Sending Secret Messages LightOJ - 1404
Sending Secret Messages LightOJ - 1404
Alice wants to send Bob some confidential messages. But their internet connection is not secured enough. As their names have been used in many networking schemes, they are very rich now. So, they don't want to send encoded messages, they want to use secured dedicated connection for them. So, they talked to some ISPS (Internet Service Providers) about their problem. Only they get is that there are N routers in the network, some of them share bidirectional links. Each link has a capacity, and for each KB of data passing through this link, they have to pay some money. Assume that Alice is connected with the 1st router and Bob is connected to the Nth router.
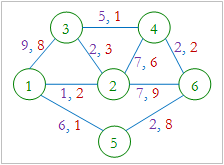
For example, in the picture, Alice wants to send 4 KB data from router 1 to router 6. Each link is identified by two integers in the form (a, b) where 'a' denotes the capacity of the link and 'b'denotes per KB cost of the link. So, Alice can send 1KB of data through 1 - 2 - 3 - 4 - 6 (cost 8), 2KB data through 1 - 5 - 6 (cost 2 * 9=18) and 1KB data through 1 - 3 - 4 - 6 (cost 11). So, the total cost is 37 units.
Now Alice wants to send P KB of data to Bob. You have to find the minimum amount of money they have to pay to achieve their goal.
Input
Input starts with an integer T (≤ 50), denoting the number of test cases.
Each case starts with a blank line. Next line contains three integers N (2 ≤ N ≤ 50), M (0 ≤ M ≤ N*(N-1)/2) and P (1 ≤ P ≤ 1000), where M denotes the number of bidirectional links. Each of the next M lines contains four integers u v w c (1 ≤ u, v ≤ N, u ≠ v, 1 ≤ w, c ≤ 100), meaning that there is a link between router u and v, and at most c KB data can be sent through this link, and each KB of data through this link will cost w. You can assume that there will be at most one connection between a pair of routers.
Output
For each case, print the case number and the minimum amount of money required or "impossible" if it's not possible to send P KB of data.
Sample Input
3
6 9 4
3 1 9 8
1 2 1 2
1 5 6 1
5 6 2 8
6 4 2 2
4 2 7 6
2 6 7 9
3 4 5 1
3 2 2 3
6 9 9
3 1 9 8
1 2 1 2
1 5 6 1
5 6 2 8
6 4 2 2
4 2 7 6
2 6 7 9
3 4 5 1
3 2 2 3
4 4 20
1 3 1 3
3 4 1 4
1 2 1 2
2 4 1 5
Sample Output
Case 1: 37
Case 2: 139
Case 3: impossible
题意:给定一个图,有n个顶点m条无向边,每条边都有容量和费用,求从1到n穿输p的数据量时的费用。
题解:费用流模板,EK算法介绍 https://blog.csdn.net/y990041769/article/details/21026445
#include <iostream>
#include <cstdio>
#include <cstring>
#include <algorithm>
#include <vector>
#include <queue>
using namespace std;
typedef long long ll;
const int MAXX=;
const int INF=0x3f3f3f3f; struct node
{
int st;
int to;
int next;
int cap;
int cost;
}edge[MAXX]; int head[MAXX],tol;
int pre[MAXX],dis[MAXX];
bool vis[MAXX];
int n,m,p; void init()
{
tol=;
memset(head,-,sizeof(head));
} void addedge(int u,int v,int cap,int cost)
{
edge[tol].st=u;
edge[tol].to=v;
edge[tol].cap=cap;
edge[tol].cost=cost;
edge[tol].next=head[u];
head[u]=tol++; edge[tol].st=v;
edge[tol].to=u;
edge[tol].cap=;
edge[tol].cost=-cost;
edge[tol].next=head[v];
head[v]=tol++;
} int minCostMaxFlow(int s,int t,int p)
{
int cost=;
while(p>)
{
queue<int> q;
memset(dis,INF,sizeof(dis));
memset(vis,,sizeof(vis));
memset(pre,-,sizeof(pre));
dis[s]=;
vis[s]=;
q.push(s);
while(!q.empty())
{
int u=q.front(); q.pop();
vis[u]=;
for(int i=head[u];i!=-;i=edge[i].next)
{
int to=edge[i].to;
if(edge[i].cap>&&dis[to]>dis[u]+edge[i].cost)
{
dis[to]=dis[u]+edge[i].cost;
pre[to]=i;
if(!vis[to])
{
vis[to]=;
q.push(to);
}
}
}
}
if(dis[t]==INF)return -;
int minn=p; for(int i=pre[t];i!=-;i=pre[edge[i].st])
minn=min(minn,edge[i].cap); for(int i=pre[t];i!=-;i=pre[edge[i].st])
{
edge[i].cap-=minn;
edge[i^].cap+=minn;
}
cost+=minn*dis[t];
p-=minn;
}
return cost;
} int main()
{
int T,x,y,z,w,cas=;
scanf("%d",&T);
while(T--)
{
scanf("%d%d%d",&n,&m,&p);
init();
for(int i=;i<=m;i++)
{
scanf("%d%d%d%d",&x,&y,&z,&w);
addedge(x,y,z,w);
addedge(y,x,z,w);
}
int ans=minCostMaxFlow(,n,p);
printf("Case %d: ",cas++);
if(ans!=-) printf("%d\n",ans);
else printf("impossible\n");
}
return ;
}
Sending Secret Messages LightOJ - 1404的更多相关文章
- How the Bitcoin protocol actually works
sklearn实战-乳腺癌细胞数据挖掘(博客主亲自录制视频教程) https://study.163.com/course/introduction.htm?courseId=1005269003&a ...
