BUGKU (Take the maze)
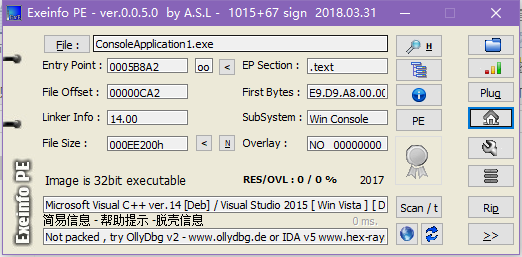
首先进行查壳,没有壳。
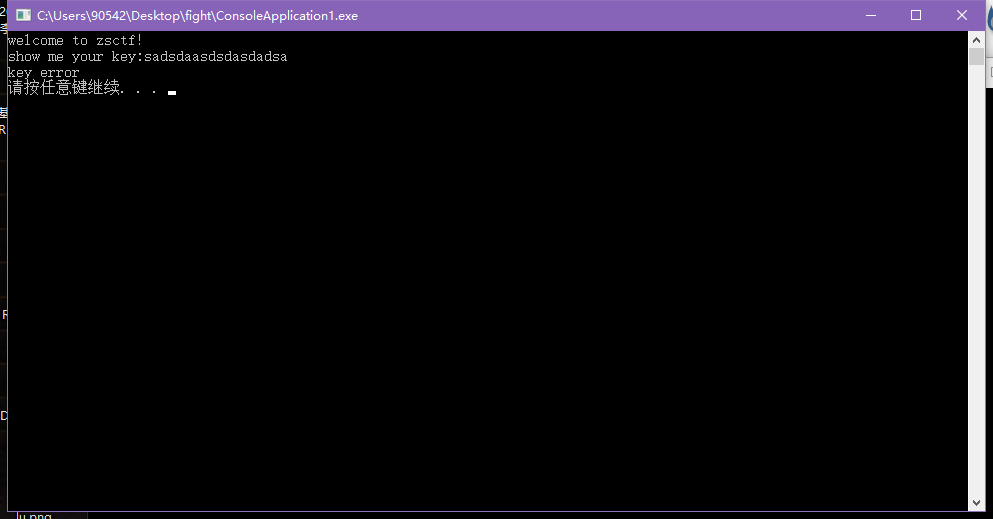
随便输入,看程序执行信息。随意输入字符串,提示key error
放到IDA中打开,在左侧函数窗口中找到main0,F5反编译,进行分析。具体已在分析在图中标识。
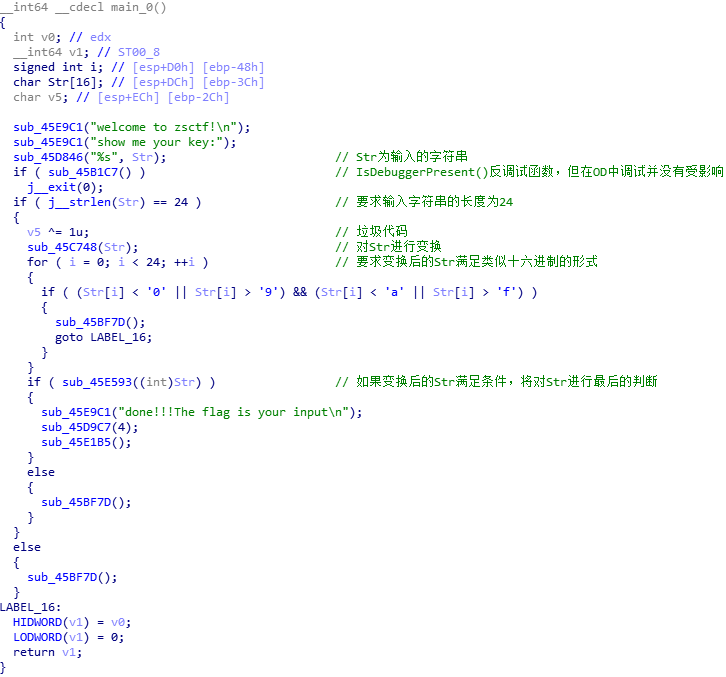
关于main函数的逻辑是很容易理解的,但是接下来可就犯难了。我首先是打开45C748(对Str进行变换的函数)。如下图,看起来应该是在进行对Str变换之前,做一些初始化工作。

整个过程不难理解,但当我打开45DCD3函数时,就一头雾水了。
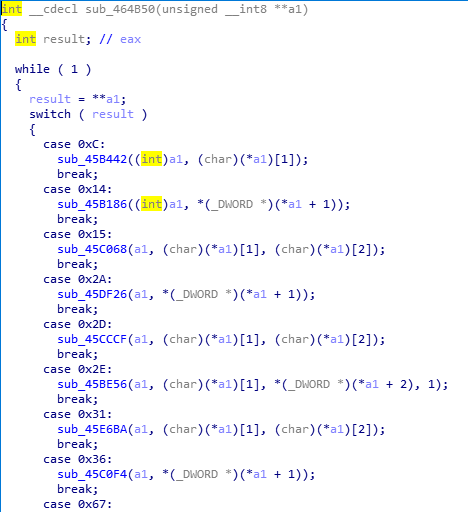
这没得分析(后来才知道是VM处理过的),于是打开OD输入012345678901234567891234,试试看(之前做过一个逆向题,印象深刻,那也是对字符串进行变换的函数,再IDA中查看,根本看不明白,拿到OD里面一跑,才知道,原来就是个base64编码啊。╮(╯▽╰)╭)经过变换,如下图所示。
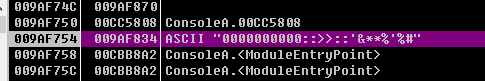
我做过的逆向题不多,根据以往的经验,在IDA中看不懂,或者是不是很理解的情况下,在OD中跟进调试一下,往往会有所收获。所以就跟进了这个函数。结果,不会就是不会,一点办法都没有。╮(╯_╰)╭。之后,也是在调试的时候偶然把上图的字符串(即0000000000::>>::'&**%'%#)当作输入,进行调试,结果发现返回的竟是012345678901234567891234。当时没有细想,没感觉有什么大不了的。后来才猛然间醒悟,如果知道了正确的输入,先输入进去,得到加密后的字符串,这不就是flag了吗?于是有了往下做下去的动力。
接着分析。
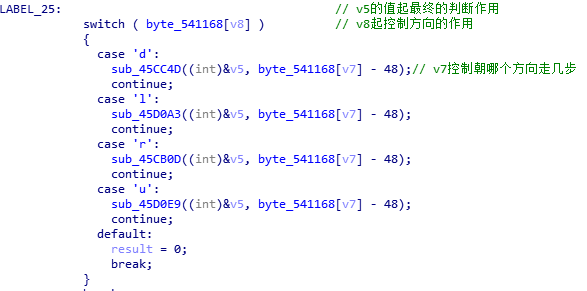
再来打开其中的45CC4D函数。(其中的注释是后来看了别人的WP加的)。
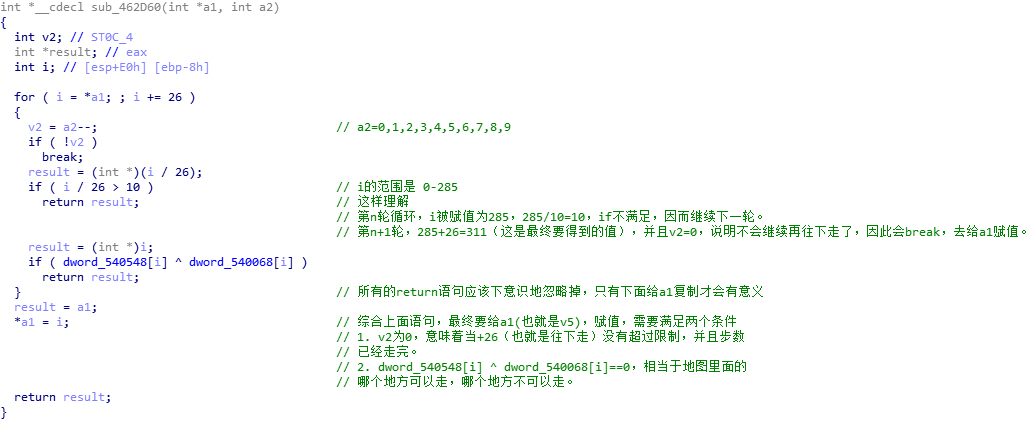
之前做过类似的迷宫逆向题,知道得有一张“地图”,可找了半天也没发现。再者这个函数里面套函数,这种return,实在绕的头疼,最后还是看了别人的WP,找了找思路。原来得在if语句这里,写一个IDC内置脚本(第一次接触)。
这个脚本很容易理解。然后的话,四个函数里面的数组都是不一样的,然后一个个把Dword中的地址改掉,dump出“地图”来就行了。
