Cppcheck 1.54 C/C++静态代码分析工具

1.使用Visual C++的话,应使用警告等级4
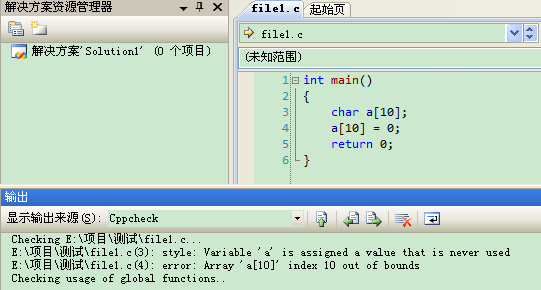
 可以添加检测的目录,但是这里不支持中文路径。测试官方的例子,新建一个文件file1.c,内容如下:
可以添加检测的目录,但是这里不支持中文路径。测试官方的例子,新建一个文件file1.c,内容如下:a[] ;
;
}
用此工具进行检测,结果如下图所示: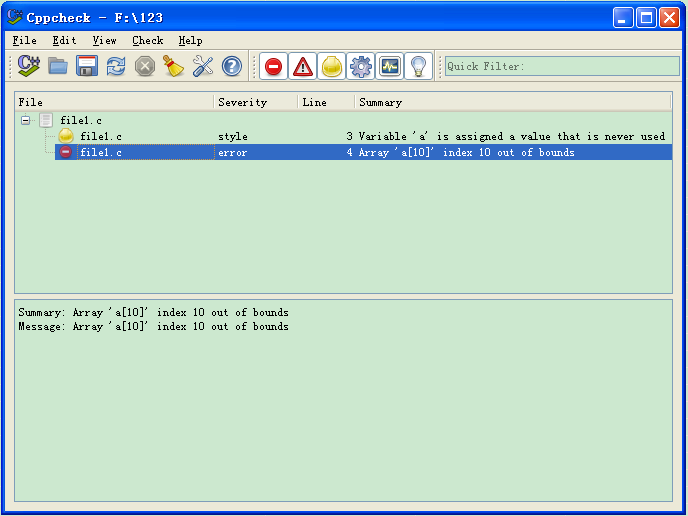
在Visual Studio下使用的话,步骤如下:
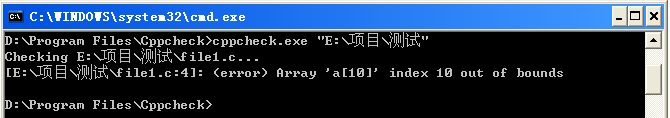
命令:D:\Program Files\Cppcheck\cppcheck.exe
参数:--enable=all--template=vs $(SolutionDir)
勾选"使用输出窗口"
2.使用时,点击"工具"→"Cppcheck"即可,如下图所示:
双击提示内容,即可定位到所在行。
If a directory is given instead of a filename, *.cpp, *.cxx, *.cc, *.c++, *.c, *.tpp, and *.txx files are checked recursively from the given directory.
| --append=<file> | This allows you to provide information about functions by providing an implementation for them. |
| --check-config | Check cppcheck configuration. The normal code analysis is disabled by this flag. |
| -D<ID> | By default Cppcheck checks all configurations. Use -D to limit the checking to a particular configuration. Example: '-DDEBUG=1 -D__cplusplus'. |
| -U<ID> | By default Cppcheck checks all configurations. Use -U to explicitly hide certain #ifdef <ID> code paths from checking. Example: '-UDEBUG' |
| --enable=<id> | Enable additional checks. The available ids are: * all Enable all checks * style Enable all coding style checks. All messages with the severities 'style', 'performance' and 'portability' are enabled. * performance Enable performance messages * portability Enable portability messages * information Enable information messages * unusedFunction Check for unused functions * missingInclude Warn if there are missing includes. For detailed information, use '--check-config'. Several ids can be given if you separate them with commas. See also --std |
| --error-exitcode=<n> | If errors are found, integer [n] is returned instead of the default '0'. '1' is returned if arguments are not valid or if no input files are provided. Note that your operating system can modify this value, e.g. '256' can become '0'. |
| --errorlist | Print a list of all the error messages in XML format. |
| --exitcode-suppressions=<file> | Used when certain messages should be displayed but should not cause a non-zero exitcode. |
| --file-list=<file> | Specify the files to check in a text file. Add one filename per line. When file is '-,' the file list will be read from standard input. |
| -f, --force | Force checking of all configurations in files. If used together with '--max-ifdefs=', the last option is the one that is effective. |
| -h, --help | Print this help. |
| -I <dir> | Give path to search for include files. Give several -I parameters to give several paths. First given path is searched for contained header files first. If paths are relative to source files, this is not needed. |
| --includes-file=<file> | Specify directory paths to search for included header files in a text file. Add one include path per line. First given path is searched for contained header files first. If paths are relative to source files, this is not needed. |
| -i <dir or file> | Give a source file or source file directory to exclude from the check. This applies only to source files so header files included by source files are not matched. Directory name is matched to all parts of the path. |
| --inline-suppr | Enable inline suppressions. Use them by placing one or more comments, like: '// cppcheck-suppress warningId' on the lines before the warning to suppress. |
| -j <jobs> | Start [jobs] threads to do the checking simultaneously. |
| --max-configs=<limit> | Maximum number of configurations to check in a file before skipping it. Default is '12'. If used together with '--force', the last option is the one that is effective. |
