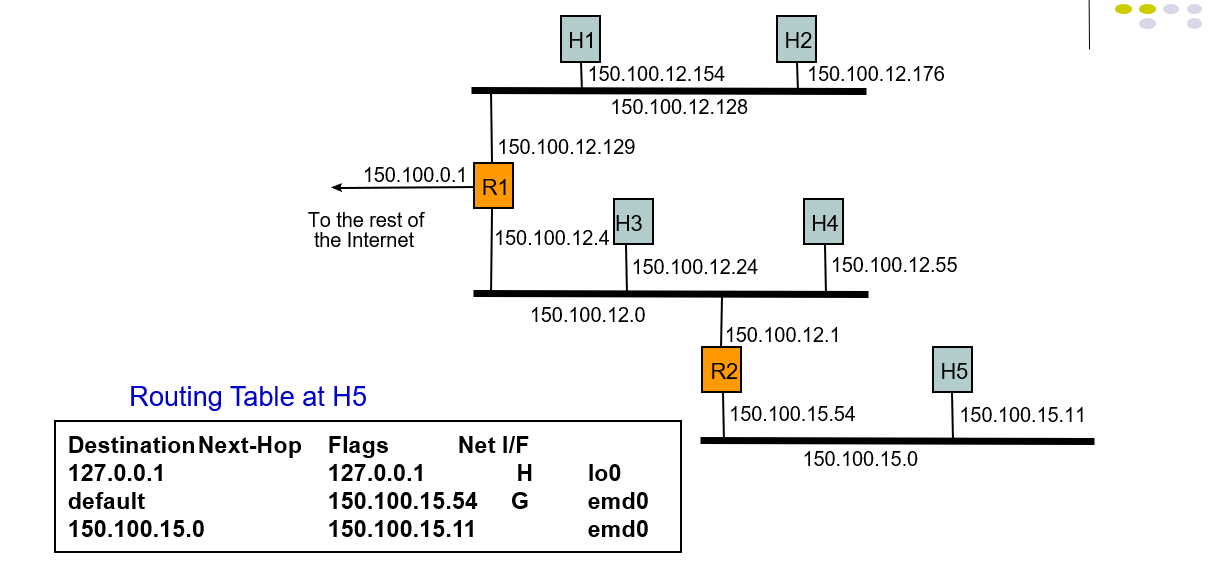
Subnet Routing Examples
Routing Table
- Each row in routing table contains:
- Destination IP address
- IP address of next-hop router
- Physical address
- Statistics information
- Flags
- H=1 (0) indicates route is to a host (network)
- G=1 (0) indicates route is to a router (directly connected destination)
Routing Search and Actions
- Routing table search order & action
- Complete destination address; send as per next-hop & G flag
- Destination network ID; send as per next-hop & G flag
- Default router entry; send as per next-hop
- Declare packet undeliverable; send ICMP “host unreachable error” packet to originating host
Example 1: A packet with 150.100.15.11 arrives at R1
- Host5 want to send a packet to Rout1, it firstly searches 150.100.0.1 in the routing table, but not match.
- So it send the packet to R2 as the default IP address.
Example 1: Subnetting Scheme
- H and R find next hop in this way.
