Kali linux 2016.2(Rolling)中metasploit的主机探测
不多说,直接上干货!
1、活跃主机扫描
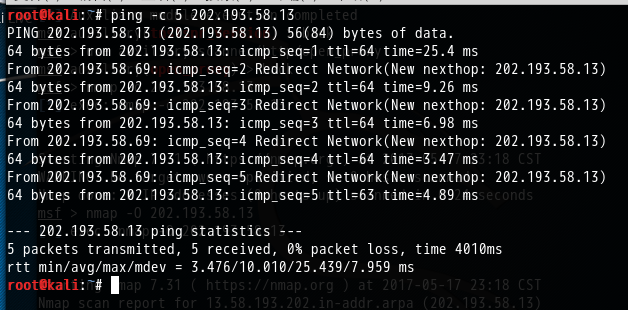
root@kali:~# ping -c 202.193.58.13
PING 202.193.58.13 (202.193.58.13) () bytes of data.
bytes from 202.193.58.13: icmp_seq= ttl= time=25.4 ms
From 202.193.58.69: icmp_seq= Redirect Network(New nexthop: 202.193.58.13)
bytes from 202.193.58.13: icmp_seq= ttl= time=9.26 ms
From 202.193.58.69: icmp_seq= Redirect Network(New nexthop: 202.193.58.13)
bytes from 202.193.58.13: icmp_seq= ttl= time=6.98 ms
From 202.193.58.69: icmp_seq= Redirect Network(New nexthop: 202.193.58.13)
bytes from 202.193.58.13: icmp_seq= ttl= time=3.47 ms
From 202.193.58.69: icmp_seq= Redirect Network(New nexthop: 202.193.58.13)
bytes from 202.193.58.13: icmp_seq= ttl= time=4.89 ms --- 202.193.58.13 ping statistics ---
packets transmitted, received, % packet loss, time 4010ms
rtt min/avg/max/mdev = 3.476/10.010/25.439/7.959 ms
root@kali:~#
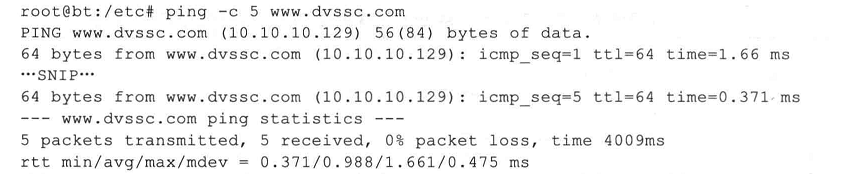
当然,你也用下面这个
2、Metasploit的主机发现模块
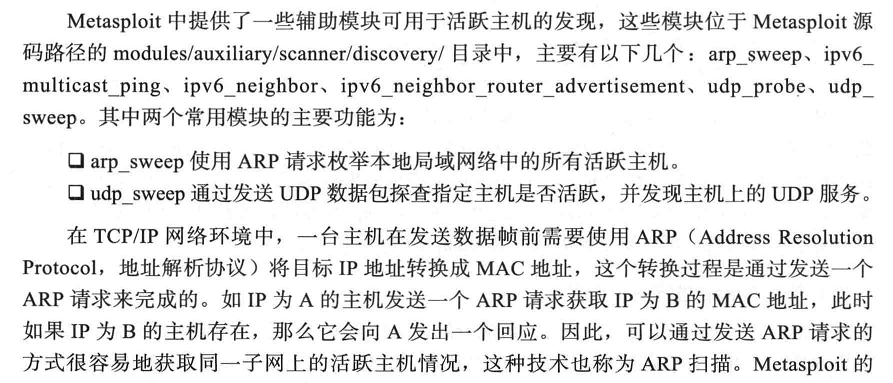
arp_sweep模块便是一个ARP扫描器,如下所示。
arp_sweep使用ARP请求美剧本地局域网中的所有活跃主机
udp_sweep通过发送UDP数据包探查制定主机是否活跃,兵发现主机上的UDP服务
root@kali:~# msfconsole
....
