]docker calico网络&docker cluster-store
docker cluster-store选项 etcd-calico(bgp)实现docker夸主机通信 配置calico网络 - 启动etcd etcd --listen-client-urls h ...
- 【Tomcat】Tomcat 系统架构与设计模式,第 1 部分: 工作原理
这个分为两个部分的系列文章将研究 Apache Tomcat 的系统架构以及其运用的很多经典设计模式.本文是第 1 部分,将主要从 Tomcat 如何分发请求.如何处理多用户同时请求,还有它的多级容器 ...
- Spring-boot(二)yml文件的使用
上一章创建了一个简单的springboot项目,配置可以说非常的简单. 不过,在实际开发中不可能都用默认的配置,还是需要根据自己的实际项目需求有自定义的配置的. 比如:端口号需要变更,模板引擎的缓存开 ...
- 【iCore4 双核心板_ARM】例程十五:USB_CDC实验——高速数据传输
实验方法: 1.安装USB CDC驱动,驱动安装方法参考例程包中安装方法文档. 2.将跳线冒跳至USB_OTG,通过Micro USB 线将iCore4 USB-OTG接口与电脑相连. 3.打开上位机 ...
- 【GMT43智能液晶模块】例程一:ARM驱动LED
实验原理: 通过STM32的一个GPIO驱动一个红色LED,GPIO为推挽输出模式,采用灌电流 方式与LED连接,基于STemWin人机界面通过按钮控制GPIO高.低电平输出,从而 控制LED亮灭. ...
