Openstack(七)keystone
官方安装文档:https://docs.openstack.org/ocata/zh_CN/install-guide-rdo/index.html
7.1 keystone简介
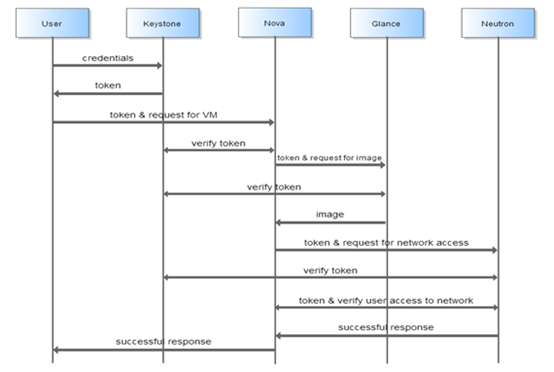
Keystone 中主要涉及到如下几个概念:User、Tenant、Role、Token:
User:使用openstack的用户。
Tenant:租户,可以理解为一个人、项目或者组织拥有的资源的合集。在一个租户中可以拥有很多个用户,这些用户可以根据权限的划分使用租户中的资源。
Role:角色,用于分配操作的权限。角色可以被指定给用户,使得该用户获得角色对应的操作权限。
Token:指的是一串比特值或者字符串,用来作为访问资源的记号。Token 中含有可访问资源的范围和有效时间。
7.2安装Keystone认证服务
7.2.1keystone数据库配置
# mysql
> create database keystone;
> grant all on keystone.* to 'keystone'@'%' identified by 'keystone';
7.2.2配置haproxy代理
Mysql port 3306,memcache port 11211,rabbitMQ port 5672双机代理,同3.3.3.3,3.3.3.5章
7.2.3验证数据库VIP端口访问
# mysql -ukeystone -h192.168.10.100 –pkeystone
7.2.4安装keystone
openstack-keystone是keystone服务,http是web服务,mod_wsgi是python的通用网关,
# yum install -y openstack-keystone httpd mod_wsgi python-memcached python2-PyMySQL
7.3配置keystone认证服务
7.3.1生成临时token
# openssl rand -hex 10
a734fda7b075fb62b75c
7.3.2修改配置文件
# vim /etc/keystone/keystone.conf
17 admin_token = a734fda7b075fb62b75c
714 connection = mysql+pymysql://keystone:keystone@192.168.10.100/keystone
2833 provider = fernet
7.3.3当前最终配置
# grep -n "^[a-Z\[]" /etc/keystone/keystone.conf
1:[DEFAULT]
17:admin_token = a734fda7b075fb62b75c
686:[database]
714:connection = mysql+pymysql://keystone:keystone@192.168.10.100/keystone
1494:[memcache]
2791:[token]
2833:provider = fernet
7.3.4初始化并验证数据库
# su -s /bin/sh -c "keystone-manage db_sync" keystone
# mysql
>use keystone;
>show tables;
7.3.5keystone日志文件
# ll /var/log/keystone/keystone.log
7.3.6初始化证书并验证
# keystone-manage fernet_setup --keystone-user keystone --keystone-group keystone
# keystone-manage credential_setup --keystone-user keystone --keystone-group keystone
# ll /etc/keystone/fernet-keys/
-rw------- 1 keystone keystone 44 Sep 10 10:56 0
-rw------- 1 keystone keystone 44 Sep 10 10:56 1
7.3.7 编辑apache配置文件
# vim /etc/httpd/conf/httpd.conf
95 ServerName 192.168.10.201:80
## ln -s /usr/share/keystone/wsgi-keystone.conf /etc/httpd/conf.d
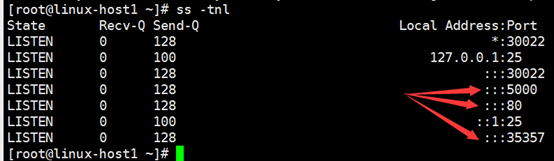
7.3.8 启动apache并验证
# systemctl start httpd
# systemctl enable httpd
# ss –tnl

7.3.9创建域、用户、项目和角色
7.3.9.1通过admin的token设置环境标量进行操作:
# export OS_TOKEN=a734fda7b075fb62b75c
# export OS_URL=http://192.168.10.201:35357/v3
# export OS_IDENTITY_API_VERSION=3
7.3.9.2创建默认域
一定要在上一步设置完成环境变量的前提下方可操作成功,否则会提示未认证。
#命令格式为:openstack domain create --description "描述信息" 域名
# openstack domain create --description "Default Domain" default
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Default Domain |
| enabled | True |
| id | 961b40ed4c6b40a9b266ce5e451a4292 |
| name | default |
+-------------+----------------------------------+
7.3.9.3创建一个admin的项目
#命令格式为openstack project --domain 域 --description "描述" 项目名
# openstack project create --domain default --description "Admin Project" admin
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Admin Project |
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 1caf792ed8d84fc089ef4c3ab6cbf3c1 |
| is_domain | False |
| name | admin |
| parent_id | 961b40ed4c6b40a9b266ce5e451a4292 |
+-------------+----------------------------------+
7.3.9.4创建admin用户并设置密码为admin:
# openstack user create --domain default --password-prompt admin
User Password:
Repeat User Password:
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 2c82b16690934cbe9b78bbffae50ecca |
| name | admin |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
7.3.9.5创建admin角色:
一个项目里面可以有多个角色,目前角色只能创建在/etc/keystone/policy.json文件中定义好的角色:
# openstack role create admin
+-----------+----------------------------------+
| Field | Value |
+-----------+----------------------------------+
