hdu4771 Stealing Harry Potter's Precious
注意……你可能会爆内存……
假设一个直接爆搜索词……
队列存储器元件被减少到……
#include<iostream>
#include<map>
#include<string>
#include<cstring>
#include<cstdio>
#include<cstdlib>
#include<cmath>
#include<queue>
#include<vector>
#include<algorithm>
using namespace std;
const int inf=(1<<30)-1+(1<<30);
int goal;
char a[110][110];
int dp[110][110][1<<4];
int row,line;
int xd[4]={-1,1,0,0};
int yd[4]={0,0,-1,1};
int state[110][110];
struct node
{
int x,y,s;
node(){}
node(int a,int b,int c){x=a;y=b;s=c;}
};
bool isbeyond(int x,int y)
{
return x<0||x>=row||y<0||y>=line;
}
int bfs(node s)
{
int ans,i;
node now,next;
queue<node>qq;
qq.push(s);
memset(dp,-1,sizeof(dp));
dp[s.x][s.y][s.s]=0;
ans=inf;
while(qq.size())
{
now=qq.front();
qq.pop();
for(i=0;i<4;i++)
{
next=now;
next.x+=xd[i];
next.y+=yd[i];
next.s|=state[next.x][next.y];
if(isbeyond(next.x,next.y))
continue;
if(a[next.x][next.y]=='#')
continue;
if(dp[next.x][next.y][next.s]!=-1)
{
if(dp[now.x][now.y][now.s]+1>=dp[next.x][next.y][next.s])
continue;
}
dp[next.x][next.y][next.s]=dp[now.x][now.y][now.s]+1;
if(next.s==goal)
{
ans=min(ans,dp[next.x][next.y][next.s]);
continue;
}
qq.push(next);
}
}
if(ans==inf)
ans=-1;
return ans;
}
int main()
{
int i,j,n,k;
node s;
while(cin>>row>>line)
{
if(row==0&&line==0)
break;
for(i=0;i<row;i++)
{
cin>>a[i];
for(j=0;j<line;j++)
if(a[i][j]=='@')
s=node(i,j,0);
}
cin>>n;
goal=(1<<n)-1;
memset(state,0,sizeof(state));
for(k=0;k<n;k++)
{
cin>>i>>j;
state[i-1][j-1]|=1<<k;
}
s.s=state[s.x][s.y];
cout<<bfs(s)<<endl;
}
return 0;
}
Stealing Harry Potter's Precious
Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 K (Java/Others)
Total Submission(s): 1828 Accepted Submission(s): 853
uncle Vernon never allows such magic things in his house. So Harry has to deposit his precious in the Gringotts Wizarding Bank which is owned by some goblins. The bank can be considered as a N × M grid consisting of N × M rooms. Each room has a coordinate.
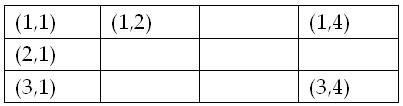
The coordinates of the upper-left room is (1,1) , the down-right room is (N,M) and the room below the upper-left room is (2,1)..... A 3×4 bank grid is shown below:
Some rooms are indestructible and some rooms are vulnerable. Goblins always care more about their own safety than their customers' properties, so they live in the indestructible rooms and put customers' properties in vulnerable rooms. Harry Potter's precious
are also put in some vulnerable rooms. Dudely wants to steal Harry's things this holiday. He gets the most advanced drilling machine from his father, uncle Vernon, and drills into the bank. But he can only pass though the vulnerable rooms. He can't access
the indestructible rooms. He starts from a certain vulnerable room, and then moves in four directions: north, east, south and west. Dudely knows where Harry's precious are. He wants to collect all Harry's precious by as less steps as possible. Moving from
one room to another adjacent room is called a 'step'. Dudely doesn't want to get out of the bank before he collects all Harry's things. Dudely is stupid.He pay you $1,000,000 to figure out at least how many steps he must take to get all Harry's precious.
In each test cases:
The first line are two integers N and M, meaning that the bank is a N × M grid(0<N,M <= 100).
Then a N×M matrix follows. Each element is a letter standing for a room. '#' means a indestructible room, '.' means a vulnerable room, and the only '@' means the vulnerable room from which Dudely starts to move.
The next line is an integer K ( 0 < K <= 4), indicating there are K Harry Potter's precious in the bank.
In next K lines, each line describes the position of a Harry Potter's precious by two integers X and Y, meaning that there is a precious in room (X,Y).
The input ends with N = 0 and M = 0
2 3
##@
#.#
1
2 2
4 4
#@##
....
####
....
