攻防世界 reverse 进阶5-7
5.re-for-50-plz-50 tu-ctf-2016
流程很简单,异或比较
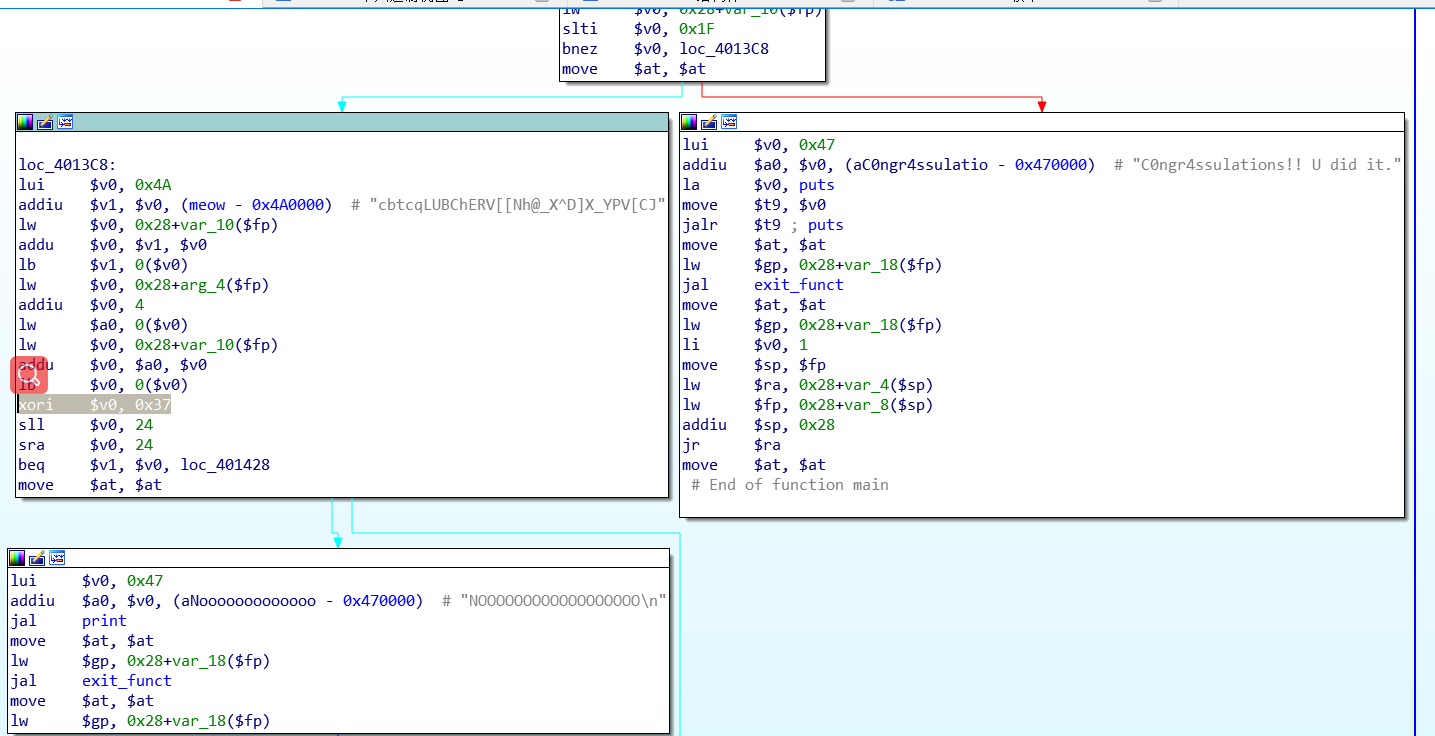
1 x=list('cbtcqLUBChERV[[Nh@_X^D]X_YPV[CJ')
2 y=0x37
3 z=''
4 for t in x:
5 z+=chr(ord(t)^y)
6 print(z)
TUCTF{but_really_whoisjohngalt}
6.key csaw-ctf-2016-quals
运行后打印完?W?h?a?t h?a?p?p?e?n? 便结束

修改指令跳过文件读取,输出=W=r=o=n=g=K=e=y=
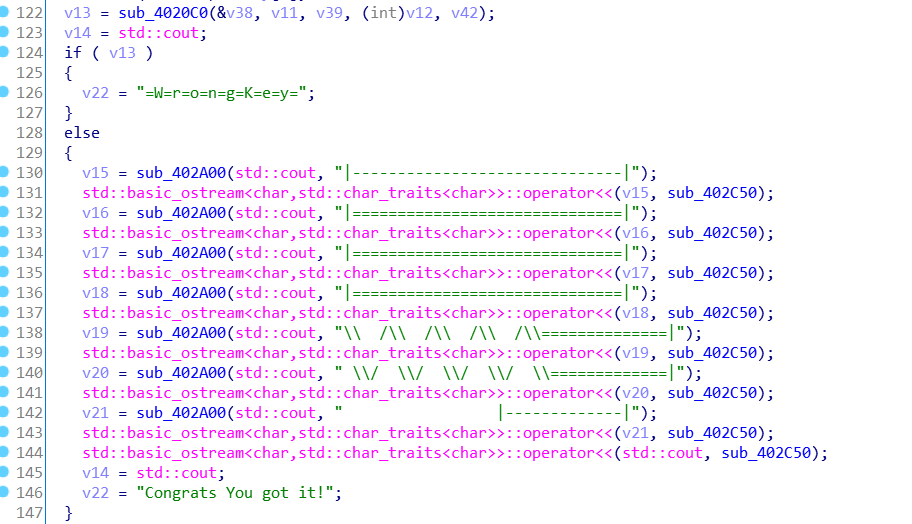
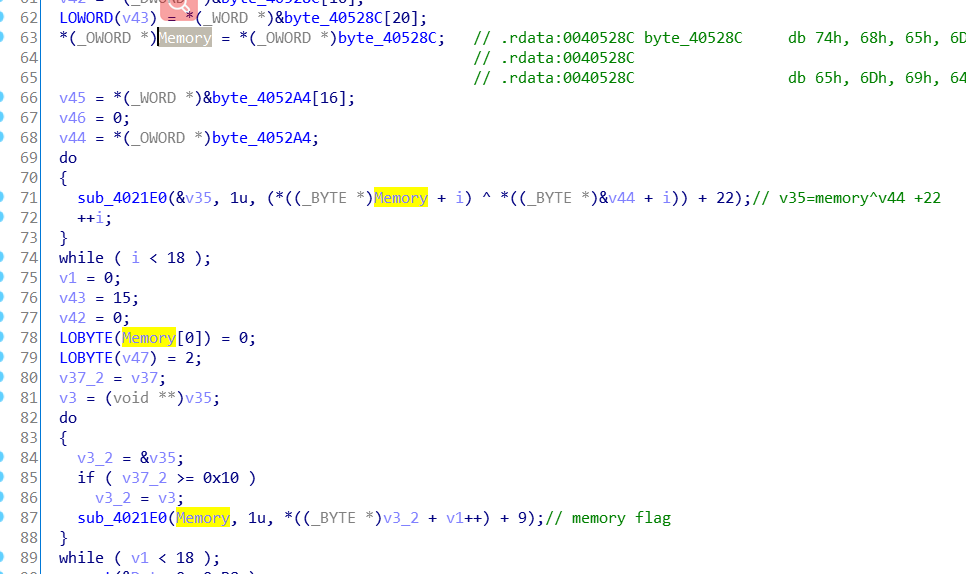
关键点就是sub_4020c0函数
关注if比较处
动态调试可直接获得flag
这里的的v7其实是sub_4020c0函数中第三个参数
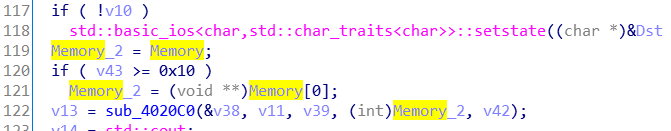
关注Memory,发现两次循环处理
脚本:
1 x=[ 0x74, 0x68, 0x65, 0x6D, 0x69, 0x64, 0x61, 0x74, 0x68, 0x65,
2 0x6D, 0x69, 0x64, 0x61, 0x74, 0x68, 0x65, 0x6D, 0x69, 0x64,
3 0x6]
4 y=[0x3E, 0x2D, 0x2D, 0x2D, 0x2D, 0x2B, 0x2B, 0x2B, 0x2B, 0x2E,
5 0x2E, 0x2E, 0x2E, 0x3C, 0x3C, 0x3C, 0x3C, 0x2E]
6 # print(len(x))
7 # print(len(y))
8 z=[]
9 for i in range(18):
10 z.append((x[i]^y[i])+22+9)
