CMDB学习之四 ——DEBUG模式
定义一个debug,进行解析调试,到测试文件
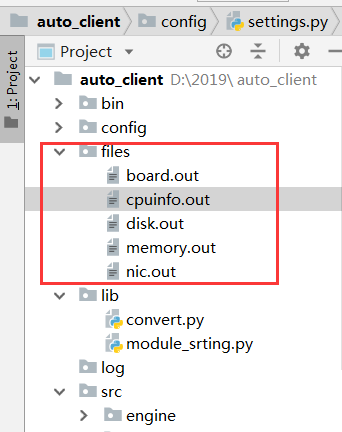
配置文件,配置debug模式,定义环境变量,
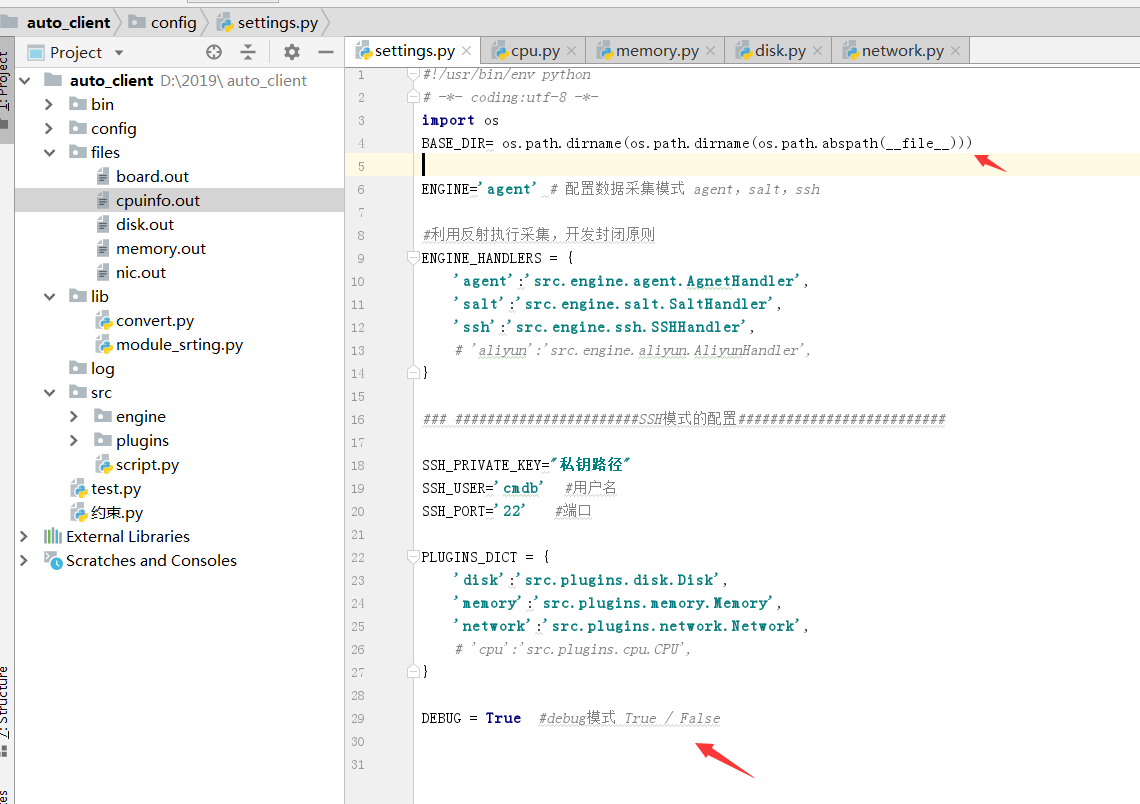
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os
BASE_DIR= os.path.dirname(os.path.dirname(os.path.abspath(__file__))) ENGINE='agent' # 配置数据采集模式 agent,salt,ssh #利用反射执行采集,开发封闭原则
ENGINE_HANDLERS = {
'agent':'src.engine.agent.AgnetHandler',
'salt':'src.engine.salt.SaltHandler',
'ssh':'src.engine.ssh.SSHHandler',
# 'aliyun':'src.engine.aliyun.AliyunHandler',
} ### #######################SSH模式的配置########################## SSH_PRIVATE_KEY="私钥路径"
SSH_USER='cmdb' #用户名
SSH_PORT='' #端口 PLUGINS_DICT = {
'disk':'src.plugins.disk.Disk',
'memory':'src.plugins.memory.Memory',
'network':'src.plugins.network.Network',
# 'cpu':'src.plugins.cpu.CPU',
} DEBUG = True #debug模式 True / False
内存采集解析,内存采集中使用的 convert,导入文件在lib目录下
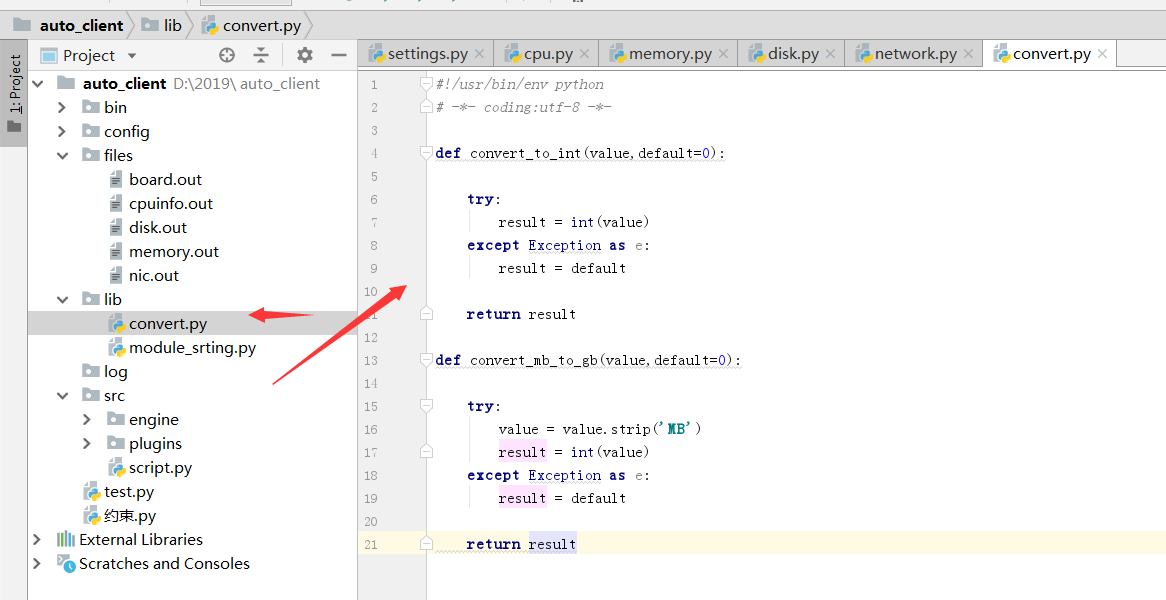
#!/usr/bin/env python
# -*- coding:utf-8 -*- def convert_to_int(value,default=0): try:
result = int(value)
except Exception as e:
result = default return result def convert_mb_to_gb(value,default=0): try:
value = value.strip('MB')
result = int(value)
except Exception as e:
result = default return result
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os
from .base import BasePlugin
from lib import convert
class Memory(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-内存
:return:
'''
print("执行win方法")
ret = handler.cmd('wmic memphysical list brief',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-内存
# :return:
# '''
# print("执行Linux方法")
# ret = handler.cmd('free',hostname)[0:10]
# return ret
def linux(self, handler, hostname): if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'memory.out'), 'r').read()
else:
shell_command = "sudo dmidecode -q -t 17 2>/dev/null"
output = handler.cmd(shell_command, hostname)
return self.parse(output) def parse(self, content):
"""
解析shell命令返回结果
:param content: shell 命令结果
:return:解析后的结果
"""
ram_dict = {}
key_map = {
'Size': 'capacity',
'Locator': 'slot',
'Type': 'model',
'Speed': 'speed',
'Manufacturer': 'manufacturer',
'Serial Number': 'sn', }
devices = content.split('Memory Device')
for item in devices:
item = item.strip()
if not item:
continue
if item.startswith('#'):
continue