| domain_id | None |
| id | 9c6f0cdfe1704fdb85c56528ebcaec16 |
| name | admin |
+-----------+----------------------------------+
7.3.9.6给admin用户授权:
将admin用户授予admin项目的admin角色,即给admin项目添加一个用户叫admin,并将其添加至admin角色,角色是权限的一种集合:
# openstack role add --project admin --user admin admin
7.3.9.7创建demo项目:
该项目可用于演示和测试等
# openstack project create --domain default --description "Demo Project" demo
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Demo Project |
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 51919be117ec4ba2bdddd206bd3a1444 |
| is_domain | False |
| name | demo |
| parent_id | 961b40ed4c6b40a9b266ce5e451a4292 |
+-------------+----------------------------------+
7.3.9.8创建demo用户并设置密码为demo:
# openstack user create --domain default --password-prompt demo
User Password:
Repeat User Password:
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 49640b553dcc43c6bccf5722eedf46af |
| name | demo |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
7.3.9.9创建一个user角色:
角色目前有user和admin:
[root@linux-host1 ~]# openstack role create user
+-----------+----------------------------------+
| Field | Value |
+-----------+----------------------------------+
| domain_id | None |
| id | 5b60565079c4475ab640f61038c1c632 |
| name | user |
+-----------+----------------------------------+
7.3.9.10把demo用户添加到demo项目:
然后赋予user权限:
# openstack role add --project demo --user demo user
7.3.9.11创建一个service项目:
各服务之间与keystone进行访问和认证,service用于给服务创建用户
# openstack project create --domain default --description "Service Project" service
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Service Project |
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | c7cf72ff26dd49f1a9216f94146cf82b |
| is_domain | False |
| name | service |
| parent_id | 961b40ed4c6b40a9b266ce5e451a4292 |
+-------------+----------------------------------+
7.3.9.11创建glance用户:
创建glance密码用户并设置密码为glance
# openstack user create --domain default --password-prompt glance
User Password:
Repeat User Password:
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 1aeb2f2695ec4008b6ff9899e88fcb82 |
| name | glance |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
7.3.9.12对glance用户授权:
把glance和neutron用户添加到service项目并授予admin角色
# openstack role add --project service --user glance admin
7.3.9.13按照以上步骤操作nova和neutron用户:
将nova用户添加到service项目并授予admin权限
创建nova用户并设置密码为nova:
# openstack user create --domain default --password-prompt nova
User Password:
Repeat User Password:
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 71580f80cd4345e19f8948b77556ae3a |
| name | nova |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
创建neutron用户并设置密码为neutron:
# openstack user create --domain default --password-prompt neutron
User Password:
Repeat User Password:
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| domain_id | 961b40ed4c6b40a9b266ce5e451a4292 |
| enabled | True |
| id | 73fe1b80b71e46f49fe1d5730dca5283 |
| name | neutron |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
对nova和neutron用户授权:
将nova和neutron用户授权为service项目的admi权限
[root@linux-host1 ~]# openstack role add --project service --user nova admin
[root@linux-host1 ~]# openstack role add --project service --user neutron admin
7.3.9.14服务注册
将keystone服务地址注册到openstack:
创建一个keystone认证服务:
# openstack service list #查看当前的服务
# openstack service create --name keystone --description "OpenStack Identity" identity
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | OpenStack Identity |
| enabled | True |
| id | 6efd80d3570f40bfafb02a1169b68aaa |
| name | keystone |
| type | identity |
+-------------+----------------------------------+