- IP address 150.100.15.11 in binary string is
10010110 01100100 00001111 00001011 - Apply subnet mask to IP addresses to find corresponding subnet
- IP address = 10010110 01100100 00001111 00001011
- Mask = 11111111 11111111 11111111 10000000
- AND = 10110110 01100100 00001111 00000000
- Subnet = 150.100.15.0
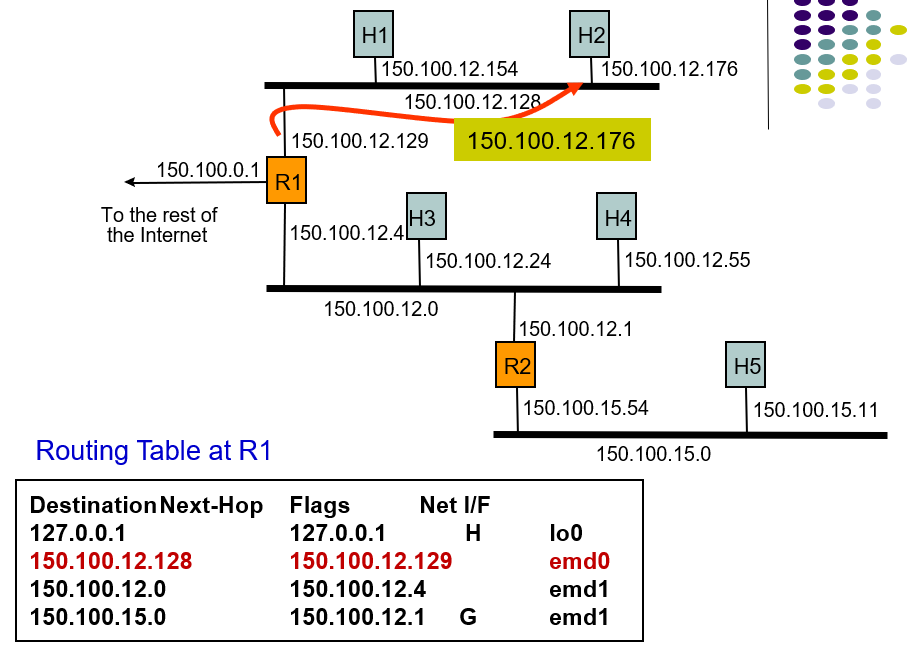
Example 2: Host H5 sends packet to host H2
- The routing table contains:destination next-hop,flags,default next-hop,physical interface.
- H5 searches the routing table but doesn't find destination next-hop, so it send the packet as the default next-hop.
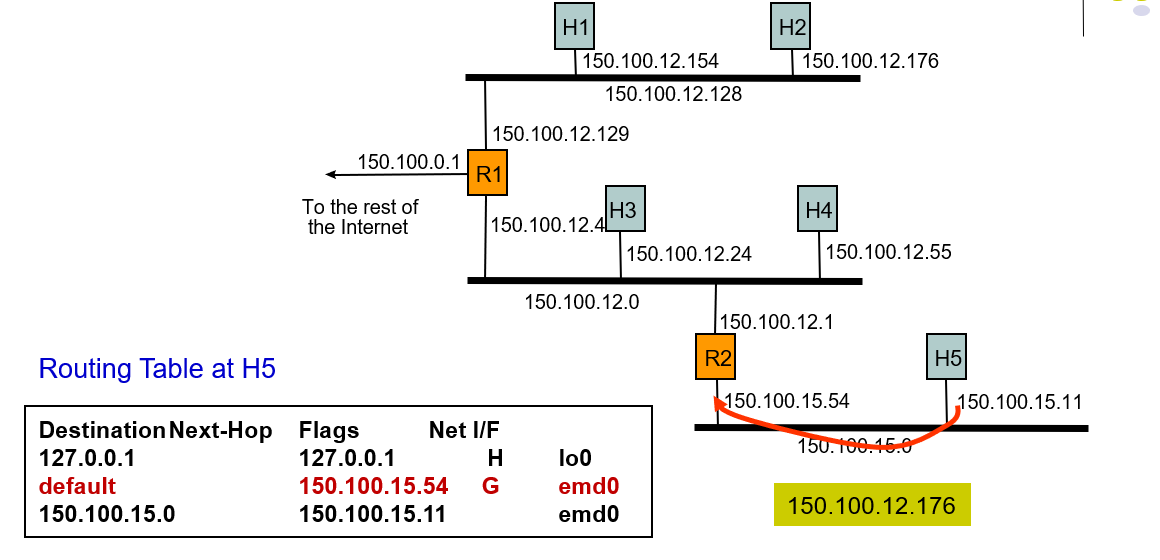
Example 2: Host H5 sends packet to host H2
- 127.0.0.1 is the native address.
