Given d and e, factorize N to attack RSA
题目如下:
RSA算法的使用一般要求每个不同的用户有一个独立的模数N。有天,Bob脑洞大开,认为似乎没有必要这样做。只需要一个模数N,然后给不同的用户分发不同的e和d就好了。可惜这种做法有严重的安全漏洞。
给定Alice的公钥(e1,N),Adv为了破解Alice的密文,他也注册一个公私钥对,得到(e2, d2, N),然后他就可以巧妙地计算出Alice的解密私钥。注意:Adv得到的私钥不一定与Alice的相同,只是它确实可以解密。
(e1 =
44379563805854841580307748547737435172564831877127303051909203409873174780389273150966396080375621148040275710628408649117613085199533826455458312376264659153842853015345496268736337902730232293424031775369541079662258443836020140399047886828048837071536578243295077689245549921524765222192270061081366989243
N =
188115669939527035644766943794256836704505079895306601119938518634078379404429524926183546093986493443422022468844644307633083886388295943602507953702360632321739073592477683222131866451975315695813478098524853358977564134499058448438525811837376172990710150323209055804682074564005014776547535959114226010493
)
(e2 =
112465763139808984065405993827008716763974555200543206549100182421914260511395374512318119557311872118857352370325610769529155517454000609905909538235321637165438962672069969201523246380106126889874030417878823876408727390390051948217715186480658609481138938023687641185709391304878382079926539531855678365763
d2 =
55881649455902117785162844948995531081646760354831350250450328774662614334096209227124014992837725793190883247171284132768863157972472923057215962250425474753160669444247876851199006665484502793278672692761545198268608005712388135980371518592854149756626148424994498979112285655516912703587302199972664162731
N =
188115669939527035644766943794256836704505079895306601119938518634078379404429524926183546093986493443422022468844644307633083886388295943602507953702360632321739073592477683222131866451975315695813478098524853358977564134499058448438525811837376172990710150323209055804682074564005014776547535959114226010493
)
求解(e1, N)加密得到的密文(没有编码,是一个整数):
