170810、spring+springmvc+Interceptor+jwt+redis实现sso单点登录
在分布式环境中,如何支持PC、APP(ios、android)等多端的会话共享,这也是所有公司都需要的解决方案,用传统的session方式来解决,我想已经out了,我们是否可以找一个通用的方案,比如用传统cas来实现多系统之间的sso单点登录或使用oauth的第三方登录方案? 今天给大家简单讲解一下使用spring拦截器Interceptor机制、jwt认证方式、redis分布式缓存实现sso单点登录,闲话少说,直接把步骤记录下来分享给大家:
1. 引入jwt的相关jar包,在项目pom.xml中引入:
<dependency>
<groupId>com.auth0</groupId>
<artifactId>java-jwt</artifactId>
<version>2.2.0</version>
</dependency>
2. 拦截器配置:
<mvc:interceptor>
<mvc:mapping path="${adminPath}/**" />
<mvc:exclude-mapping path="${adminPath}/rest/login"/>
<bean class="com.ml.honghu.interceptor.LoginInterceptor" />
</mvc:interceptor>
3. 编写jwt的加密或者解密工具类:
public class JWT {
private static final String SECRET = "HONGHUJWT1234567890QWERTYUIOPASDFGHJKLZXCVBNM";
private static final String EXP = "exp";
private static final String PAYLOAD = "payload";
//加密
public static <T> String sign(T object, long maxAge) {
try {
final JWTSigner signer = new JWTSigner(SECRET);
final Map<String, Object> claims = new HashMap<String, Object>();
ObjectMapper mapper = new ObjectMapper();
String jsonString = mapper.writeValueAsString(object);
claims.put(PAYLOAD, jsonString);
claims.put(EXP, System.currentTimeMillis() + maxAge);
return signer.sign(claims);
} catch(Exception e) {
return null;
}
}
//解密
public static<T> T unsign(String jwt, Class<T> classT) {
final JWTVerifier verifier = new JWTVerifier(SECRET);
try {
final Map<String,Object> claims= verifier.verify(jwt);
if (claims.containsKey(EXP) && claims.containsKey(PAYLOAD)) {
String json = (String)claims.get(PAYLOAD);
ObjectMapper objectMapper = new ObjectMapper();
return objectMapper.readValue(json, classT);
}
return null;
} catch (Exception e) {
return null;
}
}
}
PS:这个加密工具类是我从网上找的,如果各位要修改,可以按照自己业务修改即可。
4. 创建Login.java对象,用来进行jwt的加密或者解密:
public class Login implements Serializable{
/**
*
*/
private static final long serialVersionUID = 1899232511233819216L;
/**
* 用户id
*/
private String uid;
/**
* 登录用户名
*/
private String loginName;
/**
* 登录密码
*/
private String password;
public Login(){
super();
}
public Login(String uid, String loginName, String password){
this.uid = uid;
this.loginName = loginName;
this.password = password;
}
public String getUid() {
return uid;
}
public void setUid(String uid) {
this.uid = uid;
}
public String getLoginName() {
return loginName;
}
public void setLoginName(String loginName) {
this.loginName = loginName;
}
public String getPassword() {
return password;
}
public void setPassword(String password) {
this.password = password;
}
}
5. 定义RedisLogin对象,用来通过uid往redis进行user对象存储:
public class RedisLogin implements Serializable{
/**
*
*/
private static final long serialVersionUID = 8116817810829835862L;
/**
* 用户id
*/
private String uid;
/**
* jwt生成的token信息
*/
private String token;
/**
* 登录或刷新应用的时间
*/
private long refTime;
public RedisLogin(){
}
public RedisLogin(String uid, String token, long refTime){
this.uid = uid;
this.token = token;
this.refTime = refTime;
}
public String getUid() {
return uid;
}
public void setUid(String uid) {
this.uid = uid;
}
public String getToken() {
return token;
}
public void setToken(String token) {
this.token = token;
}
public long getRefTime() {
return refTime;
}
public void setRefTime(long refTime) {
this.refTime = refTime;
}
}
6. 编写LoginInterceptor.java拦截器
public class LoginInterceptor implements HandlerInterceptor{
