(十三)Kubernetes Dashboard
Dashboard概述
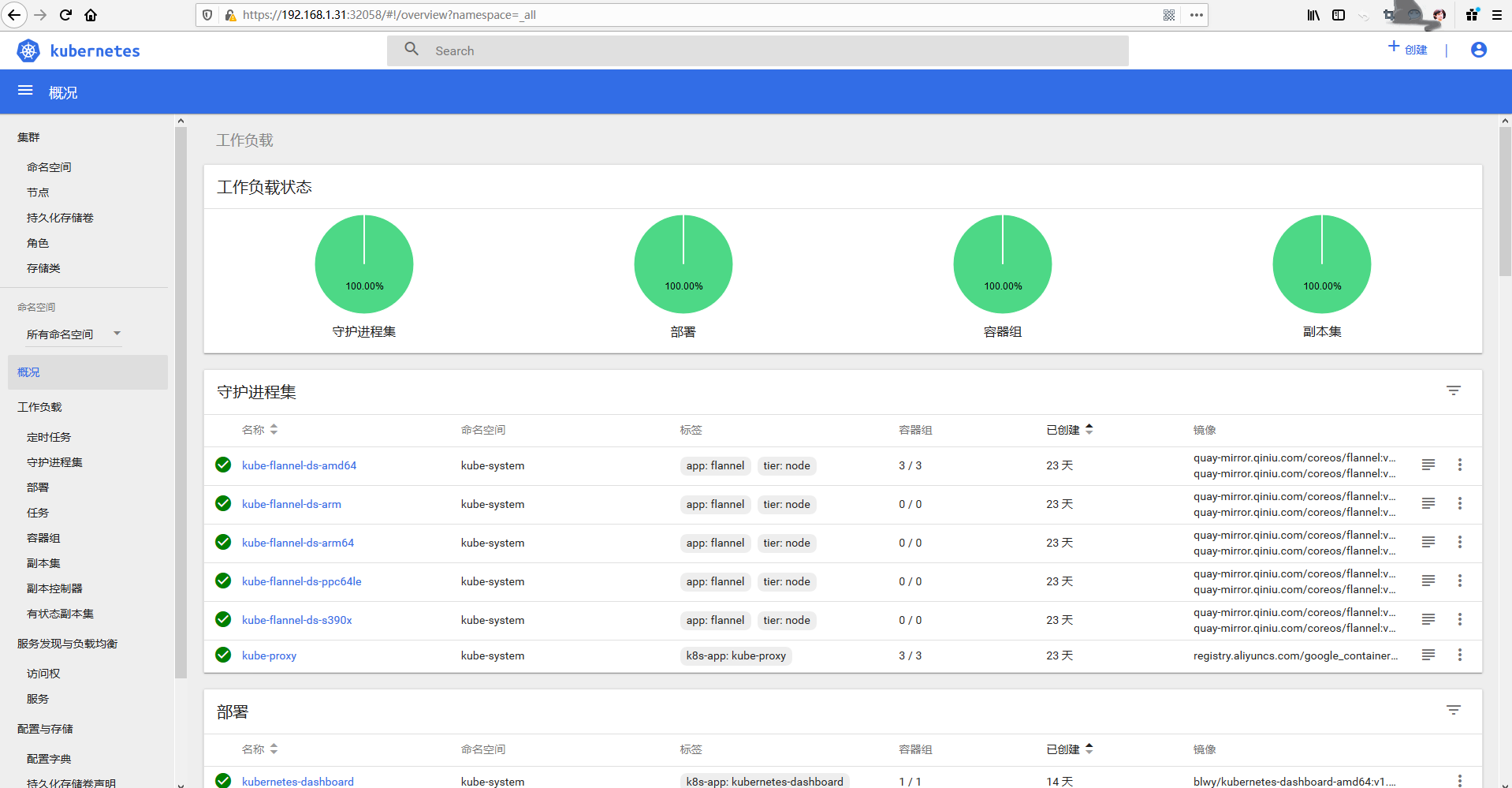
Dashboard是Kubernetes的Web GUI,可用于在Kubernetes集群上部署容器化应用、应用排障、管理集群本身及附加的资源等。常用于集群及应用速览、创建或修改单个资源(如Deployment、Jobs和DaemonSet等),以及扩展Deployment、启动滚动更新、重启Pod或使用部署向导部署一个应用等。
Dashboard的认证和授权均可由Kubernetes集群实现,它自身仅是一个代理,所有的相关操作都将发给API Server进行,而非由Dashboard自行完成。目前仅支持使用的认证方式有令牌(token)认证和kubeconfig两种,在访问之前都需要准备好相应的认证凭证。
Dashboard部署
由于用到镜像
k8s.gcr.io/kubernetes-dashboard-amd64:v1.10.1,是国外的,我们拉取不下来,这里可以使用下面两种方式。# docker pull mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.10.1
或者是
# docker pull blwy/kubernetes-dashboard-amd64:v1.10.1
1)这里将资源清单文件下载本地,编辑使用的镜像
[root@k8s-master ~]# wget https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/deploy/recommended/kubernetes-dashboard.yaml
2)将镜像地址进行更改
[root@k8s-master ~]# vim kubernetes-dashboard.yaml
......