segment = {}
lines = item.split('\n\t')
for line in lines:
if len(line.split(':')) > 1:
key, value = line.split(':')
else:
key = line.split(':')[0]
value = ""
if key in key_map:
if key == 'Size':
segment[key_map['Size']] = convert.convert_mb_to_gb(value, 0)
else:
segment[key_map[key.strip()]] = value.strip()
ram_dict[segment['slot']] = segment return ram_dict
磁盘采集解析
# !/usr/bin/env python
# -*- coding:utf-8 -*-
from .base import BasePlugin
import os,re
class Disk(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-磁盘
:return:
'''
print("执行win方法")
ret = handler.cmd('wmic diskdrive',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-磁盘
# :return:
# '''
# print("执行Linux方法")
#
# ret = handler.cmd('df -h',hostname)[0:10]
# return ret
def linux(self, handler, hostname): if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'disk.out'), 'r').read()
else:
shell_command = "sudo MegaCli -PDList -aALL" #根据执行的命令
output = handler.cmd(shell_command, hostname) return self.parse(output) def parse(self, content):
"""
解析shell命令返回结果
:param content: shell 命令结果
:return:解析后的结果
"""
response = {}
result = []
for row_line in content.split("\n\n\n\n"):
result.append(row_line)
for item in result:
temp_dict = {}
for row in item.split('\n'):
if not row.strip():
continue
if len(row.split(':')) != 2:
continue
key, value = row.split(':')
name = self.mega_patter_match(key)
if name:
if key == 'Raw Size':
raw_size = re.search('(\d+\.\d+)', value.strip())
if raw_size:
temp_dict[name] = raw_size.group()
else:
raw_size = ''
else:
temp_dict[name] = value.strip()
if temp_dict:
response[temp_dict['slot']] = temp_dict
return response @staticmethod
def mega_patter_match(needle):
grep_pattern = {'Slot': 'slot', 'Raw Size': 'capacity', 'Inquiry': 'model', 'PD Type': 'pd_type'}
for key, value in grep_pattern.items():
if needle.startswith(key):
return value
return False
网络采集解析
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os,re
from .base import BasePlugin
class Network(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-网卡
:return:
'''
print("执行win方法")
ret = handler.cmd('ipconfig',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-网卡
# :return:
# '''
# print("执行Linux方法")
# ret = handler.cmd('ifconfig',hostname)[0:10]
# return ret
def linux(self, handler, hostname):