11
12 # print(' '.join(map(hex,z)))
13 print(''.join(map(chr,z)))
idg_cni~bjbfi|gsxb
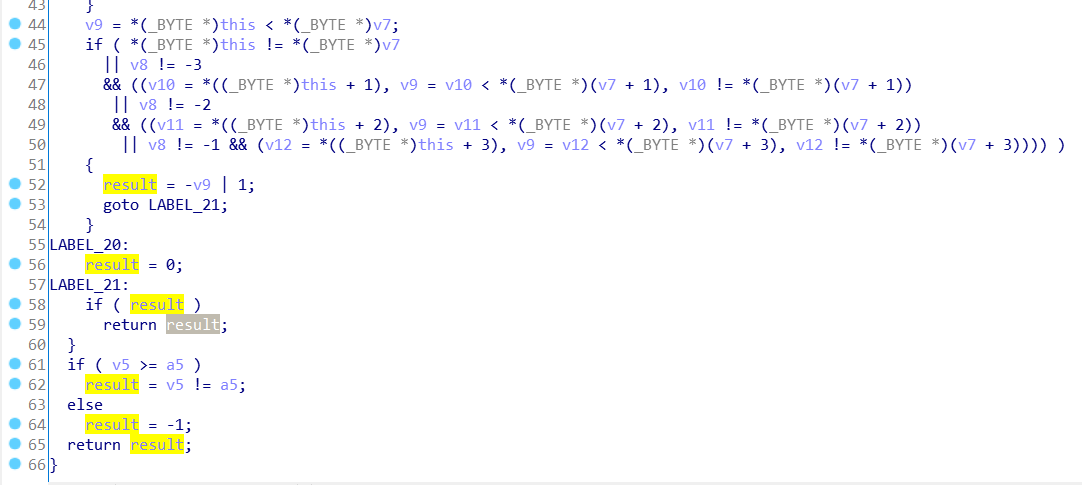
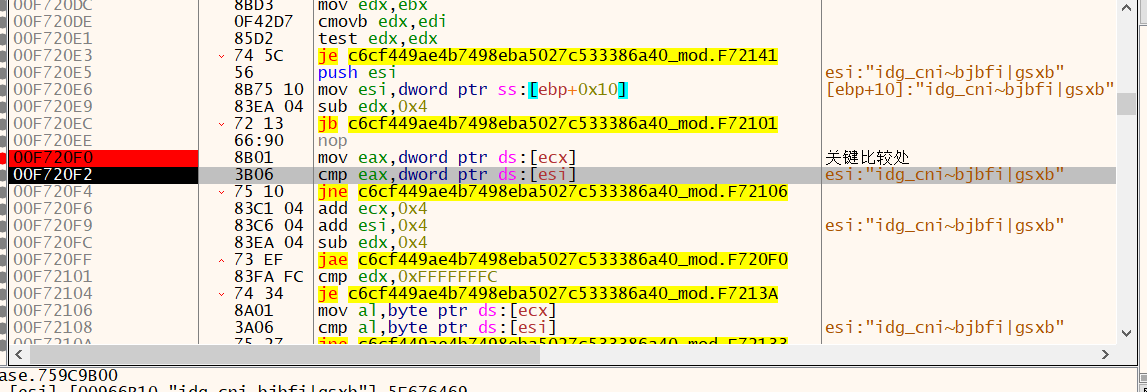
7.simple-check-100 school-ctf-winter-2015
exe文件有坑,满是辛酸泪,分析elf文件
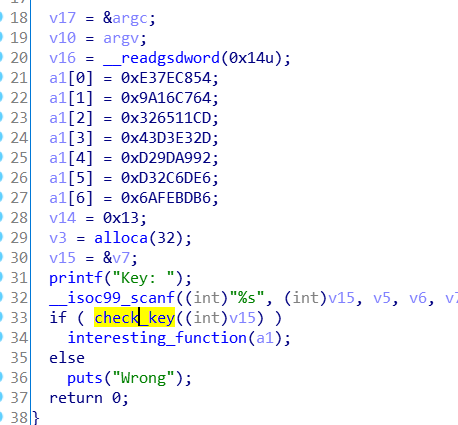
过掉check_key()函数在linux便可直接输出flag
分析:
1 a1[0] = 0xE37EC854;
2 a1[1] = 0x9A16C764;
3 a1[2] = 0x326511CD;
4 a1[3] = 0x43D3E32D;
5 a1[4] = 0xD29DA992;
6 a1[5] = 0xD32C6DE6;
7 a1[6] = 0x6AFEBDB6;
8 v14 = 0x13;
9 v3 = alloca(32);
10 v15 = &v7;
11 printf("Key: ");
12 __isoc99_scanf((int)"%s", (int)v15, v5, v6, v7, v8, v9, (int)v10, v11, v12, a1[0], a1[1], a1[2], a1[3], a1[4], a1[5]);
13 if ( check_key((int)v15) )
14 interesting_function(a1);
1 unsigned int *__cdecl interesting_function(int a1[7])
2 {
3 unsigned int *result; // eax
4 unsigned int temp; // [esp+18h] [ebp-20h]
5 int i; // [esp+1Ch] [ebp-1Ch]