spec:
containers:
- name: kubernetes-dashboard
image: blwy/kubernetes-dashboard-amd64:v1.10.1 #将镜像地址改为可以下载的地址
ports:
......
3)部署
[root@k8s-master ~]# kubectl apply -f kubernetes-dashboard.yaml
secret/kubernetes-dashboard-certs created
serviceaccount/kubernetes-dashboard created
role.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
deployment.apps/kubernetes-dashboard created
service/kubernetes-dashboard created [root@k8s-master ~]# kubectl get pods -n kube-system
NAME READY STATUS RESTARTS AGE
coredns-bccdc95cf-9gsn8 1/1 Running 0 10d
coredns-bccdc95cf-x7m8g 1/1 Running 0 10d
etcd-k8s-master 1/1 Running 0 10d
kube-apiserver-k8s-master 1/1 Running 0 10d
kube-controller-manager-k8s-master 1/1 Running 0 10d
kube-flannel-ds-amd64-gg55s 1/1 Running 0 10d
kube-flannel-ds-amd64-ssr7j 1/1 Running 5 10d
kube-flannel-ds-amd64-w6f9h 1/1 Running 4 10d
kube-proxy-77pbc 1/1 Running 3 10d
kube-proxy-qs655 1/1 Running 3 10d
kube-proxy-xffq4 1/1 Running 0 10d
kube-scheduler-k8s-master 1/1 Running 0 10d
kubernetes-dashboard-d977fcf6-d25xz 1/1 Running 0 4s
4)查看svc,并将类型改为NodePort
[root@k8s-master ~]# kubectl get svc -n kube-system
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP,9153/TCP 9d
kubernetes-dashboard ClusterIP 10.99.151.238 <none> 443/TCP 7m25s #可以像下面直接打补丁进行更改。
[root@k8s-master ~]# kubectl patch svc kubernetes-dashboard -p '{"spec":{"type":"NodePort"}}' -n kube-system
service/kubernetes-dashboard patched
[root@k8s-master ~]# kubectl get svc -n kube-system
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP,9153/TCP 9d
kubernetes-dashboard NodePort 10.99.151.238 <none> 443:32058/TCP 8m45s #或者也可以修改资源清单修改类型为NodePort
[root@k8s-master ~]# vim kubernetes-dashboard.yaml
......