auto i;
for(i=;i<*;i++){
if(Dword(0x540548+*i)^Dword(0x540068+*i))
Message("0,");
else Message("1,");
}
我用的python,它处理字符串不能够直接修改某个位置上的值,所以用C写会舒服一些。
up='0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,0,0,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,0,1,0,0,0,1,0,0,1,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,1,1,1,0,0,0,1,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,1,1,0,0,0,0,0,1,1,1,1,1,0,0,0,0,0,1,1,0,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,1,1,1,1,1,1,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,1,1,1,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0'.replace(',','')
down='1,1,0,1,0,0,0,1,0,0,1,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,1,1,1,0,0,0,1,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,1,1,0,0,0,0,0,1,1,1,1,1,0,0,0,0,0,1,1,0,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,1,1,1,1,1,1,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,1,1,1,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0'.replace(',','')
left='0,1,0,0,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,0,1,0,0,0,1,0,0,1,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,1,1,1,0,0,0,1,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,1,1,0,0,0,0,0,1,1,1,1,1,0,0,0,0,0,1,1,0,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,1,1,1,1,1,1,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,1,1,1,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,1,1'.replace(',','')
right='0,0,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,0,1,0,0,0,1,0,0,1,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,1,1,1,0,0,0,1,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,1,1,0,0,0,0,0,1,1,1,1,1,0,0,0,0,0,1,1,0,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,1,1,1,1,1,1,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,1,0,0,0,1,1,1,1,1,0,0,0,0,0,0,1,1,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,0,0,0,0,0,0,0,1,1,1,1,1,1,1,1,1,1,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,1,1,1,1,1,0'.replace(',','')
tmp='~`-.'
for i in range(len(up)):
if i%26==0:
print '\n'
if up[i]=='':
tmp=tmp.replace('~','U')
if down[i]=='':
tmp=tmp.replace('`','D')
if left[i]=='':
tmp=tmp.replace('-','L')
if right[i]=='':
tmp=tmp.replace('.','R')
print tmp+' ',
tmp='~`-.'
