12-kubernetes Dashboard 认证及分级授权
部署 dashboard
根据官方文的安装介绍,直接远程执行即可,这里先下载下来,然后执行:
[root@master ~]# wget https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/deploy/recommended/kubernetes-dashboard.yaml
[root@master ~]# kubectl apply -f kubernetes-dashboard.yaml
secret/kubernetes-dashboard-certs created
serviceaccount/kubernetes-dashboard created
role.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
deployment.apps/kubernetes-dashboard created
service/kubernetes-dashboard created
查看
[root@master ~]# kubectl get pods -n kube-system
NAME READY STATUS RESTARTS AGE
coredns-5c98db65d4-8mzfz 1/1 Running 0 44d
coredns-5c98db65d4-spjx8 1/1 Running 0 44d
etcd-master.kubernetes 1/1 Running 0 44d
kube-apiserver-master.kubernetes 1/1 Running 0 44d
kube-controller-manager-master.kubernetes 1/1 Running 0 44d
kube-flannel-ds-amd64-4szk7 1/1 Running 0 44d
kube-flannel-ds-amd64-b4ssp 1/1 Running 1 44d
kube-flannel-ds-amd64-nmklz 1/1 Running 0 44d
kube-flannel-ds-amd64-wjczq 1/1 Running 0 44d
kube-proxy-8fqsz 1/1 Running 0 44d
kube-proxy-bkrw4 1/1 Running 0 44d
kube-proxy-n75g8 1/1 Running 1 44d
kube-proxy-rmckk 1/1 Running 0 44d
kube-scheduler-master.kubernetes 1/1 Running 0 44d
kubernetes-dashboard-7d75c474bb-cqwh6 1/1 Running 0 18s # 已经启动成功
开放访问
默认dashboard中启动的svc只能集群内部访问,所以需要手动配置对外访问,打一个补丁即可:
