A barrier for Mobile Forensics - Samsung Secure Folder
Since I mentioned about "Second Space", let's take a look at Samsung "Secure Folder". This built-in feature for Samsung smartphones is a secret space for storing images, videos, documents and apps. And most important of it, it's encrypted.
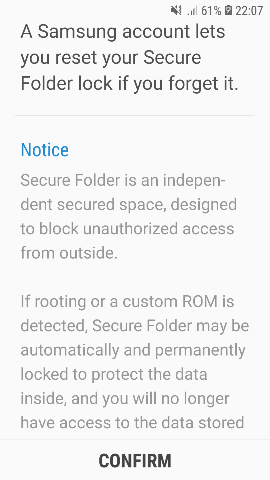
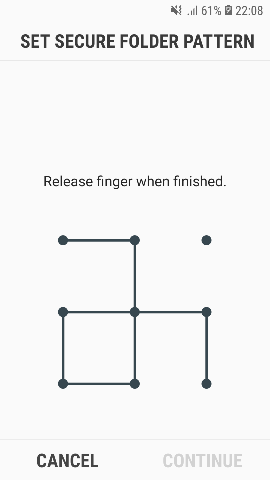
All you have to do is sign in with your Samsung cloud account and create a secure folder. You could decide the authenication method such as PIN, Password or Pattern Lock.
Suspects may make copies of Apps such as WhatsApp, WeChat, LINE...in "Secure Folder" for communicatoin with his/her parterns in crime. No ones knows what's inside the "Secure Folder". Even mobile forensic tools could extract all files from a Samsung smartphone, guess what? Those data in "Secure Folder" is meaningless because all data is encrypted. Only you could know is filename and its path, but you will never know its content.

It sounds like there is nothing you could do about decrypting Samsung "Secure Folder". Fortunately you could try to access the suspect's Samsung Cloud and you still got a chance to find backup data in "Secure Folder".
A barrier for Mobile Forensics - Samsung Secure Folder的更多相关文章
- An iOS zero-click radio proximity exploit odyssey
NOTE: This specific issue was fixed before the launch of Privacy-Preserving Contact Tracing in iOS 1 ...
- Life cycle of plist in Lockdown changes dramatically in iOS 10
We could take advantage of plist to bypass Trust Relationship so as to extract data from a iDevice. ...
- 网络-04-端口号-linux端口详解大全--TCP注册端口号大全
# John Murphy <john.m.murphy&mci.com>afs3-fileserver 7000/tcp file server itselfafs3-files ...
- 利用nginx来屏蔽指定的user_agent的访问以及根据user_agent做跳转
对于做国内站的我来说,我不希望国外蜘蛛来访问我的网站,特别是个别垃圾蜘蛛,它们访问特别频繁.这些垃圾流量多了之后,严重浪费服务器的带宽和资源.通过判断user agent,在nginx中禁用这些蜘蛛可 ...
- App Naver Line 5.3 add new features - "True Delete"
Line is getting more and more popular in recent years. Lots of peope use Line, so do "Suspects& ...
- The most interesting feature of iPhone X - FaceID
No doubt everybody knows that iPhone 8 & iPhone X appear on the market. A feature called FaceID ...
- [译] iOS 11.4.1 Beta:全新的USB限制模式
(Source/原文链接 https://blog.elcomsoft.com/2018/06/ios-11-4-1-beta-usb-restricted-mode-has-arrived/) 作者 ...
- C#设计模式(4)——抽象工厂模式(Abstract Factory)
简单工厂模式: 简单工厂模式的工厂类随着产品类的增加需要增加额外的代码 工厂方法模式: 工厂方法模式每个具体工厂类只完成单个实例的创建,所以它具有很好的可扩展性 但是在实际应用中,一个工厂不止会创建单 ...
- 3G 4G 5G中的网络安全问题——文献汇总
Modeling and Analysis of RRC-Based Signalling Storms in 3G Networks 还是使用状态机模型来做恶意UE识别 https://san.ee ...
随机推荐
- 用Visual Studio2019自定义项目模板
项目模板简介 众所周知,在我们使用VS新建项目时,都需要选择一个项目模板,如下图: 我们选择完项目模板进行创建,创建完成之后,可以发现项目中已经包含了一些基础的文件.例如MVC: 可以看到,MVC项目 ...
- .NET IoC模式依赖反转(DIP)、控制反转(Ioc)、依赖注入(DI)
依赖倒置原则(DIP) 依赖倒置(Dependency Inversion Principle,缩写DIP)是面向对象六大基本原则之一.他是指一种特定的的解耦形式,使得高层次的模块不依赖低层次的模块的 ...
- hdu2336 (匈牙利最大匹配+二分)
Describe 这是一个简单的游戏,在一个n*n的矩阵中,找n个数使得这n个数都在不同的行和列里并且要求这n个数中的最大值和最小值的差值最小. Input 输入一个整数T表示T组数据. 对于每组数据 ...
- 1.Spring 框架概述
目录 Spring 框架概述 1 我们所说的 "Spring "是什么意思 2. Spring和Spring框架的历史 3. 设计理念 4.反馈和贡献 5.开始使用 Spring ...
- java ->大的数据运算(BigInteger)
大数据运算 BigInteger java中long型为最大整数类型,对于超过long型的数据如何去表示呢.在Java的世界中,超过long型的整数已经不能被称为整数了,它们被封装成BigIntege ...
- Sentinel源码解析四(流控策略和流控效果)
引言 在分析Sentinel的上一篇文章中,我们知道了它是基于滑动窗口做的流量统计,那么在当我们能够根据流量统计算法拿到流量的实时数据后,下一步要做的事情自然就是基于这些数据做流控.在介绍Sentin ...
- POJ1321棋盘问题(DFS)
Description 在一个给定形状的棋盘(形状可能是不规则的)上面摆放棋子,棋子没有区别.要求摆放时任意的两个棋子不能放在棋盘中的同一行或者同一列,请编程求解对于给定形状和大小的棋盘,摆放k个棋子 ...
- Proteus仿真时出现Cannot open‘C:\Users\...\LISA7605.SDF’的错误
目录 打开环境变量 更改环境变量 打开环境变量 更改环境变量 "用户变量"和"系统变量"栏里,找到TEMP与TMP,都改成%SystemRoot%\TEMP 改 ...
- 数独c++
#include <bits/stdc++.h> using namespace std; const int maxn = 10; bool maps[maxn][maxn], row[ ...
- hdu2138 How many prime numbers 米勒测试
hdu2138 How many prime numbers #include <bits/stdc++.h> using namespace std; typedef long long ...