2
2 1
2 4
0 0
-1
5
版权声明:本文博主原创文章。博客,未经同意不得转载。
hdu4771 Stealing Harry Potter's Precious的更多相关文章
- hdu 4771 Stealing Harry Potter's Precious(bfs)
题目链接:hdu 4771 Stealing Harry Potter's Precious 题目大意:在一个N*M的银行里,贼的位置在'@',如今给出n个宝物的位置.如今贼要将全部的宝物拿到手.问最 ...
- hdu 4771 Stealing Harry Potter's Precious
题目:给出一个二维图,以及一个起点,m个中间点,求出从起点出发,到达每一个中间的最小步数. 思路:由于图的大小最大是100*100,所以要使用bfs求出当中每两个点之间的最小距离.然后依据这些步数,建 ...
- hdu4771 Stealing Harry Potter's Precious(DFS,BFS)
练习dfs和bfs的好题. #include<iostream> #include<cstdio> #include<cstdlib> #include<cs ...
- HDU 4771 Stealing Harry Potter's Precious
Stealing Harry Potter's Precious Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 ...
- HDU 4771 Stealing Harry Potter's Precious (2013杭州赛区1002题,bfs,状态压缩)
Stealing Harry Potter's Precious Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 ...
- HDU 4771 Stealing Harry Potter's Precious dfs+bfs
Stealing Harry Potter's Precious Problem Description Harry Potter has some precious. For example, hi ...
- hdu 4771 13 杭州 现场 B - Stealing Harry Potter's Precious 暴力bfs 难度:0
Description Harry Potter has some precious. For example, his invisible robe, his wand and his owl. W ...
- Stealing Harry Potter's Precious BFS+DFS
Problem Description Harry Potter has some precious. For example, his invisible robe, his wand and hi ...
- 【HDU 4771 Stealing Harry Potter's Precious】BFS+状压
2013杭州区域赛现场赛二水... 类似“胜利大逃亡”的搜索问题,有若干个宝藏分布在不同位置,问从起点遍历过所有k个宝藏的最短时间. 思路就是,从起点出发,搜索到最近的一个宝藏,然后以这个位置为起点, ...
随机推荐
- NET Core 中的依赖注入
NET Core 中的依赖注入 [共7篇] 一.控制反转(IoC) ASP.NET Core在启动以及后续针对每个请求的处理过程中的各个环节都需要相应的组件提供相应的服务,为了方便对这些组件进行定制, ...
- dtach-linux-分离功能-小工具 - 点点滴滴 Linux | 点点滴滴 Linux
dtach-linux-分离功能-小工具 - 点点滴滴 Linux | 点点滴滴 Linux dtach-linux-分离功能-小工具 2013年05月20日 ⁄ Linux工具 ⁄ 共 1775字 ...
- Git中的merge命令实现和工作方式
想象一下有例如以下情形:代码库中存在两个分支,而且每一个分支都进行了改动.最后你想要将当中的一个分支合并到其它的分支中.个人博客网址 http://swinghu.github.com/ 那么要问合并 ...
- 《Python学习手册》读书笔记
之前为了编写一个svm分词的程序而简单学了下Python,觉得Python很好用,想深入并系统学习一下,了解一些机制,因此开始阅读<Python学习手册(第三版)>.如果只是想快速入门,我 ...
- NET实现的DDD、CQRS与微服务架构
WeText项目:一个基于.NET实现的DDD.CQRS与微服务架构的演示案例 最近出于工作需要,了解了一下微服务架构(Microservice Architecture,MSA).我经过两周业余时间 ...
- Codeforces Round #296 (Div. 1) E. Triangles 3000
http://codeforces.com/contest/528/problem/E 先来吐槽一下,一直没机会进div 1, 马力不如当年, 这场题目都不是非常难,div 2 四道题都是水题! 题目 ...
- cf-#189-div 2
A题: 从前往后暴搜就OK: B题: 每次询问的时候都bfs一次 C题: 异或运算,从后往前运算. -------------分割线--------------------- D题:对于第K个人来说, ...
- java -D參数简化增加多个jar【简化设置classpath】
1.-D<name>=<value> set a system property 设置系统属性. java命令引入jar时能够-cp參数,但时-cp不能用通配符(多个jar时 ...
- CSDN博客的一些问题(友好的吐槽)--后记,有一点点改进
近期,CSDN博客真的非常不稳定,时常会出现503错误. 昨天.我发现自己的博客的訪问量仅仅有4万多,今天最终发现它变回原来的6万多了. 我写博客不是为了这个訪问量,可是,CSDN这点使用问题啦. 或 ...
- 〖Groovy〗语言使用贴士(Tips)(转)
[Groovy]是一门运行在[JVM]之上的动态语言.由[James Strachan]和[Bob McWhirter]于2003年启动开发,之后于2004年3月成为[JSR 241](Java Sp ...