[root@master ~]# kubectl patch svc kubernetes-dashboard -p '{"spec":{"type":"NodePort"}}' -n kube-system
service/kubernetes-dashboard patched
[root@master ~]# kubectl get svc -n kube-system
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP,9153/TCP 44d
kubernetes-dashboard NodePort 10.106.202.90 <none> 443:30090/TCP 3m16s
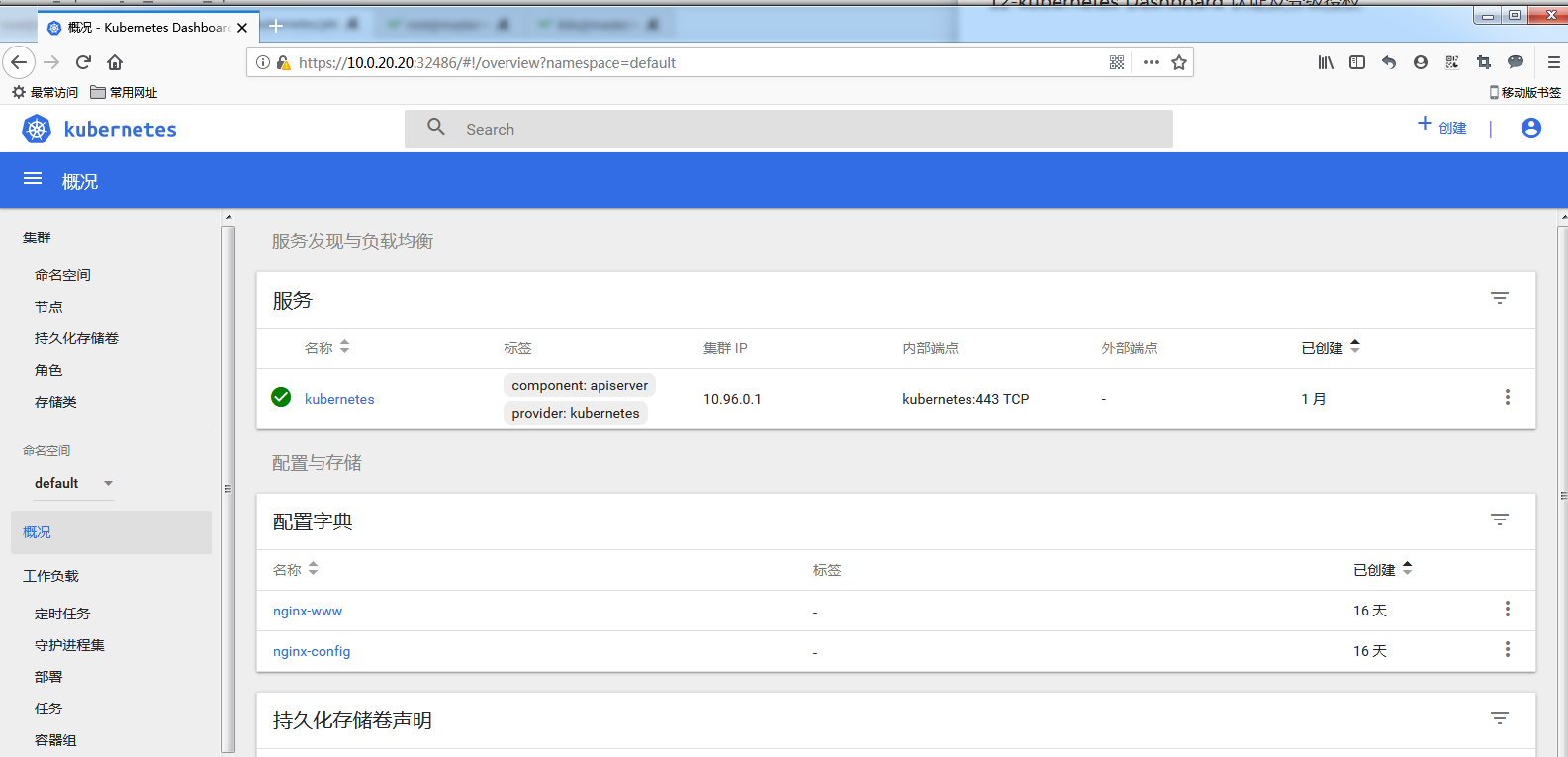
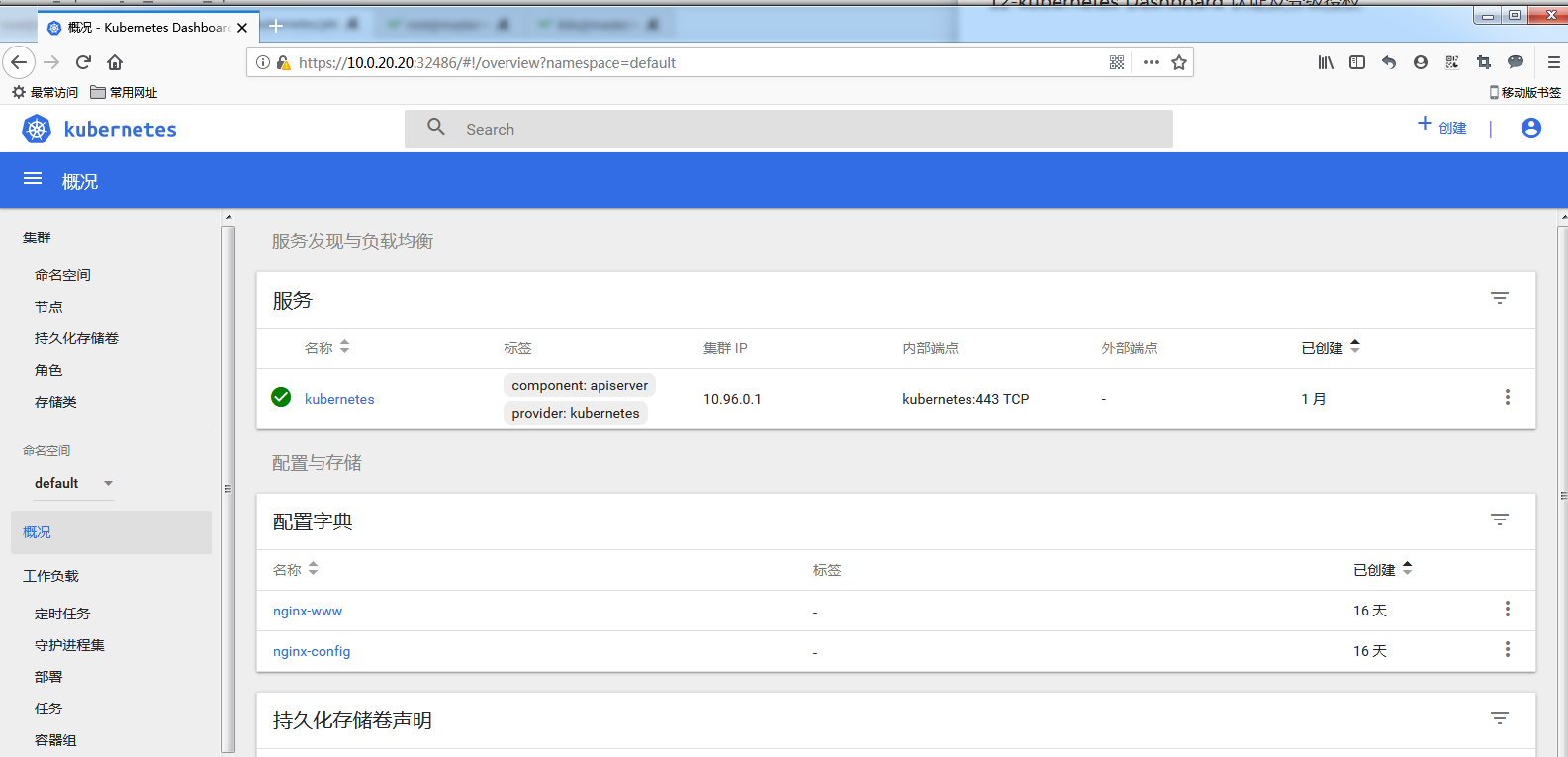
通过查看,dashboard的svc已经被映射到30090 这个端口,所以在浏览器直接输入任意节点的ip + 端口即可访问。
注意访问的地址是 https://IP:PORT

配置dashboard用户
Dashboard 登陆有两种认证方式:
- kubeconfig 文件认证
- token 令牌认证
下面对这两种认证都进行测试验证
1. token 令牌认证
创建一个 serviceAccount
在 kube-system 名称空间中创建
[root@master ~]# kubectl create serviceaccount dashboard-admin -n kube-system
[root@master ~]# kubectl describe sa/dashboard-admin -n kube-system
Name: dashboard-admin
Namespace: kube-system
Labels: <none>
Annotations: <none>
Image pull secrets: <none>
Mountable secrets: dashboard-admin-token-wrdvz
Tokens: dashboard-admin-token-wrdvz
Events: <none>
dashboard-admin 绑定 clusterbinding 的 sa
[root@master ~]# kubectl create clusterrolebinding dashboard-cluster-admin --clusterrole=cluster-admin --serviceaccount=kube-system:\dashboard-admin
clusterrolebinding.rbac.authorization.k8s.io/dashboard-cluster-admin created
