emSecure Use Digital Signatures to protect your products
emSecure Use Digital Signatures to protect your products
emSecure is an RSA based software solution to authenticate digital assets. It can be used to secure products at no per unit cost against hacking and cloning.
Features
- RSA - Dual keys, private and public make it 100% safe
- Hardware-independent, any CPU, no additional hardware needed
- High performance, small memory footprint
- Simple API, easy to integrate
- Applicable for new and existing products
- Complete package, key generator and tools included
- Drag-and-drop Sign And Verify application included
- Full source code
What is emSecure?
emSecure is a SEGGER software package that allows creation and verification of digital signatures.
One important feature is that emSecure can make it impossible to create a clone of an embedded device by simply copying hardware and firmware.
And it can do much more, such as securing firmware updates distributed to embedded devices and authenticating licenses, serial numbers, and sensitive data.
emSecure offers 100% protection against hacking. It is not just nice to have, but in fact a must-have, not only for critical devices such as election machines, financial applications, or sensors.
Compromised devices are dangerous in several ways, not just from a commercial point of view. They hamper manufacturers' reputation and might entail severe legal disputes. Not addressing the issue of hacking and cloning is irresponsible.
Based on asymmetric encryption algorithms with two keys, emSecure signatures cannot be forged by reverse engineering of the firmware. A secure, private key is used to generate the digital signature, whereas a second, public key is used to authenticate data by its signature. There is neither a way to get the private key from the public key, nor is it possible to generate a valid signature without the private key.
The emSecure source code has been created from scratch for embedded systems, to achieve highest portability with a small memory footprint and high performance. However, usage is not restricted to embedded systems.
With its easy usage, it takes less than one day to add and integrate emSecure into an existing product.
emSecure is a very complete package, including ready-to-run tools and functionality for generation of keys and signatures.
Why should I use emSecure?
Security consideration
If you want to check the integrity of your data, for instance the firmware running on your product, you would normally include a checksum or hash value into it, generated by a CRC or SHA function. Hashes are excellent at ensuring a critical data transmission, such as a firmware download, has worked flawlessly and to verify that an image, stored in memory, has not changed. However they do not add much security, as an attacker can easily compute the hash value of modified data or images.
Digital signatures can do more. In addition to the integrity check, which is provided by hash functions, a digital signature assures the authenticity of the provider of the signed data, as only he can create a valid signature.
emSecure creates digital signatures using the RSA cryptosystem that has proven robust against decades of attacks on the algorithms. For the default of 2048-bit key sizes, it is considered well beyond the capability of governments, with all their computing power and using the very latest number-theoretic methods, to recover a properly generated RSA private key before 2030, and most probably well beyond that.
emSecure can be used for two security approaches:
1. Anti-hacking: Prevent tampering or exchange of data, for example the firmware running on a product, with non-authorized data.
2. Anti-cloning: Prevent a firmware to be run on a cloned hardware device.
Anti-Hacking — Authentication of firmware
To make sure only authorized firmware images are run on a product the firmware image will be signed with emSecure.
To do this an emSecure key pair is generated one time.
The private key will be included in the production process of the firmware. Once a firmware is created and ready to be shipped or included into a product it will be signed with this private key. The signature will be transferred and stored in the product alongside the firmware.