最后在画图里面打开对应着地图,把路线画出来。
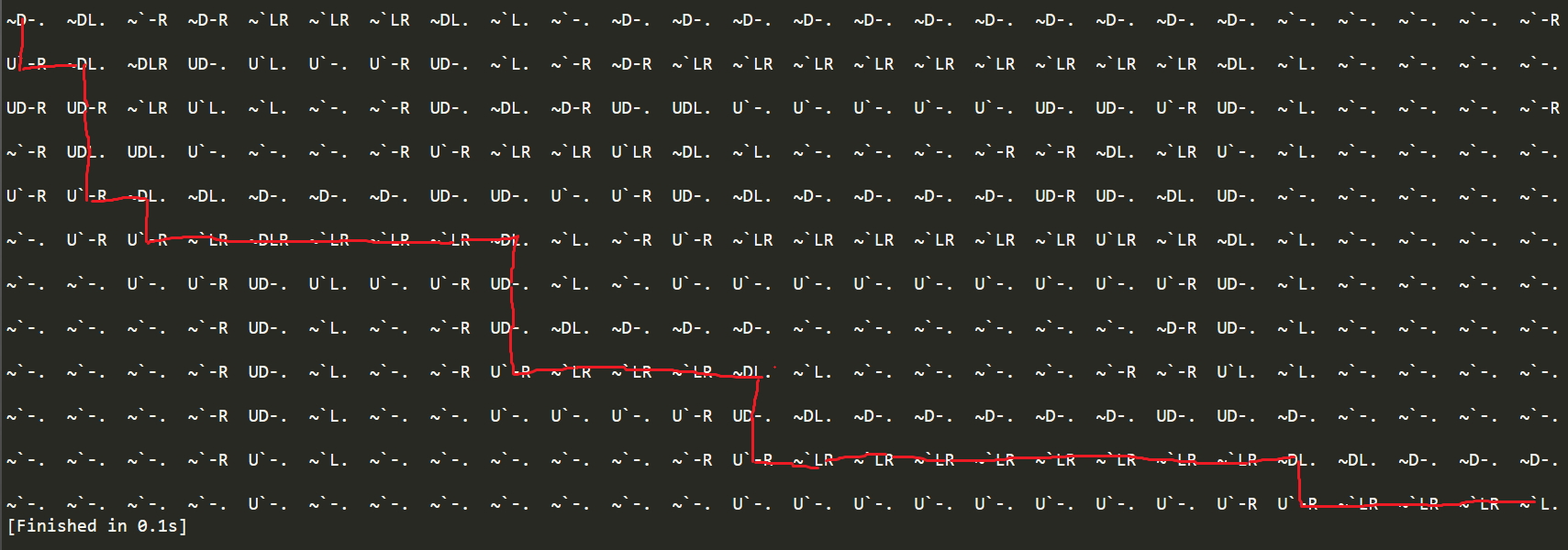
0-d
2-l
3-r
4-u
06260826062b0829072e0629
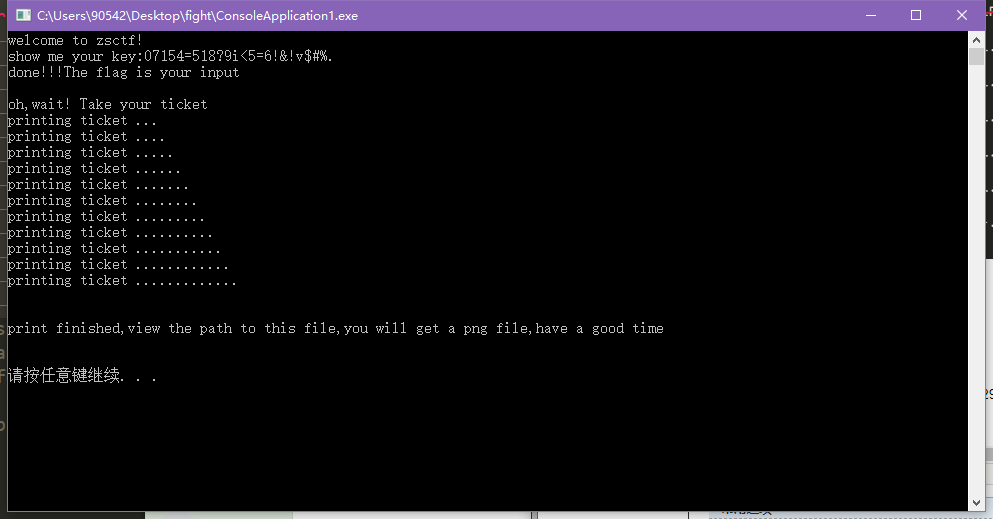
然后按照之前的想法,把06260826062b0829072e0629输进去,得到加密后的字符串,这个字符串再重新输入回去,成功,如下图。
给了张二维码,说是最终flag要加作者的名字。到此结束。
最后感觉这个题,自己感觉还是挺有趣的,其实我如果之前接触过IDC的话,不看别人的WP也会自己做出来的。
BUGKU (Take the maze)的更多相关文章
- 【bugku】【ZSCTF】【迷宫RE】Take The Maze WriteUp
Take The Maze 首先拿进PEID里查一下有没有壳: 无壳,果断拖进IDA.可是Graph View中找不到主程序的位置,在函数表里寻找主函数: 函数太多阻扰了我们找到主程序,运行一下程序找 ...
