Lab 11-3
Analyze the malware found in Lab11-03.exe and Lab11-03.dll. Make sure that both files are in the same directory during analysis.
Questions and Short Answers
What interesting analysis leads can you discover using basic static analysis?
A: Lab11-03.exe contains the strings
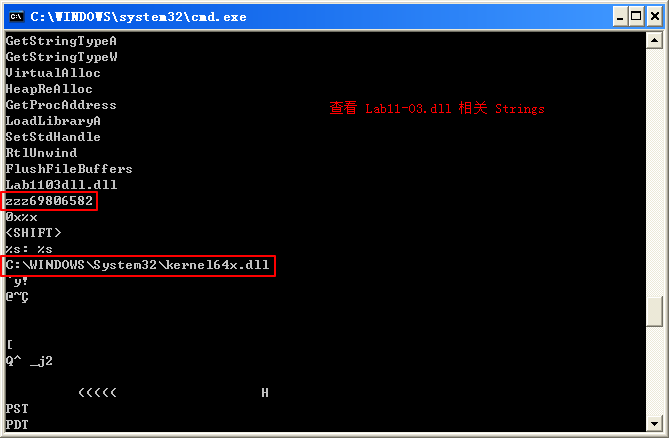
inet_epar32.dllandnet start cisvc, which means that it probably starts the CiSvc indexing service. Lab11-03.dll contains the stringC:\WINDOWS\System32\kernel64x.dlland imports the API callsGetAsyncKeyStateandGetForegroundWindow, which makes us suspect it is a keylogger that logs to kernel64x.dll.What happens when you run this malware?
A: The malware starts by copying Lab11-03.dll to
inet_epar32.dllin the Windows system directory. The malware writes data to cisvc.exe and starts the indexing service. The malware also appears to write keystrokes to C:\Windows System32 kernel64x.dll.How does Lab11-03.exe persistently install Lab11-03.dll ?
A: The malware persistently installs Lab11-03.dll by trojanizing the indexing service by entry-point redirection. It redirects the entry point to run shellcode, which loads the DLL.
Which Windows system file does the malware infect?
A: The malware infects cisvc.exe to load inet_epar32.dll and call its export
zzz69806582.What does Lab11-03.dll do?
A: Lab11-03.dll is a polling keylogger implemented in its export
zzz69806582.Where does the malware store the data it collects?
A: The malware stores keystrokes and the window into which keystrokes were entered to C:\Windows\System32\kernel64x.dll.
Detailed Analysis
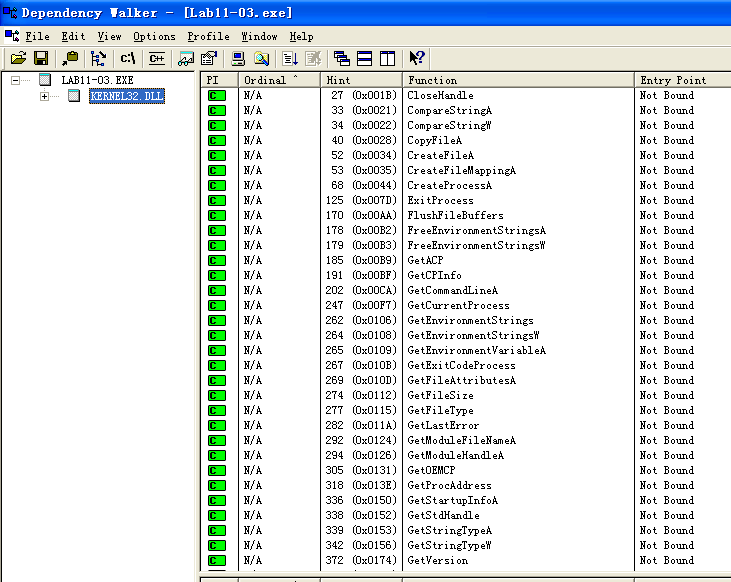
We’ll begin our analysis by examining the strings and imports for Lab11-03.exe and Lab11-03.dll. Lab11-03.exe contains the strings inet_epar32.dll and net start cisvc. The net start command is used to start a service on a Windows machine, but we don’t yet know why the malware would be starting the indexing service on the system, so we’ll dig down during in-depth analysis.