# openstack service list #验证服务创建成功
+----------------------------------+----------+----------+
| ID | Name | Type |
+----------------------------------+----------+----------+
| 6efd80d3570f40bfafb02a1169b68aaa | keystone | identity |
+----------------------------------+----------+----------+
# openstack endpoint create --region RegionOne identity public http://192.168.10.100:5000/v3 #公共端点
+--------------+----------------------------------+
| Field | Value |
+--------------+----------------------------------+
| enabled | True |
| id | 92990b4521454e1ab1b5aa9e26e3e230 |
| interface | public |
| region | RegionOne |
| region_id | RegionOne |
| service_id | 6efd80d3570f40bfafb02a1169b68aaa |
| service_name | keystone |
| service_type | identity |
| url | http://192.168.10.100:5000/v3 |
+--------------+----------------------------------+
# openstack endpoint create --region RegionOne identity internal http://192.168.10.100:5000/v3 #私有端点
+--------------+----------------------------------+
| Field | Value |
+--------------+----------------------------------+
| enabled | True |
| id | 9779a47b96ee4ffa9196fb8593bbcc1d |
| interface | internal |
| region | RegionOne |
| region_id | RegionOne |
| service_id | 6efd80d3570f40bfafb02a1169b68aaa |
| service_name | keystone |
| service_type | identity |
| url | http://192.168.10.100:5000/v3 |
+--------------+----------------------------------+
# openstack endpoint create --region RegionOne identity admin http://192.168.10.100:35357/v3 #管理端点
+--------------+----------------------------------+
| Field | Value |
+--------------+----------------------------------+
| enabled | True |
| id | c95807c1098e4cab95e11eeebba1221f |
| interface | admin |
| region | RegionOne |
| region_id | RegionOne |
| service_id | 6efd80d3570f40bfafb02a1169b68aaa |
| service_name | keystone |
| service_type | identity |
| url | http://192.168.10.100:35357/v3 |
+--------------+----------------------------------+
7.4配置keystone双机集群
7.4.1同步linux-hosts1文件
安装认证服务,同7.2.4
# scp -r -P22 /etc/keystone/ 192.168.10.202:/etc/keystone
# vim /etc/httpd/conf/httpd.conf
95 ServerName 192.168.10.201:80
# ln -s /usr/share/keystone/wsgi-keystone.conf /etc/httpd/conf.d
# systemctl start httpd
# systemctl enable httpd
# ss –tnl
7.4.2配置haporxy
linux-host5、linux-host6
# vim /etc/haproxy/haproxy.cfg
listen keystone-public-url
bind 192.168.10.100:5000
mode tcp
log global
balance source
server keystone1 192.168.10.201:5000 check inter 5000 rise 3 fall 3
server keystone1 192.168.10.202:5000 check inter 5000 rise 3 fall 3
listen keystone-admin-url
bind 192.168.10.100:35357
mode tcp
log global
balance source
server keystone1 192.168.10.201:35357 check inter 5000 rise 3 fall 3
server keystone1 192.168.10.202: 35357 check inter 5000 rise 3 fall 3
# systemctl reload haproxy
# telnet 192.168.10.100 5000
# telnet 192.168.10.100 35357
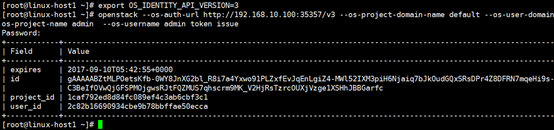
7.5验证
7.5.1测试keystone是否可以做用户验证
验证admin用户,密码admin,新打开一个窗口并进行以下操作:
# export OS_IDENTITY_API_VERSION=3
# openstack --os-auth-url http://192.168.10.100:35357/v3 --os-project-domain-name default --os-user-domain-name default --os-project-name admin --os-username admin token issue
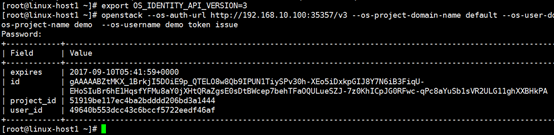
验证demo用户,密码为demo:
# export OS_IDENTITY_API_VERSION=3
# openstack --os-auth-url http://192.168.10.100:35357/v3 --os-project-domain-name default --os-user-domain-name default --os-project-name demo --os-username demo token issue
Openstack(七)keystone的更多相关文章
- OpenStack:安装Keystone
>安装Keystone1. 安装# apt-get install keystone2. 创建dbcreate database keystone;grant all privileges on ...