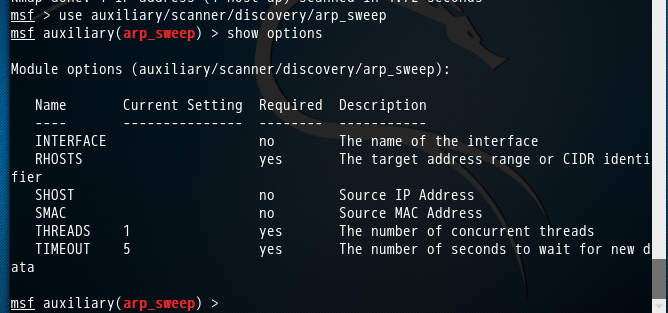
msf > use auxiliary/scanner/discovery/arp_sweep
msf auxiliary(arp_sweep) > show options Module options (auxiliary/scanner/discovery/arp_sweep): Name Current Setting Required Description
---- --------------- -------- -----------
INTERFACE no The name of the interface
RHOSTS yes The target address range or CIDR identifier
SHOST no Source IP Address
SMAC no Source MAC Address
THREADS yes The number of concurrent threads
TIMEOUT yes The number of seconds to wait for new data msf auxiliary(arp_sweep) >
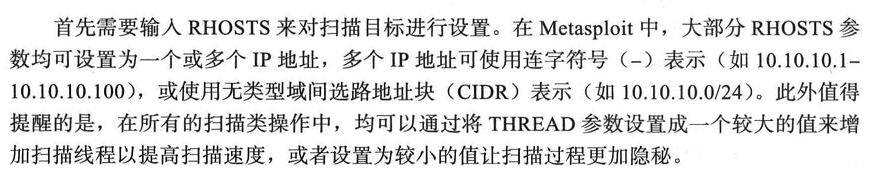
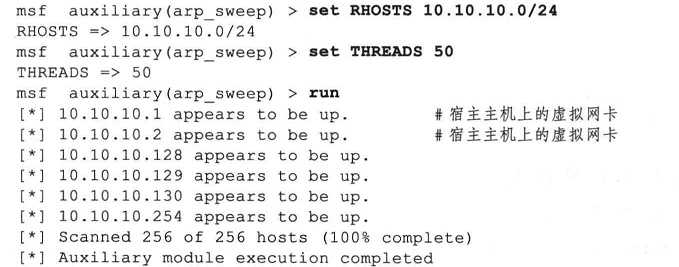
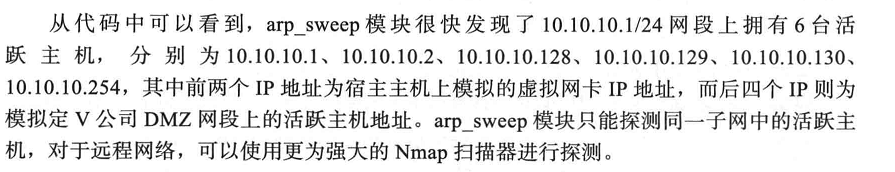
设置好RHOSTS和THREADS参数后,输入run命令启动扫描器,如下图所示。

msf auxiliary(arp_sweep) > set RHOSTS 202.193.58.13/
RHOSTS => 202.193.58.13/
msf auxiliary(arp_sweep) > set THREADS
THREADS =>
msf auxiliary(arp_sweep) > run [*] 202.193.58.7 appears to be up (UNKNOWN).
[*] 202.193.58.7 appears to be up (UNKNOWN).
[*] 202.193.58.9 appears to be up (UNKNOWN).
[*] 202.193.58.9 appears to be up (UNKNOWN).
[*] 202.193.58.11 appears to be up (UNKNOWN).
[*] 202.193.58.12 appears to be up (UNKNOWN).
[*] 202.193.58.13 appears to be up (UNKNOWN).
[*] 202.193.58.13 appears to be up (ASUSTek COMPUTER INC.).
[*] 202.193.58.14 appears to be up (UNKNOWN).
[*] 202.193.58.19 appears to be up (UNKNOWN).
[*] 202.193.58.20 appears to be up (ELITEGROUP COMPUTER SYSTEMS CO., LTD.).
[*] 202.193.58.23 appears to be up (UNKNOWN).
[*] 202.193.58.26 appears to be up (COMPAL INFORMATION(KUNSHAN)CO.,LTD).