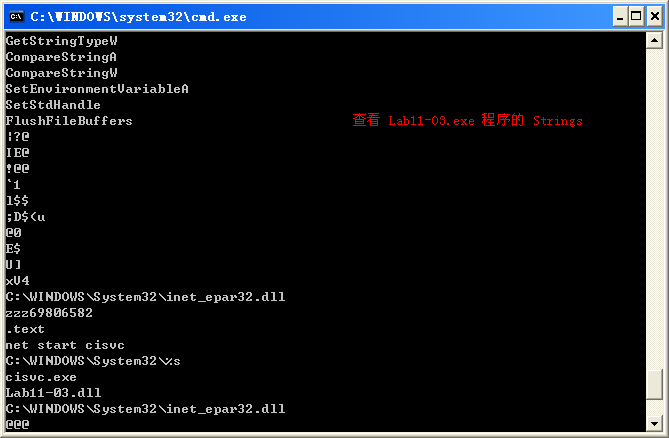
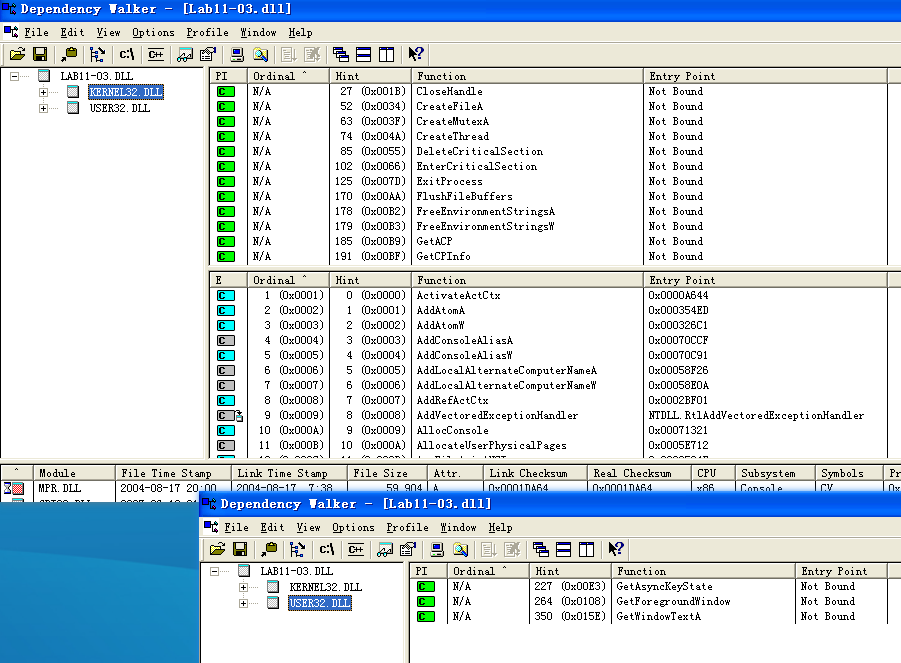
Lab11-03.dll contains the string C:\WINDOWS\System32\kernel64x.dll and imports the API calls GetAsyncKeyState and GetForegroundWindow, which makes us suspect it is a keylogger that logs keystrokes to kernel64x.dll. The DLL also contains an oddly named export: zzz69806582.
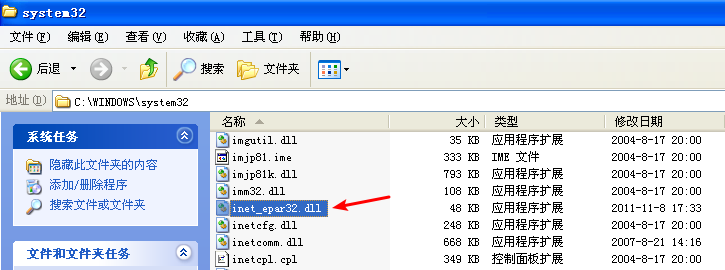
Next, we use dynamic analysis techniques to see what the malware does at runtime. We set up procmon and filter on Lab11-03.exe to see the malware create C:\Windows\System32\inet_epar32.dll. The DLL inet_epar32.dll is identical to Lab11-03.dll, which tells us that the malware copies Lab11-03.dll to the Windows system directory.