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
ports:
- port: 443
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
type: NodePort #这里添加类型为NodePort
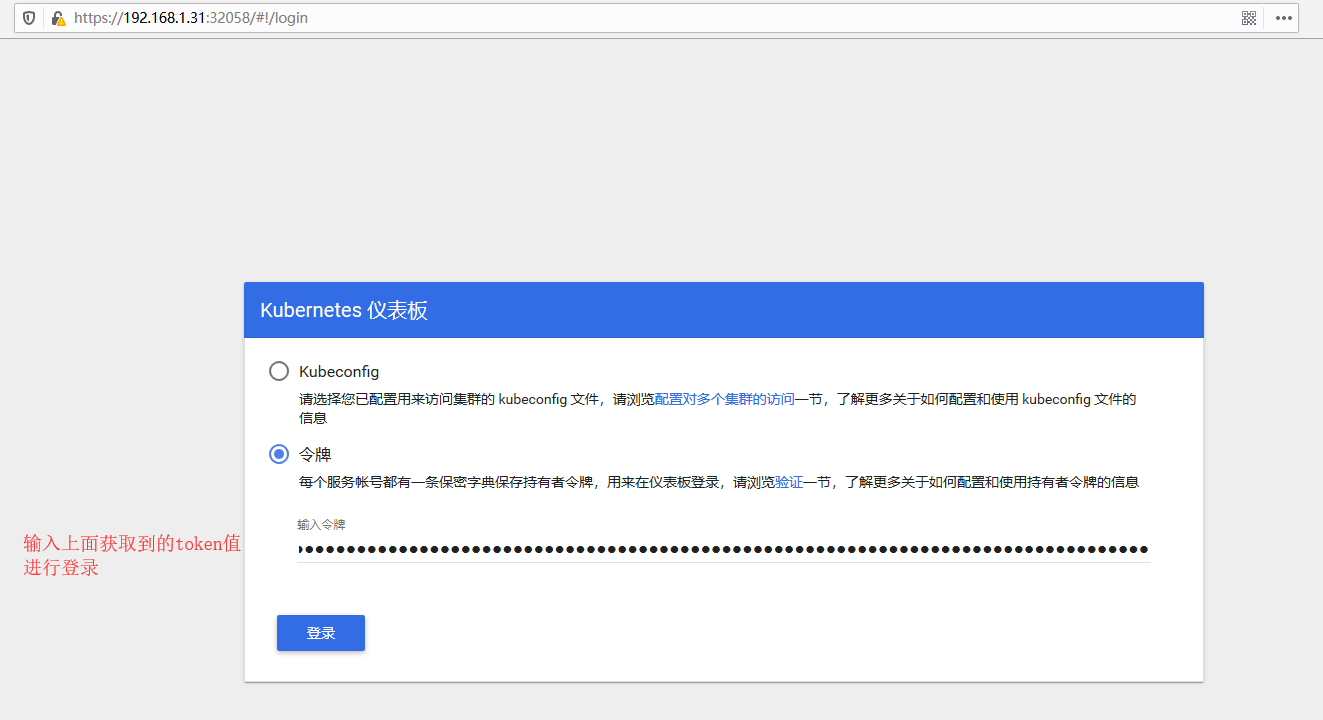
浏览器访问:https://192.168.1.31:32058 如下图;建议使用火狐浏览器,并在高级选项中添加信任,谷歌会禁止不安全证书访问。

token认证
集群级别的管理操作依赖于集群管理员权限,例如,内建的
cluster-admin集群角色拥有全部权限,创建ServiceAccount并将其绑定其上即完成集群管理员授权。而用户通过相应的ServiceAccount的token信息完成Dashboard认证也就能扮演起Dashboard接口上的集群管理员角色。例如,下面创建一个名为dashboard-admin的ServiceAccount,并完成集群角色绑定:
1)创建serviceaccount资源
[root@k8s-master ~]# kubectl create serviceaccount dashboard-admin -n kube-system
serviceaccount/dashboard-admin created
[root@k8s-master ~]# kubectl get sa/dashboard-admin -n kube-system
NAME SECRETS AGE
dashboard-admin 1 15s
2)创建clusterrolebinding,将角色cluster-admin与serviceaccount资源(dashboard-admin)进行绑定
[root@k8s-master ~]# kubectl create clusterrolebinding dashboard-admin --clusterrole=cluster-admin --serviceaccount=kube-system:dashboard-admin
clusterrolebinding.rbac.authorization.k8s.io/dashboard-admin created [root@k8s-master ~]# kubectl describe clusterrolebinding/dashboard-admin #查看绑定信息
Name: dashboard-admin
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: cluster-admin
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount dashboard-admin kube-system
3)查看token值并进行登录验证
[root@k8s-master ~]# ADMIN_SECRET=$(kubectl -n kube-system get secret |awk '/^dashboard-admin/{print $1}') #获取上面创建的dashboard-admin生成的secret的名字
[root@k8s-master ~]# kubectl describe secrets $ADMIN_SECRET -n kube-system |grep ^token #获取上面获取到的secret的token值
