codeforces 701 B. Cells Not Under Attack
2 seconds
256 megabytes
standard input
standard output
Vasya has the square chessboard of size n × n and m rooks. Initially the chessboard is empty. Vasya will consequently put the rooks on the board one after another.
The cell of the field is under rook's attack, if there is at least one rook located in the same row or in the same column with this cell. If there is a rook located in the cell, this cell is also under attack.
You are given the positions of the board where Vasya will put rooks. For each rook you have to determine the number of cells which are not under attack after Vasya puts it on the board.
The first line of the input contains two integers n and m (1 ≤ n ≤ 100 000, 1 ≤ m ≤ min(100 000, n2)) — the size of the board and the number of rooks.
Each of the next m lines contains integers xi and yi (1 ≤ xi, yi ≤ n) — the number of the row and the number of the column where Vasya will put the i-th rook. Vasya puts rooks on the board in the order they appear in the input. It is guaranteed that any cell will contain no more than one rook.
Print m integer, the i-th of them should be equal to the number of cells that are not under attack after first i rooks are put.
3 3
1 1
3 1
2 2
4 2 0
5 2
1 5
5 1
16 9
100000 1
300 400
9999800001
分析:这道题刚开始没做出来,看了题解。这道题说让你放棋子,当把这个棋子放下后当前行和当前列都会受到这个棋子的攻击,问你,当放下一个棋子后没有受到攻击的格子还有多少。其实只要统计那些行那些列被棋子占据了即可。用两个set分别保存当前状态下那些行那些列被占据,然后用总棋子数(n*n) 减去被占的行数即:r.size() * n,和被占的列数即: (n - 已受到影的行) ( n - r.size()) * l.size(); 就完成了。
/*************************************************************************
> File Name: cfC.cpp
> Author:
> Mail:
> Created Time: 2016年08月08日 星期一 13时42分35秒
************************************************************************/ #include<iostream>
#include<bits/stdc++.h>
using namespace std;
typedef long long ll;
set<ll> r,l; int main()
{
ios::sync_with_stdio(false);
cin.tie();
ll n,m;
cin >> n >> m;
ll x,y;
ll ans;
ll flag = ;
while(m--)
{
cin >> x >> y;
r.insert(x);
l.insert(y);
ans = n * n - r.size() * n - (n - r.size()) * l.size();
if(flag)
cout << ' ';
cout << ans;
flag++;
}
cout << endl;
return ;
}
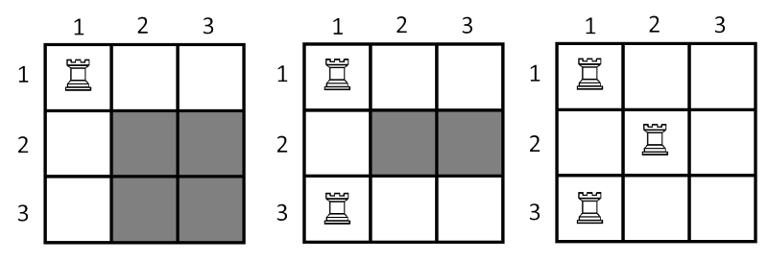
On the picture below show the state of the board after put each of the three rooks. The cells which painted with grey color is not under the attack.
codeforces 701 B. Cells Not Under Attack的更多相关文章
- codeforces 701B B. Cells Not Under Attack(水题)
题目链接: B. Cells Not Under Attack 题意: n*n的棋盘,现在放m个棋子,放一个棋子这一行和这一列就不会under attack了,每次放棋子回答有多少点还可能under ...
- Codeforces Round #364 (Div. 2) B. Cells Not Under Attack
B. Cells Not Under Attack time limit per test 2 seconds memory limit per test 256 megabytes input st ...
- Codeforces Round #364 (Div. 2) Cells Not Under Attack
Cells Not Under Attack 题意: 给出n*n的地图,有给你m个坐标,是棋子,一个棋子可以把一行一列都攻击到,在根据下面的图,就可以看出让你求阴影(即没有被攻击)的方块个数 题解: ...
- codeforces #364b Cells Not Under Attack
比赛的时候 long long sum=n*n,计算不出1e10长度到数,没有搞掉. 哎,以后要注意这个地方.这个题其实不难: 统计能被攻击到的个数,然后用总的个数减掉就可以了.注意有些地方重复计算, ...
- CF 701B Cells Not Under Attack(想法题)
题目链接: 传送门 Cells Not Under Attack time limit per test:2 second memory limit per test:256 megabyte ...
- Cells Not Under Attack
Cells Not Under Attack Vasya has the square chessboard of size n × n and m rooks. Initially the ches ...
- CodeForces 701B Cells Not Under Attack
题目链接:http://codeforces.com/problemset/problem/701/B 题目大意: 输入一个数n,m, 生成n*n的矩阵,用户输入m个点的位置,该点会影响该行和该列,每 ...
- Codeforces Round #115 A. Robot Bicorn Attack 暴力
A. Robot Bicorn Attack Time Limit: 20 Sec Memory Limit: 256 MB 题目连接 http://codeforces.com/contest/17 ...
- cf701B Cells Not Under Attack
Vasya has the square chessboard of size n × n and m rooks. Initially the chessboard is empty. Vasya ...
随机推荐
- mac同时享受教育优惠和免手续费分期
神奇地址:工商银行 http://store.apple.com/cn_icbc_edu招商银行 http://store.apple.com/cn_cmb_edu农业银行 http://sto ...
- 使用InstelliJ IDEA创建Web应用程序
环境版本 Windows 8.1IDE:InstelliJ IDEA 13 Spring:Spring 4.1.1 & Spring MVC 4.1.1 WebLogic 10.3 ...
- setjmp()和longjmp()函数
之前我们讲到了过程活动记录(AR),那么如何来操纵AR呢,一个可能的方法是,根据局部变量的地址进行推算,例如对于上面的a函数,执行a函数时的当前AR地址就是参数i的地址偏移8个字节,也就是 ((cha ...
- 嵌入式(C)笔试题
1 读程序段,回答问题 (a) int main(int argc,char *argv[]) { int c=9,d=0; c=c++%5; d=c; printf("d=%d\n&quo ...
- 压缩和还原压缩的JS代码
压缩JS代码:packer – 最好用的 javascript 压缩工具地址: http://dean.edwards.name/packer/ http://kan.willin.org/?page ...
- mysql索引的使用及优化方法
数据库高级管理及优化 MySQL性能优化 优化MySQL数据库是数据库管理员和数据库开发人员的必备技能.优化MySQL,一方面是找出系统的瓶颈,提高MySQL数据库整体的性能:另一方面是合理设计结构和 ...
- C语言打印100以内的质数
C语言打印100以内的质数 #include <stdio.h> int main() { int number; int divisor; for( number = 3; number ...
- MYSQL源代码编译的变动
Mysql的安装,对于mysql不同版本号的mysql源代码编译方式不一样 5.6.2的版本号開始编译方式已经由 configure 变成了cmake方式 ,相关的新的 编译方式在mysql官网已经提 ...
- IPS
转自:http://www.ithome.com.tw/node/79293 企業中網路環境的防護,通常都是先有防火牆,再搭配IPS.但是,實際上買得起IPS防護的企業有限,這是因為IPS的價格很昂貴 ...
- [poj 2912] Rochambeau 解题报告 (带权并查集)
题目链接:http://poj.org/problem?id=2912 题目: 题目大意: n个人进行m轮剪刀石头布游戏(0<n<=500,0<=m<=2000) 接下来m行形 ...