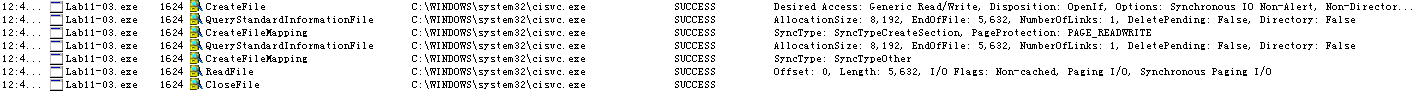
Further in the procmon output, we see the malware open a handle to cisvc.exe, but we don’t see any WriteFile operations.
Finally, the malware starts the indexing service by issuing the command net start cisvc. Using Process Explorer, we see that cisvc.exe is now running on the system. Since we suspect that the malware might be logging keystrokes, we open notepad.exe and enter a bunch of a characters. We see that kernel64x.dll is created. Suspecting that keystrokes are logged, we open kernel64x.dll in a hex editor and see the following output:

Our keystrokes have been logged to kernel64x.dll. We also see that the program in which we typed our keystrokes (Notepad) has been logged along with the keystroke data in hexadecimal. (The malware doesn’t turn the hexadecimal values into readable strings, so the malware author probably has a postprocessing script to more easily read what is entered.)
Next, we use in-depth techniques to determine why the malware is starting a service and how the keylogger is gaining execution. We begin by loading Lab11-03.exe into IDA Pro and examining the main function, as shown in Listing 11-17L.
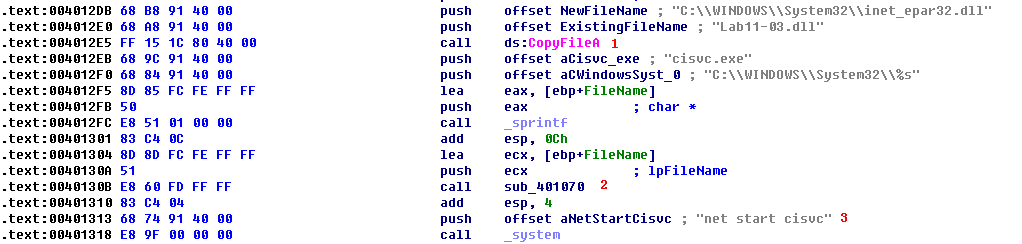
Listing 11-17L: Reviewing the main method of Lab11-03.exe
At \({\color{red}1}\), we see that the main method begins by copying Lab11-03.dll to inet_epar32.dll in C:\Windows\System32. Next, it builds the string C:\WINDOWS System32\cisvc.exe and passes it to sub_401070 at \({\color{red}2}\). Finally, the malware starts the indexing service by using system to run the command net start cisvc at \({\color{red}3}\).
We focus on sub_401070 to see what it might be doing with cisvc.exe. There is a lot of confusing code in sub_401070, so take a high-level look at this function using the cross-reference diagram shown in Figure 11-6L.