166834578157098529809222592291594342260836191039081705782260506690911922650094691879568641873546447862853989518762075081785381252999566333779425586950217410876199240677942391128773211264433855236931134494842223272683014826519273429450763047329625425561073729238027952900168036140503255431512655421527963913597
请解释过程,给出明文及其解密用的私钥。
一开始想,给定的N相同,是不是共模攻击,看并不满足共模攻击的条件
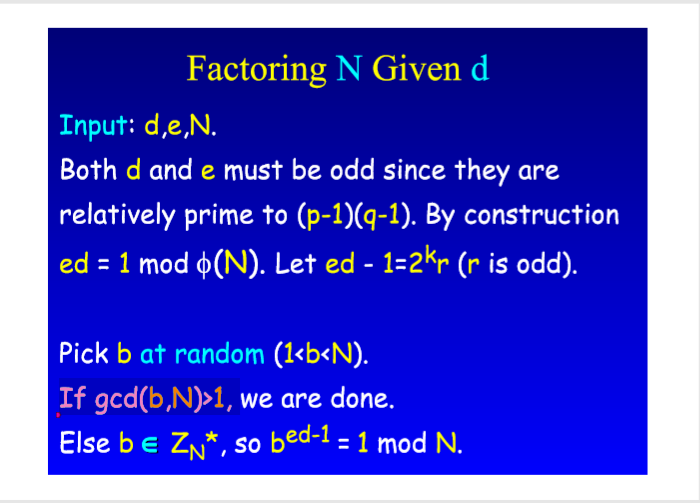
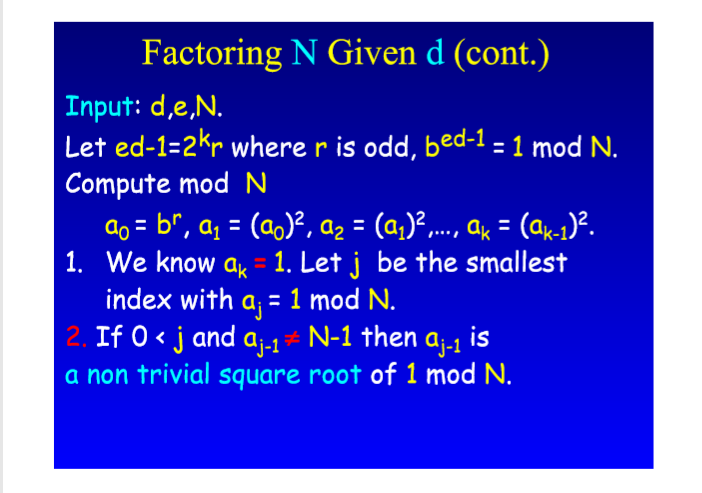
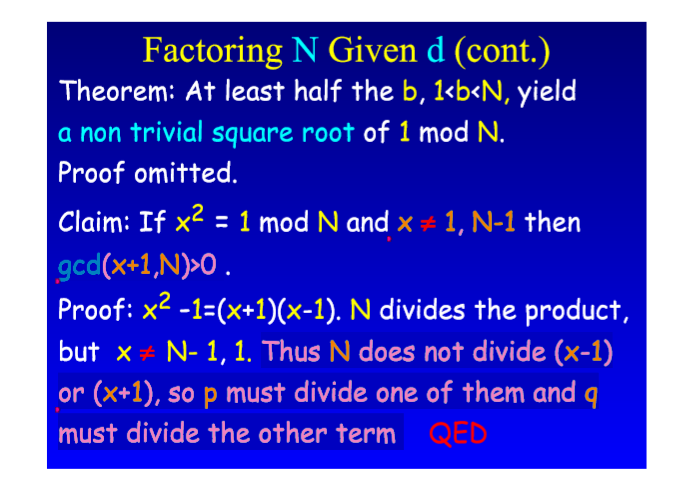
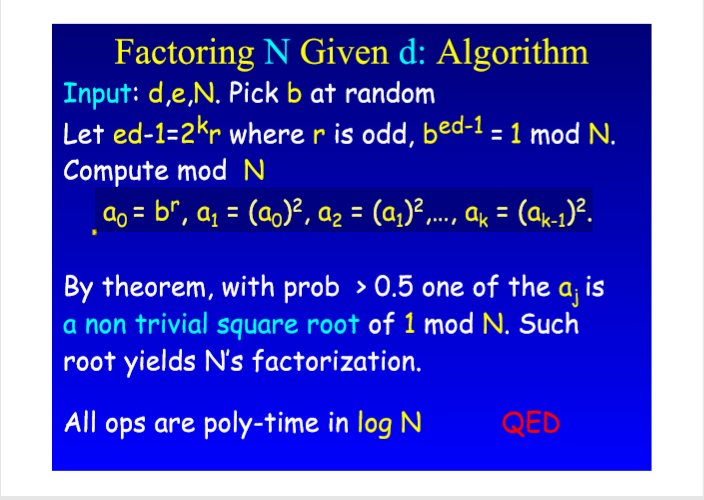
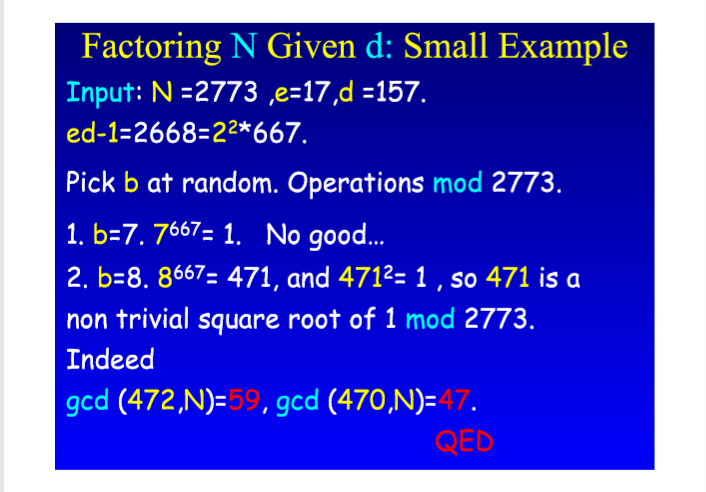
后来看到一篇博客(http://jackyc.top/2018/10/27/RSA-3/#more),里面有个参考文档(https://www.di-mgt.com.au/rsa_factorize_n.html),看完后知道原来知道(e,d,N)可以分解N,但是原理还不是很理解
找到了一个PDF,里面有原理的讲解,不过里面有些小地方和我的理解有出入,要么我错了,要么PDF出现小错误,最后还是按自己的理解和各种参考资料用python写了一下
e1 = 44379563805854841580307748547737435172564831877127303051909203409873174780389273150966396080375621148040275710628408649117613085199533826455458312376264659153842853015345496268736337902730232293424031775369541079662258443836020140399047886828048837071536578243295077689245549921524765222192270061081366989243
N = 188115669939527035644766943794256836704505079895306601119938518634078379404429524926183546093986493443422022468844644307633083886388295943602507953702360632321739073592477683222131866451975315695813478098524853358977564134499058448438525811837376172990710150323209055804682074564005014776547535959114226010493
e2 = 112465763139808984065405993827008716763974555200543206549100182421914260511395374512318119557311872118857352370325610769529155517454000609905909538235321637165438962672069969201523246380106126889874030417878823876408727390390051948217715186480658609481138938023687641185709391304878382079926539531855678365763
d2 = 55881649455902117785162844948995531081646760354831350250450328774662614334096209227124014992837725793190883247171284132768863157972472923057215962250425474753160669444247876851199006665484502793278672692761545198268608005712388135980371518592854149756626148424994498979112285655516912703587302199972664162731