6 int j; // [esp+20h] [ebp-18h]
7 int *__attribute__((__org_arrdim(0,7))) v5; // [esp+24h] [ebp-14h]
8 char *ptr_temp; // [esp+28h] [ebp-10h]
9 unsigned int v7; // [esp+2Ch] [ebp-Ch]
10
11 v7 = __readgsdword(0x14u);
12 result = (unsigned int *)a1;
13 v5 = a1;
14 for ( i = 0; i <= 6; ++i )
15 {
16 temp = v5[i] ^ 0xDEADBEEF;
17 result = &temp;
18 ptr_temp = (char *)&temp;
19 for ( j = 3; j >= 0; --j )
20 result = (unsigned int *)putchar((char)(ptr_temp[j] ^ flag_data[i][j]));
21 }
22 return result;
23 }
脚本:
1 win=[0x54, 0xB8, 0xFE, 0x61, 0x00, 0x13, 0x00, 0x00, 0x00, 0x61, 0x6A, 0xFE, 0xBD, 0xB6, 0xD3, 0x2C,
2 0x6D, 0xE6, 0xD2, 0x9D, 0xA9, 0x92, 0x43, 0xD3, 0xE3, 0x2D, 0x32, 0x65, 0x11, 0xCD, 0x9A, 0x16,
3 0xC7, 0x64, 0xE3, 0x7E, 0xC8, 0x30]#windows下调试获取的操作数据
4 win2=[0x6A, 0xFE, 0xBD, 0xB6, 0xD3, 0x2C,
5 0x6D, 0xE6, 0xD2, 0x9D, 0xA9, 0x92, 0x43, 0xD3, 0xE3, 0x2D, 0x32, 0x65, 0x11, 0xCD, 0x9A, 0x16,