- bugku 逆向 take the maze
看到如果判断正确之后 会生成一个png文件 直接用idc脚本生成: auto v,begin,end,dexbyte; v = fopen("flag.png", "wb ...
- Backtracking algorithm: rat in maze
Sept. 10, 2015 Study again the back tracking algorithm using recursive solution, rat in maze, a clas ...
- (期望)A Dangerous Maze(Light OJ 1027)
http://www.lightoj.com/volume_showproblem.php?problem=1027 You are in a maze; seeing n doors in fron ...
- 1204. Maze Traversal
1204. Maze Traversal A common problem in artificial intelligence is negotiation of a maze. A maze ...
- uva705--slash maze
/*这道题我原本是将斜线迷宫扩大为原来的两倍,但是在这种情况下对于在斜的方向上的搜索会变的较容易出错,所以参考了别人的思路后将迷宫扩展为原来的3倍,这样就变成一般的迷宫问题了*/ #include&q ...
- HDU 4048 Zhuge Liang's Stone Sentinel Maze
Zhuge Liang's Stone Sentinel Maze Time Limit: 10000/4000 MS (Java/Others) Memory Limit: 32768/327 ...
- Borg Maze(MST & bfs)
Borg Maze Time Limit: 1000MS Memory Limit: 65536K Total Submissions: 9220 Accepted: 3087 Descrip ...
- poj 3026 bfs+prim Borg Maze
Time Limit: 1000MS Memory Limit: 65536K Total Submissions: 9718 Accepted: 3263 Description The B ...
随机推荐
- 一道经典JS面试题
超过80%的候选人对下面这道JS面试题的回答情况连及格都达不到.这究竟是怎样神奇的一道JS面试题?他考察了候选人的哪些能力?对正在读本文的你有什么启示? 不起眼的开始 招聘前端工程师,尤其是中高级前端 ...
- Docker 运行ELK日志监测系统,汉化Kibana界面
1.ELK日志监控简介 ELK由Elasticsearch.Logstash和Kibana三部分组件组成: Elasticsearch是个开源分布式搜索引擎,它的特点有:分布式,零配置,自动发现,索引 ...
- Eclipse指定jdk启动
在eclipse.ini文件中加入这一句话: -vm D:/Java/jdk/jdk1.8/jre/bin/server/jvm.dll
- Oracle之:查询锁表,删除锁表
-- 查询当前哪个表被锁 select sess.sid, sess.serial#, lo.oracle_username, lo.os_user_name, ao.object_name, lo. ...
- 【agc004d】Teleporter
题目大意 一棵树,改变一些边的父亲,使得深度不超过k. 解题思路 我一开始就想到了贪心,结果莫名其妙的把这种方法给否决了, 然后考虑优化树形dp,然后优化失败⊙﹏⊙ 贪心思路很简单,也很好感受出来,从 ...
- js基础----数组
1.数组如何定义 //第一种定义方法 var arr=[1,2,3,4]; //第二种定义方法 var arr=new Array(1,2,3,4); 两者没有任何区别,[]的性能可能略高,因为代码短 ...
- intellij idea http proxy config
# custom IntelliJ IDEA properties #http proxy -DproxySet=true -Dhttp.proxyHost=127.0.0.1 -Dhttp.prox ...
- axios 的坑
必须安装axios 和qs 1.main.js中的配置 import axios from 'axios' import qs from 'qs'; axios.defaults.headers.po ...
- Mysql模拟故障恢复案例过程
一.数据库全备,全备脚本如下: [root@leader script]# cat bak_all.sh #!/bin/bash#Date: 2019-12-08#Author: chan#Mail: ...
- puppet自动化部署
puppet自动化部署 puppet 实现运维自动化管理的软件. 官方网站: http://puppetlabs.com/ pupptet下载链接:http://downloads.puppe ...
