★Kali信息收集~3.子域名系列
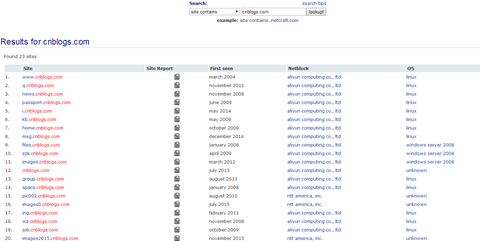
★3.1Netcraft :子域名查询
 官网:http://searchdns.netcraft.com/
官网:http://searchdns.netcraft.com/
输入要查询的域名,即可得知子域名
3.2Fierce :子域名查询
- 概述:
fierce 是使用多种技术来扫描目标主机IP地址和主机名的一个DNS服务器枚举工具。运用递归的方式来工作。它的工作原理是先通过查询本地DNS服务器来查找目标DNS服务器,然后使用目标DNS服务器来查找子域名。fierce的主要特点就是可以用来定位独立IP空间对应域名和主机名。
- 参数:
root@Kali:/home/dnt# fierce -h
fierce.pl (C) Copywrite 2006,2007 - By RSnake at http://ha.ckers.org/fierce/
Usage: perl fierce.pl [-dns example.com] [OPTIONS]
Overview:
Fierce is a semi-lightweight scanner that helps locate non-contiguous
IP space and hostnames against specified domains. It's really meant
as a pre-cursor to nmap, unicornscan, nessus, nikto, etc, since all
of those require that you already know what IP space you are looking
for. This does not perform exploitation and does not scan the whole
internet indiscriminately. It is meant specifically to locate likely
targets both inside and outside a corporate network. Because it uses
DNS primarily you will often find mis-configured networks that leak
internal address space. That's especially useful in targeted malware.
Options:
-connect Attempt to make http connections to any non RFC1918
(public) addresses. This will output the return headers but
be warned, this could take a long time against a company with
many targets, depending on network/machine lag. I wouldn't
recommend doing this unless it's a small company or you have a
lot of free time on your hands (could take hours-days).
Inside the file specified the text "Host:\n" will be replaced
by the host specified. Usage:
perl fierce.pl -dns example.com -connect headers.txt
-delay The number of seconds to wait between lookups.
-dns The domain you would like scanned.
-dnsfile Use DNS servers provided by a file (one per line) for
reverse lookups (brute force).
-dnsserver Use a particular DNS server for reverse lookups
(probably should be the DNS server of the target). Fierce
uses your DNS server for the initial SOA query and then uses
the target's DNS server for all additional queries by default.
-file A file you would like to output to be logged to.
-fulloutput When combined with -connect this will output everything
the webserver sends back, not just the HTTP headers.
-help This screen.
-nopattern Don't use a search pattern when looking for nearby
hosts. Instead dump everything. This is really noisy but
is useful for finding other domains that spammers might be
using. It will also give you lots of false positives,
especially on large domains.
-range Scan an internal IP range (must be combined with
-dnsserver). Note, that this does not support a pattern
and will simply output anything it finds. Usage:
perl fierce.pl -range 111.222.333.0-255 -dnsserver ns1.example.co
-search Search list. When fierce attempts to traverse up and
down ipspace it may encounter other servers within other
domains that may belong to the same company. If you supply a
comma delimited list to fierce it will report anything found.
This is especially useful if the corporate servers are named
different from the public facing website. Usage:
perl fierce.pl -dns examplecompany.com -search corpcompany,blahcompany
Note that using search could also greatly expand the number of
hosts found, as it will continue to traverse once it locates
servers that you specified in your search list. The more the
better.
-suppress Suppress all TTY output (when combined with -file).
-tcptimeout Specify a different timeout (default 10 seconds). You
may want to increase this if the DNS server you are querying
is slow or has a lot of network lag.
-threads Specify how many threads to use while scanning (default
is single threaded).
-traverse Specify a number of IPs above and below whatever IP you
have found to look for nearby IPs. Default is 5 above and
below. Traverse will not move into other C blocks.
-version Output the version number.
-wide Scan the entire class C after finding any matching
hostnames in that class C. This generates a lot more traffic
but can uncover a lot more information.
-wordlist Use a seperate wordlist (one word per line). Usage:
perl fierce.pl -dns examplecompany.com -wordlist dictionary.txt
- 实例:threads 是线程数,可以自己指定
 root@Kali:/home/dnt# fierce -dns cnblogs.com -threads 100
root@Kali:/home/dnt# fierce -dns cnblogs.com -threads 100Trying zone transfer first...
Unsuccessful in zone transfer (it was worth a shot)
Okay, trying the good old fashioned way... brute force
Checking for wildcard DNS...
** Found 99901599299.cnblogs.com at 42.121.252.58.
** High probability of wildcard DNS.
Now performing 2280 test(s)...