[*] 202.193.58.33 appears to be up (UNKNOWN).
[*] 202.193.58.47 appears to be up (TP-LINK TECHNOLOGIES CO., LTD.).
[*] 202.193.58.48 appears to be up (UNKNOWN).
[*] 202.193.58.53 appears to be up (UNKNOWN).
[*] 202.193.58.55 appears to be up (UNKNOWN).
[*] 202.193.58.58 appears to be up (UNKNOWN).
[*] 202.193.58.60 appears to be up (D-Link International).
[*] 202.193.58.7 appears to be up (UNKNOWN).
[*] 202.193.58.69 appears to be up (COMPAL INFORMATION (KUNSHAN) CO., LTD).
[*] 202.193.58.73 appears to be up (ELITEGROUP COMPUTER SYSTEMS CO., LTD.).
[*] 202.193.58.76 appears to be up (UNKNOWN).
[*] 202.193.58.82 appears to be up (UNKNOWN).
[*] 202.193.58.83 appears to be up (Armorlink shanghai Co. Ltd).
[*] 202.193.58.85 appears to be up (QUANTA COMPUTER INC.).
[*] 202.193.58.7 appears to be up (UNKNOWN).
[*] 202.193.58.98 appears to be up (Advantech Technology (CHINA) Co., Ltd.).
[*] 202.193.59.254 appears to be up (FUJIAN STAR-NET COMMUNICATION CO.,LTD).
[*] 202.193.58.109 appears to be up (UNKNOWN).
[*] 202.193.58.111 appears to be up (UNKNOWN).
[*] 202.193.58.7 appears to be up (UNKNOWN).
[*] 202.193.58.148 appears to be up (UNKNOWN).
[*] 202.193.58.155 appears to be up (Jetway Information Co., Ltd.).
[*] 202.193.58.13 appears to be up (UNKNOWN).
[*] 202.193.58.162 appears to be up (UNKNOWN).
[*] 202.193.58.165 appears to be up (Tenda Technology Co., Ltd.).
[*] 202.193.58.171 appears to be up (UNKNOWN).
[*] 202.193.58.179 appears to be up (UNKNOWN).
[*] 202.193.58.180 appears to be up (Dell Inc).
[*] 202.193.58.13 appears to be up (UNKNOWN).
[*] 202.193.59.254 appears to be up (FUJIAN STAR-NET COMMUNICATION CO.,LTD).
[*] 202.193.58.197 appears to be up (UNKNOWN).
[*] 202.193.58.208 appears to be up (UNKNOWN).
[*] 202.193.58.215 appears to be up (Universal Global Scientific Industrial Co., Ltd.).
[*] 202.193.58.13 appears to be up (UNKNOWN).
[*] 202.193.58.220 appears to be up (UNKNOWN).
[*] 202.193.58.224 appears to be up (UNKNOWN).
[*] 202.193.58.230 appears to be up (ELITEGROUP COMPUTER SYSTEMS CO., LTD.).
[*] 202.193.58.231 appears to be up (UNKNOWN).
[*] 202.193.58.236 appears to be up (G-PRO COMPUTER).
[*] 202.193.58.242 appears to be up (UNKNOWN).
[*] Scanned of hosts (% complete)
[*] Auxiliary module execution completed
msf auxiliary(arp_sweep) >
当然,大家可以用下面的
Kali linux 2016.2(Rolling)中metasploit的主机探测的更多相关文章
- MetaSploit攻击实例讲解------社会工程学set攻击(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 首先,如果你是用的BT5,则set的配置文件是在 /pentest/exploits/set/set_config下. APACHE_SERVER=ONSELF_SIGNED_A ...
- MetaSploit攻击实例讲解------Metasploit自动化攻击(包括kali linux 2016.2(rolling) 和 BT5)
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)里Metasploit连接(包括默认和自定义)的PostgreSQL数据库 Kali linux 2016.2(Ro ...
- MetaSploit攻击实例讲解------终端下PostgreSQL数据库的使用(包括kali linux 2016.2(rolling) 和 BT5)
不多说,直接上干货! 配置msf连接postgresql数据库 我这里是使用kali linux 2016.2(rolling) 用过的博友们都知道,已经预安装好了PostgreSQL. 1. p ...
