Subnetting
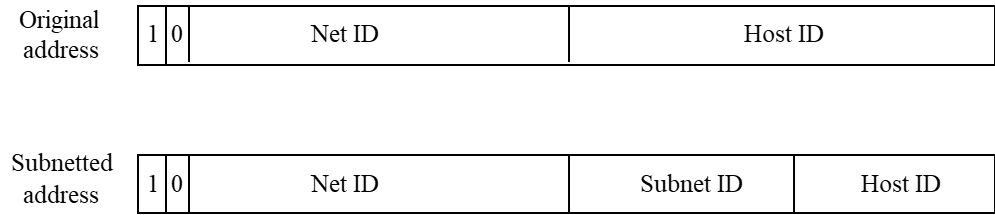
Subnet Addressing
- To better utilize IP address
- Subnet addressing introduces another hierarchical(分层) level
- Transparent to remote networks
- Simplifies management of multiplicity(多样性) of LANs
- Masking used to find subnet number(By devide Host ID into Subnet ID and Host ID)
Subnetting Scheme(体系)
- Organization has Class B address (16 host ID bits) with network ID: 150.100.0.0
- Create subnets with up to 100 hosts each
- We need one hundred hosts, so we need at least 7 bit(2^7=128>100)for host ID.
- 7 bits sufficient for each subnet (IP mask 7 bits)
- 16-7 = 9 bits for** subnet ID** (2^9 – 2 = 510 subnets)
- Apply subnet mask to IP addresses to help outside packet find corresponding subnet
- Example: Find subnet for 150.100.12.176
- Theory: We use "and operation" to get the subnet ID, compare every bit
- IP address = 10010110 01100100 00001100 10110000
- Mask = 11111111 11111111 11111111 10000000 (7 0s)
- AND = 10010110 01100100 00001100 10000000
- Subnet = 150.100.12.128
- Subnet address used by routers within organization
Subnet Range
Given the subnet 150.100.12.128
- IP address 150.100.12.128 is used to identify the subnetwork
- IP address 150.100.12.255 is used to broadcast packets in the subnet
- Range of the subnet IP address is between
- IP address = 10010110 01100100 00001100 10000001
to
IP address = 10010110 01100100 00001100 11111110
That is, 150.100.12.129 to 150.100.12.254
- IP address = 10010110 01100100 00001100 10000001
Subnet Example
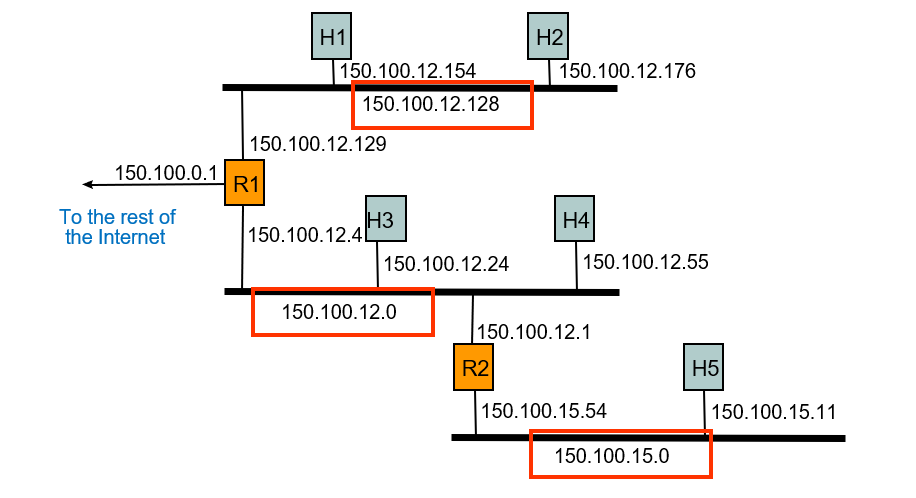
The subnetting can hide the configuration details from outside
Routing with Subnetworks
- IP layer in hosts and routers maintain a routing table
- Originating host(源主机): To send an IP packet, consult routing table
- If destination host is in same network, send packet directly using appropriate network interface
- Otherwise, send packet indirectly; typically, routing table indicates a default router
- Router: Examine IP destination address in arriving packet
- If destination IP address not own, router consults routing table to determine next-hop and associated network interface & forwards packet
Subnetting的更多相关文章
- subnetting and the subnet mask
原文:https://www.techopedia.com/6/28587/internet/8-steps-to-understanding-ip-subnetting/5 Step 4 - Sub ...