[root@master ~]# kubectl describe clusterrolebinding/dashboard-cluster-admin
Name: dashboard-cluster-admin
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: cluster-admin
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount dashboard-admin kube-system
这帮绑定后,serviceaccount 的 dashboard-admin 就有集群的管理员权限了。
获取 serviceaccount 的 dashboard-admin 的secret信息
在创建好serviceaccount 的 dashboard-admin 后,会在 kube-system名称空间下的secret 中,自动创建一个 以 dashboard-admin 开头的 secret,携带者 token 字样
[root@master ~]# kubectl get secret -n kube-system
NAME TYPE DATA AGE
attachdetach-controller-token-7nxx6 kubernetes.io/service-account-token 3 44d
bootstrap-signer-token-c44r9 kubernetes.io/service-account-token 3 44d
bootstrap-token-cgw8vp bootstrap.kubernetes.io/token 7 44d
certificate-controller-token-6682d kubernetes.io/service-account-token 3 44d
clusterrole-aggregation-controller-token-g7l5s kubernetes.io/service-account-token 3 44d
coredns-token-gsrxq kubernetes.io/service-account-token 3 44d
cronjob-controller-token-qch7l kubernetes.io/service-account-token 3 44d
daemon-set-controller-token-gmp2z kubernetes.io/service-account-token 3 44d
# 下面这个就是自动生成的
dashboard-admin-token-wrdvz kubernetes.io/service-account-token 3 6m50s
default-token-ll59x kubernetes.io/service-account-token 3 44d
... ...