| --platform=<type> | Specifies platform specific types and sizes. The available platforms are: * unix32 32 bit unix variant * unix64 64 bit unix variant * win32A 32 bit Windows ASCII character encoding * win32W 32 bit Windows UNICODE character encoding * win64 64 bit Windows |
| -q, --quiet | Only print error messages. |
| -rp, --relative-paths -rp=<paths>, --relative-paths=<paths> |
Use relative paths in output. When given, <paths> are used as base. You can separate multiple paths by ';'. Otherwise path where source files are searched is used. We use string comparison to create relative paths, so using e.g. ~ for home folder does not work. It is currently only possible to apply the base paths to files that are on a lower level in the directory tree. |
| --report-progress | Report progress messages while checking a file. |
| --rule=<rule> | Match regular expression. |
| --rule-file=<file> | Use given rule file. For more information, see: https://sourceforge.net/projects/cppcheck/files/Articles/ |
| -s, --style | Deprecated, please use '--enable=style' instead |
| --std=<id> | Enable some standard related checks. The available options are: * posix Checks related to POSIX-specific functionality * c99 C99 standard related checks * c++11 C++11 standard related checks Example to enable more than one checks: 'cppcheck --std=c99 --std=posix file.cpp' |
| --suppress=<spec> | Suppress warnings that match <spec>. The format of <spec> is: [error id]:[filename]:[line] The [filename] and [line] are optional. If [error id] is a wildcard '*', all error ids match. |
| --suppressions-list=<file> | Suppress warnings listed in the file. Each suppression is in the same format as <spec> above. |
| --template='<text>' | Format the error messages. E.g. '{file}:{line},{severity},{id},{message}' or '{file}({line}):({severity}) {message}' Pre-defined templates: gcc, vs, edit. |
| -v, --verbose | Output more detailed error information. |
| --version | Print out version number. |
| --xml | Write results in xml format to error stream (stderr). |
| --xml-version=<version> | Select the XML file version. Currently versions 1 and 2 are available. The default version is 1. |
cppcheck -I inc1/ -I inc2/ f.cpp
64-bit portability
Check if there is 64-bit portability issues:
- assign address to/from int/long
Auto Variables
A pointer to a variable is only valid as long as the variable is in scope. Check:
- returning a pointer to auto or temporary variable
- assigning address of an variable to an effective parameter of a function
- returning reference to local/temporary variable
- returning address of function parameter
Boost usage
Check for invalid usage of Boost:
- container modification during BOOST_FOREACH
Bounds checking
out of bounds checking
Class
Check the code for each class.
- Missing constructors
- Are all variables initialized by the constructors?
- Warn if memset, memcpy etc are used on a class
- If it's a base class, check that the destructor is virtual
- Are there unused private functions
- 'operator=' should return reference to self
- 'operator=' should check for assignment to self
- Constness for member functions
Exception Safety
Checking exception safety
- Throwing exceptions in destructors
- Throwing exception during invalid state
- Throwing a copy of a caught exception instead of rethrowing the original exception
- exception caught by value instead of by reference
Match assignments and conditions
Match assignments and conditions:
- Mismatching assignment and comparison => comparison is always true/false
- Mismatching lhs and rhs in comparison => comparison is always true/false
- Detect matching 'if' and 'else if' conditions
Memory leaks (address not taken)
Not taking the address to allocated memory
Memory leaks (class variables)
If the constructor allocate memory then the destructor must deallocate it.