6 0xC7, 0x64, 0xE3, 0x7E, 0xC8, 0x54]
7 win2=win2[::-1]
8
9 flag_date=[0xDC, 0x17, 0xBF, 0x5B, 0xD4, 0x0A, 0xD2, 0x1B, 0x7D, 0xDA,
10 0xA7, 0x95, 0xB5, 0x32, 0x10, 0xF6, 0x1C, 0x65, 0x53, 0x53,
11 0x67, 0xBA, 0xEA, 0x6E, 0x78, 0x22, 0x72, 0xD3]
12
13
14 a1=[0 for i in range(7)]
15 a1[0] = 0xE37EC854;
16 a1[1] = 0x9A16C764;
17 a1[2] = 0x326511CD;
18 a1[3] = 0x43D3E32D;
19 a1[4] = 0xD29DA992;
20 a1[5] = 0xD32C6DE6;
21 a1[6] = 0x6AFEBDB6;
22
23 x=[0xef,0xbe,0xad,0xde]
24
25 s=''
26 for i in range(7):
27 temp=(a1[i]^0xDEADBEEF).to_bytes(4,'little')
28 for j in range(3,-1,-1):
29 s+=chr(temp[j]^flag_date[i*4+j])
30 print(chr(win[i * 4 + j] ^ flag_date[i * 4 + j] ^ x[j]), end='')
31 # print(chr(v8[i*4+j]^flag_date[i*4+j]^x[j]),end='')
32 print()
33 print(s)
exe中栈内变量布局与linux不同,
exe文件:äìgŧ;µ`n:ç,=c!hí±t
elf文件:flag_is_you_know_cracking!!!
flag_is_you_know_cracking!!!