... ...
从上已经查看到了,下面需要查看一下详细信息即可获取到token的值
[root@master ~]# kubectl describe secret/dashboard-admin-token-wrdvz -n kube-system
Name: dashboard-admin-token-wrdvz
Namespace: kube-system
Labels: <none>
Annotations: kubernetes.io/service-account.name: dashboard-admin
kubernetes.io/service-account.uid: 4c593334-7f68-4190-85a2-f92fcab234d4
Type: kubernetes.io/service-account-token
Data
====
namespace: 11 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4td3JkdnoiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiNGM1OTMzMzQtN2Y2OC00MTkwLTg1YTItZjkyZmNhYjIzNGQ0Iiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmUtc3lzdGVtOmRhc2hib2FyZC1hZG1pbiJ9.YxE09BRCQbUA_nzE60s9eXOYZMjsWLEZfXqXuiRffpsl_KgfosSKtII_YbBESvLeaSi3qivrkgSNKHdPytS2zmZd9BdNbGbABjecRER5jSjNNeRjok6cixghSVR51VyzJN5PlpPHtlhOlshJLXg_IAXtYzq36AZTf4LQ5_17k_1DXIjOsL5j0N0CEljcQVvOhEPlyu3OGsVEJOijKSMcEXJmrV2z5Z4rUczSn83qNy1ZjT-DF2Avg3eMua5Pw0LkgP9zQF76q2MGYwWZDc5z0y53SoYxs7k12OKnRrHL0Vai11a8snGLH_Dt7jXY0UAKwpew6a6Gj4F4xsK1InxBtg
ca.crt: 1025 bytes
上面查看到的token 后面的一大串就是,把这一串复制到页面中就可以登录。

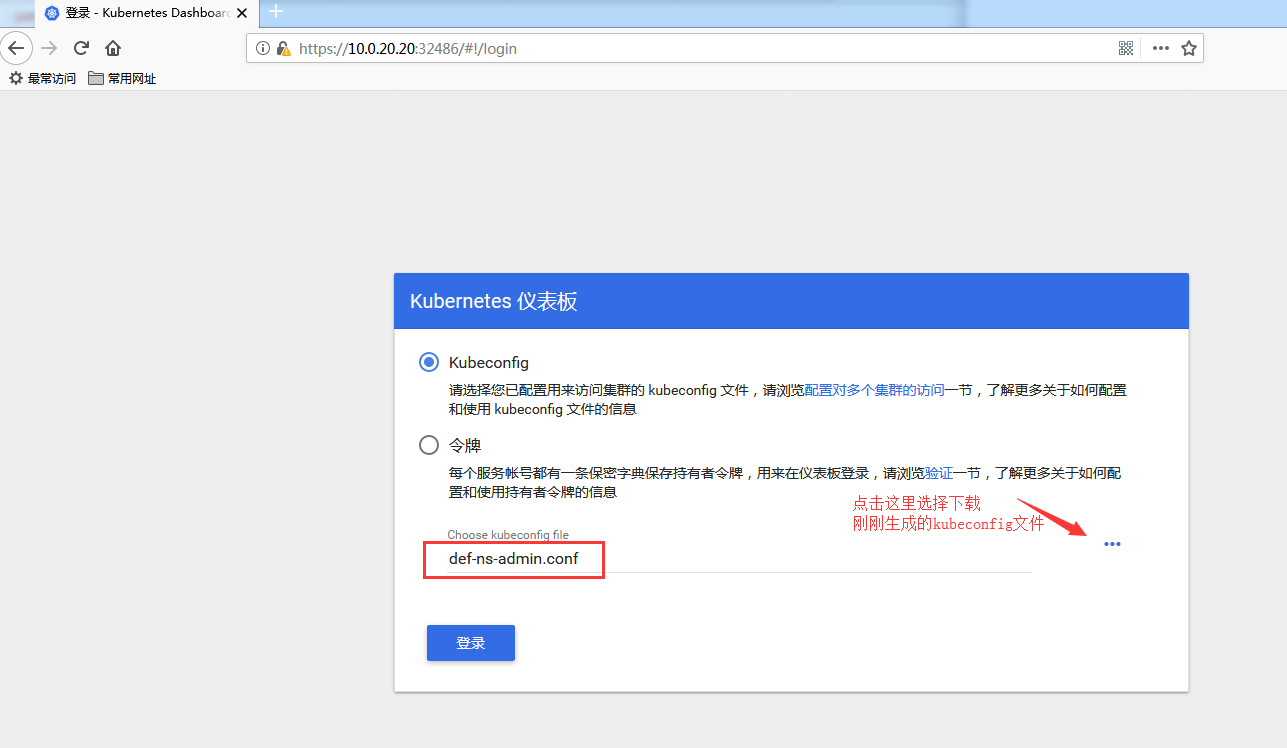
2. kubeconfig 文件认证
创建测试一个权限小一点的,只能访问default名称空间资源的账户