- [USACO 08DEC]Secret Message
Description Bessie is leading the cows in an attempt to escape! To do this, the cows are sending sec ...
- Secret Message ---- (Trie树应用)
Secret Message 总时间限制: 2000ms 内存限制: 32768kB 描述 Bessie is leading the cows in an attempt to escap ...
- [USACO08DEC] 秘密消息Secret Message
题目描述 Bessie is leading the cows in an attempt to escape! To do this, the cows are sending secret bin ...
- 「USACO08DEC」「LuoguP2922」秘密消息Secret Message(AC自动机
题目描述 Bessie is leading the cows in an attempt to escape! To do this, the cows are sending secret bin ...
- 洛谷 P2922 [USACO08DEC]秘密消息Secret Message
题目描述 Bessie is leading the cows in an attempt to escape! To do this, the cows are sending secret bin ...
- Distributed Cache Coherence at Scalable Requestor Filter Pipes that Accumulate Invalidation Acknowledgements from other Requestor Filter Pipes Using Ordering Messages from Central Snoop Tag
A multi-processor, multi-cache system has filter pipes that store entries for request messages sent ...
- Fedora 24中的日志管理
Introduction Log files are files that contain messages about the system, including the kernel, servi ...
- window下安装jupyter
1.Install [Anaconda](https://docs.continuum.io/anaconda/install#anaconda-install) 实际上安装了anaconda就已经安 ...
随机推荐
- ZOJ 3888 Twelves Monkeys (预处理+优先队列)
题目链接:ZOJ 3888 Twelves Monkeys 题意:题目描写叙述起来比較绕,直接讲案例 9 3 3 9 1 6 1 4 1 6 7 2 输入n,m,q.n限制了你询问的年份,m台时光机, ...
- LeetCode 349. Intersection of Two Arrays (两个数组的相交)
Given two arrays, write a function to compute their intersection. Example:Given nums1 = [1, 2, 2, 1] ...
- iOS 中删除cookie的正确做法
需求:删除 qq 登录的 cookie,保证下次打开 qq 登录页面不会默认登录 实现: NSString *url =@"https://w.mail.qq.com/cgi-bi ...
- 金典 SQL笔记 SQL语句汇总
SELECT * FROM (SELECT ROW_NUMBER() OVER ( ORDER BY id) AS rowN,FNumber, FName,FSalary ,Fage FROM dbo ...
- ubuntu多版本jdk安装及切换
系统:ubuntu14.04 一.安装openjdk1.7 sudo apt-get install openjdk-7-jre openjdk-7-jdk 安装完成后找到其安装路径: dpkg -L ...
- 2.EF的数据审计日志
转载:采用EntityFramework.Extended 对EF进行扩展(Entity Framework 延伸系列2) 数据审计日志: 先说一下这个审计的概念,就是对所有的实体的操作(增,删,改) ...
- Hybrid 开发
主讲人:吴彬 要学习某个东西之前,我们首先要了解这个东西是什么?然后我们要了解这东西有什么用,有什么好处和弊端?最后我们要知道这东西怎么用? 简单点就是 ——是什么?有什么用?怎么用? 那么进入正题 ...
- 快速访问GitHub
Github网站可以访问,但是由于网络代理商的原因,造成访问速度很慢. 本文采取方法:手动更改hosts Hosts是一个没有扩展名的系统文件,可以用记事本等工具打开,其作用就是将一些常用的网址域名与 ...
- Grunt环境搭建及使用
jQuery在使用grunt,bootstrap在使用grunt,百度UEditor在使用grunt,你没有理由不学.不用! 1. 前言 各位web前端开发人员,如果你现在还不知道grunt或者听说过 ...
- Android webkit keyevent 事件传递过程
前言:基于android webview 上定制自己使用的可移植浏览器apk,遇到好多按键处理的问题.所以索性研究了一下keyevent 事件的传递流程. frameworks 层 keyevent ...