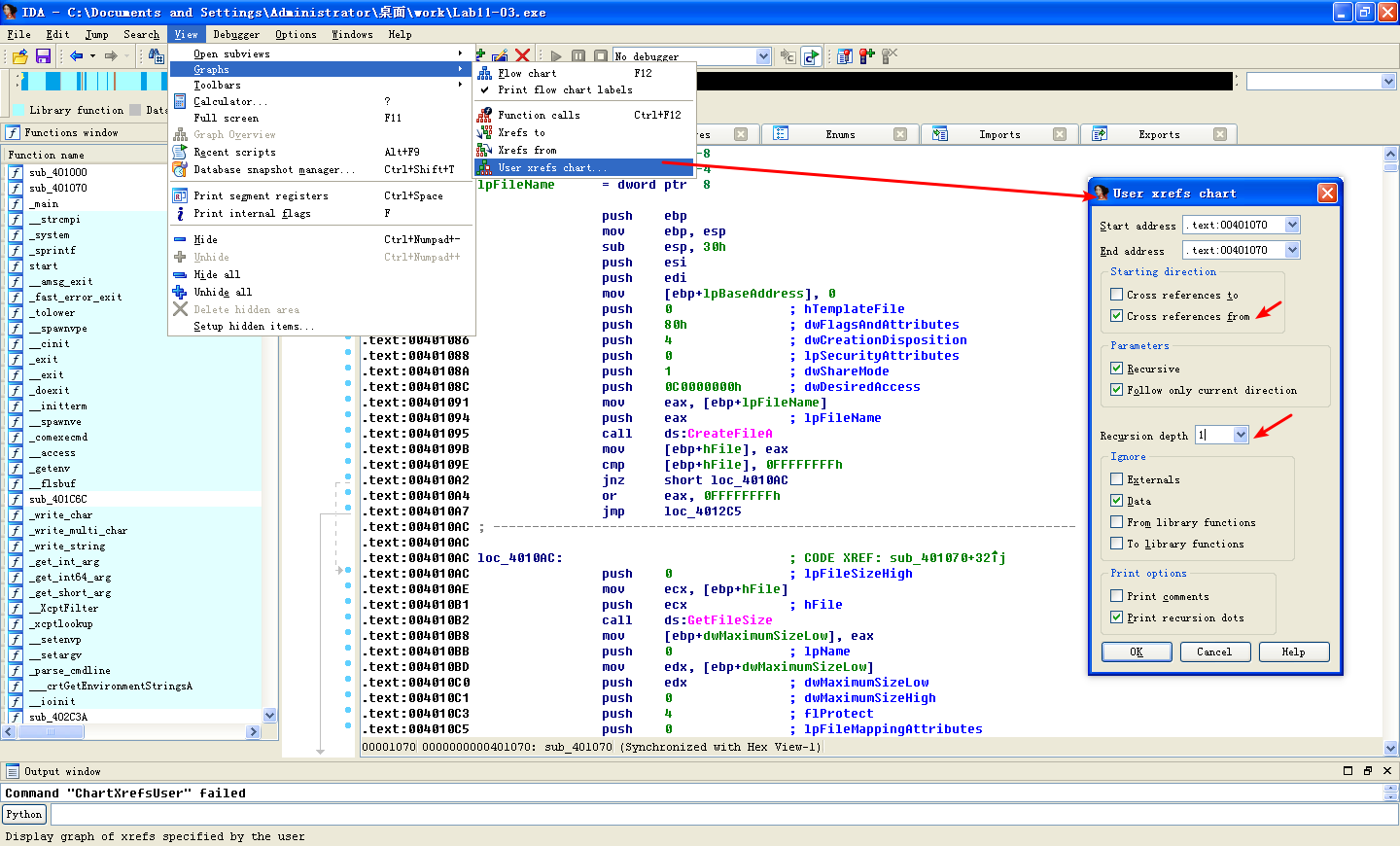
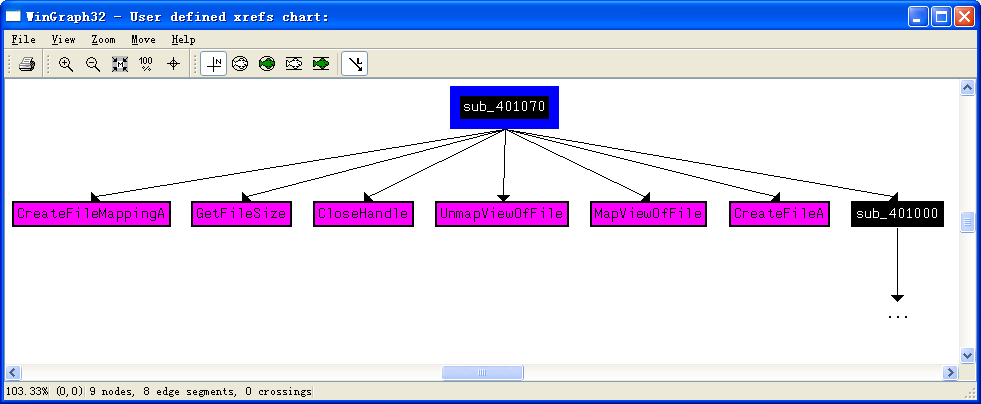
Figure 11-6L: Cross-reference graph for sub_401070
Using this diagram, we see that sub_401070 maps the cisvc.exe file into memory in order to manipulate it with calls to CreateFileA, CreateFileMappingA, and MapViewOfFile. All of these functions open the file for read and write access. The starting address of the memory-mapped view returned by MapViewOfFile (labeled lpBaseAddress by IDA Pro) is both read and written to. Any changes made to this file will be written to disk after the call to UnmapViewOfFile, which explains why we didn’t see a WriteFile function in the procmon output.
