windows内核提权
Windows by default are vulnerable to several vulnerabilities that could allow an attacker to execute malicious code in order to abuse a system. From the other side patching systems sufficiently is one of the main problems in security. Even if an organization has a patching policy in place if important patches are not implemented immediately this can still give short window to an attacker to exploit a vulnerability and escalate his privileges inside a system and therefore inside the network.
This article will discuss how to identify missing patches related to privilege escalation and the necessary code to exploit the issue.
Discovery of Missing Patches
The discovery of missing patches can be identified easily either through manual methods or automatic. Manually this can be done easily be executing the following command which will enumerate all the installed patches.
wmic qfe get Caption,Description,HotFixID,InstalledOn
The output will be similar to this:
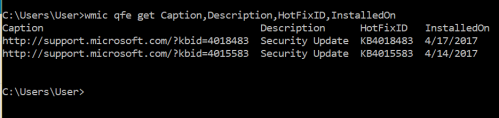
Enumeration of Installed Patches
The HotFixID can be used in correlation with the table below in order to discover any missing patches related to privilege escalation. As the focus is on privilege escalation the command can be modified slightly to discover patches based on the KB number.
wmic qfe get Caption,Description,HotFixID,InstalledOn | findstr /C:"KB3136041" /C:"KB4018483"
Alternatively this can be done automatically via Metasploit, Credential Nessus Scan or via a custom script that will look for missing patches related to privilege escalation.
Metasploit
There is a Metasploit module which can quickly identify any missing patches based on the Knowledge Base number and specifically patches for which there is a Metasploit module.
post/windows/gather/enum_patches

Metasploit – Patches Enumeration
Windows Exploit Suggester
Gotham Digital Security released a tool with the name Windows Exploit Suggester which compares the patch level of a system against the Microsoft vulnerability database and can be used to identify those exploits that could lead to privilege escalation. The only requirement is that requires the system information from the target.
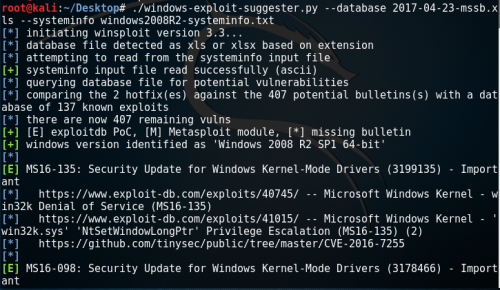
Windows Exploit Suggester
PowerShell
There is also a PowerShell script which target to identify patches that can lead to privilege escalation. This script is called Sherlock and it will check a system for the following:
- MS10-015 : User Mode to Ring (KiTrap0D)
- MS10-092 : Task Scheduler
- MS13-053 : NTUserMessageCall Win32k Kernel Pool Overflow
- MS13-081 : TrackPopupMenuEx Win32k NULL Page
- MS14-058 : TrackPopupMenu Win32k Null Pointer Dereference
- MS15-051 : ClientCopyImage Win32k
- MS15-078 : Font Driver Buffer Overflow
- MS16-016 : ‘mrxdav.sys’ WebDAV
- MS16-032 : Secondary Logon Handle
- CVE-2017-7199 : Nessus Agent 6.6.2 – 6.10.3 Priv Esc
The output of this tool can be seen below:
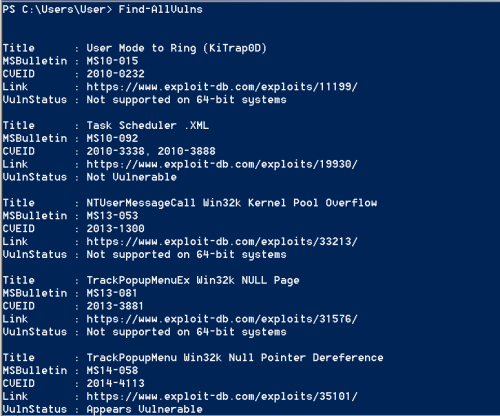
Sherlock – Missing Patches
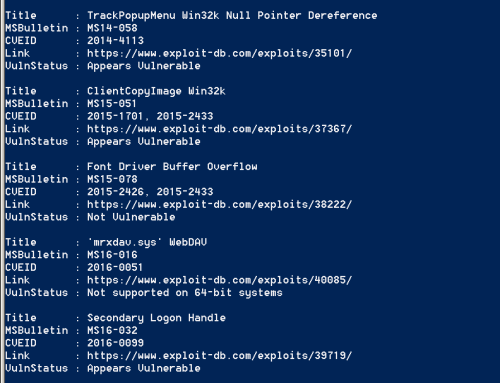
Sherlock – Identification of Privilege Escalation Patches
Privilege Escalation Table
The following table has been compiled to assist in the process of privilege escalation due to lack of sufficient patching.
