Linux 服务器加入Windows AD
背景信息:
Windows AD Version: Windows Server 2012 R2 zh-cn
计算机全名:hlm12r2n1.hlm.com
域:hlm.com
域控管理员:stone
普通用户:abc; bcd
普通组:hlmgroup,用户bcd在该组下
IP:10.0.0.6
Linux服务器:
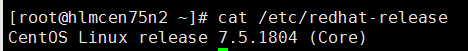
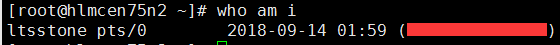
具有root权限的用户:ltsstone
操作步骤:
安装所需包文件:
yum install -y krb5-workstation realmd sssd samba-common adcli oddjob oddjob-mkhomedir samba samba-common-tools
编辑/etc/resolve.conf文件,将DNS指向DC
[root@hlmcen75n2 ~]# cat /etc/resolv.conf
; generated by /usr/sbin/dhclient-script
search lqvi3agp2gsunp1mlkwv0vudne.ax.internal.chinacloudapp.cn
nameserver 10.0.0.6
编辑/etc/hosts文件,添加DC的IP及域的对应关系
[root@hlmcen75n2 ~]# cat /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
:: localhost localhost.localdomain localhost6 localhost6.localdomain6
10.0.0.6 hlm12r2n1.hlm.com
将Linux机器加入域
[root@hlmcen75n2 ~]# realm join hlm12r2n1.hlm.com -U stone
Password for stone:
发现可以成功发现域了
[root@hlmcen75n2 ~]# realm list
hlm.com
type: kerberos
realm-name: HLM.COM
domain-name: hlm.com
configured: kerberos-member
server-software: active-directory
client-software: sssd
required-package: oddjob
required-package: oddjob-mkhomedir
required-package: sssd
required-package: adcli
required-package: samba-common-tools
login-formats: %U@hlm.com
login-policy: allow-permitted-logins
permitted-logins:
permitted-groups: hlmgroup@hlm.com
将组hlmgroup加入域
[root@hlmcen75n2 sudoers.d]# realm permit -g hlmgroup@hlm.com
可以看到用户stone,abc,bcd可以被成功发现
[root@hlmcen75n2 ~]# id stone@hlm.com
uid=(stone) gid=(domain users) groups=(domain users),(group policy creator owners),(domain admins),(schema admins),(denied rodc password replication group),(enterprise admins) [root@hlmcen75n2 ~]# id abc@hlm.com
uid=(abc) gid=(domain users) groups=(domain users) [root@hlmcen75n2 ~]# id bcd@hlm.com
uid=(bcd) gid=(domain users) groups=(domain users),(hlmgroup)
为使用户不需用带域名就可以被识别,需要修改配置文件/etc/sssd/sssd.conf,将use_fully_qualified_names行的True值修改为False
[root@hlmcen75n2 ~]# cat /etc/sssd/sssd.conf [sssd]
domains = hlm.com
config_file_version =
services = nss, pam [domain/hlm.com]
ad_server = hlm12r2n1.hlm.com
ad_domain = hlm.com
krb5_realm = HLM.COM
realmd_tags = manages-system joined-with-adcli
cache_credentials = True
id_provider = ad
krb5_store_password_if_offline = True
default_shell = /bin/bash
ldap_id_mapping = True
use_fully_qualified_names = False
fallback_homedir = /home/%u@%d
access_provider = simple
simple_allow_groups = hlmgroup@hlm.com
重启sssd服务,重新列出预控信息
[root@hlmcen75n2 ~]# systemctl restart sssd
[root@hlmcen75n2 ~]# realm list
hlm.com
type: kerberos
realm-name: HLM.COM
domain-name: hlm.com
configured: kerberos-member
server-software: active-directory
client-software: sssd
required-package: oddjob
required-package: oddjob-mkhomedir
required-package: sssd
required-package: adcli
required-package: samba-common-tools
login-formats: %U
login-policy: allow-permitted-logins
permitted-logins:
permitted-groups: hlmgroup@hlm.com
发现不加域信息,Linux服务器也可以识别域用户
[root@hlmcen75n2 ~]# id stone
uid=(stone) gid=(domain users) groups=(domain users),(group policy creator owners),(domain admins),(schema admins),(denied rodc password replication group),(enterprise admins)
[root@hlmcen75n2 ~]# id abc
uid=(abc) gid=(domain users) groups=(domain users)
[root@hlmcen75n2 ~]# id bcd
uid=(bcd) gid=(domain users) groups=(domain users),(hlmgroup)
尝试切换到域用户,发现无法进入root管理员权限,提示
[root@hlmcen75n2 ~]# su - abc
Last login: Mon Sep :: UTC on pts/
[abc@hlmcen75n2 ~]$ sudo su - root We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things: #) Respect the privacy of others.