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4tbmZ2NGgiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiOTY5MDhiMTgtYzUyYy00NWEwLWIxODEtMTM2OGM4ZGZkMGUwIiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmUtc3lzdGVtOmRhc2hib2FyZC1hZG1pbiJ9.xVHNDKiU7n8fvfN8_5RF3Z6Ppxl-ULk-zYfWywPktJ6mVgtgm4tnAX9_n8zpzHhff1tD4y04Ra7OKvnJTypkI78ELHqggrQxNLggfpbdrWnIif2qIqEbIv5Hay3s4UeOqU2p6Kex4v7UUVtdo781W4rNi7DP2yXKfV5YSTeu6ZMTQiMa3H-O6y-y4sH_ISi_UwiAtHALTJ_OX-j9BzsFIUBhryKnGbOK4ygVmlTA2tWFe8TDUI6xCTjEKSRId3iL_TpKg-uXc652JHnQPYH2ZErojWCbwGR6IqeRTH4kMlAfjvDIeDdT6sSNyjJONpgJQpdYtaGzQiHgE2CW2_q4zQ
输入上获取到的token进行登录。
Kubeconfig认证
kubeconfig是认证信息承载工具,能够持久存入秘钥和证书,或者认证令牌等作为用户的认证配置文件。为了说明如何配置一个仅具有特定名称空间管理权限的登录账号,这里创建一个新的ServiceAccount用于管理默认的default名称空间,并将之绑定于admin集群角色。
1)创建serviceaccount资源
[root@k8s-master ~]# kubectl create serviceaccount def-ns-admin -n default #创建sa资源def-ns-admin
serviceaccount/def-ns-admin created [root@k8s-master ~]# kubectl get sa/def-ns-admin -n default #查看上面创建的sa资源
NAME SECRETS AGE
def-ns-admin 1 19s
2)创建rolebinding,将上面创建的serviceaccount与clusterrole(admin)进行绑定
[root@k8s-master ~]# kubectl create rolebinding def-ns-admin --clusterrole=admin --serviceaccount=default:def-ns-admin
rolebinding.rbac.authorization.k8s.io/def-ns-admin created [root@k8s-master ~]# kubectl get secret |grep def-ns #查看生成的secret
def-ns-admin-token-m2ct6 kubernetes.io/service-account-token 3 106s [root@k8s-master ~]# kubectl describe secret/def-ns-admin-token-m2ct6 #查看secret资源详细信息
Name: def-ns-admin-token-m2ct6
Namespace: default
Labels: <none>
Annotations: kubernetes.io/service-account.name: def-ns-admin
kubernetes.io/service-account.uid: f824dbcd-d661-4776-993a-921042f7e196 Type: kubernetes.io/service-account-token Data
====
namespace: 7 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1tMmN0NiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiJmODI0ZGJjZC1kNjYxLTQ3NzYtOTkzYS05MjEwNDJmN2UxOTYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.U72TWqg3pd-zJgd0QsoYysbNm4rf8rPtEvNBDoVRpRnuX_NkJPtSniAdEIw-g_RjZXNhWHjOXOUmlQ1HwXu0FO3d_j0g6S3dX5BlEA4uPeNskgTH83T7g2BoI3XazAzLKtfGPUuOPk9F2IQQvp3m93x-D1BETOp4ga-R4CMQdVZBUl4XWqFpDxJ47pCsK_VrvP3g7LJpzJk9dnwr2i4-3ysLFwZ84x07Kbcw-1ED8jMh8LNpUGPnevpKntqwo9ghCDVN-oPdPGcXlvxrc9enDu_7gIb2H_fJbMWS_vH1pQX8SoYDhneW2gkVKg2RaW1QaF4TrcdUAabcCcfoqdiCxg