Several calculations and checks appear to be made on the PE header of cisvc.exe. Rather than analyze these complex manipulations, let’s focus on the data written to the file, and then extract the version of cisvc.exe written to disk for analysis.
A buffer is written to the memory-mapped file, as shown in Listing 11-18L.
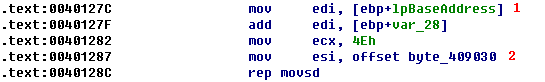
Listing 11-18L: Writing 312 bytes of shellcode into cisvc.exe
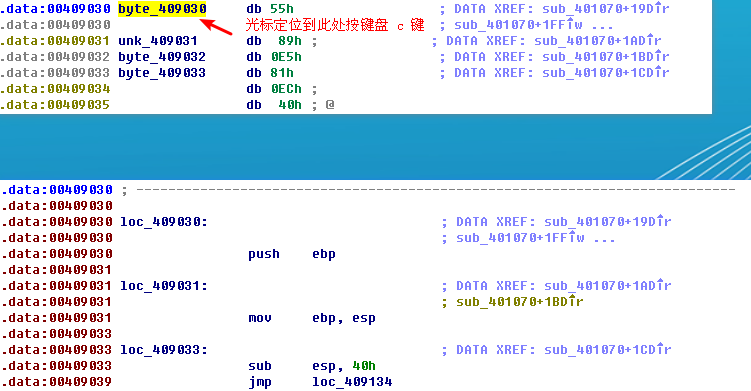
At \({\color{red}1}\), the mapped location of the file is moved into EDI and adjusted by some offset using var_28. Next, ECX is loaded with 0x4E, the number of DWORDs to write (movsd). Therefore, the total number of bytes is 0x4E * 4 = 312 bytes in decimal. Finally, byte_409030 is moved into ESI at \({\color{red}2}\), and rep movsd copies the data at byte_409030 into the mapped file. We examine the data at 0x409030 and see the bytes in the left side of Table 11-1L.
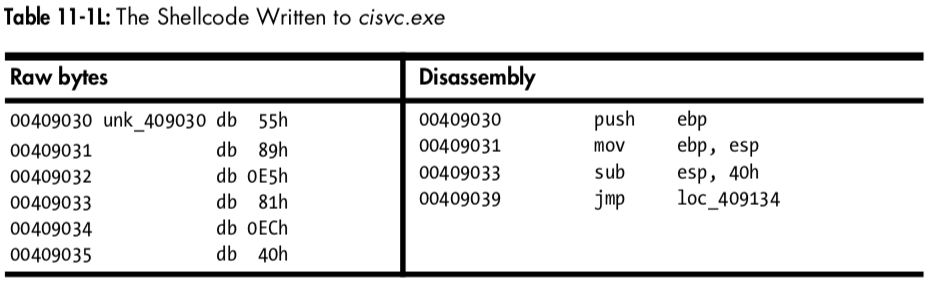
The left side of the table contains raw bytes, but if we put the cursor at 0x409030 and press C in IDA Pro, we get the disassembly shown in the right side of the table. This is shellcode—handcrafted assembly that, in this case, is used for process injection. Rather than analyze the shellcode (doing so can be a bit complicated and messy), we’ll guess at what it does based on the strings it contains.
