腾讯云CVM之间配置免密钥登录
背景:
1客户A和B俩台主机之间需要实现免密钥登录,已绑定腾讯云申请的密钥对
系统:centos7.3
A:192.168.0.100
B:192.168.0.84
A主机的私钥文件:aaa
B主机的私钥文件:bbb
公钥文件:authorized_keys
/etc/ssh/sshd.conf文件修改参数,前面有“#”注释符的需要去掉
HostKey /etc/ssh/ssh_host_rsa_key
RSAAuthentication yes
PubkeyAuthentication yes
AuthorizedKeysFile .ssh/authorized_keys
PasswordAuthentication no
参考sshd_config配置文件,注意系统版本,不适用centos6.x版本,修改配置文件前做好备份
# $OpenBSD: sshd_config,v 1.93 // :: djm Exp $ # This is the sshd server system-wide configuration file. See
# sshd_config() for more information. # This sshd was compiled with PATH=/usr/local/bin:/usr/bin # The strategy used for options in the default sshd_config shipped with
# OpenSSH is to specify options with their default value where
# possible, but leave them commented. Uncommented options override the
# default value. # If you want to change the port on a SELinux system, you have to tell
# SELinux about this change.
# semanage port -a -t ssh_port_t -p tcp #PORTNUMBER
#
#Port
#AddressFamily any
#ListenAddress 192.168.0.100
#ListenAddress 192.168.0.100 # The default requires explicit activation of protocol
#Protocol # HostKey for protocol version
#HostKey /etc/ssh/ssh_host_key
# HostKeys for protocol version
HostKey /etc/ssh/ssh_host_rsa_key
#HostKey /etc/ssh/ssh_host_dsa_key
HostKey /etc/ssh/ssh_host_ecdsa_key
HostKey /etc/ssh/ssh_host_ed25519_key # Lifetime and size of ephemeral version server key
#KeyRegenerationInterval 1h
#ServerKeyBits # Ciphers and keying
#RekeyLimit default none # Logging
# obsoletes QuietMode and FascistLogging
#SyslogFacility AUTH
SyslogFacility AUTHPRIV
#LogLevel INFO # Authentication: #LoginGraceTime 2m
#PermitRootLogin yes
#StrictModes yes
#MaxAuthTries
#MaxSessions RSAAuthentication yes
PubkeyAuthentication yes # The default is to check both .ssh/authorized_keys and .ssh/authorized_keys2
# but this is overridden so installations will only check .ssh/authorized_keys
AuthorizedKeysFile .ssh/authorized_keys #AuthorizedPrincipalsFile none #AuthorizedKeysCommand none
#AuthorizedKeysCommandUser nobody # For this to work you will also need host keys in /etc/ssh/ssh_known_hosts
#RhostsRSAAuthentication no
# similar for protocol version
#HostbasedAuthentication no
# Change to yes if you don't trust ~/.ssh/known_hosts for
# RhostsRSAAuthentication and HostbasedAuthentication
#IgnoreUserKnownHosts no
# Don't read the user's ~/.rhosts and ~/.shosts files
#IgnoreRhosts yes # To disable tunneled clear text passwords, change to no here!
#PasswordAuthentication no
#PermitEmptyPasswords no
PasswordAuthentication no # Change to no to disable s/key passwords
#ChallengeResponseAuthentication yes
ChallengeResponseAuthentication no # Kerberos options
#KerberosAuthentication no
#KerberosOrLocalPasswd yes
#KerberosTicketCleanup yes
#KerberosGetAFSToken no
#KerberosUseKuserok yes # GSSAPI options
GSSAPIAuthentication yes
GSSAPICleanupCredentials no
#GSSAPIStrictAcceptorCheck yes
#GSSAPIKeyExchange no
#GSSAPIEnablek5users no # Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# be allowed through the ChallengeResponseAuthentication and
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication via ChallengeResponseAuthentication may bypass
# the setting of "PermitRootLogin without-password".
# If you just want the PAM account and session checks to run without
# PAM authentication, then enable this but set PasswordAuthentication
# and ChallengeResponseAuthentication to 'no'.
# WARNING: 'UsePAM no' is not supported in Red Hat Enterprise Linux and may cause several
# problems.
UsePAM yes #AllowAgentForwarding yes
#AllowTcpForwarding yes
#GatewayPorts no
X11Forwarding yes
#X11DisplayOffset
#X11UseLocalhost yes
#PermitTTY yes
#PrintMotd yes
#PrintLastLog yes
#TCPKeepAlive yes
#UseLogin no
UsePrivilegeSeparation sandbox # Default for new installations.