创建一个 serviceAccount
[root@master pki]# kubectl create serviceaccount def-ns-admin -n default
serviceaccount/def-ns-admin created
[root@master pki]# kubectl describe sa/def-ns-admin -n default
Name: def-ns-admin
Namespace: default
Labels: <none>
Annotations: <none>
Image pull secrets: <none>
Mountable secrets: def-ns-admin-token-qfrqj
Tokens: def-ns-admin-token-qfrqj
Events: <none>
创建 rolebinding 绑定 def-ns-admin
[root@master pki]# kubectl create rolebinding def-ns-admin --clusterrole=admin --serviceaccount=default:def-ns-admin
rolebinding.rbac.authorization.k8s.io/def-ns-admin created
[root@master pki]# kubectl describe rolebinding/def-ns-admin -n default
Name: def-ns-admin
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: admin
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount def-ns-admin default
提示:这里和上面一样,到此步骤系统已经自动创建出一个secret,详细信息中包含token,可以直接使用此token登录dashboard,只能管理default名称空间下的资源。
创建集群和创建kubeconfig配置文件
[root@master pki]#
[root@master pki]# kubectl config set-cluster kubernetes --certificate-authority=./ca.crt --server="https://10.0.20.20:6443" --embed-certs=true --kubeconfig=/root/def-ns-admin.conf
Cluster "kubernetes" set.