Firmware signing in production:
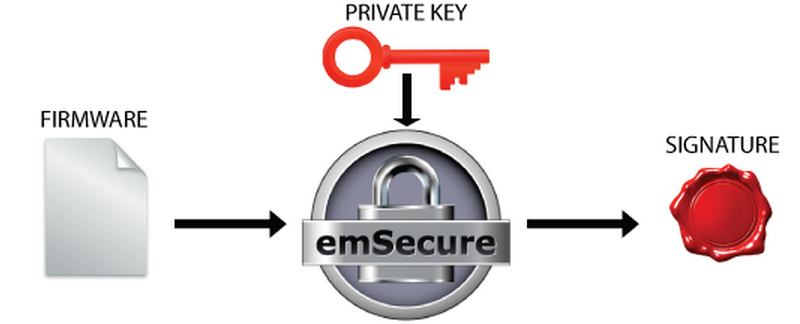
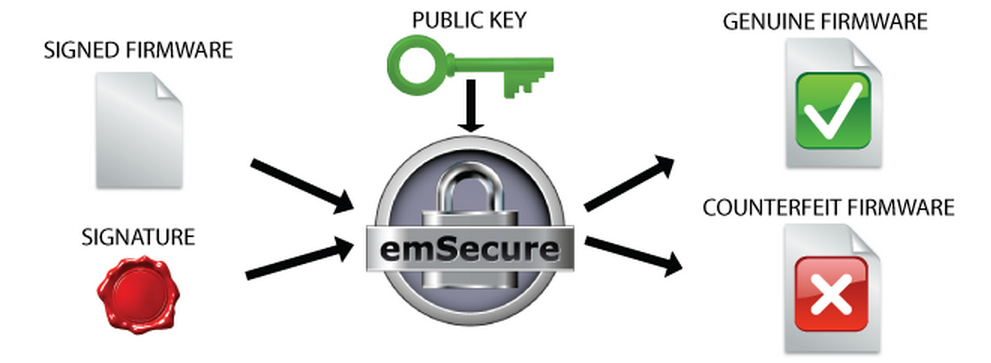
The public key will be included in the bootloader of the product, which manages firmware updates and starts the firmware.
On a firmware update and when starting the product, the bootloader will verify the firmware by its signature. If they match, the firmware is started, otherwise the application will stay in the bootloader or even erase the firmware.
Anti-Hacking Bootloader Verification:
Anti-Cloning — Authentication of hardware
To make sure a product cannot be re-produced by non-authorized manufacturers, by simply copying the hardware, emSecure will be used to sign each genuine product unit.
First an emSecure key pair is generated one time. This is likely done at the production site.
Hardware signing in production:
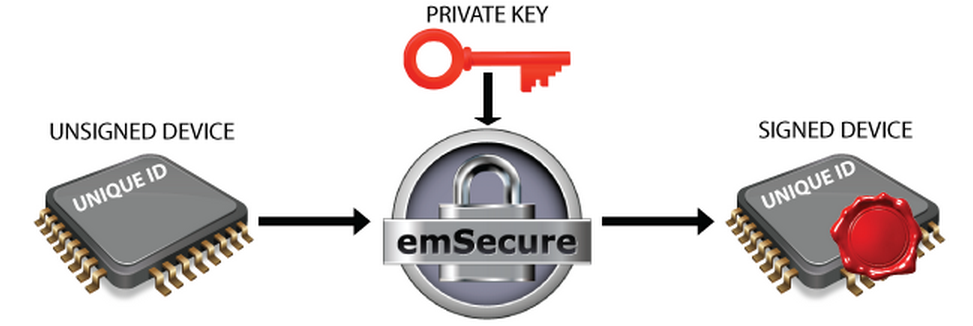
The private key will be included in the production process of the product. At the end of the production process, after the unit is assembled and tested, some hardware-specific, fixed, and unique data, like the unique id of the microcontroller is read from the unit. This data is signed by emSecure with the private key and the signature is written back to the unit into an OTP area or a specified location on memory.
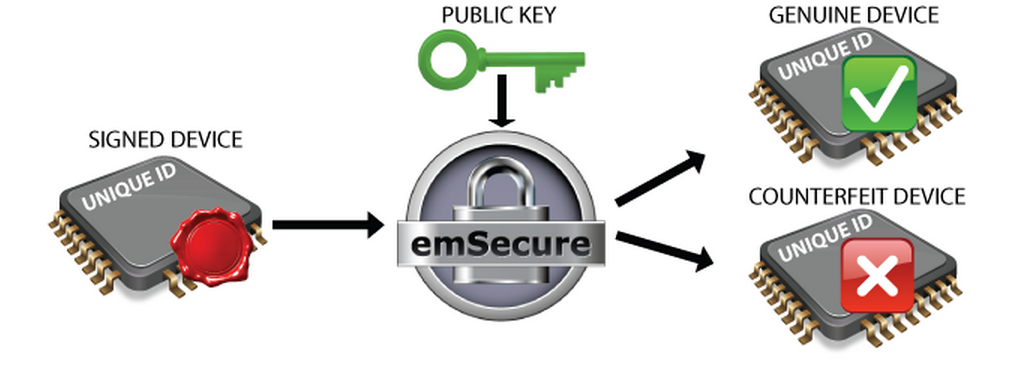
The public key will be included in the firmware which will run on the product. When the firmware is running it will read the unique data from the unit and verify it with the signature. When the signature does not match, for example, when it was simply copied to a counterfeit unit with other unique data, the firmware will refuse to run.