| Operating System | Description | Security Bulletin | KB | Exploit |
|---|---|---|---|---|
| Windows Server 2016 | Windows Kernel Mode Drivers | MS16-135 | 3199135 | Exploit |
| Windows Server 2008 ,7,8,10 Windows Server 2012 | Secondary Logon Handle | MS16-032 | 3143141 | GitHub |
| Windows Server 2008, Vista, 7 | WebDAV | MS16-016 | 3136041 | Github |
| Windows Server 2003, Windows Server 2008, Windows 7, Windows 8, Windows 2012 | Windows Kernel Mode Drivers | MS15-051 | 3057191 | GitHub |
| Windows Server 2003, Windows Server 2008, Windows Server 2012, 7, 8 | Win32k.sys | MS14-058 | 3000061 | GitHub |
| Windows Server 2003, Windows Server 2008, 7, 8, Windows Server 2012 | AFD Driver | MS14-040 | 2975684 | Python |
| Windows XP, Windows Server 2003 | Windows Kernel | MS14-002 | 2914368 | Metasploit |
| Windows Server 2003, Windows Server 2008, 7, 8, Windows Server 2012 | Kernel Mode Driver | MS13-005 | 2778930 | Metasploit |
| Windows Server 2008, 7 | Task Scheduler | MS10-092 | 2305420 | Metasploit |
| Windows Server 2003, Windows Server 2008, 7, XP | KiTrap0D | MS10-015 | 977165 | Exploit |
| Windows Server 2003, XP | NDProxy | MS14-002 | 2914368 | Exploit |
| Windows Server 2003, Windows Server 2008, 7, 8, Windows Server 2012 | Kernel Driver | MS15-061 | 3057839 | Github |
| Windows Server 2003, XP | AFD.sys | MS11-080 | 2592799 | EXE |
| Windows Server 2003, XP | NDISTAPI | MS11-062 | 2566454 | ExploitDB |
| Windows Server 2003, Windows Server 2008, 7, 8, Windows Server 2012 | RPC | MS15-076 | 3067505 | Github |
| Windows Server 2003, Windows Server 2008, 7, 8, Windows Server 2012 | Hot Potato | MS16-075 | 3164038 | GitHub |
| Windows Server 2003, Windows Server 2008, 7, XP | Kernel Driver | MS15-010 | 3036220 | GitHub |
| Windows Server 2003, Windows Server 2008, 7, XP | AFD.sys | MS11-046 | 2503665 | EXE |
windows内核提权的更多相关文章
- msf利用- windows内核提权漏洞
windows内核提权漏洞 环境: Kali Linux(攻击机) 192.168.190.141 Windows2003SP2(靶机) 192.168.190.147 0x01寻找可利用的exp 实 ...
- Windows原理深入学习系列-Windows内核提权
这是[信安成长计划]的第 22 篇文章 0x00 目录 0x01 介绍 0x02 替换 Token 0x03 编辑 ACL 0x04 修改 Privileges 0x05 参考文章 继续纠正网上文章中 ...
- 2018-2019-2 20165215《网络对抗技术》Exp10 Final Windows本地内核提权+Exploit-Exercises Nebula学习与实践
目录 PART ONE :Windows本地内核提权 漏洞概述 漏洞原理 漏洞复现 windbg调试本地内核 查看SSDT表和SSDTShadow表 查看窗口站结构体信息 利用Poc验证漏洞 漏洞利用 ...