Memory leaks (function variables)
Is there any allocated memory when a function goes out of scope
Memory leaks (struct members)
Don't forget to deallocate struct members
Non reentrant functions
Warn if any of these non reentrant functions are used:
- crypt
- ctermid
- ecvt
- fcvt
- fgetgrent
- fgetpwent
- fgetspent
- gcvt
- getgrent
- getgrgid
- getgrnam
- gethostbyaddr
- gethostbyname
- gethostbyname2
- gethostent
- getlogin
- getnetbyaddr
- getnetbyname
- getnetgrent
- getprotobyname
- getpwent
- getpwnam
- getpwuid
- getrpcbyname
- getrpcbynumber
- getrpcent
- getservbyname
- getservbyport
- getservent
- getspent
- getspnam
- gmtime
- localtime
- readdir
- strtok
- tempnam
- ttyname
Null pointer
Null pointers
- null pointer dereferencing
Obsolete functions
Warn if any of these obsolete functions are used:
- asctime
- asctime_r
- bcmp
- bcopy
- bsd_signal
- bzero
- ctime
- ctime_r
- ecvt
- fcvt
- ftime
- gcvt
- getcontext
- gethostbyaddr
- gethostbyname
- getwd
- index
- makecontext
- pthread_attr_getstackaddr
- pthread_attr_setstackaddr
- rand_r
- rindex
- scalbln
- swapcontext
- tmpnam
- tmpnam_r
- ualarm
- usleep
- utime
- vfork
- wcswcs
Other
Other checks
- Assigning bool value to pointer (converting bool value to address)
- bad usage of the function 'sprintf' (overlapping data)
- division with zero
- using fflush() on an input stream
- scoped object destroyed immediately after construction
- assignment in an assert statement
- sizeof for array given as function argument
- sizeof for numeric given as function argument
- using sizeof(pointer) instead of the size of pointed data
- incorrect length arguments for 'substr' and 'strncmp'
- invalid usage of output stream. For example: std::cout << std::cout;'
- wrong number of arguments given to 'printf' or 'scanf;'
- double free() or double closedir()
- C-style pointer cast in cpp file
- casting between incompatible pointer types
- redundant if
- bad usage of the function 'strtol'
- unsigned division
- Dangerous usage of 'scanf'
- passing parameter by value
- Incomplete statement
- check how signed char variables are used
- variable scope can be limited
- condition that is always true/false
- unusal pointer arithmetic. For example: "abc" + 'd'
- redundant assignment in a switch statement
- redundant strcpy in a switch statement
- look for 'sizeof sizeof ..'
- look for calculations inside sizeof()
- assignment of a variable to itself
- mutual exclusion over || always evaluating to true
- Clarify calculation with parentheses
- using increment on boolean
- comparison of a boolean with a non-zero integer
- comparison of a boolean expression with an integer other than 0 or 1
- suspicious condition (assignment+comparison)
- suspicious condition (runtime comparison of string literals)
- suspicious condition (string literals as boolean)
- duplicate break statement
- unreachable code
- testing if unsigned variable is negative
- testing is unsigned variable is positive
- using bool in bitwise expression
- Suspicious use of ; at the end of 'if/for/while' statement.
- incorrect usage of functions from ctype library.
- optimisation: detect post increment/decrement
STL usage
Check for invalid usage of STL:
- out of bounds errors
- misuse of iterators when iterating through a container
- mismatching containers in calls
- dereferencing an erased iterator
- for vectors: using iterator/pointer after push_back has been used
- optimisation: use empty() instead of size() to guarantee fast code
- suspicious condition when using find
- redundant condition
- common mistakes when using string::c_str()
- using auto pointer (auto_ptr)
- useless calls of string functions
Uninitialized variables
Uninitialized variables
- using uninitialized variables and data
Unused functions
Check for functions that are never called
UnusedVar
UnusedVar checks
- unused variable
- allocated but unused variable
- unred variable
- unassigned variable
- unused struct member
Using postfix operators
Warn if using postfix operators ++ or -- rather than prefix operator
Cppcheck 1.54 C/C++静态代码分析工具的更多相关文章
- 常用 Java 静态代码分析工具的分析与比较
常用 Java 静态代码分析工具的分析与比较 简介: 本文首先介绍了静态代码分析的基 本概念及主要技术,随后分别介绍了现有 4 种主流 Java 静态代码分析工具 (Checkstyle,FindBu ...
- C++静态代码分析工具推荐——PVS-Studio
长假归来,最近一直没更新,节前本来就想写这篇了,一直到今天才有时间. 关于静态代码分析在维基百科上可以查到很详细的介绍:https://en.wikipedia.org/wiki/List_of_to ...
- [转载] 常用 Java 静态代码分析工具的分析与比较
转载自http://www.oschina.net/question/129540_23043 简介: 本文首先介绍了静态代码分析的基本概念及主要技术,随后分别介绍了现有 4 种主流 Java 静态代 ...
