POJ - 1107 W's Cipher
POJ - 1107 W's Cipher
Time Limit: 1000MS |
Memory Limit: 10000KB |
64bit IO Format: %I64d & %I64u |
Description
Weird Wally's Wireless Widgets, Inc. manufactures an eclectic assortment of small, wireless, network capable devices, ranging from dog collars, to pencils, to fishing bobbers. All these devices have very small memories. Encryption algorithms like Rijndael, the candidate for the Advanced Encryption Standard (AES) are demonstrably secure but they don't fit in such a tiny memory. In order to provide some security for transmissions to and from the devices, WWWW uses the following algorithm, which you are to implement.
Encrypting a message requires three integer keys, k1, k2, and k3. The letters [a-i] form one group, [j-r] a second group, and everything else ([s-z] and underscore) the third group. Within each group the letters are rotated left by ki positions in the message. Each group is rotated independently of the other two. Decrypting the message means doing a right rotation by ki positions within each group.
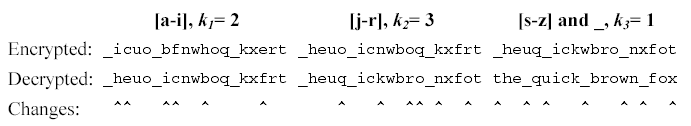
Consider the message the_quick_brown_fox encrypted with ki values of 2, 3 and 1. The encrypted string is _icuo_bfnwhoq_kxert. The figure below shows the decrypting right rotations for one character in each of the three character groups.
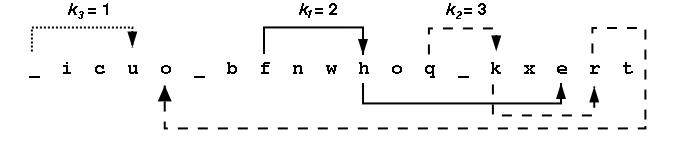
Looking at all the letters in the group [a-i] we see {i,c,b,f,h,e} appear at positions {2,3,7,8,11,17} within the encrypted message. After a right rotation of k1=2, these positions contain the letters {h,e,i,c,b,f}. The table below shows the intermediate strings that come from doing all the rotations in the first group, then all rotations in the second group, then all the rotations in the third group. Rotating letters in one group will not change any letters in any of the other groups.
All input strings contain only lowercase letters and underscores(_). Each string will be at most 80 characters long. The ki are all positive integers in the range 1-100.
Input
Input consists of information for one or more encrypted messages. Each problem begins with one line containing k1, k2, and k3 followed by a line containing the encrypted message. The end of the input is signalled by a line with all key values of 0.
Output
For each encrypted message, the output is a single line containing the decrypted string.
Sample Input
2 3 1
_icuo_bfnwhoq_kxert
1 1 1
bcalmkyzx
3 7 4
wcb_mxfep_dorul_eov_qtkrhe_ozany_dgtoh_u_eji
2 4 3
cjvdksaltbmu
0 0 0
Sample Output
the_quick_brown_fox
abcklmxyz
the_quick_brown_fox_jumped_over_the_lazy_dog
ajsbktcludmv
Source
#include<stdio.h>
#include<string.h>
char str[] = {};
char str1[] = {};
char str2[] = {};
char str3[] = {}; int main()
{
int a, b, c, len, alen, blen, clen;
while(scanf("%d%d%d", &a, &b, &c)) {
if(a == && b == && c == ) {
break;
}
scanf("%s", str);
len = strlen(str);
alen = blen = clen = ;
for(int i = ; i < len; i++) {
if(str[i] >= 'a' && str[i] <= 'i') {
str1[alen] = str[i];
alen++;
}
else if(str[i] >= 'j' && str[i] <= 'r') {
str2[blen] = str[i];
blen++;
}
else {
str3[clen] = str[i];
clen++;
}
}
// puts(str1);
// puts(str2);
// puts(str3); if(alen != ) a = a % alen;//这一步是关键
if(blen != ) b = b % blen;//这一步是关键
if(clen != ) c = c % clen;//这一步是关键
int t1 = , t2 = , t3 = ;
for(int i = ; i < len; i++) {
if(str[i] >= 'a' && str[i] <= 'i') {
printf("%c", str1[(t1-a+alen)%alen]);
t1++;
}
else if(str[i] >= 'j' && str[i] <= 'r') {
printf("%c", str2[(t2-b+blen)%blen]);
t2++;
}
else {
printf("%c", str3[(t3-c+clen)%clen]);
t3++;
}
}
printf("\n");
} return ;
}
POJ - 1107 W's Cipher的更多相关文章
- poj 2159 D - Ancient Cipher 文件加密
Ancient Cipher Description Ancient Roman empire had a strong government system with various departme ...
