Apache 配置 https
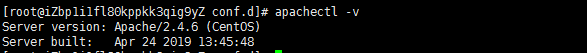
本人当前的Apache版本是:
由于我是yum安装的http,默认的http配置文件我就不多说了,
下面开始记录一下自己的线上配置过程:
1,进入/etc/httpd/conf.d目录,新建证书放置的目录cert,如下图:

说明:1.1: mi.conf 线上配置环境,我用的是虚拟:配置如图:

具体代码也粘贴出来,方便大家复制使用:
<VirtualHost *:80>
ServerAdmin admin@linuxeye.com
DocumentRoot "/home/www/longjing"
ServerName mi.mifbb.com
ErrorLog "/home/wwwlogs/error_mi.com.log"
CustomLog "/home/wwwlogs/access_mi.log" common
<IfModule mod_rewrite.c>
RewriteEngine on
RewriteCond %{SERVER_PORT} !^443$
RewriteRule (.*) https://%{SERVER_NAME}$1 [L,R=301]
</IfModule><Directory "/home/www/longjing">
SetOutputFilter DEFLATE
Options FollowSymLinks ExecCGI
Require all granted
AllowOverride All
DirectoryIndex index.html index.php
</Directory>
</VirtualHost>
1.2: ssl.conf 这个就是具体的ssl配置文件了,主要的配置在后面的较多,可以直接复制简单修改使用:
#lso provide SSL we have to listen to the
# the HTTPS port in addition.
#
Listen 443 https
##
## SSL Global Context
##
## All SSL configuration in this context applies both to
## the main server and all SSL-enabled virtual hosts.
### Pass Phrase Dialog:
# Configure the pass phrase gathering process.
# The filtering dialog program (`builtin' is a internal
# terminal dialog) has to provide the pass phrase on stdout.
SSLPassPhraseDialog exec:/usr/libexec/httpd-ssl-pass-dialog# Inter-Process Session Cache:
# Configure the SSL Session Cache: First the mechanism
# to use and second the expiring timeout (in seconds).
SSLSessionCache shmcb:/run/httpd/sslcache(512000)
SSLSessionCacheTimeout 300# Pseudo Random Number Generator (PRNG):
# Configure one or more sources to seed the PRNG of the
# SSL library. The seed data should be of good random quality.
# WARNING! On some platforms /dev/random blocks if not enough entropy
# is available. This means you then cannot use the /dev/random device
# because it would lead to very long connection times (as long as
# it requires to make more entropy available). But usually those
# platforms additionally provide a /dev/urandom device which doesn't
# block. So, if available, use this one instead. Read the mod_ssl User
# Manual for more details.
SSLRandomSeed startup file:/dev/urandom 256
SSLRandomSeed connect builtin
#SSLRandomSeed startup file:/dev/random 512
#SSLRandomSeed connect file:/dev/random 512
#SSLRandomSeed connect file:/dev/urandom 512#
# Use "SSLCryptoDevice" to enable any supported hardware
# accelerators. Use "openssl engine -v" to list supported
# engine names. NOTE: If you enable an accelerator and the
# server does not start, consult the error logs and ensure
# your accelerator is functioning properly.
#
SSLCryptoDevice builtin
#SSLCryptoDevice ubsec##
## SSL Virtual Host Context
###<VirtualHost _default_:443>
# General setup for the virtual host, inherited from global configuration
#DocumentRoot "/var/www/html"
#ServerName www.example.com:443# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
#ErrorLog logs/ssl_error_log
#TransferLog logs/ssl_access_log
#LogLevel warn# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
#SSLEngine on# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
#SSLProtocol all -SSLv2 -SSLv3# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
#SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA# Speed-optimized SSL Cipher configuration:
