20162314 《Program Design & Data Structures》Learning Summary Of The Eleventh Week
20162314 2017-2018-1 《Program Design & Data Structures》Learning Summary Of The Eleventh Week
Summary of Key Concepts
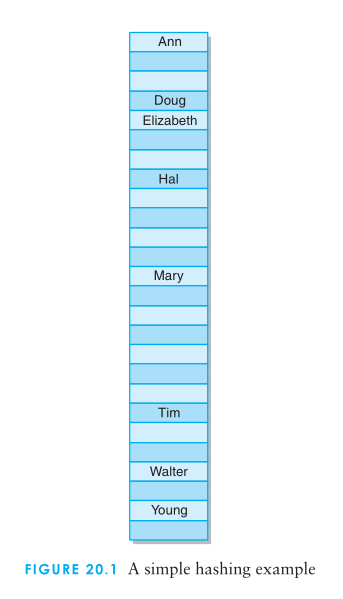
In hashing, elements are stored in a hash table, with their location in thetable determined by a hashing function.
The situation where two elements or keys map to the same location in the table is called a collision.
A hashing function that maps each element to a unique position in the table is said to be a perfect hashing function.
Extraction involves using only a part of the element’s value or key to compute the location at which to store the element.
The division method is very effective when dealing with an unknown set of key values.
In the shift folding method, the parts of the key are added together to create the index.
The length-dependent method and the mid-square method may also be effectively used with strings by manipulating the binary representations of the characters in the string.
Although Java provides a hashcode method for all objects, it is often preferable to define a specific hashing function for any particular class.
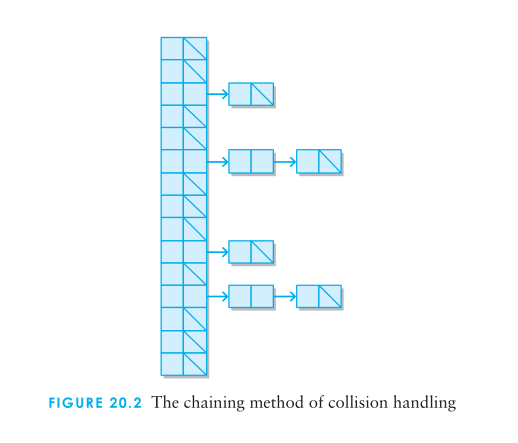
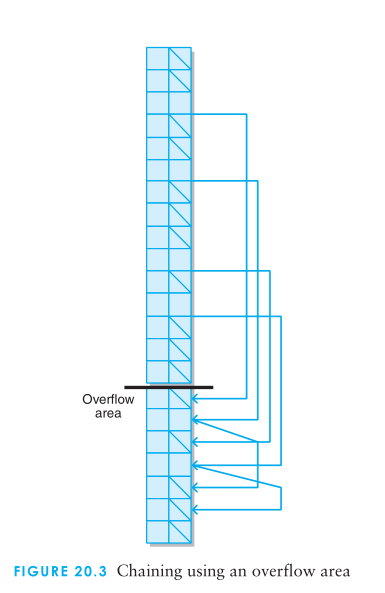
The chaining method for handling collisions simply treats the hash table conceptually as a table of collections rather than as a table of individual cells.