ca.crt: 1025 bytes
3)初始化集群信息,提供API Server的URL,以及验证API Server证书所用到的CA证书等
[root@k8s-master ~]# kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.crt --server="https://192.168.1.31:6443" --embed-certs=true --kubeconfig=/root/def-ns-admin.conf
Cluster "kubernetes" set. [root@k8s-master ~]# kubectl config view --kubeconfig=/root/def-ns-admin.conf #查看生成的配置文件信息
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://192.168.1.31:6443
name: kubernetes
contexts: []
current-context: ""
kind: Config
preferences: {}
users: []
4)获取def-ns-admin的token,并将其作为认证信息。由于直接得到的token是base64编码格式,故采用“base -d”命令将其解码
[root@k8s-master ~]# kubectl get secret -n default
NAME TYPE DATA AGE
admin-token-lc826 kubernetes.io/service-account-token 3 16d
def-ns-admin-token-m2ct6 kubernetes.io/service-account-token 3 12m [root@k8s-master ~]# kubectl -n default get secret/def-ns-admin-token-m2ct6 -o jsonpath={.data.token} |base64 -d #获取token并将其解码
eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1tMmN0NiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiJmODI0ZGJjZC1kNjYxLTQ3NzYtOTkzYS05MjEwNDJmN2UxOTYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.U72TWqg3pd-zJgd0QsoYysbNm4rf8rPtEvNBDoVRpRnuX_NkJPtSniAdEIw-g_RjZXNhWHjOXOUmlQ1HwXu0FO3d_j0g6S3dX5BlEA4uPeNskgTH83T7g2BoI3XazAzLKtfGPUuOPk9F2IQQvp3m93x-D1BETOp4ga-R4CMQdVZBUl4XWqFpDxJ47pCsK_VrvP3g7LJpzJk9dnwr2i4-3ysLFwZ84x07Kbcw-1ED8jMh8LNpUGPnevpKntqwo9ghCDVN-oPdPGcXlvxrc9enDu_7gIb2H_fJbMWS_vH1pQX8SoYDhneW2gkVKg2RaW1QaF4TrcdUAabcCcfoqdiCxg [root@k8s-master ~]# DEFNS_ADMIN_TOKEN=$(kubectl -n default get secret/def-ns-admin-token-m2ct6 -o jsonpath={.data.token} |base64 -d) #这里将上面得到的token保存为一个变量,方便调用 [root@k8s-master ~]# kubectl config set-credentials def-ns-admin --token=$DEFNS_ADMIN_TOKEN --kubeconfig=/root/def-ns-admin.conf