攻防世界 reverse 进阶5-7的更多相关文章
- 攻防世界 reverse 进阶 APK-逆向2
APK-逆向2 Hack-you-2014 (看名以为是安卓逆向呢0.0,搞错了吧) 程序是.net写的,直接祭出神器dnSpy 1 using System; 2 using System.Diag ...
- 攻防世界 reverse 进阶 10 Reverse Box
攻防世界中此题信息未给全,题目来源为[TWCTF-2016:Reverse] Reverse Box 网上有很多wp是使用gdb脚本,这里找到一个本地还原关键算法,然后再爆破的 https://www ...
- 攻防世界 reverse 进阶 9-re1-100
9.re1-100 1 if ( numRead ) 2 { 3 if ( childCheckDebugResult() ) 4 { 5 responseFalse(); 6 } 7 else if ...
- 攻防世界 reverse 进阶 8-The_Maya_Society Hack.lu-2017
8.The_Maya_Society Hack.lu-2017 在linux下将时间调整为2012-12-21,运行即可得到flag. 下面进行分析 1 signed __int64 __fastca ...
- 攻防世界 reverse 进阶 notsequence
notsequence RCTF-2015 关键就是两个check函数 1 signed int __cdecl check1_80486CD(int a1[]) 2 { 3 signed int ...
- 攻防世界 reverse 进阶 easyre-153
easyre-153 查壳: upx壳 脱壳: 1 int __cdecl main(int argc, const char **argv, const char **envp) 2 { 3 int ...
- 攻防世界 reverse 进阶 -gametime
19.gametime csaw-ctf-2016-quals 这是一个小游戏,挺有意思的 's'-->' ' 'x'-->'x' 'm'-->'m' 观察流程,发现检验函 ...
- 攻防世界 reverse 进阶 16-zorropub
16.zorropub nullcon-hackim-2016 (linux平台以后整理) https://github.com/ctfs/write-ups-2016/tree/master/nu ...
- 攻防世界 reverse 进阶 15-Reversing-x64Elf-100
15.Reversing-x64Elf-100 这题非常简单, 1 signed __int64 __fastcall sub_4006FD(__int64 a1) 2 { 3 signed int ...
- 攻防世界 reverse 进阶 12 ReverseMe-120
程序流程很清晰 1 int __cdecl main(int argc, const char **argv, const char **envp) 2 { 3 unsigned int v3; // ...
随机推荐
- Dockfile搭建极简LNMP环境
最近才发现ThinkPHP6.0和CI4.x都要求php版本为7.1以上了,本机的php版本还停留在7.0.3x,又懒得升级,于是考虑使用Docker来运行一个lnmp环境. 常规环境搭建的方式有两种 ...
- export html to canvas image
export html to canvas image canvas.toDataURL https://developer.mozilla.org/en-US/docs/Web/API/HTMLCa ...
- git cli all in one
git cli all in one https://www.atlassian.com/git/tutorials/learn-git-with-bitbucket-cloud git create ...
- js & input event & input change event
js & input event & input change event vue & search & input change <input @click=& ...
- flutter web in action
flutter web in action flutter for web https://flutter.dev/web https://flutter.dev/docs/get-started/w ...
- TypeScript Generics
TypeScript Generics https://www.typescriptlang.org/docs/handbook/generics.html 泛型 1 Generic Interfac ...
- 用WPF写了个处理视频,音频,图片的工具
处理工具依赖ffmpeg,感兴趣可以看下Github上的源码 下载地址也在Github上
- 算法型稳定币USDN有什么魔力引发市场热潮?
最近比特币重新突破了8万大关,区块链行业又再次火爆起来,吸引了圈内圈外人的火热讨论,而这其中市场投资者讨论最频繁的就要属算法型稳定币USDN了. USDN是基于NGK.IO区块链中的稳定币, 1枚US ...
- MySQL的简单使用方法备忘
这只是一篇我的个人备忘录,写的是我常用的命令.具体可以参考"菜鸟教程" https://www.runoob.com/mysql/mysql-tutorial.html 登录(用户 ...
- 基于tcp的应用层消息边界如何定义
聊聊基于tcp的应用层消息边界如何定义 背景 2018年笔者有幸接触一个项目要用到长连接实现云端到设备端消息推送,所以借机了解过相关的内容,最终是通过rabbitmq+mqtt实现了相关功能,同时在心 ...