# If speed is your main concern (on busy HTTPS servers e.g.),
# you might want to force clients to specific, performance
# optimized ciphers. In this case, prepend those ciphers
# to the SSLCipherSuite list, and enable SSLHonorCipherOrder.
# Caveat: by giving precedence to RC4-SHA and AES128-SHA
# (as in the example below), most connections will no longer
# have perfect forward secrecy - if the server's key is
# compromised, captures of past or future traffic must be
# considered compromised, too.
#SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5
#SSLHonorCipherOrder on# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
#SSLCertificateFile /etc/pki/tls/certs/localhost.crt# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
#SSLCertificateKeyFile /etc/pki/tls/private/localhost.key# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
#SSLCertificateChainFile /etc/pki/tls/certs/server-chain.crt# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location># SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
#<Files ~ "\.(cgi|shtml|phtml|php3?)$">
# SSLOptions +StdEnvVars
#</Files>
#<Directory "/var/www/cgi-bin">
# SSLOptions +StdEnvVars
#</Directory># SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
#BrowserMatch "MSIE [2-5]" \
# nokeepalive ssl-unclean-shutdown \
# downgrade-1.0 force-response-1.0# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
#CustomLog logs/ssl_request_log \
# "%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"#</VirtualHost>
<VirtualHost *:443>
ServerAdmin webmaster@dummy-host2.example.com
DocumentRoot "/home/www/longjing"
ServerName mi.mifbb.com
ErrorLog "/home/wwwlogs/mifbb.com-error443_log"
CustomLog "/home/wwwlogs/mifbb-access443_log" common
SSLEngine on
SSLProtocol -all +TLSv1 +TLSv1.1 +TLSv1.2
SSLHonorCipherOrder on
SSLCipherSuite HIGH:!RC4:!MD5:!aNULL:!eNULL:!NULL:!DH:!EDH:!EXP:+MEDIUM
#SSLCertificateFile /etc/httpd/conf.d/cert/1110500__mifbb.com_public.crt
#SSLCertificateKeyFile /etc/httpd/conf.d/cert/1110500__mifbb.com.key
#SSLCertificateChainFile /etc/httpd/conf.d/cert/1110500__mifbb.com_chain.crtSSLCertificateFile /etc/httpd/conf.d/cert/1110500__mifbb.com_public.crt
SSLCertificateKeyFile /etc/httpd/conf.d/cert/1110500__mifbb.com.key
SSLCertificateChainFile /etc/httpd/conf.d/cert/1110500__mifbb.com_chain.crt#SSLCertificateFile /etc/httpd/conf.d/cert/2_fxqdk.crt
#SSLCertificateKeyFile /etc/httpd/conf.d/cert/3_fxqdk.key
#SSLCertificateChainFile /etc/httpd/conf.d/cert/1_fxqdk_bundle.crt
<Directory "/home/www/longjing">
SetOutputFilter DEFLATE
Options FollowSymLinks ExecCGI
Require all granted
AllowOverride All
DirectoryIndex index.html index.php
</Directory>
</VirtualHost>
1.3: cert 目录里的截图如下:

到目前为止httpps的服务器简单配置可以使用了,本人的是线上环境,做个记录方便以后查看。
Apache 配置 https的更多相关文章
- Apache配置HTTPS功能
apache配置https 一.yum 安装openssl和openssl-devel,httpd-devel 二.生成证书(也可以从公司的证书颁发机构获取): #建立服务器密钥 openssl ge ...
- Windows上为Apache配置HTTPS
Windows上为Apache配置HTTPS 转 https://www.cnblogs.com/tianzijiaozi/p/7582671.html 1. 安装OpenSSL: Windo ...
- Linux下Apache配置HTTPS功能
Apache配置HTTPS功能 转 https://www.cnblogs.com/liaojiafa/p/6028816.html 一.yum 安装openssl和openssl-devel,ht ...
- Apache配置https
Apache配置https 之前一直用的是Tomcat,今天突然接到任务要给Apache配置https证书,因为小程序要用.下面把过程列出来以备后续查看. 1.首先你得有ssl证书,没有的可以去购买, ...
- 在linux下的apache配置https协议,开启ssl连接
环境:linux 配置https协议,需要2大步骤: 一.生成服务器证书 1.安装openssl软件 yum install -y openssl mod_ssl 2.生成服务器私匙,生成server ...
