8 Best DDoS Attack Tools (Free DDoS Tool Of The Year 2019)
#1) HULK
Description:
HULK stands for HTTP Unbearable Load King. It is a DoS attack tool for the web server. It is created for research purposes.
Features:
- It can bypass the cache engine.
- It can generate unique and obscure traffic.
- It generates a great volume of traffic at the web server.

https://packetstormsecurity.com/files/download/112856/hulk.zip
#2) Tor’s Hammer
Description:
This tool is created for testing purposes. It is for slow post attack.
Features:
- If you run it through Tor network then you will remain unidentified.
- In order to run it through Tor, use 127.0.0.1:9050.
- With this tool, the attack can be made on Apache and IIS servers.

https://sourceforge.net/projects/torshammer/files/Torshammer/1.0/
#3) Slowloris
Features:
- It sends authorized HTTP traffic to the server.
- It doesn’t affect other services and ports on the target network.
- This attack tries to keep the maximum connection engaged with those that are open.
- It achieves this by sending a partial request.
- It tries to hold the connections as long as possible.
- As the server keeps the false connection open, this will overflow the connection pool and will deny the request to the true connections.

https://github.com/gkbrk/slowloris
#4) LOIC
Description: LOIC stands for Low Orbit Ion Cannon. It is a free and popular tool that is available for the DDoS attack.
Features:9
- It is easy to use.
- It sends UDP, TCP, and HTTP requests to the server.
- It can do the attack based on the URL or IP address of the server.
- Within seconds, the website will be down and it will stop responding to the actual requests.
- It will NOT HIDE your IP address. Even using the proxy server will not work. Because in that case, it will make the proxy server a target.

https://sourceforge.net/projects/loic/
#5) Xoic
Description: It is a DDoS attacking tool. With the help of this tool, the attack can be made on small websites.
Features:
- It is easy to use.
- It provides three modes to attack.
- Testing mode.
- Normal DoS attack mode.
- DoS attack with TCP or HTTP or UDP or ICMP message.

https://sourceforge.net/directory/os:mac/?q=xoic
#6) DDOSIM
Description: DDOSIM stands for DDoS Simulator. This tool is for simulating the real DDoS attack. It can attack on the website as well as on the network.
Features:
- It attacks the server by reproducing many Zombie hosts.
- These hosts create a complete TCP connection with the server.
- It can do HTTP DDoS attack using valid requests.
- It can do DDoS attack using invalid requests.
- It can make an attack on the application layer