[root@master pki]# kubectl config view --kubeconfig=/root/def-ns-admin.conf
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://10.0.20.20:6443
name: kubernetes
contexts: []
current-context: ""
kind: Config
preferences: {}
users: []
拿到 def-ns-admin 用户的base64格式的token
先拿到对应的token后base64 解码
[root@master pki]# kubectl get secret def-ns-admin-token-qfrqj -o jsonpath={.data.token} | base64 -d
eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1xZnJxaiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI2ZGU3NWU2Mi1hYjViLTQyMWItOTJhYS0zN2IyMjRmODBmNjEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.k7Oq2V93mz60qxP8Xb2zOoJ9GwnlGbQjeYLJqfqTp-tuhThi_s542GpPWYvEdha-kuxYuyxRf_MUEg-YBCmilS0mqQBVoiHdvJCH6kQTbdZCpJOlML5jXHX9py7TJr8grFHI1aoyo5ZXDM8yZ9tULCpVNLVRz6sCh2wHcCP-pNIA2eaiM_3xM6Ow-0igYe2lxsv2pZcMUWNdi-ImZ9Vv72Nb9sn9rzp2de9RbZ7KMnokihMCdx8pWw18OTNxG2cMTRJc2dMBRlFEgafMVwYnIKdoDemgbHnnRh7kF0p577lv_I-qpnV4ADO0j31nlm0iKS5VZ7i0PHkeg1KVMRDNmg
这样就获取到解码后的值了,然后保存到变量中
[root@master pki]# DEF_NS_ADMIN_TOKEN=$(kubectl get secret def-ns-admin-token-qfrqj -o jsonpath={.data.token} | base64 -d)
这样执行后就保存下来了
设置 set-credentials 保存至 def-ns-admin.conf
[root@master pki]# kubectl config set-credentials def-ns-admin --token=${DEF_NS_ADMIN_TOKEN} --kubeconfig=/root/def-ns-admin.conf
[root@master pki]# kubectl config view --kubeconfig=/root/def-ns-admin.conf
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://10.0.20.20:6443
name: kubernetes
contexts: []
current-context: ""
kind: Config
preferences: {}
users:
- name: def-ns-admin # 认证的serviceaccount
user:
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1xZnJxaiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI2ZGU3NWU2Mi1hYjViLTQyMWItOTJhYS0zN2IyMjRmODBmNjEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.k7Oq2V93mz60qxP8Xb2zOoJ9GwnlGbQjeYLJqfqTp-tuhThi_s542GpPWYvEdha-kuxYuyxRf_MUEg-YBCmilS0mqQBVoiHdvJCH6kQTbdZCpJOlML5jXHX9py7TJr8grFHI1aoyo5ZXDM8yZ9tULCpVNLVRz6sCh2wHcCP-pNIA2eaiM_3xM6Ow-0igYe2lxsv2pZcMUWNdi-ImZ9Vv72Nb9sn9rzp2de9RbZ7KMnokihMCdx8pWw18OTNxG2cMTRJc2dMBRlFEgafMVwYnIKdoDemgbHnnRh7kF0p577lv_I-qpnV4ADO0j31nlm0iKS5VZ7i0PHkeg1KVMRDNmg
配置成功
配置 def-ns-admin.conf 上下文
[root@master pki]# kubectl config set-context def-ns-admin@kubernetes --cluster=kubernetes --user=def-ns-admin --kubeconfig=/root/def-ns-admin.conf
Context "def-ns-admin@kubernetes" created.
[root@master pki]# kubectl config view --kubeconfig=/root/def-ns-admin.conf
apiVersion: v1
clusters:
- cluster: # 这里是上面创建的集群
certificate-authority-data: DATA+OMITTED
server: https://10.0.20.20:6443 # 这里是集群地址
name: kubernetes # 这里集群名称
contexts:
- context: # 上面创建的上下文
cluster: kubernetes # 集群
user: def-ns-admin # serviceaccount
name: def-ns-admin@kubernetes
current-context: "" # 这里还没有配置当前上下文
kind: Config
preferences: {}
users:
- name: def-ns-admin
user:
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1xZnJxaiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI2ZGU3NWU2Mi1hYjViLTQyMWItOTJhYS0zN2IyMjRmODBmNjEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.k7Oq2V93mz60qxP8Xb2zOoJ9GwnlGbQjeYLJqfqTp-tuhThi_s542GpPWYvEdha-kuxYuyxRf_MUEg-YBCmilS0mqQBVoiHdvJCH6kQTbdZCpJOlML5jXHX9py7TJr8grFHI1aoyo5ZXDM8yZ9tULCpVNLVRz6sCh2wHcCP-pNIA2eaiM_3xM6Ow-0igYe2lxsv2pZcMUWNdi-ImZ9Vv72Nb9sn9rzp2de9RbZ7KMnokihMCdx8pWw18OTNxG2cMTRJc2dMBRlFEgafMVwYnIKdoDemgbHnnRh7kF0p577lv_I-qpnV4ADO0j31nlm0iKS5VZ7i0PHkeg1KVMRDNmg
配置当前上下文
[root@master pki]# kubectl config view --kubeconfig=/root/def-ns-admin.conf
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://10.0.20.20:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: def-ns-admin
name: def-ns-admin@kubernetes
current-context: def-ns-admin@kubernetes # 当前上下文用户
kind: Config
preferences: {}
users:
- name: def-ns-admin
user:
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1xZnJxaiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI2ZGU3NWU2Mi1hYjViLTQyMWItOTJhYS0zN2IyMjRmODBmNjEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.k7Oq2V93mz60qxP8Xb2zOoJ9GwnlGbQjeYLJqfqTp-tuhThi_s542GpPWYvEdha-kuxYuyxRf_MUEg-YBCmilS0mqQBVoiHdvJCH6kQTbdZCpJOlML5jXHX9py7TJr8grFHI1aoyo5ZXDM8yZ9tULCpVNLVRz6sCh2wHcCP-pNIA2eaiM_3xM6Ow-0igYe2lxsv2pZcMUWNdi-ImZ9Vv72Nb9sn9rzp2de9RbZ7KMnokihMCdx8pWw18OTNxG2cMTRJc2dMBRlFEgafMVwYnIKdoDemgbHnnRh7kF0p577lv_I-qpnV4ADO0j31nlm0iKS5VZ7i0PHkeg1KVMRDNmg
这样,就把当前 上下文的用户配置成功
测试使用kubeconfig文件登陆
下载刚刚生成好的 def-ns-admin.conf
然后测试登陆:
基于 tls 验证
创建 dashboard 专用的 tls 证书
进入到 kubernetes 集群的 master 节点中的 /etc/kubernetes/pki/ 目录
这个目录是专门存放 kubernetes 集群证书的目录
生成dashboard 用户的私钥
[root@master ~]# cd /etc/kubernetes/pki/
[root@master pki]# (umask 077; openssl genrsa -out dashboard.key 2048)
Generating RSA private key, 2048 bit long modulus
........................+++
.........................................................+++
e is 65537 (0x10001)
[root@master pki]# ll dashboard.key
-rw------- 1 root root 1679 Aug 22 17:51 dashboard.key
生成证书签署请求
[root@master pki]# openssl req -new -key dashboard.key -out dashboard.csr -subj "/O=tracy/CN=dashboard"
[root@master pki]# ll dashboard.csr
-rw-r--r-- 1 root root 911 Aug 22 17:54 dashboard.csr
给dashboard证书签证
这里需要注意,一定要kubernetes集群中的 ca.crt 和 ca.key 来签署,这样才能在此集群中使用。
[root@master pki]# openssl x509 -req -in dashboard.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out dashboard.crt -days 365
Signature ok
subject=/O=tracy/CN=dashboard
Getting CA Private Key
这样就签署完成了
创建 dashboard 对应的 secret
[root@master pki]# kubectl create secret generic dashboard-cert -n kube-system --from-file=dashboard.crt --from-file=dashboard.key
secret/dashboard-cert created
[root@master pki]# kubectl get secret -n kube-system dashboard-cert
NAME TYPE DATA AGE
dashboard-cert Opaque 2 16s
[root@master pki]# kubectl describe secret -n kube-system dashboard-cert
Name: dashboard-cert
Namespace: kube-system
Labels: <none>
Annotations: <none>
Type: Opaque
Data
====
dashboard.crt: 1001 bytes
dashboard.key: 1679 bytes
12-kubernetes Dashboard 认证及分级授权的更多相关文章
- kubernetes学习笔记之十一:kubernetes dashboard认证及分级授权
第一章.部署dashboard 作为Kubernetes的Web用户界面,用户可以通过Dashboard在Kubernetes集群中部署容器化的应用,对应用进行问题处理和管理,并对集群本身进行管理.通 ...