Toward the end of the 312 bytes of shellcode, we see two strings:
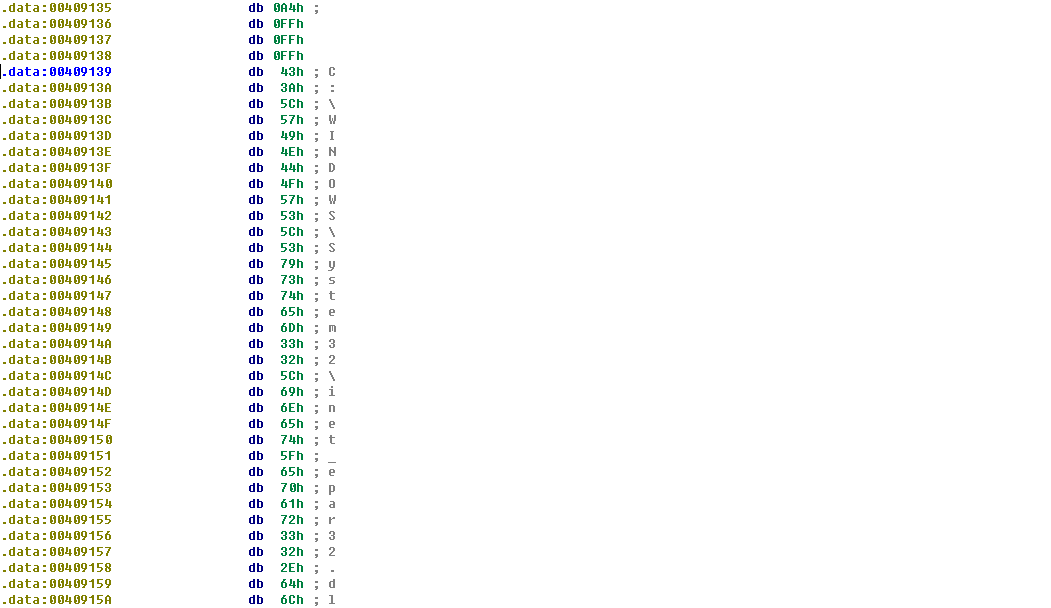
The appearance of the path to inet_epar32.dll and the export zzz69806582 suggest that this shellcode loads the DLL and calls its export.
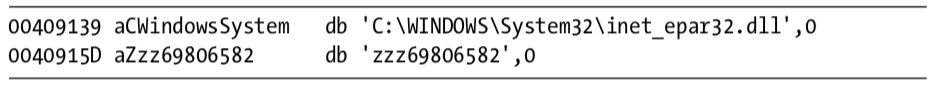
Next, we compare the cisvc.exe binary as it exists after we run the malware to a clean version that existed before the malware was run. (Most hex editors provide a comparison tool.) Comparing the versions, we see two differences: the insertion of 312 bytes of shellcode and only a 2-byte change in the PE header. We load both of these binaries into PEview to see if we notice a difference in the PE header. This comparison is shown in Figure 11-7L.
The top part of Figure 11-7L shows the original cisvc.exe (named cisvc_original.exe) loaded into PEview, and the bottom part shows the trojanized cisvc.exe. At \({\color{red}1}\) and \({\color{red}2}\), we see that the entry point differs in the two binaries. If we load both binaries into IDA Pro, we see that the malware has performed entry-point redirection so that the shellcode runs before the original entry point any time that cisvc.exe is launched. Listing 11-19L shows a snippet of the shellcode in the trojanized version of cisvc.exe.