#PermitUserEnvironment no
#Compression delayed
#ClientAliveInterval
#ClientAliveCountMax
#ShowPatchLevel no
UseDNS no
#PidFile /var/run/sshd.pid
#MaxStartups ::
#PermitTunnel no
#ChrootDirectory none
#VersionAddendum none # no default banner path
#Banner none # Accept locale-related environment variables
AcceptEnv LANG LC_CTYPE LC_NUMERIC LC_TIME LC_COLLATE LC_MONETARY LC_MESSAGES
AcceptEnv LC_PAPER LC_NAME LC_ADDRESS LC_TELEPHONE LC_MEASUREMENT
AcceptEnv LC_IDENTIFICATION LC_ALL LANGUAGE
AcceptEnv XMODIFIERS # override default of no subsystems
Subsystem sftp /usr/libexec/openssh/sftp-server # Example of overriding settings on a per-user basis
#Match User anoncvs
# X11Forwarding no
# AllowTcpForwarding no
# PermitTTY no
# ForceCommand cvs server
操作步骤
1.首先把aaa和bbb私钥文件分别上传到A主机和B主机上的/root/.ssh/目录中(上传可以安装lrzsz工具,直接拖文件到服务器即可)
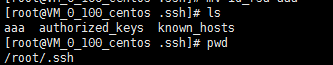
A主机:
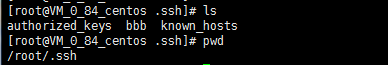
B:主机
2.将A主机中的authorized_keys中的公钥拷贝到B主机的authorized_keys文件中
将B主机中的authorized_keys中的公钥保存的A主机的authorized_keys文件中
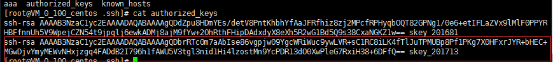
A主机的authorized_keys文件
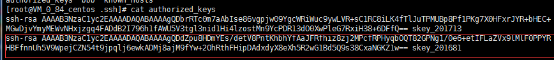
B主机的authorized_keys文件
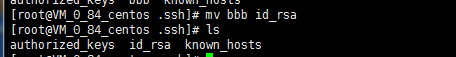
3.将A主机和B主机的私钥文件分别修改为id_rsa
A主机.ssh/目录下的内容
mv /root/.ssh/aaa /root/.ssh/id_rsa
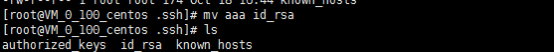
B主机.ssh/目录下的内容
mv /root/.ssh/aaa /root/.ssh/id_rsa
4.分别在A主机和B主机上执行下面授权操作
chmod 700 ~/.ssh/
chmod 600 ~/.ssh/authorized_keys
chmod 600 ~/.ssh/id_rsa
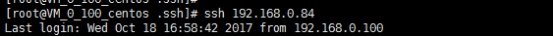
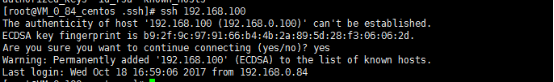
最后来验证
A主机远程B主机:
B主机远程A主机
腾讯云CVM之间配置免密钥登录的更多相关文章
- Linux机器之间SSH免密钥登录设置
SSH免密钥登录 私钥:密钥留在本机 公钥:密钥发给其他机 hadoop01 生成密钥: ssh-keygen -t rsa (密钥存放路径:/root/.ssh) id_rsa:私钥 id_rsa. ...
- linux 服务器之间配置免密登录
客户机:172.16.1.2 远程机:172.16.1.3 1.远程机 a.允许root用户通过22端口登录 vi /etc/ssh/sshd_config PORT 22 PermitRootLog ...