#) Think before you type.
#) With great power comes great responsibility. [sudo] password for abc:
abc is not in the sudoers file. This incident will be reported.
[abc@hlmcen75n2 ~]$
编辑 /etc/sudoers.d/waagent 文件,将需要root权限的用户加入到其下
[root@hlmcen75n2 ~]# vim /etc/sudoers.d/waagent
[root@hlmcen75n2 ~]# cat /etc/sudoers.d/waagent
ltsstone ALL=(ALL) ALL
abc ALL=(ALL) ALL
重新尝试切换root用户,发现已经可以
[root@hlmcen75n2 ~]# sudo su - abc
Last login: Tue Sep :: UTC on pts/
[abc@hlmcen75n2 ~]$ sudo su - root
[sudo] password for abc:
Last login: Tue Sep :: UTC on pts/
[root@hlmcen75n2 ~]#
备注:
执行命令:realm join hlm12r2n1.hlm.com -U stone,messages日志发现加入域的认证过程如下:
Sep :: hlmcen75n2 realmd: * Resolving: _ldap._tcp.hlm12r2n1.hlm.com
Sep :: hlmcen75n2 realmd: * Resolving: hlm12r2n1.hlm.com
Sep :: hlmcen75n2 realmd: * Performing LDAP DSE lookup on: 10.0.0.6
Sep :: hlmcen75n2 realmd: * Successfully discovered: hlm.com
Sep :: hlmcen75n2 realmd: * Required files: /usr/sbin/oddjobd, /usr/libexec/oddjob/mkhomedir, /usr/sbin/sssd, /usr/sbin/adcli
Sep :: hlmcen75n2 realmd: * LANG=C /usr/sbin/adcli join --verbose --domain hlm.com --domain-realm HLM.COM --domain-controller 10.0.0.6 --login-type user --login-user stone --stdin-password
Sep :: hlmcen75n2 realmd: * Using domain name: hlm.com
Sep :: hlmcen75n2 realmd: * Calculated computer account name from fqdn: HLMCEN75N2
Sep :: hlmcen75n2 realmd: * Using domain realm: hlm.com
Sep :: hlmcen75n2 realmd: * Sending netlogon pings to domain controller: cldap://10.0.0.6
Sep :: hlmcen75n2 realmd: * Received NetLogon info from: hlm12r2n1.hlm.com
Sep :: hlmcen75n2 realmd: * Wrote out krb5.conf snippet to /var/cache/realmd/adcli-krb5-zqaVb2/krb5.d/adcli-krb5-conf-N3Soi1
Sep :: hlmcen75n2 realmd: * Authenticated as user: stone@HLM.COM
Sep :: hlmcen75n2 realmd: * Looked up short domain name: HLM
Sep :: hlmcen75n2 realmd: * Using fully qualified name: hlmcen75n2
Sep :: hlmcen75n2 realmd: * Using domain name: hlm.com
Sep :: hlmcen75n2 realmd: * Using computer account name: HLMCEN75N2
Sep :: hlmcen75n2 realmd: * Using domain realm: hlm.com
Sep :: hlmcen75n2 realmd: * Calculated computer account name from fqdn: HLMCEN75N2
Sep :: hlmcen75n2 realmd: * Generated character computer password
Sep :: hlmcen75n2 realmd: * Using keytab: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * Found computer account for HLMCEN75N2$ at: CN=HLMCEN75N2,CN=Computers,DC=hlm,DC=com
Sep :: hlmcen75n2 realmd: * Sending netlogon pings to domain controller: cldap://10.0.0.6
Sep :: hlmcen75n2 realmd: * Received NetLogon info from: hlm12r2n1.hlm.com
Sep :: hlmcen75n2 realmd: * Set computer password
Sep :: hlmcen75n2 realmd: * Retrieved kvno '' for computer account in directory: CN=HLMCEN75N2,CN=Computers,DC=hlm,DC=com
Sep :: hlmcen75n2 realmd: * Modifying computer account: userAccountControl
Sep :: hlmcen75n2 realmd: * Modifying computer account: operatingSystemVersion, operatingSystemServicePack
Sep :: hlmcen75n2 realmd: * Modifying computer account: userPrincipalName
Sep :: hlmcen75n2 realmd: ! Couldn't set service principals on computer account CN=HLMCEN75N2,CN=Computers,DC=hlm,DC=com: 00002083: AtrErr: DSID-03151337, #1:
Sep :: hlmcen75n2 realmd: #: : DSID-, problem (ATT_OR_VALUE_EXISTS), data , Att (servicePrincipalName)
Sep :: hlmcen75n2 realmd:
Sep :: hlmcen75n2 realmd: * Discovered which keytab salt to use
Sep :: hlmcen75n2 realmd: * Added the entries to the keytab: HLMCEN75N2$@HLM.COM: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * Added the entries to the keytab: host/HLMCEN75N2@HLM.COM: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * Added the entries to the keytab: host/hlmcen75n2@HLM.COM: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * Added the entries to the keytab: RestrictedKrbHost/HLMCEN75N2@HLM.COM: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * Added the entries to the keytab: RestrictedKrbHost/hlmcen75n2@HLM.COM: FILE:/etc/krb5.keytab
Sep :: hlmcen75n2 realmd: * /usr/bin/systemctl enable sssd.service
Sep :: hlmcen75n2 realmd: Created symlink from /etc/systemd/system/multi-user.target.wants/sssd.service to /usr/lib/systemd/system/sssd.service.