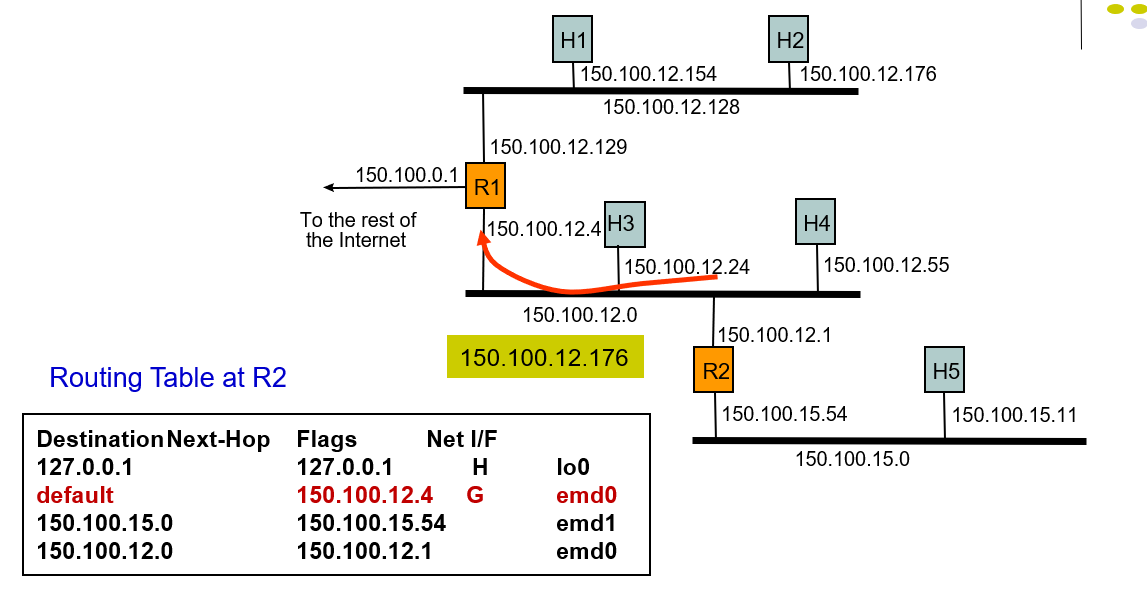
Example: Host H5 sends packet to host H2
- It sned a packet so the network interface which delivers a packet to the local are network by broadcasting and host H2 receive the packet.
Discuss
- Discuss the difficulties with using actual time in the Time-to-Live field
- TTL restricts the max hops in the network, even if it was called "Time to live", but it is hops instead of time. The distance is different in all kinds of network, and the delay time in every stops is not the same. So it difficult to confirm the actual time, using hops to stand for time to live is a better choose.
Subnet Routing Examples的更多相关文章
- ip 子网掩码 网关 DNS
这一篇文章也很好: 原文引用于: http://www.cnblogs.com/jiqing9006/p/3365939.html 内外网ip: IP地址: IPv4地址分为A.B.C.D.E五类, ...
- IP子网掩码划分及设置
IP子网掩码划分及设置 定长子网掩码: 一.子网掩码的计算 TCP/IP网间网技术产生于大型主流机环境中,它能发展到今天的规模是当初的设计者们始料未及的.网间网规模的迅速扩展对IP地址模式的威胁并不是 ...
- HCNP学习笔记之子网掩码的计算和划分详细
0x00 子网掩码的计算 TCP/IP网间网技术产生于大型主流机环境中,它能发展到今天的规模是当初的设计者们始料未及的.网间网规模的迅速扩展对IP地址模式的威胁并不是它不能保证主机地址的唯一性,而是会 ...