if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'nic.out'), 'r').read()
interfaces_info = self._interfaces_ip(output)
else:
interfaces_info = self.linux_interfaces(handler)
self.standard(interfaces_info)
return interfaces_info def linux_interfaces(self, handler):
'''
Obtain interface information for *NIX/BSD variants
'''
ifaces = dict()
ip_path = 'ip'
if ip_path:
cmd1 = handler.cmd('sudo {0} link show'.format(ip_path))
cmd2 = handler.cmd('sudo {0} addr show'.format(ip_path))
ifaces = self._interfaces_ip(cmd1 + '\n' + cmd2)
return ifaces def which(self, exe):
def _is_executable_file_or_link(exe):
# check for os.X_OK doesn't suffice because directory may executable
return (os.access(exe, os.X_OK) and
(os.path.isfile(exe) or os.path.islink(exe))) if exe:
if _is_executable_file_or_link(exe):
# executable in cwd or fullpath
return exe # default path based on busybox's default
default_path = '/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin'
search_path = os.environ.get('PATH', default_path)
path_ext = os.environ.get('PATHEXT', '.EXE')
ext_list = path_ext.split(';') search_path = search_path.split(os.pathsep)
if True:
# Add any dirs in the default_path which are not in search_path. If
# there was no PATH variable found in os.environ, then this will be
# a no-op. This ensures that all dirs in the default_path are
# searched, which lets salt.utils.which() work well when invoked by
# salt-call running from cron (which, depending on platform, may
# have a severely limited PATH).
search_path.extend(
[
x for x in default_path.split(os.pathsep)
if x not in search_path
]
)
for path in search_path:
full_path = os.path.join(path, exe)
if _is_executable_file_or_link(full_path):
return full_path return None def _number_of_set_bits_to_ipv4_netmask(self, set_bits): # pylint: disable=C0103
'''
Returns an IPv4 netmask from the integer representation of that mask. Ex. 0xffffff00 -> '255.255.255.0'
'''
return self.cidr_to_ipv4_netmask(self._number_of_set_bits(set_bits)) def cidr_to_ipv4_netmask(self, cidr_bits):
'''
Returns an IPv4 netmask
'''
try:
cidr_bits = int(cidr_bits)
if not 1 <= cidr_bits <= 32:
return ''
except ValueError:
return '' netmask = ''
for idx in range(4):
if idx:
netmask += '.'