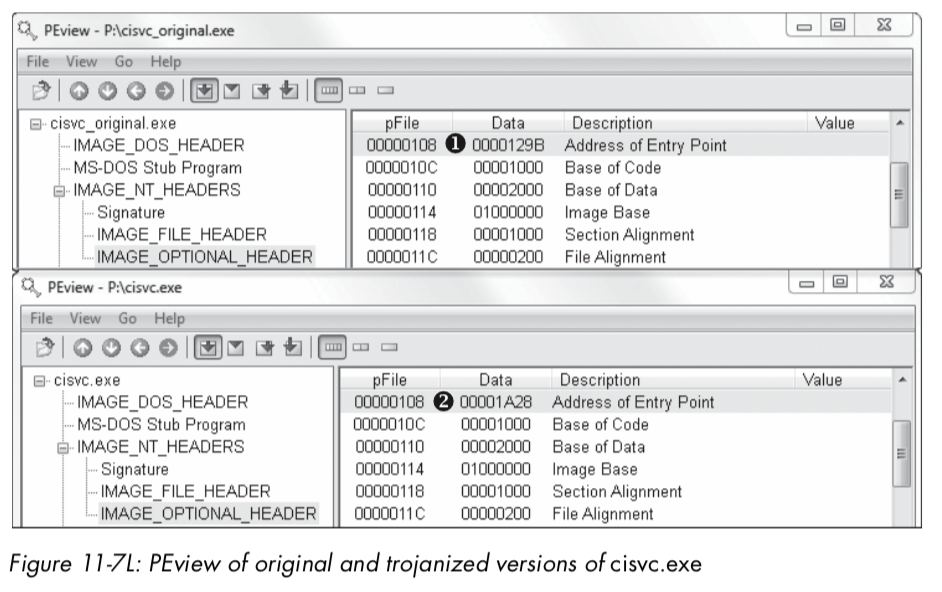
Listing 11-19L: Important calls within the shellcode inside the trojanized cisvc.exe
Now we load the trojanized version of cisvc.exe into a debugger and set
a breakpoint at 0x1001B0A. We find that at \({\color{red}1}\), the malware calls LoadLibrary to load inet_epar32.dll into memory. At \({\color{red}2}\), the malware calls GetProcAddress with the argument zzz69806582 to get the address of the exported function. At \({\color{red}3}\), the malware calls zzz69806582. Finally, the malware jumps to the original entry point at \({\color{red}4}\), so that the service can run as it would normally. The shellcode’s function matches our earlier suspicion that it loads inet_epar32.dll and calls its export.
Keylogger Analysis
Next, we analyze inet_epar32.dll, which is the same as Lab11-03.dll. We load Lab11-03.dll into IDA Pro and begin to analyze the file. The majority of the code stems from the zzz69806582 export. This export starts a thread and returns, so we will focus on analyzing the thread, as shown in Listing 11-20L.
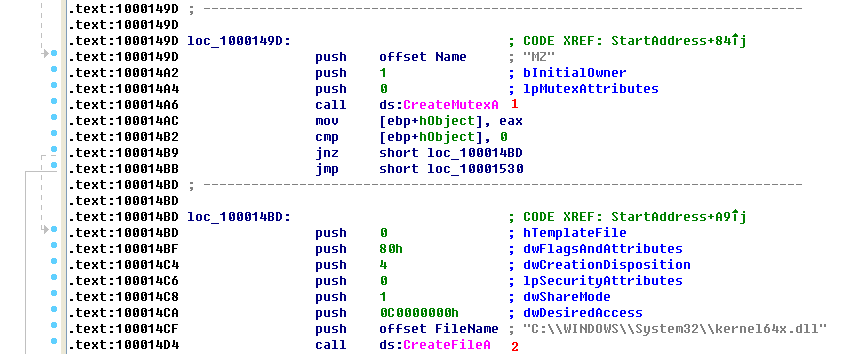
Listing 11-20L: Mutex and file creation performed by the thread created by zzz69806582
At \({\color{red}1}\), the malware creates a mutex named MZ. This mutex prevents the malware from running more than one instance of itself, since a previous call to OpenMutex (not shown) will terminate the thread if the mutex MZ already exists. Next, at \({\color{red}2}\), the malware opens or creates a file named kernel64x.dll for writing.
After getting a handle to kernel64x.dll, the malware sets the file pointer to the end of the file and calls sub_10001380, which contains a loop. This loop contains calls to GetAsyncKeyState, GetForegroundWindow, and WriteFile. This is consistent with the keylogging method we discussed in “User-Space Keyloggers” on page 239.
Summary
Lab11-03.exe trojanizes and then starts the Windows indexing service (cisvc.exe). The trojan shellcode loads a DLL and calls an exported function that launches a keylogger. The export creates the mutex MZ and logs all keystrokes to kernel64x.dll in the Windows system directory.
注:在做本实验的过程中,我选用的 Windows XP SP3 机器,并没有在相应目录下修改 CISVC.exe 文件,所以和这部分相关的,没有实现。
Preference
PRACTICAL MALWARE ANALYSIS: MALWARE BEHAVIOR(LAB 11-03)
Lab 11-3的更多相关文章
- RH033读书笔记(10)-Lab 11 Process Control
Lab 11 Process Control Sequence 1: Job Control 1. [student@stationX ~]$ su - 2. Begin some jobs in t ...
