mosquitto --- 单向认证
1.生成证书
要单向配置SSL 需要 做三项前置工作
1. 生成CA证书
2.生成server 端证书,server 端key
github 的一个开源项目已经做到这点 ,详情可见 https://github.com/iandl/mqttitude/blob/master/tools/TLS/generate-CA.sh
为方便阅读,整个shell 代码先贴出来
#!/bin/sh
#(@)generate-CA.sh - Create CA key-pair and server key-pair signed by CA # Copyright (c) 2013 Jan-Piet Mens <jpmens()gmail.com>
# All rights reserved.
#
# Redistribution and use in source and binary forms, with or without
# modification, are permitted provided that the following conditions are met:
#
# 1. Redistributions of source code must retain the above copyright notice,
# this list of conditions and the following disclaimer.
# 2. Redistributions in binary form must reproduce the above copyright
# notice, this list of conditions and the following disclaimer in the
# documentation and/or other materials provided with the distribution.
# 3. Neither the name of mosquitto nor the names of its
# contributors may be used to endorse or promote products derived from
# this software without specific prior written permission.
#
# THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
# AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
# IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
# ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE
# LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
# CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
# SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
# INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
# CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
# ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
# POSSIBILITY OF SUCH DAMAGE. set -e DIR=${TARGET:='.'}
# A space-separated list of alternate hostnames (subjAltName)
# may be empty ""
ALTHOSTNAMES="broker.example.com foo.example.de"
CA_ORG='/O=MQTTitude.org/emailAddress=nobody@example.net'
CA_DN="/CN=An MQTT broker${CA_ORG}"
CACERT=${DIR}/ca
SERVER=${DIR}/server
SERVER_DN="/CN=$(hostname -f)$CA_ORG"
keybits=2048
openssl=$(which openssl) function maxdays() {
nowyear=$(date +%Y)
years=$(expr 2032 - $nowyear)
days=$(expr $years '*' 365) echo $days
} function getipaddresses() {
/sbin/ifconfig |
sed -En '/inet6? /p' |
sed -Ee 's/inet6? (addr:)?//' |
awk '{print $1;}' |
sed -e 's/[%/].*//' |
egrep -v '(::1|127\.0\.0\.1)' # omit loopback to add it later
} function addresslist() { ALIST=""
for a in $(getipaddresses); do
ALIST="${ALIST}IP:$a,"
done
ALIST="${ALIST}IP:127.0.0.1,IP:::1," for h in $(echo ${ALTHOSTNAMES}); do
ALIST="${ALIST}DNS:$h,"
done
ALIST="${ALIST}DNS:localhost"
echo $ALIST } days=$(maxdays) if [ -n "$CAKILLFILES" ]; then
rm -f $CACERT.??? $SERVER.??? $CACERT.srl
fi if [ ! -f $CACERT.crt ]; then
# Create un-encrypted (!) key
$openssl req -newkey rsa:${keybits} -x509 -nodes -days $days -extensions v3_ca -keyout $CACERT.key -out $CACERT.crt -subj "${CA_DN}"
echo "Created CA certificate in $CACERT.crt"
$openssl x509 -in $CACERT.crt -nameopt multiline -subject -noout chmod 400 $CACERT.key
chmod 444 $CACERT.crt
fi if [ ! -f $SERVER.key ]; then
echo "--- Creating server key and signing request"
$openssl genrsa -out $SERVER.key $keybits
$openssl req -new \
-out $SERVER.csr \
-key $SERVER.key \
-subj "${SERVER_DN}"
chmod 400 $SERVER.key
fi if [ -f $SERVER.csr -a ! -f $SERVER.crt ]; then # There's no way to pass subjAltName on the CLI so
# create a cnf file and use that. CNF=`mktemp /tmp/cacnf.XXXXXXXX` || { echo "$0: can't create temp file" >&2; exit 1; }
sed -e 's/^.*%%% //' > $CNF <<\!ENDconfig
%%% [ JPMextensions ]
%%% basicConstraints = critical,CA:false
%%% nsCertType = server
%%% keyUsage = nonRepudiation, digitalSignature, keyEncipherment
%%% nsComment = "Broker Certificate"
%%% subjectKeyIdentifier = hash
%%% authorityKeyIdentifier = keyid,issuer:always
%%% subjectAltName = $ENV::SUBJALTNAME
%%% # issuerAltName = issuer:copy
%%% nsCaRevocationUrl = http://mqttitude.org/carev/
%%% nsRevocationUrl = http://mqttitude.org/carev/
!ENDconfig SUBJALTNAME="$(addresslist)"
export SUBJALTNAME # Use environment. Because I can. ;-) echo "--- Creating and signing server certificate"
$openssl x509 -req \
-in $SERVER.csr \
-CA $CACERT.crt \
-CAkey $CACERT.key \
-CAcreateserial \
-CAserial "${DIR}/ca.srl" \
-out $SERVER.crt \
-days $days \
-extfile ${CNF} \
-extensions JPMextensions rm -f $CNF
chmod 444 $SERVER.crt
fi
实际过程中大家可根据自己的需要修改这段脚本的内容,为了快速搭建我们的单向SSL, 我们这里不做任何修改,直接执行这段shell
执行完成后可生成 server.crt server.csr server.ke ca.crt ca.key ca.srl
$ wget https://github.com/iandl/mqttitude/blob/master/tools/TLS/generate-CA.sh .