Anti-Cloning Firmware Verification:
Technical Background
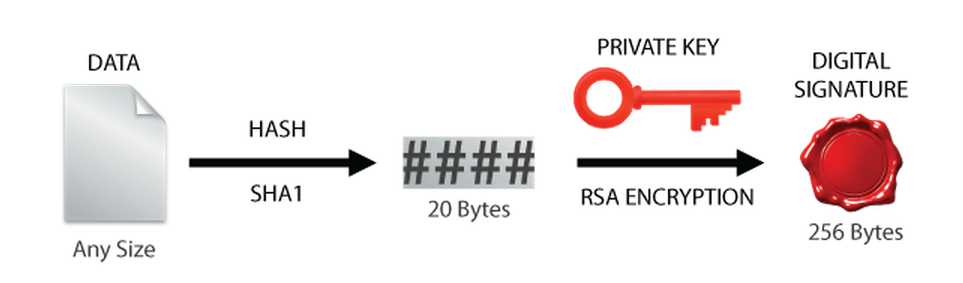
The emSecure signing operation starts by using a secure hash algorithm (SHA1) to generate a hash from the original data. Using the 2kBit RSA private key along with the hash, a digital signature is generated using RSA encryption.
emSecure Signing Technical Details:
The emSecure verification process starts with the data one wishes to verify and the digital signature which was created from the original file. A hash file is generated for the unverified data. The public key and RSA decryption is used to generate the original hash and then compared to verify whether the data file is genuine.
emSecure Verification Technical Details:

FAQs
| Q: | I want to inhibit copying a whole firmware from one product hardware to another cloned one. How can I prevent it to be run from the cloned version with emSecure? |
| A: | Nearly every modern MCU includes a unique ID, which is different on every device. When the signature covers this UID it is only valid on one single device and cannot be run on a cloned or copied product. The firmware can verify the signature at boot-time. |
| Q: |
I added a digital signature to my product. Where should I verify it? |
| A: | Signature verification can be done in-product or off-product. With in-product verification the firmware for example verifies the digital signature at boot-time and refuses to run when the signature cannot be verified. With off-product verification an external application, e.g. a PC application communicating with the device, reads the signature and data from the product and verifies it. |
| Q: | I want my product to only run genuine firmware images. How can I achieve this with emSecure? |
| A: | To make sure a firmware image is genuine, the complete image can be signed with a digital signature. Like when using a CRC for integrity checks, the signature is sent with the firmware data upon a firmware update. The application or bootloader programming the firmware onto the device validates the firmware data with its signature. The signature can only be generated with the private key and should be provided by the developer with the firmware data. |
| Q: | I am providing additional licenses for my product which shall be locked to a specific user or computer. Can I generate license keys with emSecure? |
| A: | Yes. emSecure can generate unique license keys for any data, like a computer ID, a user name, e-mail address or any other data. |
| Q: | My product is sending data to a computer application. Can I make sure the computer application is getting data only from my product with emSecure? |
| A: | Yes. In this case the product is used to sign the data and the computer applications verifies it. To prevent the private key from being read from the product it might be stored encrypted on the product or in the application and decrypted prior to signing the data. |
| Q: | Does emSecure support DSA or ECDSA? |
| A: | No, but both DSA and ECDSA signing and verification code is available from SEGGER. Please get in touch with us if you feel DSA or ECDSA signature verification is what you need. |
emSecure Use Digital Signatures to protect your products的更多相关文章
- Android Application Digital Signatures - Android 数字签名
Android 数字签名 同一个开发人员的多个程序尽可能使用同一个数字证书,这能够带来下面优点. (1)有利于程序升级,当新版程序和旧版程序的数字证书同样时,Android系统才会觉得这两个程序是同一 ...