- RH133读书笔记(11)-Lab 11 System Rescue and Troubleshooting
Lab 11 System Rescue and Troubleshooting Goal: To build skills in system rescue procedures. Estimate ...
- Lab 1-1
LABS The purpose of the labs is to give you an opportunity to practice the skills taught in the chap ...
- 第一章 Lab
关于Lab 教材恶意代码分析实战 课后练习恶意代码样本https://practicalmalwareanalysis.com或https://nostarch.com/malware.htm 以下是 ...
- 7 天玩转 ASP.NET MVC — 第 3 天
目录 第 1 天 第 2 天 第 3 天 第 4 天 第 5 天 第 6 天 第 7 天 0. 前言 我们假定你在开始学习时已经阅读了前两天的学习内容.在第 2 天我们完成了关于显示 Employee ...
- RAC之常用方法-----新手入门
年后换工作新入职,公司开发在使用RAC,之前居然一直没有了解过,独立开发的弊端,信息闭塞,而且自己也懒,这几天看了下RAC,确实很强大有木有. 什么是ARC 简单的说,RAC就是一个第三方库,他可以大 ...
- vmware目录2
http://www.globalknowledge.com/training/course.asp?pageid=9&courseid=17880&country=United+St ...
- 很好的vmware目录
http://www.globalknowledge.com/training/course.asp?pageid=9&courseid=18023&country=United+St ...
- 【转】Automated Testing Detail Test Plan
Automated Testing Detail Test PlanAutomated Testing DTP Overview This Automated Testing Detail Test ...
- Cygwin Run in the Windows(Simulation of UNIX)
Preface Environment Cygwin Run in the Windows(Simulation of UNIX) Resource Cygwin Install:http://cyg ...
随机推荐
- HDU 1556 BIT区间修改+单点查询(fread读入优化)
BIT区间修改+单点查询 [题目链接]BIT区间修改+单点查询 &题解: BIT区间修改+单点查询和求和的bit是一模一样的(包括add,sum) 只不过是你使用函数的方式不一样: 使用区间的 ...
- C++中浮点数比较大小,即小数比较大小
浮点数比较大小,由于精度问题,所以直接比较有时可能会出错. 单精度数7位有效数字. (float)双精度数16位有效数字.(double) 单精度数的尾数用23位存储,加上默认的小数点前的1位1,2^ ...
- storm-sql-kafka问题情况
首先上官方文档:http://storm.apache.org/releases/1.2.2/storm-sql.html 解决的问题 1.kafka版本不对 开始测试时采用storm1.2.2+ka ...
- Oarcle之事务
update:更新 例如转账: update emp_ temp set sal = sal-500 where ename = 'JONES':(更新表中sal项 为sal-500 是当ename= ...
- 利用multiprocessing.managers开发跨进程生产者消费者模型
研究了下multiprocessing.managers,略有收获,随笔一篇: 核心思路是构造一个manager进程,这个进程可以通过unix socket或tcp socket与其它进程通信:因为利 ...
- java 接口详解
定义接口 接口继承和实现继承的规则不同,一个类只有一个直接父类,但可以实现多个接口.Java 接口本身没有任何实现,只描述 public 行为,因此 Java 接口比 Java 抽象类更抽象化.Jav ...
- bzoj4710 [Jsoi2011]分特产(容斥)
4710: [Jsoi2011]分特产 Time Limit: 10 Sec Memory Limit: 128 MBSubmit: 814 Solved: 527[Submit][Status] ...
- spring boot使用mongodb时,xxxRepository不能Autowired的问题
默认情况下,当继承MongoRepository的CRUD在@SpringBootApplication的子包下时,xxxRepository是能够自动被扫描和创建代理的.但是如果不在默认路径下,就无 ...
- MySQL主从复制虽好,能完美解决数据库单点问题吗?
一.单个数据库服务器的缺点 数据库服务器存在单点问题: 数据库服务器资源无法满足增长的读写请求: 高峰时数据库连接数经常超过上限. 二.如何解决单点问题 增加额外的数据库服务器,组建数据库集群: 同一 ...
- UI自动化(十四)yaml配置文件
import yamlimport jsonf = open('config.yaml','rb')data = yaml.load(f)print(json.dumps(data,indent=4) ...