public boolean preHandle(HttpServletRequest request, HttpServletResponse response, Object handler)
throws Exception {
PrintWriter writer = null;
HandlerMethod method = null;
try {
method = (HandlerMethod) handler;
} catch (Exception e) {
writer = response.getWriter();
ResponseVO responseVO = ResponseCode.buildEnumResponseVO(ResponseCode.REQUEST_URL_NOT_SERVICE, false);
responseMessage(response, writer, responseVO);
return false;
}
IsLogin isLogin = method.getMethodAnnotation(IsLogin.class);
if(null == isLogin){
return true;
}
response.setCharacterEncoding("utf-8");
String token = request.getHeader("token");
String uid = request.getHeader("uid");
//token不存在
if(StringUtils.isEmpty(token)) {
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.LOGIN_TOKEN_NOT_NULL, false);
responseMessage(response, writer, responseVO);
return false;
}
if(StringUtils.isEmpty(uid)){
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.USERID_NOT_NULL, false);
responseMessage(response, writer, responseVO);
return false;
}
Login login = JWT.unsign(token, Login.class);
//解密token后的loginId与用户传来的loginId判断是否一致
if(null == login || !StringUtils.equals(login.getUid(), uid)){
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.USERID_NOT_UNAUTHORIZED, false);
responseMessage(response, writer, responseVO);
return false;
}
//验证登录时间
RedisLogin redisLogin = (RedisLogin)JedisUtils.getObject(uid);
if(null == redisLogin){
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.RESPONSE_CODE_UNLOGIN_ERROR, false);
responseMessage(response, writer, responseVO);
return false;
}
if(!StringUtils.equals(token, redisLogin.getToken())){
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.USERID_NOT_UNAUTHORIZED, false);
responseMessage(response, writer, responseVO);
return false;
}
//系统时间>有效期(说明已经超过有效期)
if (System.currentTimeMillis() > redisLogin.getRefTime()) {
writer = response.getWriter();
ResponseVO responseVO = LoginResponseCode.buildEnumResponseVO(LoginResponseCode.LOGIN_TIME_EXP, false);
responseMessage(response, writer, responseVO);
return false;
}
//重新刷新有效期
redisLogin = new RedisLogin(uid, token, System.currentTimeMillis() + 60L* 1000L* 30L);
JedisUtils.setObject(uid , redisLogin, 360000000);
return true;
}
public void postHandle(HttpServletRequest request, HttpServletResponse response, Object handler,
ModelAndView modelAndView) throws Exception {
}
public void afterCompletion(HttpServletRequest request, HttpServletResponse response, Object handler, Exception ex)
throws Exception {
}
private void responseMessage(HttpServletResponse response, PrintWriter out, ResponseVO responseVO) {
response.setContentType("application/json; charset=utf-8");
JSONObject result = new JSONObject();
result.put("result", responseVO);
out.print(result);
out.flush();
out.close();
}
}
7. 定义异常的LoginResponseCode
public enum LoginResponseCode {
USERID_NOT_NULL(3001,"用户id不能为空."),
LOGIN_TOKEN_NOT_NULL(3002,"登录token不能为空."),
USERID_NOT_UNAUTHORIZED(3003, "用户token或ID验证不通过"),
RESPONSE_CODE_UNLOGIN_ERROR(421, "未登录异常"),
LOGIN_TIME_EXP(3004, "登录时间超长,请重新登录");
// 成员变量
private int code; //状态码
private String message; //返回消息
// 构造方法
private LoginResponseCode(int code,String message) {
this.code = code;
this.message = message;
}
public int getCode() {
return code;
}
public void setCode(int code) {
this.code = code;
}
public String getMessage() {
return message;
}