$ bash ./generate-CA.sh
配置mosquitto 配置文件
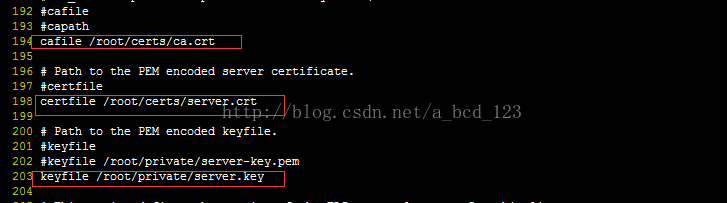
ca.crt, sever.crt, server.key 是上面生成的文件
启动 broker
启动 subscribe 端, 这里需要注意,如果sbuscreibe 端和broker 不在同一台机器,请将第一步生成的ca.crt 拷贝到 该机器的/root/certs下

启动 publish 端, 如果publish 端和broker 不在同一台机器,请将第一步生成的ca.crt 拷贝到 该机器的/root/certs下

mosquitto --- 单向认证的更多相关文章
- mosquitto ---SSL/TLS 单向认证+双向认证
生成证书 # * Redistributions in binary form must reproduce the above copyright # notice, this list of ...
- 基于mosquitto的MQTT服务器---SSL/TLS 单向认证+双向认证
基于mosquitto的MQTT服务器---SSL/TLS 单向认证+双向认证 摘自:https://blog.csdn.net/ty1121466568/article/details/811184 ...
- mosquitto SSL认证
[11]MQTT mosquitto 双向SSL认证配置方式 [12]MQTT mosquitto 单向SSL认证的配置方式 Mosquitto服务器的搭建以及SSL/TLS安全通信配置(比较可信) ...
- java https单向认证(忽略认证)并支持http基本认证
https单向认证(忽略认证)并支持http基本认证, 温馨提示 1,jar包要导入对 2,有匿名类编译要注意 3,欢迎提问,拿走不谢!背景知识 Https访问的相关知识中,主要分为单向验证和双向验证 ...
- https单向认证和双向认证
单向认证: .clinet<--server .clinet-->server .client从server处拿到server的证书,通过公司的CA去验证该证书,以确认server是真实的 ...
- ssl双向认证和单向认证原理
有朋友在搞一个项目,周末有聊到一些安全性的东西,很自然会想起https,但https究竟如何实施,其原理又是什么? 基于ssl,一般的应用都是单向认证,如果应用场景要求对客户来源做验证也可以实现成双向 ...
- wildfly9 配置SSL单向认证/https
D:\>keytool -genkey -keystore cdi-init.keystore -alias cdi-init -keyalg RSA -keysize 2048 -validi ...
- tomcat 配置https (单向认证)
1.单向认证,就是传输的数据加密过了,但是不会校验客户端的来源 2.双向认证,如果客户端浏览器没有导入客户端证书,是访问不了web系统的,找不到地址 如果只是加密,单向就行 如果想要用系统的人没有证书 ...
- tomcat------https单向认证和双向认证
一.https分为单向认证和双向认证: 单向认证就是说,只有客户端使用ssl时对服务器端的证书进行认证,也就是说,客户端在请求建立之前,服务器端会向客户端发送一个证书,一般情况下,这种证书都是由自己 ...
随机推荐
- C# httpwebrequest post 传输百分号‘%’
转载:http://blog.csdn.net/qqstrive/article/details/8229601 通过webrequest的post传输数据的时候,如果url里面的参数带有‘%’,那么 ...
- Ext的表格控件如何绑定
1. XML数据源 假设我们有一个数据源是以XML的形式存在的,我们需要从里面取出数据并绑定在界面.XML的结构如下: </age> <name>石曼迪</name&g ...
- 如何使用花生壳 发布WCF服务 进行外网访问 z
http://www.cnblogs.com/wanglg/p/5375230.html 当我们发布WCF服务的时候,可以直接通过服务器的域名或者IP进行. 但是如果仅仅是通过花生壳进行域名解析,需要 ...
- python笔记20-yaml文件写入(ruamel.yaml)
前言 yaml作为配置文件是非常友好的一种格式,前面一篇讲了yaml的一些基础语法和读取方法,本篇继续讲yaml文件写入方法 用yaml模块写入字典嵌套字典这种复杂的数据,会出现大括号{ },不是真正 ...
- Unity3d地图制作之模型高光
由于颇受暗黑破坏神美工的影响,最近都在研究怎么制作场景地图之类的. 那么今日讲的模型高光虽然和地图无关,但是也涉及到一些美工的知识,尤其是shader. 按照国际惯例,先贴一张图饱饱眼福. 大家可以看 ...
- PhD Positions opening at University of Nevada, Reno (Wireless Networking / Cognitive Radio / Wireless Security)
PhD Positions opening at University of Nevada, RenoDept. of Computer Science and Engineering Researc ...
- poj 3130 How I Mathematician Wonder What You Are! - 求多边形有没有核 - 模版
/* poj 3130 How I Mathematician Wonder What You Are! - 求多边形有没有核 */ #include <stdio.h> #include ...
- Python学习(七)面向对象 ——类和实例
Python 面向对象 —— 类和实例 类 虽然 Python 是解释性语言,但是它是面向对象的,能够进行对象编程.至于何为面向对象,在此就不详说了.面向对象程序设计本身就很值得深入学习,如要了解,请 ...
- django ORM创建数据库方法
1.指定连接pymysql(python3.x) 先配置_init_.py import pymysql pymysql.install_as_MySQLdb() 2.配置连接mysql文件信息 se ...
- unexpected token: * 和 java.lang.ClassCastException: [Ljava.lang.Object; cannot be cast to 解决办法
一.unexpected token: * 的解决办法 首先要搞清楚sql与hql的区别! sql操作的是数据库表,而hql操作的是对象! sql中“select * from table”,而hq ...
