Openssl s_server命令
一、简介
s_server是openssl提供的一个SSL服务程序。使用此程序前,需要生成各种证书。本命令可以用来测试ssl客户端,比如各种浏览器的https协议支持
二、语法
openssl s_server [-accept port] [-context id] [-verify depth] [-Verify depth] [-crl_check] [-crl_check_all] [-cert filename] [-certform DER|PEM] [-key filename] [-keyform DER|PEM] [-pass arg] [-dcert filename] [-dcertform DER|PEM ] [-dkey keyfile] [-dkeyform DER|PEM ] [-dpass arg] [-dhparam filename] [-name_curve arg][-nbio] [-nbio_test] [-crlf] [-debug] [-msg] [-state] [-CApath directory] [-CAfile filename] [-nocert] [-cipher cipherlist] [-quiet] [-no_tmp_rsa] [-ssl2] [-ssl3] [-tls1_1] [-tls1_2] [-tls1] [-dtls1] [-timeout] [-mtu] [-chain] [-no_ssl2][-no_ssl3] [-no_tls1] [-no_tls1_1] [-no_tls1_2] [-no_dhe] [-no_ecdhe][-bugs] [-hack] [-www] [-WWW] [-HTTP][-engine id] [-tlsextdebug] [-no_ticket] [-id_prefix arg] [-rand file(s)]
选项
-accept arg - port to accept on (default is )
-context arg - set session ID context
-verify arg - turn on peer certificate verification
-Verify arg - turn on peer certificate verification, must have a cert.
-cert arg - certificate file to use
(default is server.pem)
-crl_check - check the peer certificate has not been revoked by its CA.
The CRL(s) are appended to the certificate file
-crl_check_all - check the peer certificate has not been revoked by its CA
or any other CRL in the CA chain. CRL(s) are appened to the
the certificate file.
-certform arg - certificate format (PEM or DER) PEM default
-key arg - Private Key file to use, in cert file if
not specified (default is server.pem)
-keyform arg - key format (PEM, DER or ENGINE) PEM default
-pass arg - private key file pass phrase source
-dcert arg - second certificate file to use (usually for DSA)
-dcertform x - second certificate format (PEM or DER) PEM default
-dkey arg - second private key file to use (usually for DSA)
-dkeyform arg - second key format (PEM, DER or ENGINE) PEM default
-dpass arg - second private key file pass phrase source
-dhparam arg - DH parameter file to use, in cert file if not specified
or a default set of parameters is used
-named_curve arg - Elliptic curve name to use for ephemeral ECDH keys.
Use "openssl ecparam -list_curves" for all names
(default is nistp256).
-nbio - Run with non-blocking IO
-nbio_test - test with the non-blocking test bio
-crlf - convert LF from terminal into CRLF
-debug - Print more output
-msg - Show protocol messages
-state - Print the SSL states
-CApath arg - PEM format directory of CA's
-CAfile arg - PEM format file of CA's
-trusted_first - Use trusted CA's first when building the trust chain
-nocert - Don't use any certificates (Anon-DH)
-cipher arg - play with 'openssl ciphers' to see what goes here
-serverpref - Use server's cipher preferences
-quiet - No server output
-no_tmp_rsa - Do not generate a tmp RSA key
-psk_hint arg - PSK identity hint to use
-psk arg - PSK in hex (without 0x)
-ssl2 - Just talk SSLv2
-ssl3 - Just talk SSLv3
-tls1_2 - Just talk TLSv1.
-tls1_1 - Just talk TLSv1.
-tls1 - Just talk TLSv1
-dtls1 - Just talk DTLSv1
-timeout - Enable timeouts
-mtu - Set link layer MTU
-chain - Read a certificate chain
-no_ssl2 - Just disable SSLv2
-no_ssl3 - Just disable SSLv3
-no_tls1 - Just disable TLSv1
-no_tls1_1 - Just disable TLSv1.
-no_tls1_2 - Just disable TLSv1.
-no_dhe - Disable ephemeral DH
-no_ecdhe - Disable ephemeral ECDH
-bugs - Turn on SSL bug compatibility
-www - Respond to a 'GET /' with a status page
-WWW - Respond to a 'GET /<path> HTTP/1.0' with file ./<path>
-HTTP - Respond to a 'GET /<path> HTTP/1.0' with file ./<path>
with the assumption it contains a complete HTTP response.
-engine id - Initialise and use the specified engine
-id_prefix arg - Generate SSL/TLS session IDs prefixed by 'arg'
-rand file:file:...