public void setMessage(String message) {
this.message = message;
}
public static ResponseVO buildEnumResponseVO(LoginResponseCode responseCode, Object data) {
return new ResponseVO(responseCode.getCode(),responseCode.getMessage(),data);
}
public static Map<String, Object> buildReturnMap(LoginResponseCode responseCode, Object data) {
Map<String, Object> map = new HashMap<String, Object>();
map.put("code", responseCode.getCode());
map.put("message", responseCode.getMessage());
map.put("data", data);
return map;
}
}
8. 编写统一sso单点登录接口:
@RequestMapping(value = "/login", method = RequestMethod.POST)
public Map<String, Object> login(@RequestBody JSONObject json){
String loginName = json.optString("loginName");
String password = json.optString("password");
//校验用户名不能为空
if(StringUtils.isEmpty(loginName)){
return MemberResponseCode.buildReturnMap(MemberResponseCode.RESPONSE_CODE_USER_NAME_IS_NOT_EMPTY, null);
}
//校验用户密码不能为空
if(StringUtils.isEmpty(password)){
return MemberResponseCode.buildReturnMap(MemberResponseCode.RESPONSE_CODE_PWD_CAN_NOT_BE_EMPTY, null);
}
//根据用户名查询数据库用户信息
User user = systemService.getBaseUserByLoginName(loginName);
//用户名或密码不正确
if(null == user){
return MemberResponseCode.buildReturnMap(MemberResponseCode.RESPONSE_CODE_USER_VALIDATE_NO_SUCCESS, false);
}
boolean isValidate = systemService.validatePassword(password, user.getPassword());
if(!isValidate){
return MemberResponseCode.buildReturnMap(MemberResponseCode.RESPONSE_CODE_USER_VALIDATE_NO_SUCCESS, false);
}
if(isValidate){
//HttpSession session =request.getSession(false);
Login login = new Login(user.getId(), user.getLoginName(), user.getPassword());
//给用户jwt加密生成token
String token = JWT.sign(login, 60L* 1000L* 30L);
Map<String,Object> result =new HashMap<String,Object>();
result.put("loginToken", token);
result.put("userId", user.getId());
result.put("user", user); //保存用户信息到session
//session.setAttribute(user.getId() + "@@" + token, user);
//重建用户信息
this.rebuildLoginUser(user.getId(), token);
return ResponseCode.buildReturnMap(ResponseCode.RESPONSE_CODE_LOGIN_SUCCESS, result);
} return ResponseCode.buildReturnMap(ResponseCode.USER_LOGIN_PWD_ERROR, false);
}
9. 测试sso单点登录:
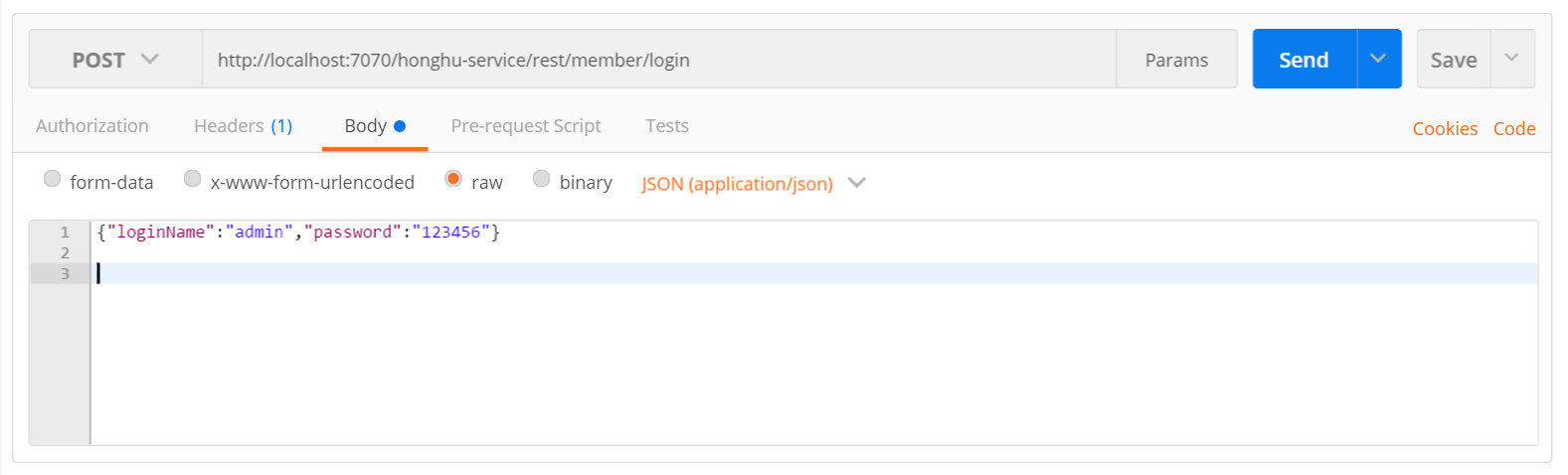
返回结果集:
{
"message": "用户登录成功",
"data": {
"loginToken": "eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJleHAiOjE1MDkzODA1OTU0NTksInBheWxvYWQiOiJ7XCJ1aWRcIjpcIjExXCIsXCJsb2dpbk5hbWVcIjpcImFkbWluXCIsXCJwYXNzd29yZFwiOlwiZjU0NGQxM2QyY2EwNDU5ZGQ0ZTU1NzVjNmZkYWIzMzM0MzE1MWFlZjgwYmE5ZTNiN2U1ZjM2MzJcIn0ifQ.56L60WtxHXSu9vNs6XsWy5zbmc3kP_IWG1YpReK50DM",
"userId": "11",
"user": {
"QQ":"2147775633",
"id": "11",
"isNewRecord": false,
"remarks": "",
"createDate": "2017-08-08 08:08:08",
"updateDate": "2017-10-29 11:23:50",
"loginName": "admin",
"no": "00012",
"name": "admin",
"email": "2147775633@qq.com",
"phone": "400000000",
"mobile": "13888888888",
"userType": "",
"loginIp": "0:0:0:0:0:0:0:1",
"loginDate": "2017-10-30 10:48:06",
"loginFlag": "1",
"photo": "",
"idCard": "420888888888888888",
"oldLoginIp": "0:0:0:0:0:0:0:1",
"oldLoginDate": "2017-10-30 10:48:06",
"roleNames": "",
"admin": false
}
},
"code": 200
}
原文地址:http://2147775633.iteye.com/blog/2398104
170810、spring+springmvc+Interceptor+jwt+redis实现sso单点登录的更多相关文章
- 简单使用redis实现sso单点登录
前面几篇分享了nosql只mongodb,今天简单分享另一个nosql神兵redis. 主要模仿sso单点登录,将登录人信息写入redis.话不多说,直接上马,驾. /// <summary&g ...