c = 166834578157098529809222592291594342260836191039081705782260506690911922650094691879568641873546447862853989518762075081785381252999566333779425586950217410876199240677942391128773211264433855236931134494842223272683014826519273429450763047329625425561073729238027952900168036140503255431512655421527963913597 from random import randint
import gmpy2
def oddR(r):
while r%2==0:
r=r//2
return r def bits(b):
k=[]
while b:
if b%2!=0:
k.append(1)
else:
k.append(0)
b>>=1
k.reverse() #对于List等Sequence等类型的变量,比如此处的List变量,其内置函数reverse,是直接操作变量本身,调用reverse后,变量本身的值就是reverse后的值了,所以不能出现:kk=k.reverse()这样的操作
return k def quickmod(a,b,n): #a^b mod n 快速幂模n运算
f=1
k=bits(b)
for i in range(len(k)):
f=(f*f)%n
if k[i]:
f=(f*a)%n
return f def gcd(m,n):
while(n!=0):
m,n=n,m%n
return m def func(e,d,N):
k=e*d-1 #k是一个even number
r=oddR(k) #求出k=2^t*r中的r while True:
b=randint(2,N-1) #获取区间(2,N-1)的一个随机数
a=quickmod(b,r,N) #求解出b^r mod N的值
if a==1: #如果求得的a=1,则需要重新获取一个随机数b
continue
y=gcd(a-1,N)
if a>1 and y>1: #a要大于1,
q=N//y
return q
else:
r=r*2 #如果不满足的话,b就平方 a0 = br, a1 = (a0)^2, a2 = (a1)^2,…, ak = (ak-1)^2 #print(func(3,16971,25777))
def deciphering(e1,e2,d,N,c): #e1用来求解p和q,e2用来求解e2*d=1 (mod)
p=func(e1,d,N)
q=N//p
phi=N-(p+q)+1 #N和phi之间的关系 d=gmpy2.invert(e2,phi) #得到e2对应的私钥d
m=gmpy2.powmod(c,d,N)
return d,m d,m=deciphering(e2,e1,d2,N,c)
print("The private key is:",d)
print("The message is:",m)
结果:
明文为:131
密钥为:72818963105077629740558410461847080457967247911531271148355717844840007560618118158503931879141520737129717539191898962908710378608064897528018640573684648011556192613882739251759874374669201358126911422986850885586463283920904391451268159684723197972233648239891580239064904439566608991520126027809037410483
Given d and e, factorize N to attack RSA的更多相关文章
- URAL 1141. RSA Attack RSA加密演算法
标题来源:URAL 1141. RSA Attack 意甲冠军:给你e n c 并有m^e = c(mod n) 求 m 思路:首先学习RSA算法 here 过程大致是 1.发送的信息是m 2.随机选 ...