if cidr_bits >= 8:
netmask += ''
cidr_bits -= 8
else:
netmask += '{0:d}'.format(256 - (2 ** (8 - cidr_bits)))
cidr_bits = 0
return netmask def _number_of_set_bits(self, x):
'''
Returns the number of bits that are set in a 32bit int
'''
# Taken from http://stackoverflow.com/a/4912729. Many thanks!
x -= (x >> 1) & 0x55555555
x = ((x >> 2) & 0x33333333) + (x & 0x33333333)
x = ((x >> 4) + x) & 0x0f0f0f0f
x += x >> 8
x += x >> 16
return x & 0x0000003f def _interfaces_ip(self, out):
'''
Uses ip to return a dictionary of interfaces with various information about
each (up/down state, ip address, netmask, and hwaddr)
'''
ret = dict()
right_keys = ['name', 'hwaddr', 'up', 'netmask', 'ipaddrs'] def parse_network(value, cols):
'''
Return a tuple of ip, netmask, broadcast
based on the current set of cols
'''
brd = None
if '/' in value: # we have a CIDR in this address
ip, cidr = value.split('/') # pylint: disable=C0103
else:
ip = value # pylint: disable=C0103
cidr = 32 if type_ == 'inet':
mask = self.cidr_to_ipv4_netmask(int(cidr))
if 'brd' in cols:
brd = cols[cols.index('brd') + 1]
return (ip, mask, brd) groups = re.compile('\r?\n\\d').split(out)
for group in groups:
iface = None
data = dict() for line in group.splitlines():
if ' ' not in line:
continue
match = re.match(r'^\d*:\s+([\w.\-]+)(?:@)?([\w.\-]+)?:\s+<(.+)>', line)
if match:
iface, parent, attrs = match.groups()
if 'UP' in attrs.split(','):
data['up'] = True
else:
data['up'] = False
if parent and parent in right_keys:
data[parent] = parent
continue cols = line.split()
if len(cols) >= 2:
type_, value = tuple(cols[0:2]) iflabel = cols[-1:][0]
if type_ in ('inet',):
if 'secondary' not in cols:
ipaddr, netmask, broadcast = parse_network(value, cols)
if type_ == 'inet':
if 'inet' not in data:
data['inet'] = list()
addr_obj = dict()
addr_obj['address'] = ipaddr
addr_obj['netmask'] = netmask
addr_obj['broadcast'] = broadcast
data['inet'].append(addr_obj)
else:
if 'secondary' not in data:
data['secondary'] = list()
ip_, mask, brd = parse_network(value, cols)
data['secondary'].append({
'type': type_,
'address': ip_,
'netmask': mask,
'broadcast': brd,
})
del ip_, mask, brd
elif type_.startswith('link'):
data['hwaddr'] = value
if iface:
if iface.startswith('pan') or iface.startswith('lo') or iface.startswith('v'):
del iface, data
else:
ret[iface] = data
del iface, data
return ret def standard(self, interfaces_info): for key, value in interfaces_info.items():
ipaddrs = set()
netmask = set()
if not 'inet' in value:
value['ipaddrs'] = ''
value['netmask'] = ''
else:
for item in value['inet']:
ipaddrs.add(item['address'])
netmask.add(item['netmask'])
value['ipaddrs'] = '/'.join(ipaddrs)
value['netmask'] = '/'.join(netmask)
del value['inet']
CMDB学习之四 ——DEBUG模式的更多相关文章
- python flask框架学习——开启debug模式
学习自:知了课堂Python Flask框架——全栈开发 1.flask的几种debug模式的方法 # 1.app.run 传参debug=true app.run(debug=True) #2 设置 ...
- 8086汇编语言学习(二) 8086汇编开发环境搭建和Debug模式介绍
1. 8086汇编开发环境搭建 在上篇博客中简单的介绍了8086汇编语言.工欲善其事,必先利其器,在8086汇编语言正式开始学习之前,先介绍一下如何搭建8086汇编的开发环境. 汇编语言设计之初是用于 ...