Sep :: hlmcen75n2 systemd: Reloading.
Sep :: hlmcen75n2 realmd: * /usr/bin/systemctl restart sssd.service
Sep :: hlmcen75n2 systemd: Starting System Security Services Daemon...
Sep :: hlmcen75n2 sssd: Starting up
Sep :: hlmcen75n2 sssd[be[hlm.com]]: Starting up
Sep :: hlmcen75n2 sssd[nss]: Starting up
Sep :: hlmcen75n2 sssd[pam]: Starting up
Sep :: hlmcen75n2 systemd: Started System Security Services Daemon.
Sep :: hlmcen75n2 realmd: * /usr/bin/sh -c /usr/sbin/authconfig --update --enablesssd --enablesssdauth --enablemkhomedir --nostart && /usr/bin/systemctl enable oddjobd.service && /usr/bin/systemctl start oddjobd.service
Sep :: hlmcen75n2 systemd: Reloading.
Sep :: hlmcen75n2 systemd: Reloading.
Sep :: hlmcen75n2 realmd: * Successfully enrolled machine in realm
执行命令:realm list列出域的相关信息,messages日志发现相应的记录信息如下:
Sep :: hlmcen75n2 dbus[]: [system] Activating via systemd: service name='org.freedesktop.realmd' unit='realmd.service'
Sep :: hlmcen75n2 systemd: Starting Realm and Domain Configuration...
Sep :: hlmcen75n2 dbus[]: [system] Successfully activated service 'org.freedesktop.realmd'
Sep :: hlmcen75n2 systemd: Started Realm and Domain Configuration.
执行命令:realm leave hlm.com,messages日志发现脱域的相关记录如下:
Sep :: hlmcen75n2 python: // ::39.018384 INFO Event: name=WALinuxAgent, op=HeartBeat, message=, duration=
Sep :: hlmcen75n2 realmd: * Removing entries from keytab for realm
Sep :: hlmcen75n2 realmd: * /usr/sbin/sss_cache --users --groups --netgroups --services --autofs-maps
Sep :: hlmcen75n2 realmd: * Removing domain configuration from sssd.conf
Sep :: hlmcen75n2 realmd: * /usr/sbin/authconfig --update --disablesssdauth --nostart
Sep :: hlmcen75n2 systemd: Reloading.
Sep :: hlmcen75n2 realmd: * /usr/bin/systemctl disable sssd.service
Sep :: hlmcen75n2 realmd: Removed symlink /etc/systemd/system/multi-user.target.wants/sssd.service.
Sep :: hlmcen75n2 systemd: Reloading.
Sep :: hlmcen75n2 realmd: * /usr/bin/systemctl stop sssd.service
Sep :: hlmcen75n2 systemd: Stopping System Security Services Daemon...
Sep :: hlmcen75n2 sssd[nss]: Shutting down
Sep :: hlmcen75n2 sssd[be[hlm.com]]: Shutting down
Sep :: hlmcen75n2 sssd[pam]: Shutting down
Sep :: hlmcen75n2 systemd: Stopped System Security Services Daemon.