- 1141. RSA Attack(RSA)
1141 越来越喜欢数论了 很有意思 先看个RSA的介绍 RSA算法是一种非对称密码算法,所谓非对称,就是指该算法需要一对密钥,使用其中一个加密,则需要用另一个才能解密. RSA的算法涉及三个参数,n ...
- id0-rsa WP合集
忙里偷闲做做题wwwwwwwwwwwww Intro to Hashing Intro to PGP Hello PGP Hello OpenSSL Intro to RSA Caesar Hello ...
- 【Cocos2d-x for WP8 学习整理】(2)Cocos2d-Html5 游戏 《Fruit Attack》 WP8移植版 开源
这一阵花了些时间,把 cocos2d-html5 里的sample 游戏<Fruit Attack>给移植到了WP8上来,目前已经实现了基本的功能,但是还有几个已知的bug,比如WP8只支 ...
- Web 服务器 low bandth DOS attack
https://www.owasp.org/images/0/04/Roberto_Suggi_Liverani_OWASPNZDAY2010-Defending_against_applicatio ...
- CF 701B Cells Not Under Attack(想法题)
题目链接: 传送门 Cells Not Under Attack time limit per test:2 second memory limit per test:256 megabyte ...
- ASP.NET Padding Oracle Attack EXP
#!/usr/bin/perl## PadBuster v0.3 - Automated script for performing Padding Oracle attacks# Brian Hol ...
- 人机接口设备攻击(HID Attack)
人机接口设备攻击(HID Attack) HID Attack是最近几年流行的一类攻击方式.HID是Human Interface Device的缩写,意思是人机接口设备.它是对鼠标.键盘.游戏手 ...
- Codeforces Round #364 (Div. 2) B. Cells Not Under Attack
B. Cells Not Under Attack time limit per test 2 seconds memory limit per test 256 megabytes input st ...
随机推荐
- django的url配置
在一个请求到达的时候,最先达到的就是视图层,然后根据url映射到视图函数.这一部分我们来说明url的配置. 概述 为了给一个应用设计URL,你需要创建一个Python 模块,通常称为URLconf(U ...
- git小技巧--如何从其他分支merge个别文件或文件夹
在实际工作中,一个大型的项目或版本迭代可能不是一次上线,可能会分好几次上线,这时候就会涉及创建多个分支,进行分别开发. 创建分支 功能分为2个分支,分别为A.B. A上面有个列表页功能 B上面有个详情 ...
- 《论vue在前后端分离项目中的实践之年终总结》
我是2014年的时候开始了解知道的vue,当时vue还不太成熟,想用但是又怕自己hold不住,况且那时候vue还没有成熟的(路由.验证.ui组件)插件,社区也是不温不火的,再说也没有合适的机遇让我去项 ...
- linux 函数库使用
程序函数库可分为3种类型:静态函 数库(static libraries).共享函数库(shared libraries)和动态加载函数库(dynamically loaded libraries) ...
- Codeforces 839B Game of the Rows - 贪心
Daenerys Targaryen has an army consisting of k groups of soldiers, the i-th group contains ai soldie ...
- CentOS7 安装git服务器
在CentOS7系统中安装git服务器有两种方法,分别为yum安装和下载git安装包手动安装,这篇文章只有下载git安装包手动安装方法. 方法一:使用yum安装 暂无 方法二:下载git安装包手动安装 ...
- (转)tomcat架构&session共享
(二期)16.tomcat的整体架构与session共享方案 [课程16]tomcat...共享.xmind47.6KB [课程16]tomcat...流程.xmind0.6MB [课程16]tomc ...
- Windows常用的CMD命令
mspaint 打开画图 write 打开写字板 explorer 打开文件资源管理器 notepad 打开记事本 devmgmt.msc 打开设备管理器 regedit 打开注册表编辑器 Mscon ...
- [HDU 2520] 我是菜鸟,我怕谁(不一样的for循环)
题目链接:http://acm.hdu.edu.cn/showproblem.php?pid=2520 //学学不一样的for循环 #include<iostream> #include& ...
- Java基础【冒泡、选择排序、二分查找】
冒泡排序的思路就是前一个和后一个进行比较,如果大的就交换位置 大的数字后浮 如 12 8 5 31 第一轮 8 5 12 31 第二轮 5 8 ...