- What is a Digital Signature? 理解数字签名与数字证书
What is a Digital Signature?An introduction to Digital Signatures, by David Youd Bob (Bob's public k ...
- Vacuum Pump Manufacturer - Vacuum Pump: Prevents Reactive Compound Decomposition Products
Vacuum packaging has been popular in the industry for a long time. Many large companies have joined ...
- Core Java Volume I — 1.2. The Java "White Paper" Buzzwords
1.2. The Java "White Paper" BuzzwordsThe authors of Java have written an influential White ...
- Cryptographic method and system
The present invention relates to the field of security of electronic data and/or communications. In ...
- Method and system for public-key-based secure authentication to distributed legacy applications
A method, a system, an apparatus, and a computer program product are presented for an authentication ...
- BlackArch-Tools
BlackArch-Tools 简介 安装在ArchLinux之上添加存储库从blackarch存储库安装工具替代安装方法BlackArch Linux Complete Tools List 简介 ...
- 著名ERP厂商的SSO单点登录解决方案介绍一
SSO英文全称Single Sign On,单点登录.SSO是在多个应用系统中,用户只需要登录一次就可以访问所有相互信任的应用系统.它包括可以将这次主要的登录映射到其他应用中用于同一个用户 ...
- 比特币_Bitcoin 简介
2008-11 Satoshi Nakamoto Bitcoin: A Peer-to-Peer Electronic Cash System http://p2pbucks.com/?p=99 ...
随机推荐
- centos 6.5环境利用iscsi搭建SAN网络存储服务及服务端target和客户端initiator配置详解
一.简介 iSCSI(internet SCSI)技术由IBM公司研究开发,是一个供硬件设备使用的.可以在IP协议的上层运行的SCSI指令集,这种指令集合可以实现在IP网络上运行SCSI协议,使其能够 ...
- 03-Bootstrap学习
一.Bootstrap的介绍 凡是使用过Bootstrap的开发者,都不在乎做这么两件事情:复制and粘贴.哈哈~,是的使用Bootstrap非常简单,但是在复制粘贴之前,需要先对Bootstrap的 ...
- pyspark遇到报错:_PYSPARK_DRIVER_CONN_INFO_PATH
1. 环境 : centos,启动pyspark,执行如下python命令: import pyspark from pyspark import SparkContext from pyspark ...
- python 运行日志logging代替方案
以下是自己写的 记录日志的代码.(和logging不搭嘎,如果如要学loggging模块,本文末尾有他人的链接.) # prtlog.py ############################## ...
- Python-CSS进阶
0. 什么时候该用什么布局 <!-- 定位布局: 以下两种布局不易解决的问题, 盒子需要脱离文档流处理 --> <!-- 浮动布局: 一般有block特性的盒子,水平排列显示 --& ...
- PYTHON-模块 json pickle shelve xml
""" pickle 和 shevle 序列化后得到的数据 只有python才能解析 通常企业开发不可能做一个单机程序 都需要联网进行计算机间的交互 我们必须保证这个数据 ...
- OCM_第十八天课程:Section8 —》RAC 数据库 _ RAC DB 搭建/RAC DB 配置使用
注:本文为原著(其内容来自 腾科教育培训课堂).阅读本文注意事项如下: 1:所有文章的转载请标注本文出处. 2:本文非本人不得用于商业用途.违者将承当相应法律责任. 3:该系列文章目录列表: 一:&l ...
- Js引擎解析执行 阅读笔记
Js引擎解析执行 阅读笔记 一篇阅读笔记 http://km.oa.com/group/2178/articles/show/145691?kmref=search&from_page=1&a ...
- ORA-12638: 身份证明检索失败 的解决办法
今天在使用应用程序连接Oracle时碰到了 “ORA-12638: 身份证明检索失败” 错误, 解决方法:这是因为Oracle-client端的高级安全性验证导致,解决办法如下: 开始 -> 程 ...
- 一次流式处理的submit
考虑很多: 压背.限流.JVM优化,出错的重试等 #!/bin/bash num_executors=1 executor_memory=1g driver_memory=1g executor_co ...