- ZOJ 1042 W’s Cipher
原题链接 题目大意:按照规则解码.26个字母分成三组,每一组按照顺时针移位编码.现在已知移动的位数,要求解码. 解法:以前看过一本古典密码学的书,百度贴吧密码吧也有很多经典的加密方法,想什么凯撒移位. ...
- POJ 1107
水题一道,注意取模时不能为0 #include <iostream> #include <algorithm> #include <cstring> #includ ...
- POJ题目细究
acm之pku题目分类 对ACM有兴趣的同学们可以看看 DP: 1011 NTA 简单题 1013 Great Equipment 简单题 102 ...
- 【转】POJ百道水题列表
以下是poj百道水题,新手可以考虑从这里刷起 搜索1002 Fire Net1004 Anagrams by Stack1005 Jugs1008 Gnome Tetravex1091 Knight ...
- HOJ题目分类
各种杂题,水题,模拟,包括简单数论. 1001 A+B 1002 A+B+C 1009 Fat Cat 1010 The Angle 1011 Unix ls 1012 Decoding Task 1 ...
- PHP的AES加密类
PHP的AES加密类 aes.php <?php /* - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - ...
- ethereumjs/ethereumjs-wallet
Utilities for handling Ethereum keys ethereumjs-wallet A lightweight wallet implementation. At the m ...
- SSIS 学习之旅 FTP文件传输-脚本任务
这一章主要讲解一下用脚本怎么把CSV文件抛送到FTP服务器上 设计: 通过Demon库的Users表数据生成CSV文件. 生成后的CSV文件抛送到FTP指定目录下. 控件的使用这里就不做详细讲 ...
随机推荐
- Material Design - CollapsingToolbarLayout
一.概述 CollapsingToolbarLayout是Material Design的一个Layout,直接继承于FrameLayout. 二.使用 1.导包 2.使用 - 设置相关属性 三.参考 ...
- Hadoop.2.x_伪分布环境搭建
一. 基本环境搭建 1. 设置主机名.静态IP/DNS.主机映射.windows主机映射(方便ssh访问与IP修改)等 设置主机名: vi /etc/sysconfig/network # 重启系统生 ...
- jQuery -> 获取元素的各种过滤器
转自http://blog.csdn.net/feelang/article/details/26613023
- Tomcat启动脚本catalina.sh
1 - 概述脚本catalina.sh用于启动和关闭tomcat服务器,是最关键的脚本另外的脚本startup.sh和shutdown.sh都是使用不同的参数调用了该脚本该脚本的使用方法如下(引自该脚 ...
- CSS3初学篇章_3(属性选择符/字体样式/元素样式)
属性选择符 选择符 说明 E[att] 选择具有att属性的E元素. E[att="val"] 选择具有att属性且属性值等于val的E元素. E[att~=&quo ...
- springmvc4+hibernate4+spring4注解一对多级联保存
package com.h3c.zgc.user.entity; import java.util.HashSet; import java.util.Set; import javax.persis ...
- 使用Sublime Text 直接运行Quick-cocos2d-x 项目
一.新建一个编译系统 { "cmd": "D:/WorkSoftWare/Quick/quick-cocos2d-x-3.3rc0/quick/samples/Runni ...
- php获取真实IP地址
function user_realip() { if (getenv('HTTP_CLIENT_IP')) { $ip = getenv('HTTP_CLIENT_IP'); } elseif (g ...
- Silverlight控件——如何提升应用程序信任度与问题解决
从silverlight5开始,可以在项目设置中勾选“在浏览器内运行时需要提升的信任”来达到在浏览器内运行提权silverlight客户端的目的,在个特性很有用处. 可我使用这个功能时遇到了一个奇怪的 ...
- Python3.5连接Mysql
由于mysqldb目前仅支持到python3.4,所以这里选择pymysql. pymysql下载地址: https://pypi.python.org/packages/source/P/PyMyS ...