- Routing 功能概述 - 每天5分钟玩转 OpenStack(98)
路由服务(Routing)提供跨 subnet 互联互通功能. 例如前面我们搭建了实验环境: cirros-vm1 172.16.100.3 vlan100 cirros-vm ...
- 理解 OpenStack 高可用(HA)(3):Neutron 分布式虚拟路由(Neutron Distributed Virtual Routing)
本系列会分析OpenStack 的高可用性(HA)概念和解决方案: (1)OpenStack 高可用方案概述 (2)Neutron L3 Agent HA - VRRP (虚拟路由冗余协议) (3)N ...
- Examples of MIB Variables - SNMP Tutorial
30.5 Examples of MIB Variables Versions 1 and 2 of SNMP each collected variables together in a singl ...
- 东大OJ-1588: Routing Table
题目描述 In the computer network, a Router is a device which finds an optimal way to transmit the datagr ...
- ural 1072. Routing
1072. Routing Time limit: 1.0 secondMemory limit: 64 MB There is a TCP/IP net of several computers. ...
- Top 30 Nmap Command Examples For Sys/Network Admins
Nmap is short for Network Mapper. It is an open source security tool for network exploration, securi ...
随机推荐
- mysql-profiling详解
要想优化一条 Query,我们就需要清楚的知道这条 Query 的性能瓶颈到底在哪里,是消耗的 CPU计算太多,还是需要的的 IO 操作太多?要想能够清楚的了解这些信息,在 MySQL 5.0 和 M ...
- Bazaar 版本控制工具
Bazaar是一个分布式的版本控制系统,它发布在GPL许可协议之下,并可用于Windows.GNU/Linux.UNIX以及Mac OS系统.Bazaar由Canonical公司赞助,目前已服务于Sa ...
- 关于Sychronized和volatile自己总结的一点点理解(草稿)
问答形式列举: 1. 为什么说sychronized能保证可见性 synchronized和Lock能保证同一时刻只有一个线程获取锁然后执行同步代码,并且在释放锁之前会将对变量的修改刷新到主存当中.因 ...
- Eclipse常用操作
一 Eclipse常用快捷键 ctrl+Q:跳到最后一次编辑处. ctrl+F:在当前文件中查找并替换. ctrl+T:查看类的继承关系. alt+左箭头:返回到光标的上一个位置. alt+右箭头:前 ...
- iframe 子页面改变父页面样式
iframe 子窗口调节父窗口样式: $(window.parent.document).find("body").attr("style"," 父元 ...
- Jupyter 常用快捷键 及 常用方法笔记
两个不同的cell有上下的关系, 不是完全独立的, 下图可以看出下面的res是引用上面的 保存节点 就像虚拟机的快照与恢复 回到节点 保存文件 s(快捷键) 实际写 ...
- 如何解决织梦DedeCMS后台模块管理列表不显示
在使用织梦Dedecms的过程中,我们会遇到模块管理列表无法显示的问题,造成织梦模块管理列表无法显示的原因,可能有很多种,现小编总结了遇到过的一种方法仅供参考. 方法步骤一: 由于/data/modu ...
- day14 HTML CSS
HTML HTML是英文Hyper Text Mark-up Language(超文本标记语言)的缩写,他是一种制作万维网页面标准语言(标记).相当于定义统一的一套规则,大家都来遵守他,这样就可以让浏 ...
- Jmeter参数化设置,多用户登录
一.模拟多用户登录场景 如登录模式如下图所示,登录界面中需要输入:用户名.密码.验证码 用户名以及密码均是固定值,不需要做处理.验证码需要处理一下,可以后台配置成固定值,具体可以找开发咨询. 在此场景 ...
- QT 编译遇到重定义;不同的基类型&在QT中使用C++ lib库
最近在使用osg和qt开发,在集成osg时候因为我使用的qt版本为非opengl的版本,导致qt自己封了一遍opengl的一些基类变量如double 这时候就会跟osg中声明的opengl的类型冲突, ...