- MetaSploit攻击实例讲解------工具Meterpreter常用功能介绍(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 说在前面的话 注意啦:Meterpreter的命令非常之多,本篇博客下面给出了所有,大家可以去看看.给出了详细的中文 由于篇幅原因,我只使用如下较常用的命令. 这篇博客,利用下面 ...
- MetaSploit攻击实例讲解------攻击445端口漏洞(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 大家,相信最近的这个事件,对于445端口已经是非常的小心了.勒索病毒 445端口是一个毁誉参半的端口,有了它我们可以在局域网中轻松访问各种共享文件夹或共享打印机,但也正是因为有了 ...
- Kali linux 2016.2 的 plyload模块之meterpreter plyload详解
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)中的payloads模块详解 当利用成功后尝试运行一个进程,它将在系统进程列表里显示,即使在木马中尝试执行系统命令, ...
- Kali linux 2016.2(Rolling)中的Metasploit如何更新与目录结构初步认识
如何更新MSF 1.Windows平台 方法1: 运行msfupdate.bat 在msfconsole里执行命令svn update 或者 方法2: 2.unix/linux平台 方法1: 运行m ...
- Kali linux 2016.2(Rolling)中的payloads模块详解
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)中的Exploits模块详解 payloads模块,也就是shellcode,就是在漏洞利用成功后所要做的事情.在M ...
- Kali linux 2016.2(Rolling)里Metasploit连接(包括默认和自定义)的PostgreSQL数据库之后的切换到指定的工作空间
不多说,直接上干货! 为什么要这么做? 答: 方便我们将扫描不同的目标或目标的不同段,进行归类.为了更好的后续工作! 前期博客 Kali linux 2016.2(Rolling)里Metasploi ...
随机推荐
- 多项福利回馈会员,且看Hao123怎样玩转“霸权主义”
谈到"霸权主义",我们非常easy将其与国际政治联系在一起.只是.霸权主义可不全然用来形容政治,在7月14日,Hao123上线了一个会员福利活动,命名为"Hao1 ...
- 使用C++实现学生管理系统
我在前面的博客中分别使用C语言的动态数组和链表实现了学生成绩管理系统.近期正好在学习C++,于是我便使用C++实现了学生成绩管理系统.算法和前面的C语言的动态数组实现的学生成绩管理系统几乎相同,仅仅是 ...
- Android ImageView 不显示JPEG图片 及 Android Studio中怎样引用图片资源
Android ImageView 不显示JPEG图片 今天在写一个小实例,ImageView在xml里面设置的是INVISIBLE,在代码里须要设置成setVisibility(View.VISIB ...
- nyoj 628 小媛在努力 【搜索】
第一次是直接建一个10^7的数组 结果 内存大的要死.! 是不是能够不建数组 这下好了 小媛在努力 时间限制:1000 ms | 内存限制:65535 KB 难度:2 描写叙述 在多媒体数据处理 ...
- zzulioj--1799--wrz的压岁钱(贪心)
1799: wrz的压岁钱 Time Limit: 1 Sec Memory Limit: 128 MB Submit: 407 Solved: 71 SubmitStatusWeb Boa ...
- Oracle GoldenGate
Oracle GoldenGate实现数据库同步 前言:最近刚好在弄数据库同步,网上查了些资料再加上自己整理了一些,做个分享! 一.GoldenGate的安装 官方文档: Oracle®GoldenG ...
- 推荐几个bootstrap 后端UI框架
转载地址 https://blog.csdn.net/u013816448/article/details/81563051
- 1028C:Rectangles
You are given n rectangles on a plane with coordinates of their bottom left and upper right points. ...
- lua中调用C++函数
lua中调用C++函数 我们产品中提供了很多lua-C API给用户在lua中调用,之前一直没用深究其实现原理,只是根据已有的代码在编码.显然这不是一个好的习惯,没用达到知其所以然的目的. 一.基本原 ...
- Swift 中的协议
Swift 中的协议协议是为方法.属性等定义一套规范,没有具体的实现,类似于Java中的抽象接口,它只是描述了方法或属性的骨架,而不是实现.方法和属性实现还需要通过定义类,函数和枚举完成. 协议定义 ...