- 弹性配置为构建提速 - CODING & 腾讯云 CVM 最佳实践
CODING 中提供了内置云主机用来执行持续集成(CI)中的构建计划,能够胜任大部分构建任务.但如果碰上了大型项目的构建,或者需要在本地服务器生成构建成果,单个计算资源就显得有点捉急了.针对这一部分需 ...
- 集群中配置多台机器之间 SSH 免密码登录
集群中配置多台机器之间 SSH 免密码登录 问题描述 由于现在项目大多数由传统的单台机器部署,慢慢转变成多机器的集群化部署. 但是,这就涉及到机器间的 SSH 免密码互通问题. 当集群机器比较多的时候 ...
- java:Linux(简单命令,远程ssh使用hostname访问,.免密钥登录配置)
1.临时关闭防火墙: service iptables stop 临时开启防火墙: service iptables start 查看防火墙状态: service iptables sta ...
- linux系统ssh免密钥登录配置
linux主机配置ssh免密钥登录,具体配置如下: 1.执行命令ssh-keygen -t rsa,生成公钥和私钥(具体步骤详见下图) 2.会在当前用户的家目录的.ssh/生成公钥和私钥, 3.执行s ...
- 集群之间配置 SSH无密码登录
集群之间配置 SSH无密码登录 配置 ssh (1)基本语法 ssh 另一台电脑的 ip 地址 (2)ssh 连接时出现 Host key verification failed 的解决方法 # ss ...
- [CentOS] SSH 免密钥登录
一.环境说明: 操作系统:CentOS-7-x86_64-Minimal-1611 虚拟机:VMware® Workstation 12 Pro:12.5.5 build-5234757 服务器:no ...
- 014-配置SSH免密钥登录
问题:client端需要免密钥登录服务器server如何配置?1.前提:客户端已安装openssh-client;服务端已安装openssh-server;服务器端22号端口已经打开2.需要密钥登录时 ...
随机推荐
- MQTT学习笔记
因为工作需要,了解了一下MQTT.顺便记下来,现在还不会用. 一.概述 MQTT(Message Queuing Telemetyr Transport 消息队列遥测传输协议):基于发布/订阅(Pu ...
- Mybatis中#{}和${}传参的区别及#和$的区别小结
最近在用mybatis,之前用过ibatis,总体来说差不多,不过还是遇到了不少问题,再次记录下, 比如说用#{},和 ${}传参的区别, 使用#传入参数是,sql语句解析是会加上"&quo ...
- 关于MySQL常用的查询语句
一查询数值型数据: SELECT * FROM tb_name WHERE sum > 100; 查询谓词:>,=,<,<>,!=,!>,!<,=>,= ...
- Docker 容器内存限制 - 八
Docker 内存限制: centos /bin/bash 查看容器实例 内存限制: 限制容器内存大小:docker run -d -i -t -m 256M --memory-swap 512M ...
- HMM拓扑与转移模型
<Topology> <TopologyEntry> <ForPhones> 1 2 3 4 5 6 7 8 </ForPhones> < ...
- IT界的一些朗朗上口的名言
序 中国有很多古代警世名言,朗朗上口,凝聚了很多故事与哲理.硅谷的互联网公司里头也有一些这样的名言,凝聚了很多公司价值观和做事的方法,对于很多程序员来说,其影响潜移默化.这里收集了一些,如下. Sta ...
- android 内存回收及怎样避免内存泄露
http://blog.vunso.com/201307/android%E5%9E%83%E5%9C%BE%E5%9B%9E%E6%94%B6%E6%9C%BA%E5%88%B6%E5%8F%8A% ...
- app-web 开发 追溯debug
1.iphone5 运行vue项目时,方法格式:fun(){}这种格式容易不显示页面 2.vue未绑定上数据有可能是js文本过大,手机内存不足引起的 3.根据方法走向追溯debug 4.一定要用try ...
- Django REST framework 第三章 CBV
从介绍Django快开始,我们就一直在使用FBV的方式来撰写代码,二者本质上并没有太大的区别,然而到了REST framework,更会倾向于用CBV来写API的视图,后面会看到这个方式的强大,它允许 ...
- 🍓 JRoll、React滑动删除 🍓
import React, { Component } from 'react'; import '../src/css/reset.css'; import '../src/css/delete.c ...