- apache 配置https(转)
主要讲述在windows下apache配置SSL以实现http转换为https SSL: SSl是为Http传输提供安全的协议,通过证书认证来确保客户端和网站服务器之间的数据是安全.也就是说在SSL下 ...
- lamp之apache配置https访问
配置apache 使用https 注:怕其他人由于路径的原因出问题,首先声明一下,本人apache的安装目录为 : /usr/local/httpd2.4.25,如果不是,请参考进行配置 注: 对于如 ...
- Linux Apache配置https访问
配置https访问 该环境是rh254课程配套的一个环境,不过配置方法步骤相同. 要求: 使用虚拟主机技术部署两个网站: 网站1: 绑定域名 www0.example.com 目录在 /srv/www ...
- Apache 配置Https 转发Tomcat Http
Apache 相对于nginx的配置对比起来相当复杂啦,朋友之前的系统使用的是Apache需要增加一个虚拟主机,主要配置从Apache转发Tomcat. 首先需要拆解下步骤: Apache 支持Htt ...
- apache配置https协议
安装openssl有两种方式,第一种直接下载安装包,装上就可运行:第二种可以自己下载源码,自己编译.下面对两种方式均进行详细描述. 一.下载和安装openss 方法一:直接使用openssl安装包 W ...
随机推荐
- Shrio多Realm认证及认证策略
在大型的系统中,安全数据可能会存放在多个数据库中,而且每个数据的加密方式也是不一样的,那么单一的Realm就无法完成. 这时,就需要用到多Realm认证了,多Realm又涉及到认证策略,及在多个Rea ...
- 微信小程序踩坑日记1——调用微信授权窗口
0. 引言 微信小程序为了优化用户体验,取消了在进入小程序时立马出现授权窗口.需要用户主动点击按钮,触发授权窗口. 那么,在我实践过程中,出现了以下问题. . 无法弹出授权窗口 . 希望在用户已经授权 ...
- Java EE API
百度云:链接:http://pan.baidu.com/s/1nvTlMLb 密码:vulq 官方下载网址:http://www.oracle.com/technetwork/java/jav ...
- window平台下 cmd 命令窗口的编码设置
在WINDOWS上打开控制台界面,发现默认的编码是GBK,这样有时候写完的代码运行的时候就会出码,基于此,查阅各方资料,终于得出两种方案. 一.临时解决方案(只针对本次会话有效) 1. 打开控制台,输 ...
- Java基础之方法
方法 某段代码经常使用,可以使用大括号将这段代码包括起来,起个名字,以后就使用这个名字来代替这段代码. 定义格式: 修饰符 返回值类型 方法名(参数列表) { 方法体语句: return语句: } ...
- SpringBoot(18)---通过Lua脚本批量插入数据到Redis布隆过滤器
通过Lua脚本批量插入数据到布隆过滤器 有关布隆过滤器的原理之前写过一篇博客: 算法(3)---布隆过滤器原理 在实际开发过程中经常会做的一步操作,就是判断当前的key是否存在. 那这篇博客主要分为三 ...
- Java类的加载 链接 初始化
原文地址 Java类的加载.链接和初始化.Java字节代码的表现形式是字节数组(byte[]),而Java类在JVM中的表现形式是java.lang.Class类的对象.一个Java类从字节代码到能够 ...
- javaweb入门-----request与response的作用
request对象和request对象的原理 1.request和response对象request对象和request对象的原理时由服务器创建的,我们来使用它们 2.request对象是来获取请求消 ...
- spring autowrited注解
@Autowired 注释,它可以对类成员变量.方法及构造函数进行标注,完成自动装配的工作. 通过 @Autowired的使用来消除 set ,get方法.在使用@Autowired之前,我们对一个b ...
- django数据库事务
数据库原子操作 举个例子: 一个消费者在一个商户里刷信用卡消费,交易正常时,银行在消费者的账户里减去相应的款项,在商户的帐户加上相应的款项.但是如果银行从消费者的账户里扣完钱之后,还未在商户的帐户里加 ...