- 9.CVE-2016-5195(脏牛)内核提权漏洞分析
漏洞描述: 漏洞编号:CVE-2016-5195 漏洞名称:脏牛(Dirty COW) 漏洞危害:低权限用户利用该漏洞技术可以在全版本Linux系统上实现本地提权 影响范围:Linux内核>=2 ...
- Linux本地内核提权漏洞复现(CVE-2019-13272)
Linux本地内核提权漏洞复现(CVE-2019-13272) 一.漏洞描述 当调用PTRACE_TRACEME时,ptrace_link函数将获得对父进程凭据的RCU引用,然后将该指针指向get_c ...
- CVE-2019-13272:Linux本地内核提权漏洞复现
0x00 简介 2019年07月20日,Linux正式修复了一个本地内核提权漏洞.通过此漏洞,攻击者可将普通权限用户提升为Root权限. 0x01 漏洞概述 当调用PTRACE_TRACEME时,pt ...
- ssh远程端口转发&&windows系统提权之信息收集&&网安工具分享(部分)
一.ssh远程端口转发 背景:当我们在渗透过程中,获取到内网的一台仅有内网IP的服务器后,我们可以通过ssh隧道,将内网某个主机的端口进行远程转发 1.网络拓扑图 假设获取的服务器为web服务器,we ...
- windows下提权基础
拿到webshell很多时候代表渗透的开始,下面带来windows提权基础 环境:虚拟机 win7系统 首先:查看权限whoami 我们知道windows的高权限应该是administrator和sy ...
- 新Windows本地提权漏洞学习(CVE-2019-0841)
1.这是一个啥漏洞? 睁眼一看,妈呀本地提权,快加入本地提权漏洞利用包里,速度加入.github连接我就不发了.担心被认为是传播黑客工具,咱们在这里单纯学习一下漏洞的原理和部分源代码. 2.文件读写权 ...
随机推荐
- JS基础,课堂作业,计算器
网页内的简单计算器 <script> var a = parseInt(prompt("请输入第一个数字:")); var b = parseInt(prompt(&q ...
- XAF-如何调整按钮的显示顺序
在 XAF 应用程序用户界面,按钮位于按钮容器内.您可以使用 ActionBase.Category属性和应用程序模型 ActionDesign |ActionToContainerMapping 节 ...
- Unity 编辑器扩展 Chapter2—Gizmos
二. 使用Gizoms绘制网格及矩阵转换使用 1. 创建Leve类,作为场景控制类: using UnityEngine; //使用namespace方便脚本管理 namespace RunAndJu ...
- TCP/IP三次握手四次挥手分析
流程图 全部11种状态 客户端独有的:(1)SYN_SENT (2)FIN_WAIT1 (3)FIN_WAIT2 (4)CLOSING (5)TIME_WAIT 服务器独有的:(1)LISTEN (2 ...
- 常用monkey_app稳定性
Monkey稳定性测试 1 前言 为方便快速上手Monkey测试相关问题,针对测试中发现的Monkey问题进行了整理总结,供定位Monkey参考. 2 关于Monkey测试 2 ...
- Java实现网上商城
// 第一个JavaWeb项目 //练手项目没有使用框架 github下载 https://github.com/dejavudwh/Online-Shopping 项目截图 1.基本实现了购物网站该 ...
- MongoDB开启权限认证
MongoDB默认安装完后,如果在配置文件中没有加上auth = true,是没有用户权限认证的,这样对于一个数据库来说是相对不安全的,尤其是在外网的情况下. 接下来是配置权限的过程: //切入到 ...
- spring-boot 项目整合logback
使用spring-boot项目中添加日志输出,java的日志输出一共有两个大的方案log4j/log4j2 ,logback.log4j2算是对log4j的一个升级版本. 常规做法是引入slf4j作为 ...
- PHP使用static关键字声明静态属性和静态方法
PHP使用static关键字声明静态属性和静态方法 在PHP中,通过static关键字修饰的成员属性和成员方法被称为静态属性和静态方法. 静态属性和静态方法不需要在被类实例化的情况下就可以直接使用. ...
- 微软职位内部推荐-Principal Development Lead - SharePoint
微软近期Open的职位: SharePoint is a multi-billion dollar enterprise business that has grown from an on-prem ...