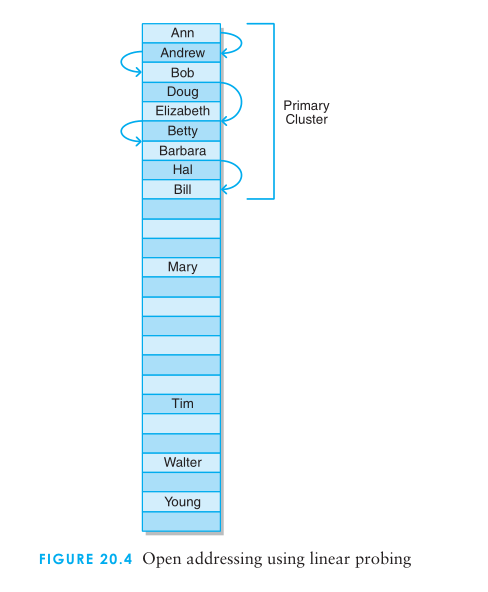
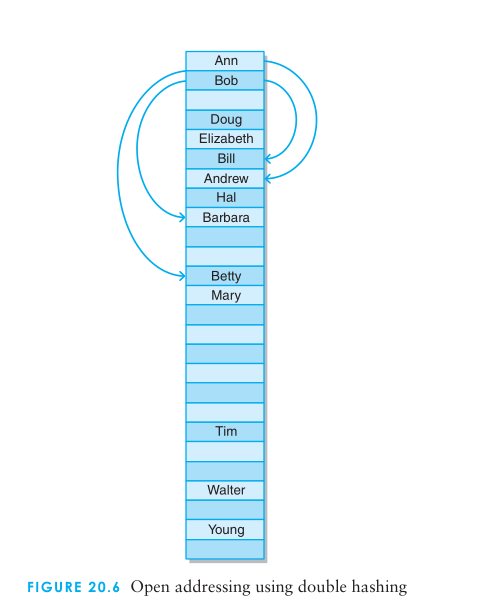
The open addressing method for handling collisions looks for another open position in the table other than the one to which the element is originally hashed.
The load factor is the maximum percentage occupancy allowed in the hash table before it is resized.
Problem and solution in teaching materials.
What is the difference between a hash table and the other collections we have discussed?
- Elements are placed into a hash table at an index produced by a function of the value of the element or a key of the element.
- This is unique from other collections where the position/locationof an element in the collection is determined either by comparison
- with the other values in the collection or by the order in which the elements were added or removed from the collection.
What is our goal for a hashing function?
- We need a hashing function that will do a good job of distributing elements into positions in the table.
What is the consequence of not having a good hashing function?
- If we do not have a good hashing function, the result will be too many elements mapped to the same location in the table. This will result in poor performance.
Why is deletion from an open addressing implementation a problem?
- Because of the way that a path is formed in open addressing,deleting an element from the middle of that path can cause elements beyond that on the path to be unreachable.
What is the load factor and how does it affect table size?
- The load factor is the maximum percentage occupancy allowed in the hash table before it is resized. Once the load factor has
- been reached, a new table is created that is twice the size of the current table, and then all of the elements in the current table
- are inserted into the new table.
Code hosting
What is the maximum number of edges for an undirected graph? A directed graph?
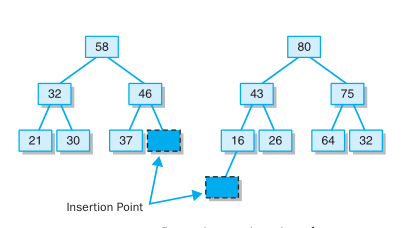
- The maximum element is removed from a heap (maxheap) by replacing the root with the last leaf of the tree, then moving that
- element down the tree as appropriate to reassert the proper relationships among the elements.
Summary of error for last week.
Linear search is always more effective than binary search.The answer should be false, for the situation of "n = 2".
Evaluate for my partner
- Advantage and problem in the blog:
- Concise and comprehensie
- Uncleary to the content
- Mould is amazing
- Advantage and problem in the code:
- Serious writing.
- Wonderful idea
- Too less
Learning situation of partner
- Learning content of partner:
- Algorithm
- Recursion
- HanoiTowers and maze
Anything else that want to say
- It's not easy to persere on utizing English to write a blog.But I'm getting used to doing this because of the benefit.