- Kubernetes 学习17 dashboard认证及分级授权
一.概述 1.我们前面介绍了kubernetes的两个东西,认证和授权 2.在kubernetes中我们对API server的一次访问大概会包含哪些信息?简单来讲它是restfule风格接口,也就是 ...
- k8s系列--- dashboard认证及分级授权
http://blog.itpub.net/28916011/viewspace-2215214/ 因版本不一样,略有改动 Dashboard官方地址: https://github.com/kube ...
- Kubernetes学习之路(十九)之Kubernetes dashboard认证访问
Dashboard:https://github.com/kubernetes/dashboard 一.Dashboard部署 由于需要用到k8s.gcr.io/kubernetes-dashboar ...
- kubernetes Dashboard 使用RBAC 权限认证控制
kubernetes RBAC实战 环境准备 先用kubeadm安装好kubernetes集群,[包地址在此](https://market.aliyun.com/products/56014009/ ...
- Kubernetes Dashboard 安装与认证
1.安装dashboard $ kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/ ...
- kubernetes dashboard 安装
环境:CentOS Linux release 7.3.1611 (Core)IP:192.168.0.103 [1]组件安装yum install device-mapperyum install ...
- (十三)Kubernetes Dashboard
Dashboard概述 Github地址 Dashboard是Kubernetes的Web GUI,可用于在Kubernetes集群上部署容器化应用.应用排障.管理集群本身及附加的资源等.常用于集群及 ...
- k8s之dashboard认证、资源需求、资源限制及HeapSter
1.部署dashboard kubernetes-dashboard运行时需要有sa账号提供权限 Dashboard官方地址:https://github.com/kubernetes/dashboa ...
随机推荐
- Node.js 使用 express-jwt 解析 JWT
Node.js 上 Token 鉴权常用的是 passport,它可以自定义校验策略,但如果你是用 express 框架,又只是解析 JWT 这种简单需求,可以尝试下 express-jwt 这个中间 ...
- Java 计算n对应的二进制位上有几个1,分别在什么位置
Java计算n的二进制位上有几个1,分别在什么位置 public List<Integer> getBinOneCount(int n){ List<Integer> ...
- CSPS模拟 52
我貌似曾经说过我是个只会做水题的巨型辣鸡.. 这次证明我水题都不会做.. T1 平均数 区间数$n^2$ 枚举是不可能了 可是好像没有无用的计算量.. 刚想到这里,此时开考15min 看见天皇比手势说 ...
- es ik 分词 5.x后,设置默认分词
1.使用模板方式,设置默认分词 注: 设置模板,需要重新导入数据,才生效 通过模板设置全局默认分词器 curl -XDELETE http://localhost:9200/_template/rtf ...
- 开源跳板机(堡垒机)系统 Jumpserver安装教程(带图文)
环境 系统: CentOS 7 IP: 192.168.244.144 关闭 selinux 和防火墙 # CentOS 7 $ setenforce 0 # 可以设置配置文件永久关闭 $ syste ...
- egret常用功能
egret常用功能<pre>//////////////////////////////////////////////////////////////////////////////// ...
- websocket socketJs
springboot实现服务器端消息推送(websocket + sockjs + stomp) 服务器端推送技术在web开发中比较常用,可能早期很多人的解决方案是采用ajax向服务器轮询消息,这 ...
- pandas的使用(5)
pandas的使用(5)-- 缺失值的处理
- 【dp】B-number
题目链接:http://acm.hdu.edu.cn/showproblem.php?pid=3652 题解:先预处理([0,0][1,1],[2,2]....[0,9],[10, 19],[20,2 ...
- NPM 源的管理器nrm
作为一个 NPM 源管理器,nrm允许快速地在如下 NPM 源间切换: 列表项目 npm cnpm strongloop enropean australia nodejitsu taobao Ins ...