120.26.70.206 files.cnblogs.com
42.121.129.234 images.cnblogs.com
223.6.251.45 group.cnblogs.com
223.6.251.45 home.cnblogs.com
42.121.129.234 download.cnblogs.com
221.181.200.235 cdn.cnblogs.com
42.121.131.85 mail.cnblogs.com
42.121.129.234 downloads.cnblogs.com
223.6.251.45 news.cnblogs.com
223.6.251.45 ad.cnblogs.com
42.121.254.229 p.cnblogs.com
。。。。。。。。
★Kali信息收集~3.子域名系列的更多相关文章
- Kali信息收集系列:(都是我以前的笔记整理了一下,就没加水印,习惯就好)
好几天没发微信公众号了,今天一起发下.(最近有点事情) 前些天老业界的一位朋友问我一些Safe新时代信息收集的问题 逆天虽然好多年不干老本行,但隔段时间都会关注一下 于是就花了点时间整理了一下,你们就 ...
- ★Kali信息收集★8.Nmap :端口扫描
★Kali信息收集~ 0.Httrack 网站复制机 http://www.cnblogs.com/dunitian/p/5061954.html ★Kali信息收集~ 1.Google Hackin ...
- Kali信息收集
前言 渗透测试最重要的阶段之一就是信息收集,需要收集关于目标主机的基本细腻些.渗透测试人员得到的信息越多,渗透测试成功的概率也就越高. 一.枚举服务 1.1 DNS枚举工具DNSenum DNSenu ...
- ★Kali信息收集~★6.Dmitry:汇总收集
概述: DMitry(Deepmagic Information Gathering Tool)是一个一体化的信息收集工具.它可以用来收集以下信息: 1. 端口扫描 2. whois主机IP和域名信息 ...
- ★Kali信息收集~ 5.The Harvester:邮箱挖掘器
官网:http://www.edge-security.com 安装:apt-get install theHarvester 运行:终端输入 theharvester (小写) 用法+参数:(返回邮 ...
- ★Kali信息收集~4.DNS系列
★.1host:DNS信息 参数: 一般情况下,host查找的是A,AAAA,和MX的记录 案例: DNS服务器查询 host -t ns 域名 A记录和MX记录查询 host 域名(host - ...
- ★Kali信息收集~ 1.Google Hacking + Github Hacking
一.google hacking site site:cnblogs.com 毒逆天 intitle intitle:login allintitle allintitle:index of alli ...
- Kali信息收集-搜索引擎
1.google hacking intext:搜索正文内容 intitile:网页标题中的内容 inurl:url中的关键字 site:目标站点下 filetype:文件类型 cache:缓存 li ...
- ★Kali信息收集~★7.FPing :ip段扫描
参数: 使用方法: fping [选项] [目标...] -a显示是活着的目标 -A 显示目标地址 -b n 大量 ping 数据要发送,以字节为单位 (默认 56) -B f 将指数退避算法因子设置 ...
随机推荐
- python3 threading初体验
python3中thread模块已被废弃,不能在使用thread模块,为了兼容性,python3将thread命名为_thread.python3中我们可以使用threading进行代替. threa ...
- nohup程序后台执行
Linux常用命令,用于不挂断的执行程序. nohup命令:如果你正在运行一个进程,而且你觉得在退出帐户时该进程还不会结束,那么可以使用nohup命令.该命令可以在你退出帐户/关闭终端之后继续运行相应 ...
- Akka.net路径里的user
因为经常买双色球,嫌每次对彩票号麻烦,于是休息的时候做了个双色球兑奖的小程序,做完了发现业务还挺复杂的,于是改DDD重做设计,拆分服务,各种折腾...,不过这和本随笔没多大关系,等差不多了再总结一下, ...
- StringMVC 中如何做数据校验
步骤一:引入四个jar包 步骤二:注册类型转换器 <context:component-scan base-package="cn.happy.controller"> ...
- POCO Controller 你这么厉害,ASP.NET vNext 知道吗?
写在前面 阅读目录: POCO 是什么? 为什么会有 POJO? POJO 的意义 POJO 与 PO.VO 的区别 POJO 的扩展 POCO VS DTO Controller 是什么? 关于 P ...
- Objective-C三种定时器CADisplayLink / NSTimer / GCD的使用
OC中的三种定时器:CADisplayLink.NSTimer.GCD 我们先来看看CADiskplayLink, 点进头文件里面看看, 用注释来说明下 @interface CADisplayLin ...
- [转]利用URLConnection来发送POST和GET请求
URL的openConnection()方法将返回一个URLConnection对象,该对象表示应用程序和 URL 之间的通信链接.程序可以通过URLConnection实例向该URL发送请求.读取U ...
- Android混合开发之WebViewJavascriptBridge实现JS与java安全交互
前言: 为了加快开发效率,目前公司一些功能使用H5开发,这里难免会用到Js与Java函数互相调用的问题,这个Android是提供了原生支持的,不过存在安全隐患,今天我们来学习一种安全方式来满足Js与j ...
- jQuery学习之路(7)- 用原生JavaScript实现jQuery的某些简单功能
▓▓▓▓▓▓ 大致介绍 学习了妙味,用原生的JavaScript实现jQuery中的某些部分功能 定义自己的函数库lQuery ▓▓▓▓▓▓ $()选择器的实现 jQuery是面向对象的,所以自己编写 ...
- nginx源码分析之模块初始化
在nginx启动过程中,模块的初始化是整个启动过程中的重要部分,而且了解了模块初始化的过程对应后面具体分析各个模块会有事半功倍的效果.在我看来,分析源码来了解模块的初始化是最直接不过的了,所以下面主要 ...