User "def-ns-admin" set.
5)设置cotext列表,定义一个名为def-ns-admin的context
[root@k8s-master ~]# kubectl config set-context def-ns-admin@kubernetes --cluster=kubernetes --user=def-ns-admin --kubeconfig=/root/def-ns-admin.conf
Context "def-ns-admin@kubernetes" created.
6)最后指定要使用的context为前面定义的名为def-ns-admin的context
[root@k8s-master ~]# kubectl config use-context def-ns-admin@kubernetes --kubeconfig=/root/def-ns-admin.conf [root@k8s-master ~]# kubectl config view --kubeconfig=/root/def-ns-admin.conf #查看最终生成的配置文件信息
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://192.168.1.31:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: def-ns-admin
name: def-ns-admin@kubernetes
current-context: def-ns-admin@kubernetes
kind: Config
preferences: {}
users:
- name: def-ns-admin
user:
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1tMmN0NiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiJmODI0ZGJjZC1kNjYxLTQ3NzYtOTkzYS05MjEwNDJmN2UxOTYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.U72TWqg3pd-zJgd0QsoYysbNm4rf8rPtEvNBDoVRpRnuX_NkJPtSniAdEIw-g_RjZXNhWHjOXOUmlQ1HwXu0FO3d_j0g6S3dX5BlEA4uPeNskgTH83T7g2BoI3XazAzLKtfGPUuOPk9F2IQQvp3m93x-D1BETOp4ga-R4CMQdVZBUl4XWqFpDxJ47pCsK_VrvP3g7LJpzJk9dnwr2i4-3ysLFwZ84x07Kbcw-1ED8jMh8LNpUGPnevpKntqwo9ghCDVN-oPdPGcXlvxrc9enDu_7gIb2H_fJbMWS_vH1pQX8SoYDhneW2gkVKg2RaW1QaF4TrcdUAabcCcfoqdiCxg
7)将这个配置文件保存client上,通过加装该配置文件进行登录

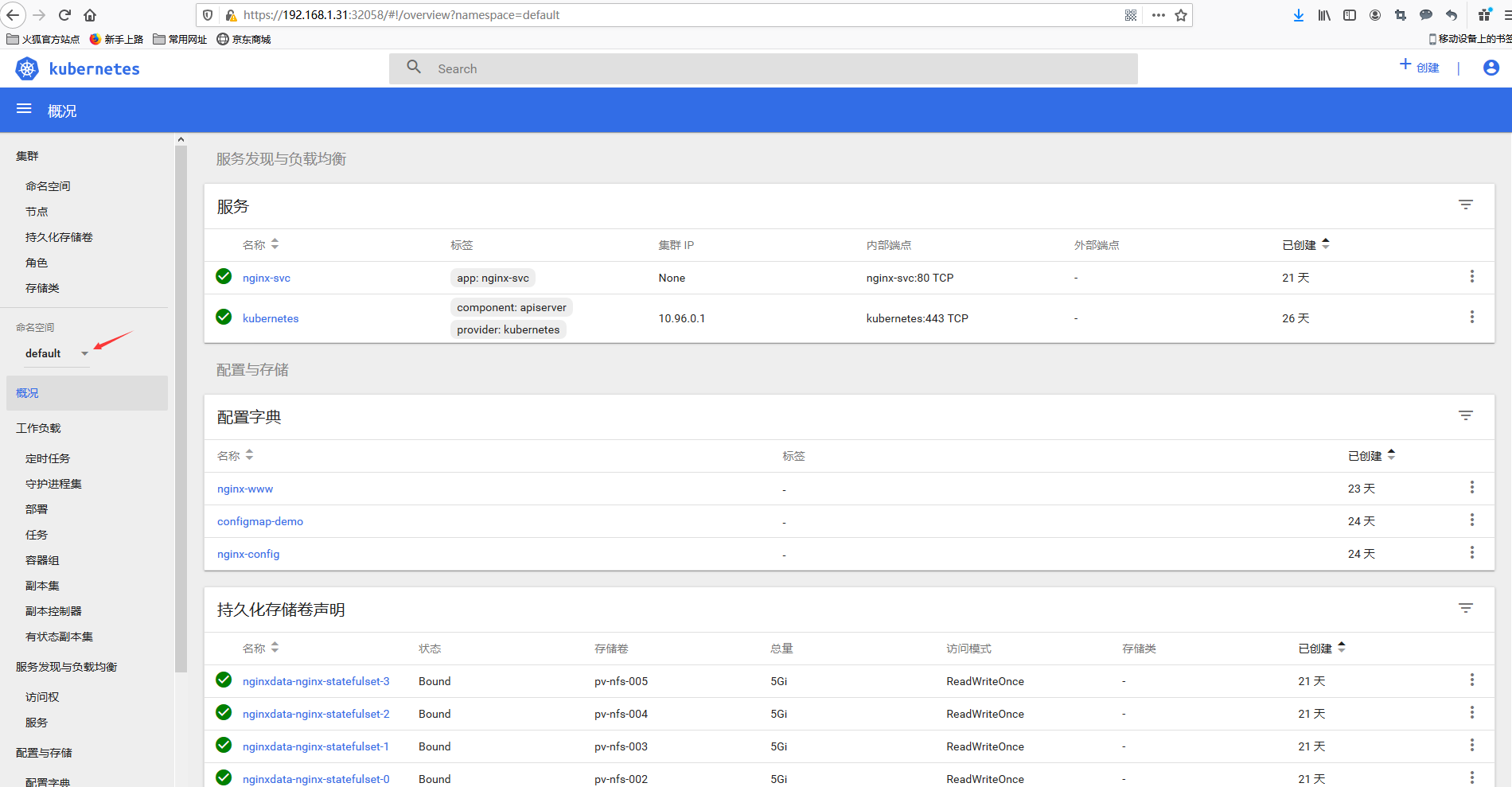
这里通过测试可以发现,这里的def-ns-admin用户登录进来只能看到default名称空间的内容。也只能对default名称空间的资源进行管理。
(十三)Kubernetes Dashboard的更多相关文章
- Kubernetes Dashboard - 每天5分钟玩转 Docker 容器技术(173)
前面章节 Kubernetes 所有的操作我们都是通过命令行工具 kubectl 完成的.为了提供更丰富的用户体验,Kubernetes 还开发了一个基于 Web 的 Dashboard,用户可以用 ...