- Openstack中keystone与外部LDAP Server的集成
openstack中keystone鉴权的用户user和password信息,通常保存在mysql数据库的keystone库: 表local_user和表password: keystone也支持外部 ...
- OpenStack之Keystone模块
一.Keystone介绍 OpenStack Identity(Keystone)服务为运行OpenStack Compute上的OpenStack云提供了认证和管理用户.帐号和角色信息服务,并为Op ...
- 在安装Openstack的keystone认证服务时,出现The request you have made requires authentication. (HTTP 401) (Request-ID: req-f94bebba-f0c5-4a92-85问题的处理
创建openstack的keystone认证服务器报错: The request you have made requires authentication. (HTTP 401) (Reques ...
- 003-官网安装openstack之-keystone身份认证服务
以下操作均在控制节点进行 1.控制节点安装keystone服务 概念理解: Keystone是OpenStack框架中,负责身份验证.服务规则和服务令牌的功能, 它实现了OpenStack的Ident ...
- openstack核心组件——keystone身份认证服务(5)
云计算openstack核心组件——keystone身份认证服务(5) 部署公共环境 ntp openstack mariadb-server rabbitmq-server memcache 1.w ...
- OpenStack 安装 Keystone
OpenStack 安装 Keystone 本篇主要记录一下 如何安装 openstack的 第一个组件 keystone 认证授权组件 openstack 版本 我选的是queens 版本 1.Op ...
- openstack 之~keystone基础
第一:keystone是什么? keystone是 OpenStack Identity Service 的项目名称,是一个负责身份管理验证.服务规则管理和服务令牌功能.它实现了openstack的i ...
- openstack学习-KeyStone安装(二)
一.安装keystone # yum install -y openstack-keystone httpd mod_wsgi memcached python-memcached 二.设置Memca ...
随机推荐
- 在php代码中调用帝国cms头部变量temp.header的方法
在php代码中调用帝国cms头部变量temp.header的方法 代码如下: <?php require("../e/class/connect.php"); if(!def ...
- [mysql] Install/Remove of the Service Denied
在windos 的cmd下安装mysql 在mysql的bin目录下面执行: mysqld --install 报错: 信息如下: Install/Remove of the Service Deni ...
- Mike Gancarz:Linux/Unix设计思想
Mike Gancarz是一位技术布道者. 他是Linux/Unix最基本的倡导者之中的一个,也是最早开发X Window System的先驱.他把一些在Unix/Linux社区里口口相 ...
- 微软Azure、谷歌GAE、亚马逊AWS比較
谷歌Google App Engine 亚马逊AWS 微软Microsoft Azure 提供服 务类型 PaaS, SaaS Iaas, PaaS IaaS, PaaS, SaaS 服务间 ...
- linux下安装pip以及导入第三方包
python有着强大的第三方库,数量很多且功能强大. 最原始的办法是在官网上下载压缩包,解压,然后运行setup.py来进行安装. 显然这种方法很繁琐,不方便.因此有了包管理工具. pip是一个包管理 ...
- 用命令行执行ROBOT FRAMEWORK用例
转自:http://www.51testing.com/html/86/n-1430786.html 除了在ride中执行用例,我们也可以通过命令行的形式执行用例. 1.执行一整个项目 pybot+项 ...
- kubectl get 输出格式
常见的输出格式有: * custom-columns=<spec> # 根据自定义列名进行输出,逗号分隔 * custom-columns-file=<filename> # ...
- Linux 下配置网卡的别名即网卡子IP的配置
what 什么是ip别名?用windows的话说,就是为一个网卡配置多个ip.when 什么场合增加ip别名能派上用场?布网需要.多ip访问测试.特定软件对多ip的需要...and so on. ho ...
- php执行外部命令
php执行外部命令的不少,例如:exec.shell_exec.system.popen等.我特意的讲一下popen,它跟其他函数不太一样,其他函数执行一个命令后,会等待其返回后,再向下执行,而pop ...
- PHP-Yii框架下提交表单form防止csrf攻击
解决办法: 在form标签下,写入一个隐藏的input控件 <form id="form_submit" action="http://v2admin.doneve ...
