hdu 4119 Isabella's Message
Isabella's Message
Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 K (Java/Others)
Total Submission(s): 1365 Accepted Submission(s): 400
The encrypted message is an N * N matrix, and each grid contains a character.
Steve uses a special mask to work as a key. The mask is N * N(where N is an even number) matrix with N*N/4 holes of size 1 * 1 on it.
The decrypt process consist of the following steps:
1. Put the mask on the encrypted message matrix
2. Write down the characters you can see through the holes, from top to down, then from left to right.
3. Rotate the mask by 90 degrees clockwise.
4. Go to step 2, unless you have wrote down all the N*N characters in the message matrix.
5. Erase all the redundant white spaces in the message.
For example, you got a message shown in figure 1, and you have a mask looks like figure 2. The decryption process is shown in figure 3, and finally you may get a message "good morning".
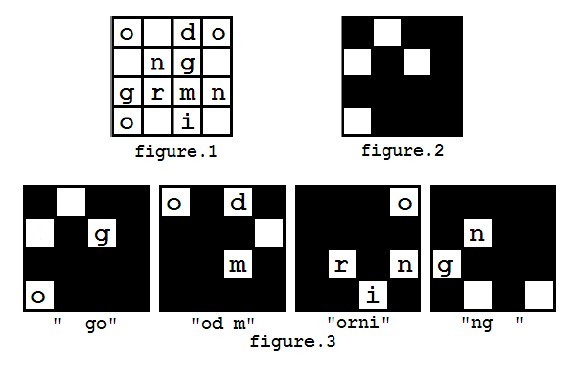
You can assume that the mask is always carefully chosen that each character in the encrypted message will appear exactly once during decryption.
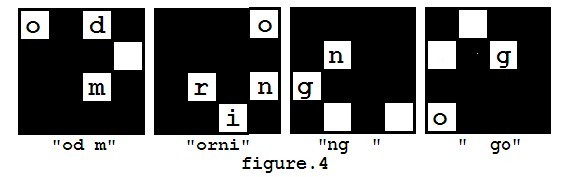
However, in the first step of decryption, there are several ways to put the mask on the message matrix, because the mask can be rotated (but not flipped). So you may get different results such as "od morning go" (as showed in figure 4), and you may also get other messages like "orning good m", "ng good morni".
Steve didn't know which direction of the mask should be chosen at the beginning, but after he tried all possibilities, he found that the message "good morning" is the only one he wanted because he couldn't recognize some words in the other messages. So he will always consider the message he can understand the correct one. Whether he can understand a message depends whether he knows all the words in the message. If there are more than one ways to decrypt the message into an understandable one, he will choose the lexicographically smallest one. The way to compare two messages is to compare the words of two messages one by one, and the first pair of different words in the two messages will determine the lexicographic order of them.
Isabella sends letters to Steve almost every day. As decrypting Isabella's message takes a lot of time, and Steve can wait no longer to know the content of the message, he asked you for help. Now you are given the message he received, the mask, and the list of words he already knew, can you write a program to help him decrypt it?
Each test case contains several lines.
The first line contains an even integer N(2 <= N <= 50), indicating the size of the matrix.
The following N lines each contains exactly N characters, reresenting the message matrix. The message only contains lowercase letters and periods('.'), where periods represent the white spaces.
You can assume the matrix contains at least one letter.
The followingN lines each containsN characters, representing the mask matrix. The asterisk('*') represents a hole, and period('.') otherwise. The next line contains an integer M(1 <= M <= 100), the number of words he knew.
Then the following M lines each contains a string represents a word. The words only contain lowercase letters, and its length will not exceed 20.
If Steve cannot understand the message, just print the Y as "FAIL TO DECRYPT".
4
o.do
.ng.
grmn
o.i.
.*..
*.*.
....
*...
2
good
morning
4
..lf
eoyv
oeou
vrer
..*.
.*..
....
*.*.