- 【转】IP协议详解之子网寻址、子网掩码、构造超网
子网寻址 1. 从两级IP地址到三级IP地址 <1>. IP地址利用率有时很低. <2>. 给每一个物理网络分配一个网络号会使路由表变得太大而使网络性能变坏. <3> ...
- [转]CIDR简介
IP Subnetting and Variable Length Subnet Masks Subnetting Basics 子网划分(subnetting)的优点: 1.减少网络流量 2.提高网 ...
- IP子网划分
CIDR值: 1.掩码255.0.0.0:/8(A类地址默认掩码) 2.掩码255.128.0.0:/9 3.掩码255.192.0.0:/10 4.掩码255.224.0.0:/11 5.掩码255 ...
- Linux就这个范儿 第13章 打通任督二脉
Linux就这个范儿 第13章 打通任督二脉 0111010110……你有没有想过,数据从看得见或看不见的线缆上飞来飞去,是怎么实现的呢?数据传输业务的未来又在哪里?在前面两章中我们学习了Linux网 ...
- TCP/IP协议原理与应用笔记18:构成子网和超网
1. 引言: (1)类别IP编址(Classful IP)的缺陷 • 固定的3种IP网络规模 C类地址:少于255台主机的网络 B类地址:介于255~65535台主机的网络 ...
- ip 子网掩码 网关 DNS
这一篇文章也很好: 原文引用于: http://www.cnblogs.com/jiqing9006/p/3365939.html 内外网ip: IP地址: IPv4地址分为A.B.C.D.E五类, ...
- IP子网掩码划分及设置
IP子网掩码划分及设置 定长子网掩码: 一.子网掩码的计算 TCP/IP网间网技术产生于大型主流机环境中,它能发展到今天的规模是当初的设计者们始料未及的.网间网规模的迅速扩展对IP地址模式的威胁并不是 ...
- IP地址、子网掩码详解
如何通过子网掩码划分网段 资料一: 一.缺省A.B.C类地址,子网掩码: 二.子网掩码的作用: code: IP地址 192.20.15.5 11000000 00010100 00001111 ...
随机推荐
- Spring Cloud面试题
引言 面试中面试官喜欢问组件的实现原理,尤其是常用技术,我们平时使用了SpringCloud还需要了解它的实现原理,这样不仅起到举一反三的作用,还能帮助轻松应对各种问题及有针对的进行扩展.以下是 课程 ...
- Grid标签计算结果集中的合计行
方法一: var detailT= grid.gettable("11"); var r=detailT.rows.length; detailT.rows[r-1].cells[ ...
- hdu 3091 Necklace 状态压缩dp *******
Necklace Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 327680/327680 K (Java/Others)Total ...
- C#学习笔记15
1.平台互操作性和不安全的代码:C#功能强大,但有些时候,它的表现仍然有些“力不从心”,所以我们只能摒弃它所提供的所有安全性,转而退回到内存地址和指针的世界. C#通过3种方式对此提供支持. (1)第 ...
- PL/SQL: numeric or value error: character to number conversion error
在最简单的plsql块编程中出现这个错误,是因为 DBMS_OUTPUT.PUT_LINE('the x is '+x);这里面不能用“+”,而是要用“||” DECLARE x number; ; ...
- Windows下etc文件夹
etc etcetera[ɛtsɛtərə]缩写 等等的意思 放置一些其他文件
- 软件项目技术点(5)——在canvas上绘制动态网格线
AxeSlide软件项目梳理 canvas绘图系列知识点整理 grid类的实现 当鼠标在画布上缩放时,网格能跟着我的鼠标滚动而相应的有放大缩小的效果. 下面是具体实现的代码,draw函数里计算出大 ...
- 03_Zookeeper基本数据模型及基本命令操作
[Zookeeper基本数据模型及注意点] * zk的数据模型可以类比为Linux的文件目录,是一种树状结构,如:/dubbo/com.service.DemoService/provider.... ...
- DELPHI SOKET 编程--使用TServerSocket和TClientSocket
本文采用delphi7+TServerSocket+TClientSocket; 笔者在工作中遇到对局域网中各工作站与服务器之间进行Socket通信的问题.现在将本人总结出来的TServerSocke ...
- git go使用socket5代理
git # set git through socks5 proxy: git config --global http.proxy socks5://127.0.0.1:1080 # Recover ...