Sep :: hlmcen75n2 realmd: * Successfully unenrolled machine from realm
在测试时,发现加域的命令为 "realm join hlm.com -U stone" 时,可以成功加入域,但无法设别DC下的用户,需要在域名前加上DC的主机名,正确加域的命令为 "realm join hlm12r2n1.hlm.com -U stone"
Linux 服务器加入Windows AD的更多相关文章
- linux服务器加入windows域时报错Ticket expired
[root@rusky]# net ads join -U administrator Enter administrator's password: kinit succeeded but ads_ ...
- 如何在Linux服务器和windows系统之间上传与下载文件
Do not let dream just be your dream. 背景:Linux服务器文件上传下载. XShell+Xftp安装包(解压即用)百度网盘链接:https://pan.baidu ...
- Linux服务器挂载windows共享文件夹和nas存储
需求: 公司有3.4T多的小文件需要copy到公司内部的nas存储中,由于小文件太多,数据量太大,整盘copy时速度极慢:只能人工对3.4T多的数据分批次的导入,这对于搞计算机的来说是不能忍受的,于是 ...
- 上传文件到阿里云linux服务器(windows到Linux的文件上传)
在"运行"中输入cmd,打开控制台,切换到刚才Putty的安装目录下,我的是E:\Putty,然后输入pscp命令,我们需要这个命令来实现文件的上传.如下命令格式: F:\PuTT ...
- 使用frp进行内网穿透,实现ssh远程访问Linux服务器
搭建一个完整的frp服务链需要: VPS一台(也可以是具有公网IP的实体机) 访问目标设备(就是你最终要访问的设备) 简单的Linux基础(如果基于Linux配置的话) 我这里使用了腾讯云服务器作为服 ...
- windows下运行的linux服务器批量管理工具(带UI界面)
产生背景: 由于做服务器运维方面的工作,需要一人对近千台LINUX服务器进行统一集中的管理,如同时批量对LINUX服务器执行相关的指令.同时批量对LINUX服务器upload程序包.同时批量对LINU ...
- 使用pscp实现Windows 和 Linux服务器间远程拷贝文件
转自:http://www.linuxidc.com/Linux/2012-05/60966.htm 在工作中,每次部署应用时都需要从本机Windows服务器拷贝文件到Linux上,有时还将Linux ...
- 从Windows 服务器通过sync向Linux服务器定时同步文件
本文解决的是Windows 下目录及文件向Linux同步的问题,Windows向 Windows同步的请参考:http://www.idcfree.com/article-852-1.html 环境介 ...
- SVN服务器从Windows迁移到Linux
gerui 2013.9.14 ge-rui@sohu.com 一.备份VisualSVN项目 1. 现在要使用Linux作为svn服务器,之前是在windows Server 2008上的,用的是V ...
随机推荐
- 62. Unique Paths (Graph; DP)
A robot is located at the top-left corner of a m x n grid (marked 'Start' in the diagram below). The ...
- MySQL 根据年、季度、月、周、日统计数据
-- 计算每年订单的总价格 select date_format(t.order_time,'%Y') years,sum(t.order_amount) '总价格' from lf_order t ...
- 文件读取草稿(excel,csv)
using NPOI.XSSF.UserModel; using System; using System.Collections.Generic; using System.Data; using ...
- oj1089-1096总结(输入输出练习)
//无限输出类 #include<stdio.h>int main(void){ int a,b; while((scanf("%d %d",&a,&b ...
- mysql的.sql文件头部 /*!32312 IF NOT EXISTS*/;
/*!40101 SET @OLD_CHARACTER_SET_CLIENT=@@CHARACTER_SET_CLIENT */; /*!40101 SET @OLD_CHARACTER_SET_RE ...
- What Are Tango Poses?Tango姿态是什么?
What Are Tango Poses?什么是Tango姿态? As your device moves through 3D space, it calculates where it is ( ...
- (广搜) Find a way -- hdu -- 2612
链接: http://acm.hdu.edu.cn/showproblem.php?pid=2612 Find a way Time Limit: 3000/1000 MS (Java/Others) ...
- Poj2231 Moo Volume 2017-03-11 22:58 30人阅读 评论(0) 收藏
Moo Volume Time Limit: 1000MS Memory Limit: 65536K Total Submissions: 22104 Accepted: 6692 Descr ...
- handsontable-integrations
jquery:可以通过$选择元素 bootstrap:使用bootstrap,有些样式需要重置 backbone:整合
- [转载]MVC、MVP以及Model2(下)
通过采用MVC模式,我们可以将可视化UI元素的呈现.UI处理逻辑和业务逻辑分别定义在View.Controller和Model中,但是对于三者之间的交互,MVC并没有进行严格的限制.最为典型的就是允许 ...