5
i
you
the
love
forever
4
.sle
s.c.
e.fs
..uu
*...
.*..
...*
..*.
1
successful
Case #2: love you forever
Case #3: FAIL TO DECRYPT
#include <iostream>
#include <stdio.h>
#include <string.h>
using namespace std;
#define MAXN 55
struct node {
char map[MAXN][MAXN];
};
int n,kk;char str[4][10000],lib[10000][25],anss[10000],stemp[10000];int strnum[4];
bool strflag[4];
node change(node a)
{
int i,j,ii,k;node b;
for(i=0,ii=0;i<n;i++,ii++)
{
for(j=n-1,k=0;j>=0;j--,k++)
{
b.map[ii][k]=a.map[j][i];
}
}
return b;
}
bool find(char str[])
{
int i;
for(i=0;i<kk;i++)
{
if(strcmp(str,lib[i])==0)
return true;
}
return false;
}
int main()
{
int tcase,i,j,i2,space,tt=1;
node a,b;
scanf("%d",&tcase);
while(tcase--)
{
memset(strnum,0,sizeof(strnum));
memset(strflag,true,sizeof(strflag));
for(i=0;i<4;i++)
{
memset(str[i],0,sizeof(str[i]));
}
scanf("%d",&n);
gets(stemp);
for(i=0;i<n;i++)
{
for(j=0;j<n;j++)
{
char c=getchar();
a.map[i][j]=c;
}
gets(stemp);
}
for(i=0;i<n;i++)
{
for(j=0;j<n;j++)
{
char c=getchar();
b.map[i][j]=c;
}
gets(stemp);
}
scanf("%d",&kk);
gets(stemp);
for(i=0;i<kk;i++)
{
scanf("%s",lib[i]);
}
memset(stemp,0,sizeof(stemp));
int space=0;node primeb=b;
for(i=0;i<4;i++)
{
bool flag=true;space=0;b=primeb;
for(j=0;j<4&&flag;j++)
{
for(int ii=0;ii<n&&flag;ii++)
for(int jj=0;jj<n&&flag;jj++)
{
if(b.map[ii][jj]=='*')
{
if(a.map[ii][jj]=='.'&&space>0)
{
stemp[space++]='\0';
if(!find(stemp))
{
flag=false;
strflag[i]=false;
}
else
{
str[i][strnum[i]++]=' ';
for(i2=0;i2<=space-2;i2++)
{
str[i][strnum[i]++]=stemp[i2];
}
}
space=0;
}
if(a.map[ii][jj]!='.')
{
stemp[space++]=a.map[ii][jj];
}
}
} b=change(b);
}
if(space>0&&flag)
{
stemp[space++]='\0';
if(!find(stemp))
{
flag=false;
strflag[i]=false;
}
else
{
str[i][strnum[i]++]=' ';
for(i2=0;i2<=space-2;i2++)
{
str[i][strnum[i]++]=stemp[i2];
}
}
space=0;
}
primeb=change(primeb);
}
bool flag=true;
for(i=0;i<4;i++)
{
if(strflag[i])
{
str[i][strnum[i]++]='\0';
if(flag)
{
strcpy(anss,str[i]);
flag=false;
}
if(strcmp(anss,str[i])>0)
strcpy(anss,str[i]);
}
}
if(!flag)
printf("Case #%d:%s\n",tt++,anss);
else
printf("Case #%d: FAIL TO DECRYPT\n",tt++);
}
return 0;
}
hdu 4119 Isabella's Message的更多相关文章
- hdu 4119 Isabella's Message 模拟题
Isabella's Message Time Limit: 20 Sec Memory Limit: 256 MB 题目连接 http://acm.hdu.edu.cn/showproblem.p ...
- hdu 3410 Passing the Message(单调队列)
题目链接:hdu 3410 Passing the Message 题意: 说那么多,其实就是对于每个a[i],让你找他的从左边(右边)开始找a[j]<a[i]并且a[j]=max(a[j])( ...