- 使用JWT+RSA完成SSO单点登录
无状态登录原理 1.1.什么是有状态? 有状态服务,即服务端需要记录每次会话的客户端信息,从而识别客户端身份,根据用户身份进行请求的处理,典型的设计如tomcat中的session. 例如登录:用户登 ...
- SpringSecurityOAuth使用JWT Token实现SSO单点登录
⒈认证服务器 1.添加pom依赖 <dependency> <groupId>org.springframework.boot</groupId> <arti ...
- redis实现SSO单点登录,集群,分布式锁
https://blog.csdn.net/aussme/article/details/80660443
- 第04项目:淘淘商城(SpringMVC+Spring+Mybatis)【第十天】(单点登录系统实现)
https://pan.baidu.com/s/1bptYGAb#list/path=%2F&parentPath=%2Fsharelink389619878-229862621083040 ...
- Spring Security OAuth2 SSO 单点登录
基于 Spring Security OAuth2 SSO 单点登录系统 SSO简介 单点登录(英语:Single sign-on,缩写为 SSO),又译为单一签入,一种对于许多相互关连,但是又是各自 ...
- .NET基于Redis缓存实现单点登录SSO的解决方案[转]
一.基本概念 最近公司的多个业务系统要统一整合使用同一个登录,这就是我们耳熟能详的单点登录,现在就NET基于Redis缓存实现单点登录做一个简单的分享. 单点登录(Single Sign On),简称 ...
- .NET基于Redis缓存实现单点登录SSO的解决方案
一.基本概念 最近公司的多个业务系统要统一整合使用同一个登录,这就是我们耳熟能详的单点登录,现在就NET基于Redis缓存实现单点登录做一个简单的分享. 单点登录(Single Sign On),简称 ...
- Redis缓存实现单点登录SSO
.NET基于Redis缓存实现单点登录SSO的解决方案 .NET基于Redis缓存实现单点登录SSO的解决方案 一.基本概念 最近公司的多个业务系统要统一整合使用同一个登录,这就是我们耳熟能详的单 ...
随机推荐
- Line云端全自动加好友机器人
一个 LINE 帐号可以加入 5,000 名好友,让这些 5,000 名好友收到 LINE 的主动提醒,好友会看到我的头像.主页照片.姓名与状态消息等,这种行为称为 LINE 的曝光. 如果我们要针对 ...
- mysql中使用show variables同时查询多个参数值?show variables的使用?
需求描述: 今天在查mysq关于连接数的问题,想要通过一个show variables命令同时查出来多个值.在此记录下. 操作过程: 1.通过show variables语句的like可以匹配多个值或 ...
- python类和模块区别,python命名空间
在python中,类可以提供模块级别之下的命名空间. 如果一个模块写很多函数,某些函数之间共同完成一组功能,用类会看起来更清晰,在调用时候也会更好,对于ide补全有更小范围的限定提示. 类提供 继承 ...
- 让Json更懂中文(JSON_UNESCAPED_UNICODE)
我们知道, 用PHP的json_encode来处理中文的时候, 中文都会被编码, 变成不可读的, 类似”\u***”的格式, 还会在一定程度上增加传输的数据量. <?php echo json_ ...
- 一致性Hash算法原理及C#代码实现
一.一致性Hash算法原理 基本概念 一致性哈希将整个哈希值空间组织成一个虚拟的圆环,如假设某哈希函数H的值空间为0-2^32-1(即哈希值是一个32位无符号整形),整个哈希空间环如下: 整个空间按顺 ...
- 8 -- 深入使用Spring -- 2... Spring的“零配置”支持
8.2 Spring的“零配置”支持 Spring支持使用Annotation来代替XML配置文件.
- grid简单布局
<!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8&quo ...
- ios开发之--NSDictionary和NSData之间的互转/NSString和NSData之间的互转
NSDictionary转NSData,代码如下: +(NSData*)returnDataWith:(NSDictionary*)dict { NSData *data = [NSJSONSeria ...
- Bypass ngx_lua_waf SQL注入防御(多姿势)
0x00 前言 ngx_lua_waf是一款基于ngx_lua的web应用防火墙,使用简单,高性能.轻量级.默认防御规则在wafconf目录中,摘录几条核心的SQL注入防御规则: select.+ ...
- mongo数据库查询结果不包括_id字段方法
db.GPRS_PRODUCT_HIS_FEE.find({"条件字段" : "412171211145135"},{_id:0}) db.GPRS_PRODU ...