https://sourceforge.net/projects/ddosim/files/ddosim-0.2.tar.gz/download
#7) RUDY
Description: RUDY stands for R-U-Dead-Yet. This tool makes the attack using a long form field submission through POST method.
Features:
- Interactive console menu.
- You can select the forms from the URL, for the POST-based DDoS attack.
- It identifies the form fields for data submission. Then injects the long content length data to this form, at a very slow rate.
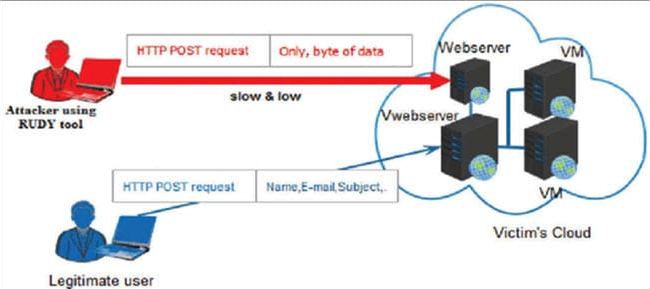
https://sourceforge.net/projects/r-u-dead-yet/
#8) PyLoris
Description:
This tool is created for testing. To make a DoS attack on the server, this tool uses SOCKS proxies and SSL connections.
Features:
- The attack can be made on HTTP, FTP, SMTP, IMAP, and Telnet.
- It has an easy to use GUI.
- It directly makes an attack on service.
https://sourceforge.net/projects/pyloris/
8 Best DDoS Attack Tools (Free DDoS Tool Of The Year 2019)的更多相关文章
- DDoS ATTACK PROCESSING APPARATUS AND METHOD IN OPENFLOW SWITCH
An OpenFlow switch in an OpenFlow environment includes an attack determination module to collect sta ...
- Identifying a distributed denial of service (DDOS) attack within a network and defending against such an attack
The invention provides methods, apparatus and systems for detecting distributed denial of service (D ...
- 使用DDOS deflate抵御少量DDOS攻击
DDoS-Deflate是一款非常小巧的防御和减轻DDoS攻击的工具,它可以通过监测netstat来跟踪来创建大量互联网连接的IP地址信息,通过APF或IPTABLES禁止或阻档这些非常IP地址. 工 ...
- f5 ddos cc——Mitigating DDoS Attacks with F5 Technology
摘自:https://f5.com/resources/white-papers/mitigating-ddos-attacks-with-f5-technology Mitigating Appli ...
- 国外DDoS产品的一些调研—— Akamai Arbor Networks Cloudflare DOSarrest F5 Fastly Imperva Link11 Neustar Nexusguard Oracle (Dyn) Radware Verisign
Global DDoS Threat LandscapeQ4 2017 https://www.incapsula.com/ddos-report/ddos-report-q4-2017.html,D ...
- Varnish简介
Varnish介绍: Varnish是一个反向HTTP代理,有时也被称为HTTP的加速器或网络加速器:它存在于真实服务器的前面(可能有多级代理),将来自于客户端的请求中的部分内容存储在自身的内存中,以 ...
- 知名黑客组织Anonymous(匿名者)的装备库
原文出处: infosecinstitute 译文出处:freebuf 欢迎分享原创到伯乐头条 本文关注的是世界著名的黑客组织Anonymous(匿名者).“我将描述他们的攻击方法和方式的计划 ...
- Azure上Linux VM DDOS攻击预防: 慢速攻击
在上篇博客(http://www.cnblogs.com/cloudapps/p/4996046.html)中,介绍了如何使用Apache的模块mod_evasive进行反DDOS攻击的设置,在这种模 ...
- DDoS
Distributed Denial of Service (DDoS) Attacks/tools https://staff.washington.edu/dittrich/misc/ddos/ ...
随机推荐
- tomcat配置通过域名访问项目
tomcat配置通过域名访问项目,是修改conf/server.xml里面的配置信息实现.具体如下: (1)修改Connector节点的port属性值 <Connector port=" ...
- BayaiM__ORACLE之ASM概念 --V 1.0.0
BayaiM__ORACLE之ASM概念 --V 1.0.0 -------------------------------------- ...
- BayaiM__MYSQL千万级数据量的优化方法积累__初级菜鸟
-----------------------------------------------------------------------------———————-------------- ...
- ubuntu 改键
参考: https://www.jianshu.com/p/9411ee427cfd https://www.cnblogs.com/zhengchl/archive/2012/08/25/26557 ...
- .htaccess设置301跳转及常用技巧整理
在虚拟主机环境中,基本上都是Apache环境.Apache的伪静态的设置,都是在网站根目录设置.htaccess文件,在.htaccess文件中无论是伪静态, 还是301跳转,甚至是防盗链和禁止某个I ...
- Vue中怎样使用swiper组件?
我用的VS Code编译器,首先打开终端,进入项目(我是在13-vue文件夹下面的elem中使用) D:\study\web\13-vue\elem> cnpm install vue-awes ...
- 19.8.2 luogu 夏令营 游
人生第一次游记....是在学校机房,在luogu网校,在炎炎夏日,在薯条汉堡,在自己的博客里... 十二天快吗? 刚上课那会真的比较兴奋,把每天的计划都排的满满的,希望这十二天慢点,再慢点,我得好好过 ...
- df 查看磁盘使用情况
1.查看磁盘使用情况 2.查看boot目录详情 3.提取已使用的百分比 4.切割提取出数字
- Git仓库占用空间太大的解决方法
git gc --aggressive对本地git库进行更彻底清理和优化,这个指令花费的时间也会更长. 胡云飞系统部署搭建整体把控:git gc --auto这是一个设置的指令,并不会进行gc操作.如 ...
- [Algorithm] 1290. Convert Binary Number in a Linked List to Integer
Given head which is a reference node to a singly-linked list. The value of each node in the linked l ...