- hdu 4300 Clairewd’s message KMP应用
Clairewd’s message 题意:先一个转换表S,表示第i个拉丁字母转换为s[i],即a -> s[1];(a为明文,s[i]为密文).之后给你一串长度为n<= 100000的前 ...
- hdu 4300 Clairewd’s message(具体解释,扩展KMP)
题目链接:http://acm.hdu.edu.cn/showproblem.php?pid=4300 Problem Description Clairewd is a member of FBI. ...
- hdu 4300 Clairewd’s message(扩展kmp)
Problem Description Clairewd is a member of FBI. After several years concealing in BUPT, she interce ...
- HDU 4300 Clairewd’s message(KMP+思维)
题目链接:http://acm.hdu.edu.cn/showproblem.php?pid=4300 题目大意:题目大意就是给以一段字符xxxxzzz前面x部分是密文z部分是明文,但是我们不知道是从 ...
- 【HDU 4300 Clairewd’s message】
Clairewd is a member of FBI. After several years concealing in BUPT, she intercepted some important ...
- HDU - 3410 Passing the Message 单调递减栈
Passing the Message What a sunny day! Let’s go picnic and have barbecue! Today, all kids in “Sun Flo ...
- hdu 4300 Clairewd’s message 字符串哈希
Clairewd’s message Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 K (Java/Other ...
随机推荐
- 使用Spire PDF for .NET将HTML转换成PDF文档
目录 开发环境说明 Spire PDF for .NET (free edition)体验 资源下载 开发环境说明 Microsoft Visual Studio 2013 Ultimate Edit ...
- python 备份脚本
import osimport timesource= r"out_res.txt"target_dir= r"F:\python\Doc"target=tar ...
- 关于Scrapy框架的基本概念
Scrapy爬取网页基本概念 Scrapy爬取网页基本概念 怎么样用Scrapy生成project? scrapy startproject xxx 如何用Scrapy爬取网页? import scr ...
- js函数绑定同时,如何保留代码执行环境?
经常写js的程序员一定不会对下面这段代码感到陌生. var EventUtil = { addHandler : function(element, type, handler){ if(elemen ...
- latex 批量注释
在LaTex中的注释有3种方法: 1. 右键单击选中要注释的文本,选择 Insert Comment ,WinEdt 就会自动给选定的行添加 % ,完成段落文本的注释: 右键单击选中已经注释的文本,选 ...
- 组合框里添加复选框的方法(使用勾选的假象,用图片代替而已,并非QT原生支持)
组合框可以看作是列表框和文本框的组合,因其占据的空间少,使用操作方便,常被界面设计人员用于界面开发设计中,在有限个输入的条件下,组合框常用来代替文本框,这样从用户使用角度来看,更趋人性化,所见即所得. ...
- Flex和Servlet结合上传文件报错(二)
1.详细报错例如以下 一个表单域 不是一个表单域 java.io.FileNotFoundException: D:\MyEclipse\workspace\FlexFileUpload\Web\up ...
- Android 匿名共享内存C接口分析
在Android 匿名共享内存驱动源码分析中详细分析了匿名共享内存在Linux内核空间的实现,虽然内核空间实现了匿名共享内存,但仍然需要在用户空间为用户使用匿名共享内存提供访问接口.Android系统 ...
- python闭包以及装饰器
通俗的定义:如果在一个内部函数里,对在外部作用域(但不是在全局作用域)的变量进行引用,那么内部函数就被认为是闭包(closure).它只不过是个“内层”的函数,由一个名字(变量)来指代,而这个名字(变 ...
- c++类的实例化,有没有new的区别
A a; A * a = new a(); 以上两种方式皆可实现类的实例化,有new的区别在于: 1.前者在堆栈中分配内存,后者为动态内存分配,在一般应用中是没有什么区别的,但动态内存分配会使对象的可 ...