- 初学node.js,安装nodemon,学习debug模式,安装cpu-stat
1.运行node 文件 node .\01.js 文件内容 console.log('aaaa'); 2.因为每次更新文件都需要重新,所以安装nodemon npm i ...
- flask学习(四):debug模式
一. 设置debug模式 1. flask 1.0之前 在app.run()中传入一个关键字参数debug,app.run(debug=True),就设置当前项目为debug模式 2. flask 1 ...
- odoo Windows10启动debug模式报错(Process finished with exit code -1073740940 (0xC0000374))
之前用win10系统,安装odoo总是启动debug模式启动不起来很恼火. 报错问题:Process finished with exit code -1073740940 (0xC0000374) ...
- Flask debug 模式 PIN 码生成机制安全性研究笔记
Flask debug 模式 PIN 码生成机制安全性研究笔记 0x00 前言 前几天我整理了一个笔记:Flask开启debug模式等于给黑客留了后门,就Flask在生产网络中开启debug模式可能产 ...
- Eclipse Debug模式的开启与关闭问题简析_java - JAVA
文章来源:嗨学网 敏而好学论坛www.piaodoo.com 欢迎大家相互学习 默认情况下,eclipse中右键debug,当运行到设置的断点时会自动跳到debug模式下.但由于我的eclipse环境 ...
- IDea 工具debug模式详细使用说明
IDea 工具debug模式详细使用说明 IDEA中如何使用debug调试项目 一步一步详细教程 Debug用来追踪代码的运行流程,通常在程序运行过程中出现异常,启用Debug模式可以分析定位异常发生 ...
- 手机改 user模式为debug模式
logcat 是Android中一个命令行工具,可用于监控手机应用程序的log信息.网上相关的教学很多,这里只想把自己折腾 2 部手机(一个是三星S4 I9500 港水,Android 5.01,一个 ...
随机推荐
- bzoj1090 字符串折叠
问题描述 折叠的定义如下: 1. 一个字符串可以看成它自身的折叠.记作S S 2. X(S)是X(X>1)个S连接在一起的串的折叠.记作X(S) SSSS…S(X个S). 3. 如果A ...
- springboot实现热部署,修改代码不用重启服务
1.引入热部署依赖 <!-- 热部署模块 --> <dependency> <groupId>org.springframework.boot</groupI ...
- HBase快照、Snapshots 淘宝快照
淘宝在2011年之前所有的后端持久化存储基本上与我们所认知的意义, 大量存于 mysql .少量 oracle mongdb 等,使用mysql 的原因相信各位也很熟悉了. 开源.社区庞大.解决方 ...
- hdu 思维风暴
点击打开链接 偶然在杭电上看到的题目,数学题.好像是一道六年级奥赛题目,反正我是没有想出来,也知道往那上面想.就是找不到规律啊.学习了网上的方法, 这道题须要求出来多添加的点,就是与之前每条边添加的点 ...
- Raphaeljs入门到精通(一)
<!DOCTYPE html> <html xmlns="http://www.w3.org/1999/xhtml"> <head> <t ...
- BZOJ 2242 [SDOI2011]计算器 BSGS+高速幂+EXGCD
题意:id=2242">链接 方法: BSGS+高速幂+EXGCD 解析: BSGS- 题解同上.. 代码: #include <cmath> #include <c ...
- strchr函数的实现而不是使用
刚刚在写一个程序的时候突然须要用到定位到一个字符串中第一次出现某个字符的位置,于是就找到了strchr()函数,之前从没实用过的,^_^当然我能够直接调用就可以.可是拥有良好程序素质的洗衣袋决定要想实 ...
- 概率编程语言(Probabilistic Programming Languages)库 —— edward
注意:tensorflow api 在 1.1.0 以后迎来重大变化,edward 的稳定版依赖于 tensorflow 1.1.0. edward是一个支持概率建模.推断的 Python 第三方库, ...
- 如何判断自己IP是内网IP还是外网IP
tcp/ip协议中,专门保留了三个IP地址区域作为私有地址,其地址范围如下: 10.0.0.0/8:10.0.0.0-10.255.255.255 172.16.0.0/12:172.16.0.0- ...
- 2.AngularJS-验证
转自:https://www.cnblogs.com/best/p/6225621.html 一.验证 angularJS中提供了许多的验证指令,可以轻松的实现验证,只需要在表单元素上添加相应的ng属 ...