- Kubernetes dashboard安装
1. To download Dashboard plugin deployment YAML file from internet. #cd /home #mkdir k8s #cd k8s # w ...
- centos7下kubernetes(5。部署kubernetes dashboard)
基于WEB的dashboard,用户可以用kubernetes dashboard部署容器话的应用,监控应用的状态,执行故障排查任务以及管理kubernetes各种资源. 在kubernetes da ...
- kubernetes学习笔记之十一:kubernetes dashboard认证及分级授权
第一章.部署dashboard 作为Kubernetes的Web用户界面,用户可以通过Dashboard在Kubernetes集群中部署容器化的应用,对应用进行问题处理和管理,并对集群本身进行管理.通 ...
- Mac搭建kubernetes dashboard全流程
1. 下载dashboard文件: curl -o kubernetes-dashboard.yaml https://raw.githubusercontent.com/kubernetes/das ...
- kubernetes Dashboard 使用RBAC 权限认证控制
kubernetes RBAC实战 环境准备 先用kubeadm安装好kubernetes集群,[包地址在此](https://market.aliyun.com/products/56014009/ ...
- docker for mac 安装 kubernetes、kubernetes dashboard
安装参考地址(按照此文档,安装成功):https://yq.aliyun.com/articles/508460 官方说明:https://kubernetes.io/docs/tasks/acces ...
- Kubernetes学习之路(十九)之Kubernetes dashboard认证访问
Dashboard:https://github.com/kubernetes/dashboard 一.Dashboard部署 由于需要用到k8s.gcr.io/kubernetes-dashboar ...
- Kubernetes dashboard 配置
安装前准备 下载dashboard的yaml文件 wget -O kube-dashboard.yaml https://git.io/kube-dashboard-no-rbac 这个版本是没有权限 ...
随机推荐
- leetcode 947. 移除最多的同行或同列的石头
题目描述: 在二维平面上,我们将石头放置在一些整数坐标点上.每个坐标点上最多只能有一块石头. 现在,move 操作将会移除与网格上的某一块石头共享一列或一行的一块石头. 我们最多能执行多少次 move ...
- Java中的数据类型与运算符
一.变量的命名 (1)什么是变量:变量是java中存储数据的空间. (2)变量命名的规则:由:数(数字),字(字母),下(下划线),美(美元符号),人(人名币符号)组成的标识符.注:数字不能作为首字母 ...
- SQL Server DBCC命令大全
原文出处:https://www.cnblogs.com/lyhabc/archive/2013/01/19/2867174.html DBCC DROPCLEANBUFFERS:从缓冲池中删除所有缓 ...
- 报错 xxx@1.0.0 dev D:\> webpack-dev-server --inline --progress --configbuild/webpack.dev.conf.js
是因为node_modules有意外改动,导致依赖库不完整. 解决:1.删除项目下的node_modules,在你的项目目录下 重新执行npm install,这会重新生成node_modules, ...
- 通过Queue控制线程并发,并监控队列执行进度
# -*- coding:utf-8 -*- import Queue import time import threading # 需要执行的业务主体 def domain(id): time.sl ...
- ML学习笔记之Anaconda中命令形式安装XGBoost(pip install)
0x00 概述 在没有安装XGBoost之前,import xgboot会出错,如下: # ModuleNotFoundError: No module named ‘xgboost’ 0x01 安装 ...
- Linux学习笔记之CentOS 7系统使用firewalld管理防火墙端口
0x00 firewalld的基本使用 # 启动: systemctl start firewalld # 查看状态: systemctl status firewalld # 停止: systemc ...
- Mybatis+MySql 一个标签中执行多条sql语句
版权声明:本文为博主原创文章,未经博主允许不得转载. https://blog.csdn.net/cxfly957/article/details/77896590 MySql默认是不支持这种骚操作的 ...
- B树索引最通俗易懂的介绍
先来一段有莫的对话: 前几天下班回到家后正在处理一个白天没解决的bug,厕所突然传来对象的声音: 对象:xx,你有<时间简史>吗? 我:我去!妹子,你这啥癖好啊,我有时间也不会去捡屎 ...
- [Leetcode] 1120. Maximum Average Subtree
Given the root of a binary tree, find the maximum average value of any subtree of that tree. (A subt ...