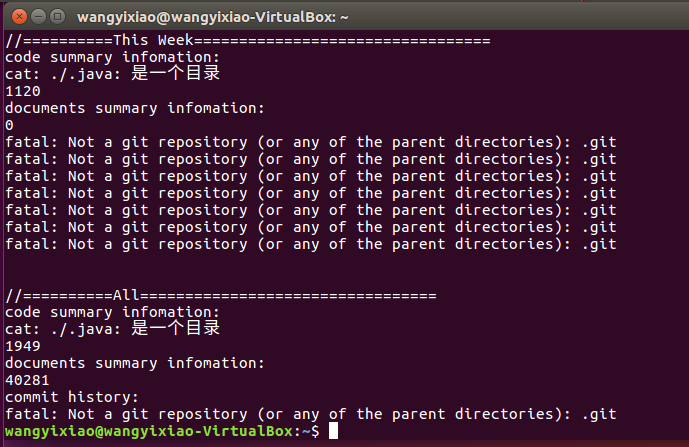
Academic progress check
| Code line number(increasing/accumulative) | Blog number(inc/acc) | studying time(inc/acc) | progress | |
|---|---|---|---|---|
| target | 5000lines | 30articles | 400hours | |
| First week | 180/180 | 1/1 | 20/20 | |
| Second week | 1049/1229 | 1/2 | 18/38 | |
| Third week | 1037/2266 | 3/7 | 22/60 | |
| Fourth week | 1120/3386 | 2/9 | 30/90 |
20162314 《Program Design & Data Structures》Learning Summary Of The Eleventh Week的更多相关文章
- 20162314 《Program Design & Data Structures》Learning Summary Of The Ninth Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Ninth Week ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The Seventh Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Seventh Wee ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The Fifth Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Fifth Week ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The Second Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Second Week ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The First Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The First Week ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The Tenth Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Tenth Week ...
- 20162314 《Program Design & Data Structures》Learning Summary Of The Eighth Week
20162314 2017-2018-1 <Program Design & Data Structures>Learning Summary Of The Eighth Week ...
- 20182320《Program Design and Data Structures》Learning Summary Week9
20182320<Program Design and Data Structures>Learning Summary Week9 1.Summary of Textbook's Con ...
- 【Python学习笔记】Coursera课程《Python Data Structures》 密歇根大学 Charles Severance——Week6 Tuple课堂笔记
Coursera课程<Python Data Structures> 密歇根大学 Charles Severance Week6 Tuple 10 Tuples 10.1 Tuples A ...
随机推荐
- PHP之变量范围
前面的话 变量范围即它定义的上下文背景(也就是它的生效范围).在javascript中,并没有变量范围这一概念,相似的可能是作用域.但是,由于javscript使用的是词法作用域,指变量声明时的位置: ...
- 跳表 SkipList
跳表是平衡树的一种替代的数据结构,和红黑树不同,跳表对树的平衡的实现是基于一种随机化的算法,这样就使得跳表的插入和删除的工作比较简单. 跳表是一种复杂的链表,在简单链表的节点信息之上又增加了额 ...
- 关于Java中按值传递和按引用传递的问题详解
写了两个方法,一个是多关键字的快速排序,一个是基于多关键字的基速排序.两个方法的参数列表是一样一样的,但是快速排序正常工作,但是基数排序传出来的参数一点没有改变,苦思冥想了半天也没想通是怎么回事,于是 ...
- with操作符损耗性能的原因
当函数运行是,创建一个[[scope]]指向的被称为作用域链的可变对象集合,作用域链的最前端是一个包含所有的局部变量.参数.this等的被称为“激活对象”的对象. 在标示符查找的过程中,从作用域的最前 ...
- office2010如何使用excel冻结窗格
当我们在制作一个Excel表格时,如果列数较多,行数也较多时,一旦向下滚屏,则上面的标题行也跟着滚动,在处理数据时往往难以分清各列数据对应的标题,事实上利用"冻结窗格"功能可以很好 ...
- 树链剖分-点的分治(点数为k且距离最长的点对)
hdu4871 Shortest-path tree Time Limit: 6000/3000 MS (Java/Others) Memory Limit: 130712/130712 K ( ...
- 无向连通图求割点(tarjan算法去掉改割点剩下的联通分量数目)
poj2117 Electricity Time Limit: 5000MS Memory Limit: 65536K Total Submissions: 3603 Accepted: 12 ...
- 02Del.ashx(删除班级)
using System; using System.Collections.Generic; using System.Linq; using System.Web; using WebHelper ...
- 传智播客微金所项目实战移动web开发
1.源码笔记 我的源码+笔记(很重要):链接: http://pan.baidu.com/s/1kULKqcJ 感谢传智播客项目相关视频:1.6天 链接: https://pan.baidu.com/ ...
- jira-source--plugin
X11 forward impact on jira plugin system initialization. 而Linux的curl使用的证书库在文件“/etc/pki/tls/certs/ca- ...