- 来试试这个来自静态代码分析工具PVS Studio提供C++的小测验吧
博客搬到了fresky.github.io - Dawei XU,请各位看官挪步.最新的一篇是:来试试这个来自静态代码分析工具PVS Studio提供C++的小测验吧.
- 【转载】常用 Java 静态代码分析工具的分析与比较
摘自:http://www.oschina.net/question/129540_23043常用 Java 静态代码分析工具的分析与比较 简介: 本文首先介绍了静态代码分析的基本概念及主要技术,随后 ...
- java静态代码分析工具infer
infer是一个静态代码分析工具,探测bugs. 主要支持Java.C/C++ 安装:brew install infer 在线展示:https://codeboard.io/projects/115 ...
- Https与Http,SSL,DevOps, 静态代码分析工具,RFID, SSH, 非对称加密算法(使用最广泛的一种是RSA), 数字签名, 数字证书
在URL前加https://前缀表明是用SSL加密的. 你的电脑与服务器之间收发的信息传输将更加安全. Web服务器启用SSL需要获得一个服务器证书并将该证书与要使用SSL的服务器绑定. http和h ...
- Eclipse插件(导出UML图,打开文件资源管理器插件,静态代码分析工具PMD,在eclipse上安装插件)
目录 能够导出UML图的Eclipse插件 打开文件资源管理器插件 Java静态代码分析工具PMD 如何在eclipse上安装插件 JProfiler性能分析工具 从更新站点安装EclEmma 能够导 ...
- Android 静态代码分析工具
简评: 作者在文中提到的三个静态代码分析工具不是互相替代的关系,各有各的侧重点,如果有需要完全可以同时使用. 静态代码分析是指无需运行被测代码,仅通过分析或检查源程序的语法.结构.过程.接口等来检查程 ...
随机推荐
- NET Core1
NET Core .net core最近园子讨论频率很高的话题,从不久前发布正式版本后,也是开始从netcore官网一步一步走向学习之路:.net跨平台的设计让人很是兴奋起来,因为做了多年的互联网研发 ...
- logback自定义格式转换器
创建自定义格式转换符有两步. 首先,必须继承ClassicConverter类.ClassicConverter对象负责从ILoggingEvent 提取信息,并产生一个字符串.例如,LoggerCo ...
- Mybatis 的Log4j日志输出问题 - 以及有关日志的所有问题
使用Mybatis的时候,有些时候能输出(主要是指sql,参数,结果)日志.有些时候就不能. 无法输出日志的时候,无论怎么配置log4j,不管是properties的还是xml的,都不起作用. 有些时 ...
- poj 1664 put apples(dfs)
题目链接:http://poj.org/problem?id=1664 思路分析:数据较小,考虑深度优先搜索搜索解空间. 代码如下: #include <iostream> using n ...
- SQL查询各阶段的统计信息
我们经常会遇到各种分类统计问题,须要将这些结果一次显示出来.这次老师提出的要求是我想看60分下面多少人.60~70多少人,70~80多少人.80~90多少人,90~100多少人.他们曾 ...
- 小猪猪C++笔记基础篇(六)参数传递、函数重载、函数指针、调试帮助
小猪猪C++笔记基础篇(六) ————参数传递.函数重载.函数指针.调试帮助 关键词:参数传递.函数重载.函数指针.调试帮助 因为一些事情以及自己的懒惰,大概有一个星期没有继续读书了,已经不行了,赶紧 ...
- 使用Intel编译器获得一致的浮点数值计算结果
使用Intel编译器获得一致的浮点数值计算结果大多数十进制的浮点数, 用二进制表示时不是完全一致的; 与此同时, 大多数与浮点数值相关的计算结果, 存在着固有的不确定性.通常, 编写浮点计算应用软件希 ...
- ibatis3.0调用Oracle的存储过程
直接上源码 一,oracle储存过程. create or replace procedure proc_get_th(i_hth in varchar2,o_ret out sys_refcurso ...
- js模态窗口
最近在看js,正好公司用的框架中用到了模态窗口,以前没有接触过,现在把模态窗口的用法先记下来. 常用的浏览器chrome,Firefox,ie11,这三种分别支持document.open(),win ...
- [转] iOS (OC) 中 KVC 与 KVO 理解
转自: http://magicalboy.com/kvc_and_kvo/ KVC 与 KVO 是 Objective C 的关键概念,个人认为必须理解的东西,下面是实例讲解. Key-Value ...