-servername host - servername for HostName TLS extension
-servername_fatal - on mismatch send fatal alert (default warning alert)
-cert2 arg - certificate file to use for servername
(default is server2.pem)
-key2 arg - Private Key file to use for servername, in cert file if
not specified (default is server2.pem)
-tlsextdebug - hex dump of all TLS extensions received
-no_ticket - disable use of RFC4507bis session tickets
-legacy_renegotiation - enable use of legacy renegotiation (dangerous)
-nextprotoneg arg - set the advertised protocols for the NPN extension (comma-separated list)
-use_srtp profiles - Offer SRTP key management with a colon-separated profile list
-keymatexport label - Export keying material using label
-keymatexportlen len - Export len bytes of keying material (default )
三、实例
1、启动s_server服务(站点证书及私钥,证书链,协议版本,算法组合)
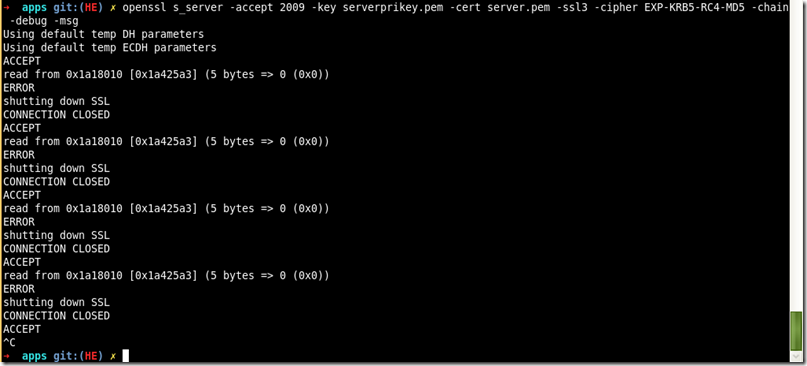
openssl s_server -accept 2009 -key serverprikey.pem -cert server.pem -ssl3 -cipher EXP-KRB5-RC4-MD5 -chain -debug -msg
参考:http://blog.csdn.net/as3luyuan123/article/details/16850727 http://www.tuicool.com/articles/6ny6Fv
Openssl s_server命令的更多相关文章
- OpenSSL s_server / s_client 应用实例
netkiller openssl tls 目录[-] 12.6. s_server / s_client 12.6.1. SSL POP3 / SMTP / IMAP 12.6.2. server ...
- openssl常用命令行汇总
openssl常用命令行汇总 随机数 openssl rand -out rand.dat -base64 32 摘要 直接做摘要 openssl dgst -sha1 -out dgst.dat p ...
- (转)openssl 命令: openssl req 命令详解
openssl req命令主要的功能有,生成证书请求文件, 查看验证证书请求文件,还有就是生成自签名证书.本文就主要记录一下open ...
- Openssl asn1parse命令
一.简介 asn1parse命令是一种用来诊断ASN.1结构的工具,也能用于从ASN1.1数据中提取数据 二.语法 openssl asn1parse [-inform PEM|DER] [-in f ...
- Openssl pkcs7命令
一.简介 pkcs7命令用于处理DER或者PEM格式的pkcs#7文件. 二.语法 openssl pkcs7 [-inform PEM|DER] [-outform PEM|DER] [-in ...
- Openssl crl2pkcs7命令
一.简介 crl2pkcs命令用来根据CRL或证书来生成pkcs#7消息. 二.语法 openssl crl2pkcs7 [-inform PEM|DER ] [-outform PEM|DER ...
- Openssl verify命令
一.简介 verify命令对证书的有效性进行验证,verify 指令会沿着证书链一直向上验证,直到一个自签名的CA 二.语法 openssl verify [-CApath directory] [- ...
- Openssl rsa命令
一.简介 Rsa命令用于处理RSA密钥.格式转换和打印信息 二.语法 openssl rsa [-inform PEM|NET|DER] [-outform PEM|NET|DER] [-in fil ...
- Openssl pkeyutl命令
一.简介 pkeyutl命令能够测试所支持的密钥算法的性能 二.语法 openssl rsautl [-in file] [-out file] [-sigfile file] [-inkey fil ...
随机推荐
- 【转】redis GEO地理位置
redis目前已经到了3.2版本,3.2版本里面新增的一个功能就是对GEO(地理位置)的支持. 地理位置大概提供了6个命令,分别为: GEOADD GEODIST GEOHASH GEOPOS GEO ...
- 微信卡券领取页面提示签名错误,微信卡券JSAPI签名校验工具对比签名一模一样,cardExt扩展字段有问题
一.领券页面错误 二.给到前端的数据 三.根据给前端的额数据做签名校验 四.给前端的签名和校验的签名一致(这一步能判断签名没有问题,基本可以判断是前端调用微信接口时拼接的数据有问题) 五.以下是微信的 ...
- golang回调函数的例子
package main import "fmt" type TestStruct struct { } func (object *TestStruct) test(msg st ...
- 干货:这也许是最全面透彻的一篇RabbitMQ指南!
本文大纲: RabbitMQ 历史 RabbitMQ 应用场景 RabbitMQ 系统架构 RabbitMQ 基本概念 RabbitMQ 细节阐明 历史-从开始到现在 RabbitMQ是一个Erlan ...
- free 命令结果完全剖析
free 命令结果完全剖析 total 总物理内存大小. used 已分配的大小,注意,对操作系统来说任何被使用的内存都是used. free 未被分配的物理内存大小. shared 共享内存大小,主 ...
- java之IO整理(下)
一:对象的序列化 对象序列化就是把一个对象变为二进制数据流的一种方法. 一个类要想被序列化,就行必须实现java.io.Serializable接口.虽然这个接口中没有任何方法,就如同之前的clone ...
- python 之 functools模块
functools模块用于高阶函数:作用于或返回其他函数的函数.一般而言,任何可调用对象都可以作为本模块用途的函数来处理. 官方文档已经有了详尽的介绍,这里就不在复述,详情请见:官方文档 .这里主要介 ...
- IDA Pro 权威指南学习笔记(八) - 基本 IDA 导航
导航目标 在分析阶段,IDA 会通过检查二进制文件的符号表生成符号名称,或根据二进制文件引用位置的方式自动生成一个名称 反汇编窗口中显示的任何名称都是导航目标 双击任何一个符号,IDA 将跳转到相应的 ...
- vs2010 安装 Ajax Control Toolkit
Ajax Control Toolkit 7.1005.0 The Ajax Control Toolkit contains a rich set of controls that you can ...
- Tomcat实践
1.1Java环境介绍 jdk java 开发工具包 jre sdk J2EE 企业版 J2SE 标准版 J2ME 手机开发 1.2Tomcat自动部署 通过saltstack来批量安装tomcat ...
